Arctic Wolf Labs
Threat Report
2023
The most forward-thinking ideas from our elite security researchers
Geopolitical conflicts a world away impact security decisions at home. The rise of AI poses new risks as threat actors adopt this powerful new tool to conduct cyber attacks. Root points of compromise spark lingering vulnerabilities, and business email compromise attacks climb. Organizations need all the advice and insights they can get to fight back against this shifting threat landscape.
Now, for the first time, you can gain access to the intelligence and insights developed by Arctic Wolf Labs over the past year as we ingested trillions of weekly observations within thousands of unique environments, engaged sophisticated adversaries, and built new safeguards in our mission to end cyber risk for customers around the world.


10 Cybersecurity Predictions for 2023
2023 will see another rise in the volume and complexity of cyber attacks. The time is now to understand the full scope of your organization’s risk and take proactive steps to secure your environment against these ten significant shifts in the threat landscape:
01
Geopolitical instability and economic stress will drive cybercrime increases
02
AI-driven information warfare and cybercrime will increase

Rising Risk
2022 brought about a rise in attacks that require less technical proficiency but can still deal a damaging blow. Ransomware-as-a-service (RaaS) has allowed inexperienced cybercriminals to launch effective ransomware attacks. Business email compromise attacks, a long-standing social engineering staple, soared last year, affording cybercriminals a reliable payday. And publicly known vulnerabilities remained a common method for threat actors to launch an attack, as the security talent shortage led to CVEs going unaddressed and unpatched.
The previous year served as a harsh reminder that no amount of tools and no advancement in technology can prevent user error. Organizations need to make credential hygiene and security awareness training top priorities.
Business Email Compromise
Business email compromise accounted for over a quarter (29%) of incident response cases last year.
Ransomware-as-a-service (RaaS)
The median initial ransom demand across all industries was $500,000 USD.
Publicly Known Vulnerabilities
45% of incidents were caused by vulnerabilities that could have been mitigated through available security patches and updates.
Root point of Compromise
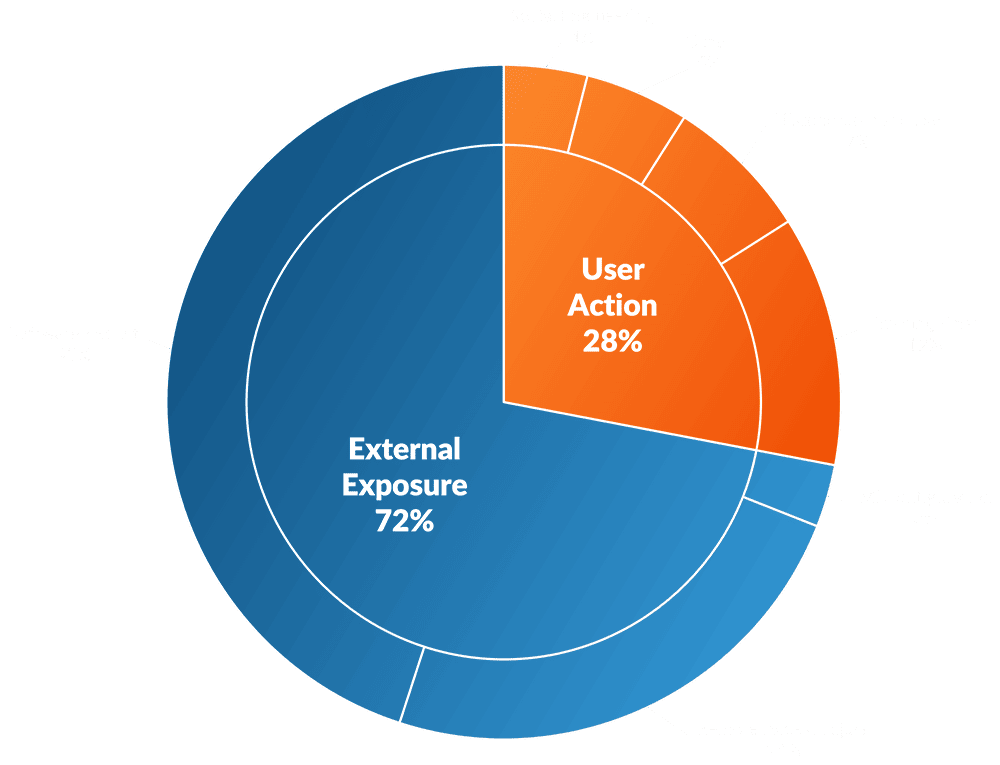
External Exposure Trumps User Action
Arctic Wolf Labs has determined that a handful of attack vectors and vulnerabilities were responsible for a significant portion of incidents responded to by Arctic Wolf Incident Response over the last 12 months.* Of the top five vulnerabilities leveraged by threat actors in 2022, four of them were published in 2021. This is noteworthy because human error is often held up as the most vulnerable part of a security environment, while our data shows that external actions from unpatched vulnerabilities is an even greater threat.
*Chart intentionally excludes business email compromise incidents
"With broader public access to AI, we expect to see more bots and automation spread disinformation across the web. We expect to see AI-generated imagery and videos used by threat actors to spread propaganda, influence public opinion, and launch advanced social engineering campaigns."
- - - - - - 2023 Arctic Wolf Labs Threat Report
Our Recommendations
How to Build a Stronger Security Posture
Cybercriminals continue to evolve their attack techniques. The attack surface continues to expand. The rush to adopt new technologies continues to open organizations up to new risks. But that doesn’t mean you’re on your own. There are many proactive ways to harden your security posture and better protect your data. Arctic Wolf Labs have identified these six as having the most impact:
"We believe sharing intelligence and insights like those in this report is a critical responsibility for those of us in the cybersecurity industry and is vital in helping organizations of all types end cyber risk."
- - - - - - 2023 Arctic Wolf Labs Threat ReportOn-Demand Webinar
Arctic Wolf Labs Presents:
2023 Predictions and 2022 Threat Landscape
AIR DATE: Thursday, March 16, 2023
Join Arctic Wolf Labs Product Marketing Manager Sule Tatar and Adrian Korn, Sr. Manager, Threat Intelligence Research at Arctic Wolf Labs, for a deep dive into the pages of this exclusive report. You’ll gain access to the intelligence and insights we developed as we ingested trillions of weekly observations within thousands of unique environments, engaged sophisticated adversaries, and built new safeguards to end cyber risk for customers around the world.
You’ll discover:
- The most common root point of compromise utilized by threat actors, and where you need to place organizational priorities
- How disruptive technologies like cryptocurrency and augmented reality will introduce new possibilities and risks to the threat landscape
- The most notable emerging threat actor tactics, techniques, and procedures (TTPs) and what you can do to thwart them
REPORT AVAILABLE!
Arctic Wolf Labs Threat Report 2023
With the Arctic Wolf Labs Threat Report 2023 you can gain access to the intelligence and insights developed by Arctic Wolf Labs over the past year as we ingested trillions of weekly observations within thousands of unique environments, engaged sophisticated adversaries, and built new safeguards in our mission to end cyber risk for customers around the world.
Get the most forward-thinking ideas from our elite security researchers.
As one of the largest security operations centers in the world, our insights into recent trends will help you cut through the noise, understand the current and potential threats to your organization, and keep your focus on delivering the critical tasks that protect your organization 24×7.
Simply fill out the form below to get instant access to your personal copy of the 2023 Arctic Wolf Labs Threat Report, featuring our predictions and recommendations for 2023, and our industry-leading insights into the current threat landscape.