As cybercrime evolves, one avenue for attack has risen to prominence across the world: Ransomware.
According to Arctic Wolf’s State of Cybersecurity 2023 Trends Report, 48% of organizations view ransomware as the top attack vector concern. A concern comes with just cause, as the Arctic Wolf Labs 2024 Threats Report showed 48.6% of incidents investigated by Arctic Wolf were ransomware attacks.
In addition, the cost of ransomware has steadily increased, with IBM’s 2023 Cost of a Data Breach stating, “at USD 5.13 million, the average cost of a ransomware attack in the 2023 report increased 13% from the average cost of USD 4.54 million in the 2022 report.” The amounts cybercriminals are trying to extort is following a similar pattern. The 2024 Arctic Wolf Labs Threat Report showed the median ransom increased 20% over last year to $600,000 USD.
Ransomware can take many forms, and while each attack is different, it’s becoming the go-to attack vector for cybercriminals. So, it’s critical that organizations understand these attacks and learn how to defend against this growing threat.
How Ransomware Attacks Have Evolved
Ransomware was first documented in 1989, but it wasn’t until the 2010s and the simultaneous rise of cryptocurrency, remote applications, and cloud-based networks that the attack -type really took hold among cybercriminals. Since then, the illegal industry has exploded, with innovations like ransomware gangs, ransomware-as-a-service (RaaS), more complex strains, data exfiltration, and leak sites taking hold.
Two common techniques that have evolved as ransomware expands are double and triple extortion . In a double extortion use case, the threat actor will exfiltrate data from the system and threaten to release it if the ransom is not paid. In a triple-extortion scenario, the threat actor will do the above, and, in addition, contact individuals whose data may have been compromised, asking them for payment under threat of data release, or threatening the ransomed organization with a second kind of attack. These tactics can allow for multiple payouts from a single attack.
While ransomware groups, and the strains they use, appear to always be shuffling and changing, there are a few broader trends that hold.
Common types of ransomware, seen repeatedly, include:
1. Crypto ransomware. This is the most common ransomware seen today, where systems, assets, or applications are encrypted, and can only be unlocked once a ransom is paid.
2. Lockers. Lockers work by locking users out of a system completely, instead of encrypting individual parts of the system. Often, a lock screen will appear on the endpoints with a ransom note attached.
3. Scareware. Scareware operates like a scam, telling users that a virus is on the endpoint, and they must pay to resolve the problem. This kind of ransomware more often targets individuals rather than organizations.
4. Dox or Leakware. Leakware distributes exfiltrated data onto the dark web. This has become a more common tactic in recent years, often employed by ransomware gangs, as stolen credentials can assist in future attacks and personal data can often sell for a hefty price.
5. Ransomware-as-a-service (RaaS). In this ransomware distribution system, valid credentials, encryption software, leak sites, or other initial access methods are sold to another group to launch an attack in return for a cut of the ransom.
Ransomware has also seen a steady increase of ransomware gangs — groups of cybercriminals who band together to launch a signature ransomware strain and attack multiple organizations. Some, but not all, of these groups operate under the ransomware-as-a-service model.
The five groups Arctic Wolf® Incident Response encountered the most in 2023 were:
- BlackCat
- LockBit 3.0
- Akira
- Royal
- BlackBasta
The Rise of Ransomware-as-a-Service
While all five of those methods have risen in popularity as ransomware and cybercrime have evolved, it’s RaaS that has truly changed the hacking game.
RaaS participants offer resources such as encryption software, leak sites, and branding to independent affiliates who then carry out the ransomware attack. The proceeds of RaaS attacks are commonly split between affiliates and the operators, but some organizations employ cybercriminals long term, so they may get a flat fee, a percentage cut, or a payment akin to a salary. The easiest way to think of it is as the cybercrime version of the technology industry’s software-as-a-service (SaaS) model.
While in the past, ransomware was conducted primarily by highly skilled threat actors, this model has opened the playing field by dividing responsibilities. It allows less technical cybercriminals to execute attacks while also shielding the identities of the individuals involved.
In addition, RaaS has helped ransomware gangs dominate the landscape.
Example of a Ransomware Attack
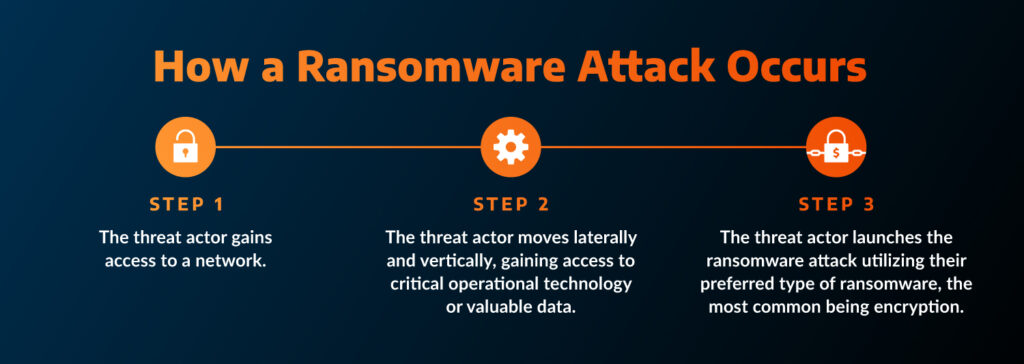
The best way to understand ransomware is to look at an attack’s three main stages.
Stage 1: The threat actor gains access to a network.
This could happen through social engineering, through a vulnerability exploit, through malware, or another method, but access is always the first step.
By far, external exposure is the top initial access point for threat actors, making up 70.1% of Arctic Wolf Incident Response cases in 2023. Following that was user action at 24.4%.
Stage 2: The threat actor moves laterally and vertically, gaining access to critical operational technology or valuable data.
These movements could include gaining privileged access, exploiting a vulnerability in Active Directory, launching a spear-phishing campaign, or deploying malware.
The access granted could include digital operational technology and IT technology, or the personal identifying information (PII) contained within healthcare systems, as is common with the currently active Royal ransomware gang.
Stage 3: The threat actor launches the ransomware attack utilizing one of the forms mentioned above — the most common being encryption.
The threat actor, or ransomware group, is banking on the fact that the organization’s data is so valuable, or the downtime is so damaging, that they will pay, and fast. This was the case when MGM was hacked in the summer of 2023. The Las Vegas hotel had to pay $10 million to recover from the ransomware incident and lost about $100 million in bookings.
Ransomware In Action: The MCNA Dental Data Breach
In May of 2023, the public was notified that MCNA Dental, a United States dental insurance company, had been the victim of a ransomware attack by the group LockBit.
Known for attacking critical infrastructure and healthcare groups, LockBit is quickly becoming one of the most prolific ransomware groups. While the initial access technique has not been disclosed, LockBIt claimed they were in MCNA’s system for ten days without detection, and used that time to exfiltrate 700GB of data, including personal identifying information (PII) of MCNA’s clients, with a ransom set at $10 million USD.
LockBit ultimately published the exfiltrated data on the dark web, which contained PII for 8.9 million individuals.
This attack highlights not only how ransomware groups have evolved to evade detection, but how they are targeting large organizations rich in data, and are not afraid to exfiltrate, extort, and ultimately leak the data on the dark web — or even sell the data to another cybercriminal.
How To Stop a Ransomware Attack
A ransomware attack doesn’t have to end with an organization paying millions and dealing with the fallout of compromised data. As much as cybercrime has been evolving, so has cybersecurity, and through research and analysis, we know there are a few tactics that can prevent a threat from turning into a full ransomware attack.
1. Conduct file backups
It’s best to follow the 3-2-1 principle of file backup, meaning an organization has 3 copies of data (1 primary and 2 backup), 2 copies stored (at separate locations), and 1 off-site storage (ideally in a secure private cloud)
2. Secure your cloud environment
A security incident originating from within your organization that destroys or disrupts your cloud data is your responsibility, and many cloud security incidents can be traced back to misconfigurations and/or overly permissive access policies. With the shared responsibility model, it’s important for your organization to understand your role so security gaps don’t appear that you presume are covered by the provider.
3. Enforce identity and access controls
Credential security is paramount for preventing ransomware attacks. These security measures include implementing multi-factor authentication (MFA), monitoring the dark web for credential leaks, hardening active directory, implementing a zero-trust framework, and reducing human risk through security awareness training.
4. Create a vulnerability management program
The majority of ransomware attacks originate with external exposure, and not from zero-day exploits. By regularly identifying, prioritizing, and patching known vulnerabilities, your organization can harden its exterior and limit the attack surface.
5. Employ a 24×7 monitoring, detection, and response solution
Early detection is critical for stopping a ransomware attack. By identifying signs of a potential ransomware attack — from unusual logins to rule changes in an application — your organization can act and stop incidents before they escalate.
Where MDR stops and IR Begins
There are two major solutions involved in the prevention and response to ransomware — managed detection and response (MDR) and incident response (IR). But the two aren’t interchangeable, and one cannot replace the other.
MDR helps your organization prevent threats from turning into incidents and can offer not only 24×7 monitoring across your environment, but hands-on-keyboards to swiftly respond to threats and shut them down before lateral movement or escalation occurs. In action, this could look like the solution noticing an unusual login at 3 a.m. and then isolating the endpoint it’s attached to and notifying your organization to the action.
Learn more about Arctic Wolf® Managed Detection and Response.
IR is needed when a threat has turned into an incident such as a ransomware attack. An IR provider will help your organization stop the attack and restore operations. Just like MDR, not all IR providers are built the same, so it’s important to work with one who is approved by your cyber insurance policy, and in the case of ransomware, has threat actor negotiation and other ransomware specific expertise. Exploring IR retainers is a good way to not only build familiarity with an IR provider, but help your organization do proactive IR work and stay prepared in case the worst happens.
Learn more about Arctic Wolf® Incident Response.
Explore how a security operations solution can reduce risk will help your organization’s budget.
See what Arctic Wolf Labs predicts for the cybercrime landscape in 2024 — and how you can prepare your organization for what’s ahead.






