The continued increase in cybercrime and breach attempts is not a new trend. For years now, the percentages have ticked upwards, and though cybersecurity has evolved, so have hackers seeking data, money, or infamy. While the initial attack vectors can be myriad — vulnerability exploits, misconfigurations, and credential theft to name a few — there are two tactics that stand tall above the rest: Ransomware and business email compromise (BEC).
Both attack methods allow threat actors to gain access, data, and money, and with the rise of credential theft and ransomware-as-a-service (RaaS), both methods have become increasingly simple for cybercriminals to carry out. Multiple high-target industries, such as finance and insurance, are particularly susceptible to BEC attacks, and ransomware can strike both small businesses and major enterprises, taking down networks and exfiltrating troves of data.
Therefore, it’s critical that organizations understand both kinds of attacks, how they are increasing, and what proactive and reactive steps need to be taken for full protection.
Why Ransomware Is So Popular
In 2022, nine of the top 20 breaches observed by Arctic Wolf involved ransomware, highlighting how damaging ransomware can be for large organizations. The median ransomware demand for 2022 was $500,000. This number varied by industry, with technology taking the top spot with a median initial ransom ask of $1.2 million.

That kind of money is a major motivator for cybercriminals, and as RaaS becomes more popular, the prospect of that kind of payday is enticing more, often amateur, hackers to launch their own ransomware attacks. From a victim perspective, the digital revolution, the rise of work from home, and the onslaught of social engineering tactics create more, often new, risks for organizations and individual users.
It’s important to note, however, that while larger organizations were attacked and ransomware gangs made themselves known, 2022 did see a statistical drop in the frequency of ransomware attacks. Researchers believe this is due to the ongoing war in Ukraine, and believe that, when the war resolves, many citizens may turn to ransomware and other cybercrime due to limited financial options.
Not only is ransomware now easier to implement, but organizations are also, unfortunately, willing to pay hackers when an attack occurs. Over half of organizations in 2022 paid at least partial ransom. While it’s recommended by the U.S. government that businesses do not engage with cybercriminals, recommendations differ from reality. It’s important to note that a strong incident response partner can help an organization during a ransomware attack, preventing downtime, aiding restoration, and more.
See How Arctic Wolf’s Incident Response Responds to Ransomware
BEC Attacks Keep Increasing
While business email compromise may not get the spotlight that ransomware basks in, this method of social engineering is a favorite among threat actors, and it’s costing organizations millions.
According to an Arctic Wolf survey, BEC attacks were listed as the “top concern” for 38% of respondents, and of the 52% that experienced a breach in the last year, a third stated the attack was BEC related. That’s backed up by Arctic Wolf Lab’s data, where BEC attacks accounted for 29% of incident response cases in 2022.
There are a few reasons this tactic keeps increasing, and a main one is that there are multiple ways to execute it. Credential theft, phishing, or even an external exploit can give a hacker access to email accounts and from there the attack can take many forms, all with the goal of financial exploitation. The most common types are CEO fraud, vendor impersonation, HR data theft, and attorney impersonation. The broad approaches put almost every industry at risk, and in 2022 the median cost of a BEC attack was $79,000, but for money-heavy industry financial services, that median more than doubled to $182,000.
Many BEC attacks take the form of social engineering, and according to Arctic Wolf Labs, 58% of observed impacted organizations did not have multi-factor authentication (MFA) in place. MFA is simple for organizations to implement and is a major proactive step in preventing costly attacks.
MFA, however, is just one of the steps organizations should take to protect themselves from these kinds of breaches.
How to Combat Ransomware and BEC Attacks
A strong cybersecurity strategy is one that is holistic and is both proactive and reactive. When it comes to these two major attack types, both kinds of strategies need to be in place to make sure an organization is fully prepared.
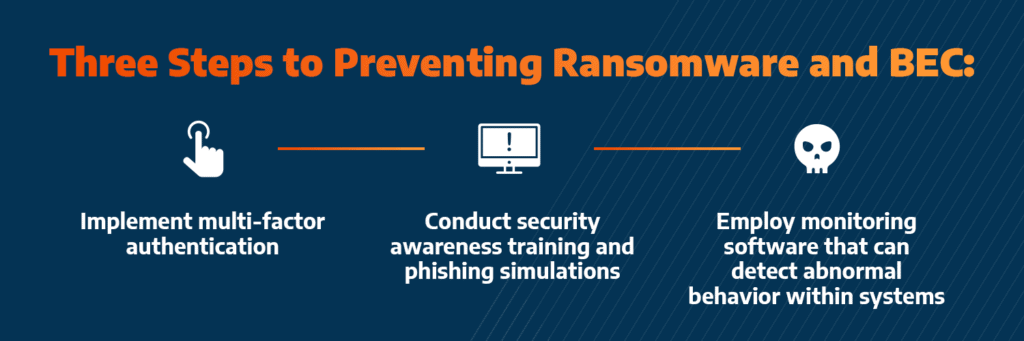
How to Prevent Ransomware and Business Email Compromise
- Implement MFA
- Conduct security awareness training and phishing simulations
- Employ monitoring software that can detect abnormal behavior within systems, such as unusual login attempts or suspicious email activity
How to Respond to a Ransomware or BEC Attack
If the worst-case scenario happens, having a strong incident response partner can make a major difference. Organizations need to act fast and focus on quick restoration, and a partnership can help with exactly that. Arctic Wolf® Incident Response leverages an elastic framework that enables rapid remediation to any cyber emergency at scale. With fast response, complete remediation, and quicker restoration, Arctic Wolf Incident Response is the preferred partner of cyber insurance companies.
- Learn how to craft a robust incident response plan via real-world examples in our on-demand webinar.
- View our business email compromise incident response timeline.