
ARCTIC WOLF
Managed Risk
Reduce Risk, Increase Resilience
Discover
Identify assets in your environment and define your attack surface to gain broader visibility.
Assess
Determine your cyber risk in context of your business.
Harden
Leverage actionable remediation guidance to close vulnerability gaps and continually harden your security posture.
The Arctic Wolf Managed Risk Difference
Benefits:
Unified Visibility
Gain greater insight into your security posture and broader visibility into your attack surface by pairing the detection and response of MDR with the risk-based vulnerability management provided through Managed Risk.
24x7 Monitoring
24x7 monitoring for vulnerabilities, system misconfigurations, and account takeover exposure across your endpoints, networks, and cloud environments. Deliver timely critical outcomes with the deep scan tools.
Up-to-Date Threat Intelligence 3.9
Gain the latest emerging threat intelligence with reliable and actionable information from the security intelligence experts of Arctic Wolf Labs.
Strategic Recommendations
Your named Concierge Security engineer becomes your trusted security advisor, working with you to make recommendations that harden your security posture over time.
Concierge-Led Managed Risk Experience
The Concierge Security Team (CST) is your single point of contact for your Arctic Wolf Managed Risk solution. Your CST intimately learns your environment and then develops a Security Journey based on your security objectives, hardening your security posture and helping to contextualize your environment.
Personalized Engagement
Regular meetings with your named security operations expert let you review your overall security posture and find areas of improvement that are optimized for your environment.

Arctic Wolf Managed Risk Capabilities
Discover the Risks That Traditional Tools Miss
Organizations need comprehensive visibility into attack vectors and sources of risk. In addition to software vulnerabilities, Arctic Wolf Managed Risk addresses corporate credential exposure and system misconfigurations for a more robust view into your digital risk.
Scan internet-facing assets to understand your
company’s digital footprint and quantify your
business’s risk exposure
Arctic Wolf delivers continuous scanning of all your internal IP-connected devices while cataloging your core infrastructure, equipment/peripherals, workstations, Internet of things (IoT) devices,
and personal (e.g., tablets, cell phones) devices.
This capability extends visibility inside devices
through continuous host-based monitoring with Arctic Wolf Agent™ to identify and categorize assets, as well as reveal system misconfigurations, user behaviors, and vulnerabilities that put your organization at risk.
Agent-based security configuration benchmark scans your environment to reveal gaps in system configurations that can drift over time and identify digital risks beyond vulnerability assessment. To help you prioritize your risk mitigation, configuration benchmarking is a risk score based on criteria such as the attack vector accessibility, attack complexity, and the impact of accessed data. These benchmarks provide context so you can address the most critical misconfigurations first.
By continuously scanning the dark and gray web for corporate credentials harvested in data breaches, account takeover detection enables you to quickly take action to secure compromised accounts.
Security Operations Bundles
Arctic Wolf Security Operations Bundles offer a full suite of technology, security expertise, and risk transfer options to end your cyber risk.
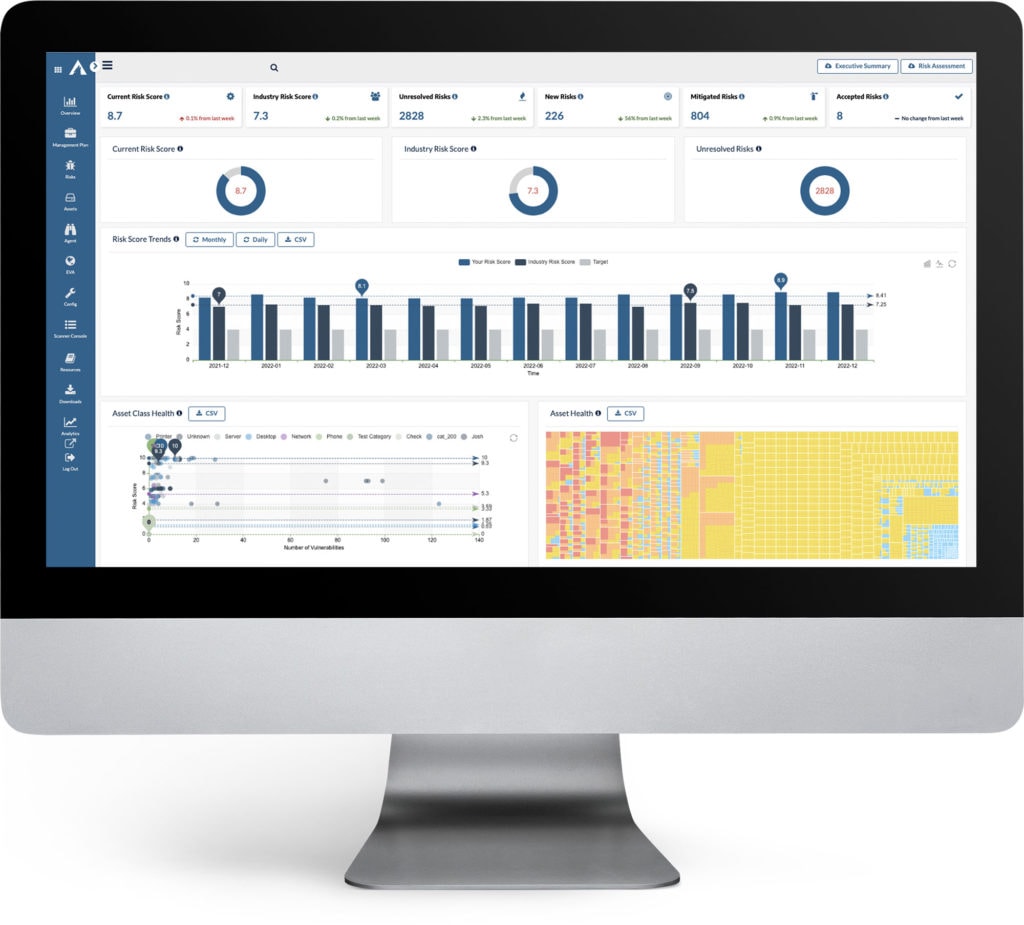
See your current risk score.
See how you are doing against your industry peers.
See your overall trending risk score.
See your overall asset health.
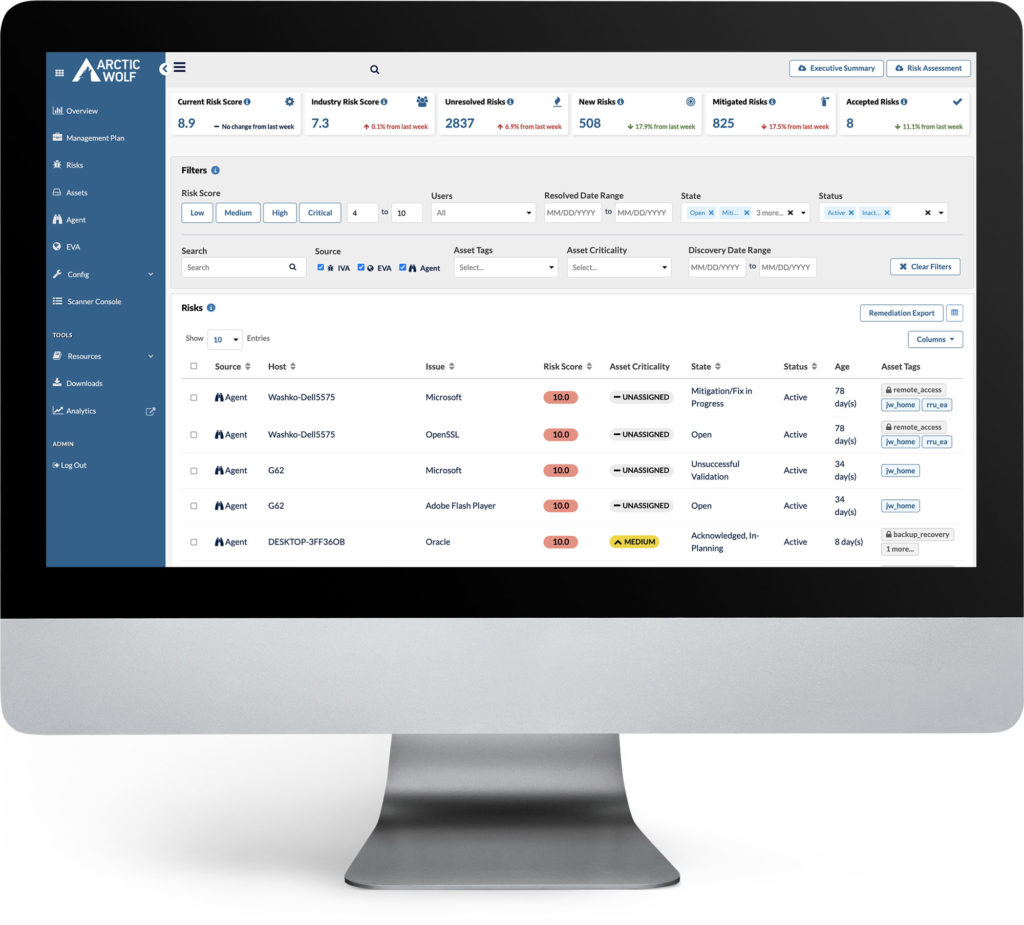
Filter down by the risk score.
Filter by resolved date.
Filter by state including: Open, False Positive, In-Planning, Mitigated and more.
Filter by status - Active; Inactive; Obsolete; Mitigated.
Filter by asset tags that your CST helps you to create.
Filter by asset criticality that your CST helps you assign.
Filter by risk discovery date.
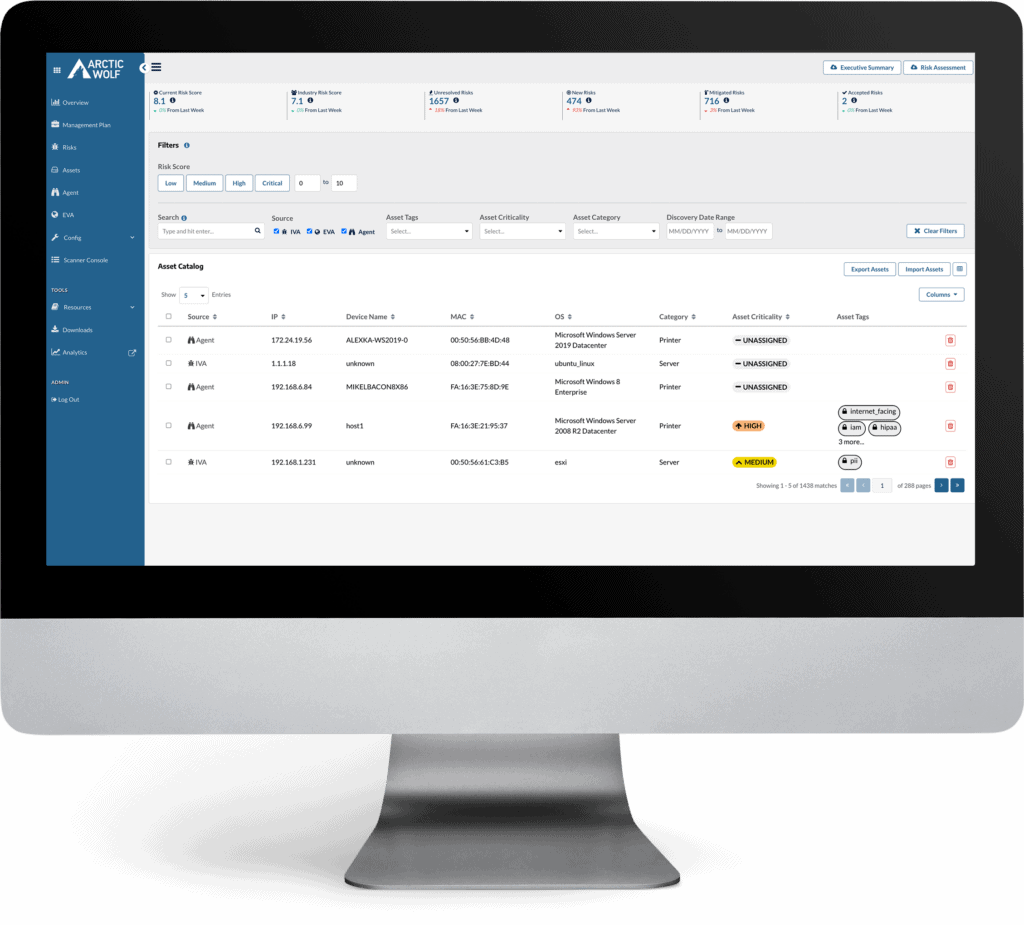
Filter down your assets by risk criticality.
Filter by asset criticality that your CST helps you assign.
Filter by asset category that automatically gets assigned.
Filter by risk discovery date.
See the Managed Risk Dashboard in Action
The Arctic Wolf Managed Risk Dashboard is a cloud-based portal that provides visibility into the real-time risk landscape on your networks, endpoints, and cloud environments. We tailor the dashboard to your organization’s priorities to help you make sense of vulnerabilities, while also managing and prioritizing patching to reduce cyber risk exposure.
A single interface for all things cyber risk:
-
Visibility into your cybersecurity posture, including prioritized threats and your overall cyber risk score
-
Insight into your organization’s risk trends and industry comparisons
-
Operational optimization by giving insight into prioritizing your information security and technology activities
Cloud Security Posture Management Extends Managed Risk to the Cloud
The cloud is the new frontier in business IT—and in cyber risk.
Cloud Security Posture Management (CSPM) provides cloud asset auditing, environment benchmarking, plus posture hardening and remediation guidance.

Security Operations Warranty
Arctic Wolf Security Operations Warranty
Cybersecurity, IT, and risk management leaders need a plan to manage the outcomes of inevitable cyber attacks against their businesses. Through Arctic Wolf Managed Risk, get access to the Arctic Wolf Security Operations Warranty, a no-cost customer benefit that provides up to $3 million (USD) in financial assistance for cybersecurity incidents.


"Arctic Wolf Managed Risk Experience"

"My relationship with Arctic Wolf helps me sleep at night."

"Great product, it's like having a security professional on your team"
WHAT OUR CUSTOMERS SAY
Having a team to assess and manage vulnerabilities while monitoring our environment really helps us reduce our threat surface. We've made considerable progress in rebuilding intregrity and trust in our IT systems, but reisk never goes away and if we aren't aware of it, we can't work to mitigate it.
Dr. Jason A. ThomasCOO and CIO, Jackson Parish Hospital

They’ll alert us when we have vulnerabilities that we need to investigate before things happen. They’ll give us a list to prioritize. ‘These devices are critical, and they’re outdated.’ Arctic Wolf has given us a clearer insight into our environment. We know what’s going on and that allows us to be proactive.
Jeshirl BriceIT Director, City of Monroe

