AI in cybersecurity is hard.
We make it easy.
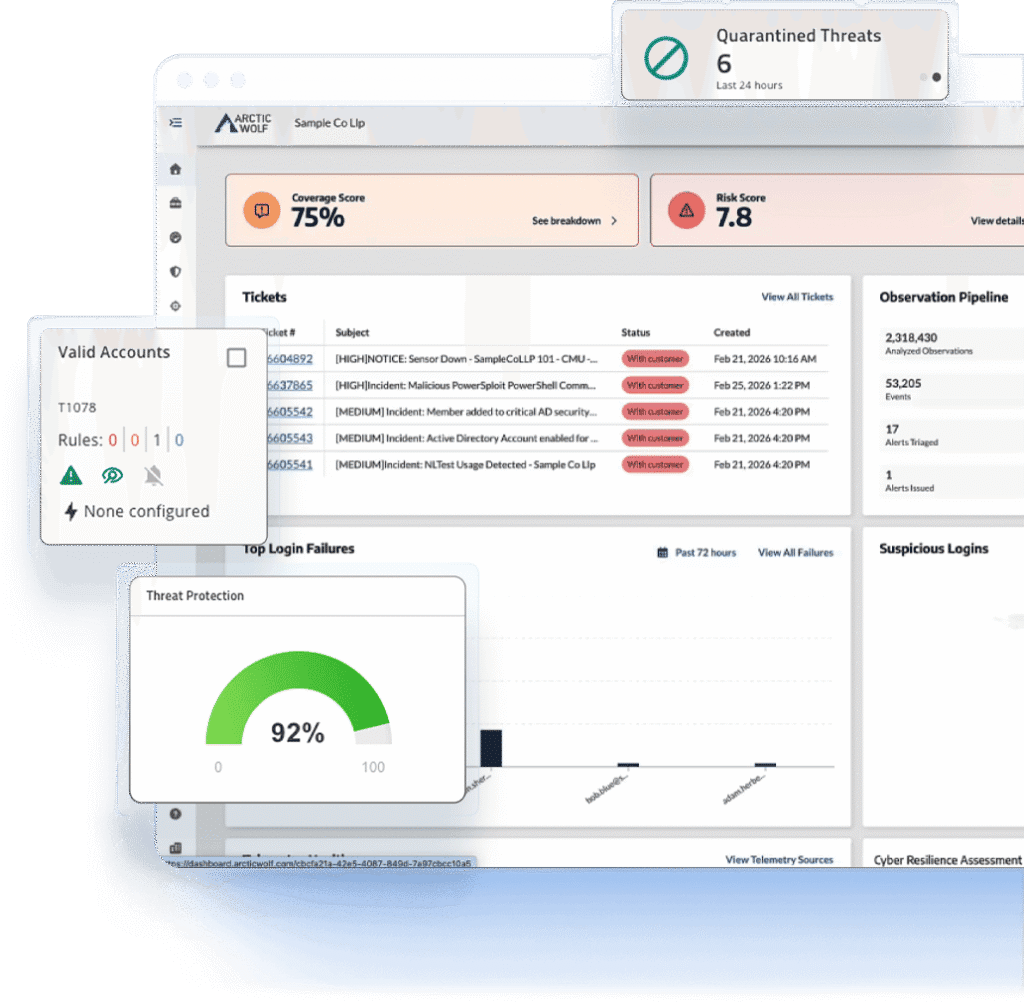
A fully managed agentic SOC is just a click away. It really can be that simple.













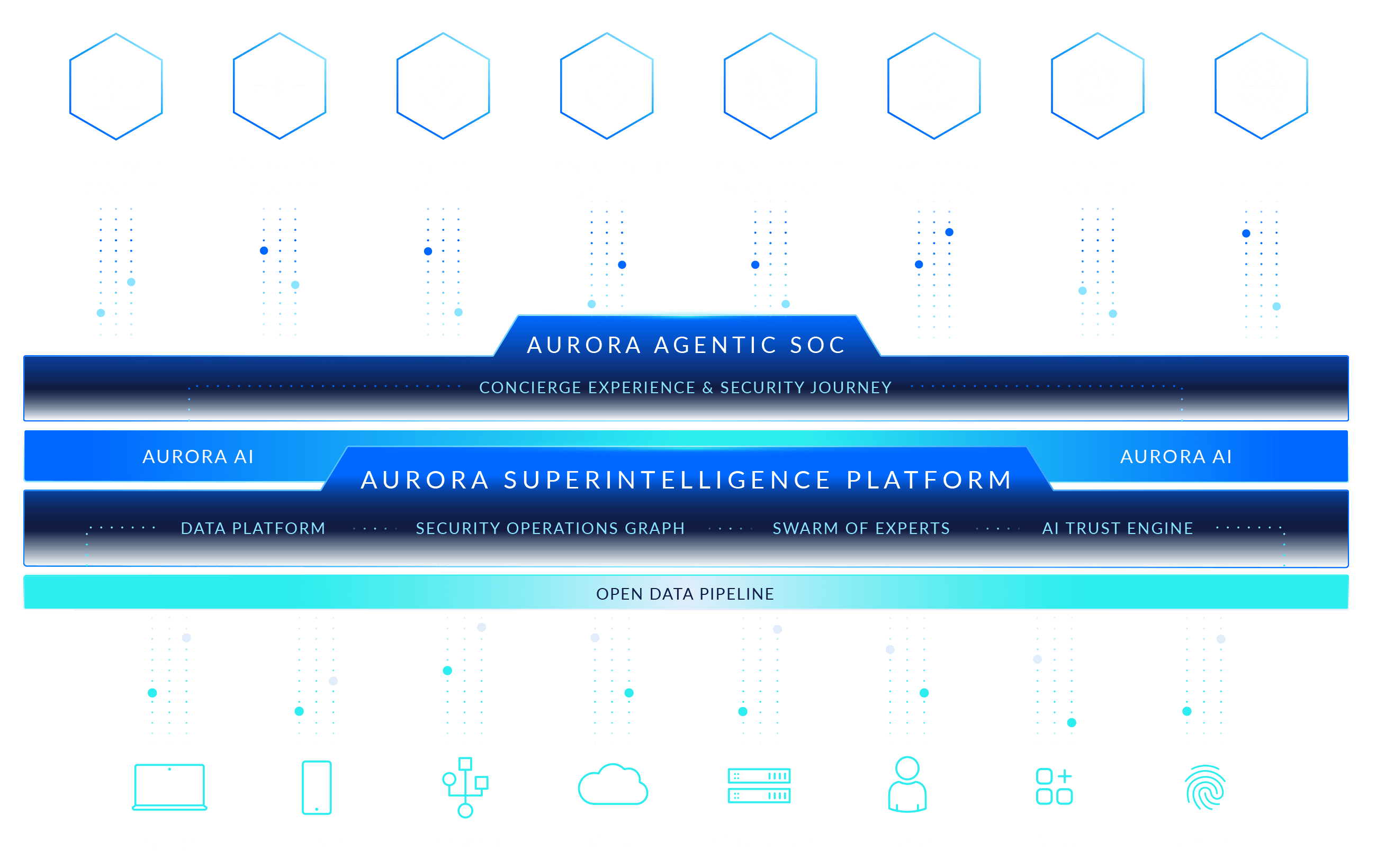
The Arctic Wolf Aurora® Superintelligence Platform
Bringing the transformational power of superintelligence to any organization. Because in a world where attacks move at machine speed, your cybersecurity should too.
Security Teams Are at Their Breaking Point
The AI Inflection Point
Adversaries are using AI to move faster and scale attacks in ways that legacy defenses can’t match. Meanwhile, many security teams are still searching for AI capabilities that actually deliver reliable, trustworthy outcomes.
The opportunity lies in AI built to transform cybersecurity, but fewer than 5 percent of security teams have agentic capabilities today. Bringing the benefits of agentic AI to every organization requires a superintelligent platform purpose-built for security operations.
Security Budgets Are Under Pressure
Teams are already stretched thin, and security leaders are being asked to deliver an agentic AI strategy without the time, training, or funding to build one from scratch.
Security teams need a partner that can remove the operational overhead of running an agentic SOC and demonstrate real, immediate impact and ROI for their organization.
Stalled Progress
Security teams are overwhelmed and under water, so they cannot advance on their Security Journey.
Being trapped in reactive, ad-hoc work means teams simply don’t have time to focus on critical proactive measures like incident response retainers and incident readiness. They struggle to understand and demonstrate if their overall security posture is getting better or worse, which prevents them from unlocking risk transfer benefits like cyber insurance or warranties.
Explore Arctic Wolf Incident 360, a first-of-its-kind incident response retainer. Learn More
Explore the Arctic Wolf Security Operations Warranty, with up to $3 million (USD) in financial coverage. Learn More
Work with Arctic Wolf to implement the necessary controls to qualify for, maintain, and optimize cyber insurance. Learn More
AI that Works the Way Security Demands
Designed for Trust
The AI Trust Engine built into the Aurora Superintelligence Platform provides the oversight, validation, and guardrails to ensure safe, trustworthy AI outcomes.
Built In, Not Bolted On
AI agents are delivered as features of the platform, eliminating the requirement for the customer to build, maintain, and govern the agents. This approach delivers immediate time to value and unbeatable return on investment.
Humans in the Loop
It has been said that there will never be a fully agentic SOC, and we couldn’t agree more. Agents are an incredible force multiplier that enable the SOC to operate at machine speed, but the nuance of the cybersecurity domain demands that humans remain in the loop for oversight, adaptation, and ongoing reinforcement learning.
Bringing the Security Ecosystem Together
Arctic Wolf works with the technologies and partners organizations already rely on. With 250+ integrations, 20+ alliance partnerships, and the backing of 2,700+ MSP and channel partners, the Aurora Superintelligence Platform helps security teams connect data, preserve choice, and move faster with AI-led security operations.
Integrations
MSP & CHANNEL PARTNERS
ALLIANCE PARTNERS

“Arctic Wolf’s unparalleled expertise and cutting-edge Aurora Platform will provide us with the confidence and protection necessary to safeguard our operations at every level, ensuring we can dedicate our full attention and energy to what matters most: winning races.”
Joshua David