Having some form of a security operations center (SOC) to protect and secure your assets, applications, and infrastructure is no longer optional. As cyber criminals grow more sophisticated and modern complexities (remote work, the cloud, international operations) expand the attack surface, a SOC becomes a critical line of defense. It works proactively and reactively and can help an organization advance their security posture while dealing with immediate threats.
Considering that the average data breach takes 277 days to contain (according to IBM), lowering that timeline – which can be achieved with an effective SOC – lowers overall cost and impact, meaning a SOC becomes a highly valuable component to any environment.
However, while an effective SOC is an important element of a cybersecurity structure, it’s not easy for organizations to spend time, money, and employee resources on one. SOCs, if built in-house, can be costly, complicated to maintain, and require expertise that isn’t easy to come by, especially for less mature organizations.
Every business has unique needs that evolve over time, so how much an organization should budget for a SOC depends on the size of the attack surface and the level of protection it expects the SOC to deliver. A small business with a few hundred users in one office will naturally have different requirements than a multinational enterprise with hundreds of thousands of employees spread around the world. There’s also the question of whether an organization should build a SOC fully in-house, pay a third party to manage an internal SOC, or export the entire process.
To implement a SOC that will be both cost- effective and operationally effective, you first need to understand the factors that impact costs and the level of SOC you wish to achieve.
The Different Types of SOCs Organizations Use
There is no shortage of SOC vendors, SOC-as-a-service (SOCaaS) providers, and new tools across the cybersecurity market, all of which purport to be the solution that will stop attacks. While there is plenty of promise and fancy marketing across the cybersecurity ecosystem, all SOCs come down to just three models.
According to Gartner, these SOC models are:
1. Internal SOCs. An internal SOC contains full-time, dedicated analysts who provide 24×7 centralized threat detection and response in a self-contained setting. While additional services may be outsourced, the core security functions operate in-house and under organizational control. This kind of SOC is commonly employed by large enterprises who have complex internal security needs and the budget and staff to meet those needs.
2. Tiered SOCs. Tiered SOCs rely on the oversight of a single “command” or “parent” SOC, in which most tools and analysts work, that synchronizes with the other independent, satellite SOCs. This model is often employed by vast enterprises with a national or international footprint, as it allows them to monitor multiple “satellite” environments simultaneously.
3. Hybrid SOC. A hybrid SOC uses the partnership of third-party managed service or solutions providers for maintenance and day-to-day management. This is an ideal model for small and midsize enterprises (SMEs), as it allows for threat monitoring, detection, and response at a reduced cost – often through a subscription model.
Explore different SOC models in-depth.
When it comes to building a SOC, the National Institute of Science and Technology (NIST) has a cybersecurity framework that every organization should follow.
The functions of an effective SOC include:
- Identification
- Protection
- Detection
- Response
- Recovery
- Govern
Each of these functions has specific traits associated with them, and you can learn more about the framework with our Security Operations Maturity Assessment.
Why an Organization Needs a SOC
As mentioned above, combining technology and the human element into a sophisticated command center is critical in the modern cybersecurity age. The benefits of utilizing a SOC, be it in-house or outsourced, include:
- Improved efficiency. An effective security operations team functions like a well-oiled machine.
- Optimization of existing security technology. Security operations analyzes the telemetry from the organization’s existing security solutions, allowing them to optimize the value an organization realizes from these investments.
- Continuous improvement. Security operations looks at the big picture to derive strategic insights that can improve an organization’s overall security posture.
- Security assurance. Organizations can focus on other goals knowing their security is in the right hands and ready for whatever threats emerge.
- Knowledge. You can’t protect what you don’t know, and security operations offer thorough knowledge of both assets, vulnerabilities, and the attack surface.
- Broad visibility. When organizations rely on a multitude of applications, end points, and cloud environments. Gaining visibility across the vast security environment can be difficult, leading to blind spots and missed threats. SOCs solve that.
- Better threat intelligence. Back to the knowledge component, SOCs can gather threat intelligence, allowing an organization to better prepare for, and thwart attacks.
- Vulnerability management. SOCs can help organizations implement a strong vulnerability management strategy to help prevent attacks before they occur by eliminating the weaknesses attackers can exploit to gain a foothold in the environment.
The important thing to remember is that each of the benefits does not stand alone. They all work in parallel to help an organization not only react to immediate threats, but continually improve their security posture as their business and security needs develop. Many SOCs create a single pane of glass, allowing organizations to not only respond to alerts, but to track behavior across sources, see how different parts of the environment are affecting each other, and more accurately assess their attack surface and overall cyber risk.
What to Consider When Building a SOC
Before discussing budget, there are a few logistical considerations an organization needs to make when it comes to building a SOC.
1. People
A SOC can’t run effectively without cybersecurity experts taking the lead. Unfortunately, in the current climate, these experts can be difficult to find. According to a recent survey conducted by Arctic Wolf, 41% of organizations listed “talent shortages” as their top concern for 2023.
In addition, layoffs have hit enterprises hard, with 62% of organizations having to reduce staff in 2022. Staff instability often means that institutional knowledge leaves when employees do, creating more risk.
People are the most important part of a SOC, as they take the data presented and make decisions on how to respond and what to prioritize in order to keep an organization protected in both the short and long term.
2. Infrastructure
A SOC not only needs security experts, but it also requires the right security tools in place to maximize their capabilities. Significant software and hardware infrastructure investments must be made to ensure your business achieves an optimal security posture.
As each new tool is added, it takes your staff time to implement and learn the software, which is time not spent looking for current threats. Not to mention that while technology is important, it can also lead to alert fatigue which can overwhelm an already strained staff and cause organizations to miss critical threats.
3. Time
Standing up an internal SOC can take months or even years to hire staff, buy security hardware and software, and then implement it throughout the enterprise. Depending on where you are in your SOC journey, you may have to spend more than you would otherwise to cover up gaps and take baby steps on your security journey.
In addition, a SOC cannot run on its own. The time it takes to sift through alerts, prioritize threats, and act adds up. It’s necessary time, but it’s not a quick process, especially for an organization that may be struggling with talent and budget.
The Challenges of Building an In-house SOC
As shown above, each consideration that comes with an in-house SOC has pros and cons, and while building in internal SOC from the ground up may be an organization’s first thought, for many, including SMB’s, it will come with some challenges, especially if the security needs are robust and the risks are plentiful.
Those challenges include:
- Budget constraints
- Desire and effort
- Time investment
- Managing evolving threats
- A skills shortage and gap
- Alert fatigue
- False positives
- Changes in the environment that will create needed changes for the SOC
It’s a lot to consider, and that’s before we even get to the price tag.
How Much Does a SOC Cost?
Depending on your current maturity and desired SOC end state, the cost of building a SOC can vary wildly. If you assume the average security analyst costs $90,000 a year, a fully staffed, 24×7 team could easily cost more than $1 million a year at a minimum. Factor in the cost of the software, hardware, and training they need to effectively do their job and you’re looking at anywhere from $2 million to $7 million annually.
Of course, these numbers don’t factor in the months or years it will take to fully build out the function, which will leave you exposed to threats while your IT team is distracted from other valuable initiatives.
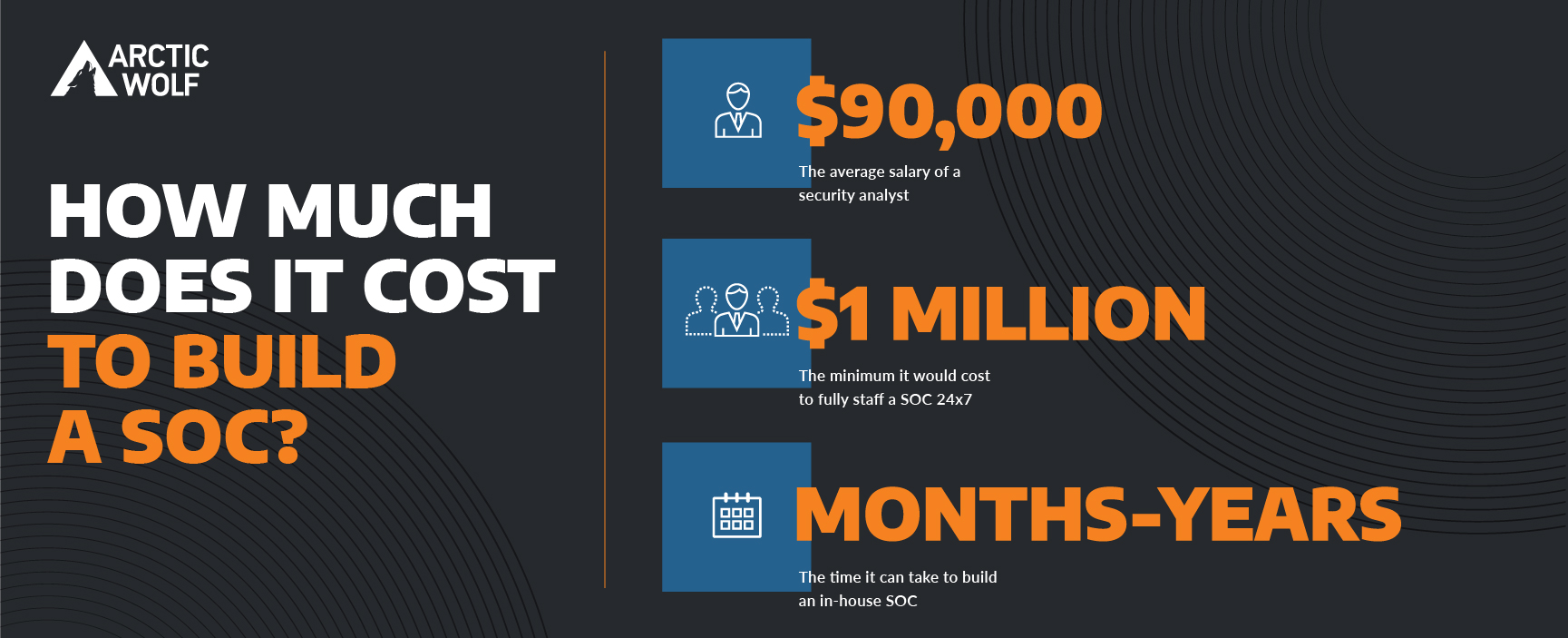
As mentioned above, the cost of a SOC is determined by the people, the infrastructure desired, and the time it takes to build and maintain the SOC.
When mapping out the cost, there are five core components an organization should consider:
- SOC staffing
- SIEM and professional services
- Cloud monitoring
- External threat intelligence
- Vulnerability scanning
We recommend utilizing our Security Operations Calculator to better understand what your organization needs and how building a SOC will impact your budget and security goals.
Should your organization build an in-house SOC? There’s no right or wrong answer to this question. Large enterprises may benefit greatly from the control a SOC gives them, even if it means taking bites of the budget. For an SMB who’s more focused on growing business, a SOC may take too much time and resources away from business operations. It all depends.
However, there is a clear trend where organizations are moving toward managed SOC models, as new platforms and tooling offer more expertise, detection, and response, as well as other capabilities that can be difficult to replicate internally. This is why Gartner® estimates that, “By 2025, 33% of organizations that currently have internal security functions will attempt and fail to build an effective internal SOC due to resource constraints, such as lack of budget, expertise and staffing.” And why, according to Arctic Wolf, 87% of environments are currently using two or more unique endpoint vendor solutions to monitor, detect, and respond to threats within their environment.
How Arctic Wolf Can Help
An MDR solution built on open-XDR architecture is rooted to the endpoint and will use the combination of technology and humans to detect and respond to threats, often by identifying the root cause and submitting automated workflow recommendations. By utilizing this kind of solution, an organization can free up their security teams to focus on what they want out of either their own SOC or internal security tools, knowing their previous blind spots and threat detection gaps are now covered.
Arctic Wolf is exactly that, and then some. Offering 24×7 coverage with broad visibility and rapid detection and response, our leading-edge platform helps your organization reduce cyber risk, increase your security posture, and harden your attack surface, without having to invest in staff, resources, and new internal technology.
Learn more about security operations with our comprehensive guide.
Read our white paper to understand how security operations models, like Arctic Wolf® Managed Detection and Response, can increase an organization’s security maturity.
And in our on-demand webinar, learn 8 Ways SMBs Can Grow Their Cybersecurity Program.