To compete in an increasingly cutthroat marketplace, retailers spend vast sums in hopes of becoming household names. But brand recognition is a double-edged sword when it comes to cybersecurity. The bigger your name, the bigger the cyber target on your back (no pun intended for the number one breach on our list).
Retailers face growing cybersecurity risks. And unlike breaches to businesses in other sectors of the economy that operate in relative obscurity, when a breach involves a major retailer, it often becomes front-page news, since far more people are aware of the company and may, in fact, be devoted customers.
Phishing, ransomware, advanced persistent threats, and supply chain attacks continue to climb in the retail industry, while cybercriminal innovations are uncovering new ways to exploit vulnerabilities in retail POS systems, IoT devices, endpoints, and cloud and server environments.
Meanwhile, the retail industry faces additional “people” challenges, with high turnover and a large contingent of seasonal workers, meaning proactive cybersecurity can too easily slip down the list of priorities. And that’s a dangerous path to walk for an industry so firmly in threat actors’ crosshairs.
According to Verizon’s 2022 Data Breach Investigations Report, 98% of the 629 incidents in the retail sector involved a financial motive. Unsurprisingly, many of those involved payment data, and personal data was compromised in one out of every four attacks. Cybercriminals also focused their attention on credentials, with 45% of incidents involving such data.
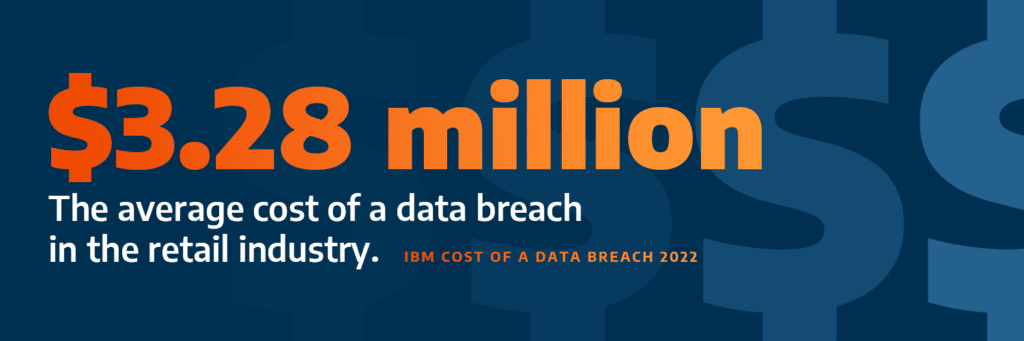
At a time when the average cost of a data breach in the retail industry is $3.28 million, retailers have to make cybersecurity a priority. But that can prove nearly impossible when 63% of retail organizations report a high turnover of security staff.
A separate report from IBM reveals that retail cyber attack victims experienced extortion in 50% of attacks and credential harvesting in 25% of attacks. These tactics can cripple retail organizations by erasing profits and damaging reputations past the point of recovery.
So, attacks are rising, trained security professionals are tough to find and retain, and costs are climbing. What’s a retail organization to do? First step: learn from the others’ mistakes. Here’s a look at 10 major retail cyber attacks which underscore the depth and severity of the threat facing the sector.
10 of the Biggest Cyber Attacks Against Retailers
10. Forever 21
Over the course of seven months in 2018, attackers accessed payment card data of an unknown number of Forever 21 customers. After obtaining network access, the threat actors deployed malware to gather credit card data from the fashion retailer’s point-of-sale (POS) system. Forever 21 admitted to not previously encrypting some of its POS devices.
Cyber attack type: Malware targeting POS systems
Location: Los Angeles, CA
Cost: Undisclosed
Number of people affected: Undisclosed
Far from a shining example of transparency, it’s still unclear how many customers were impacted five years post-breach. Ultimately, the company settled a class-action lawsuit and agreed to pay claims for “valid out-of-pocket expenses and charges that were incurred and plausibly arose” from the incident. But that total cost was also not revealed.
9. Bonobos
Retail organizations don’t only need to worry about the security of their own environments. They also must concern themselves with the security of their network of third-party vendors and suppliers. This has become even more urgent as cloud adoption grows.
Case in point? In January 2021, a 70-gigabyte SQL backup file belonging to Bonobos, the apparel subsidiary of Walmart, was stolen from a third-party cloud provider and posted in a hacker forum. The file contained 7 million shipping addresses, 1.8 million registered customer accounts, and 3.5 million partial credit card records.
Cyber attack type: Attack against third-party cloud provider
Location: Not disclosed
Cost: Not disclosed
Number of people affected: 7 million
Bonobos turned off access points, forced customer password resets, and notified customers whose information was exposed in the attack.
These steps may have spared customers from worse outcomes and also helped shore up their reputation by taking swift action and providing ample notification. This might help explain why, in early 2022, a U.S. district judge dismissed a class-action lawsuit against the company pertaining to the breach.
8. JD Sports
In January of 2023, threat actors made off with the personal information of 10 million customers of fashion retailer JD Sports. Cybercriminals gained access to a database of purchases made between 2018 and 2020 and made off with the “full name, delivery and billing address(es), email address, phone number, final 4 digits of payment card and/or order details,” according to an email sent by JD Sports Group.
Cyber attack type: Undisclosed
Location: Los Angeles, CA
Cost: Undisclosed
Number of people affected: 10 million
The breach raised serious questions about JD Sports’ data management policies, as this database contained millions of records from transactions going back as much as four years.
7. Under Armour
Usernames, email addresses, and hashed passwords for approximately 150 million users of Under Armour’s MyFitnessPass were compromised when an unauthorized third party accessed the data in February 2018. Making matters worse, the company didn’t discover the breach until the following month.
Cyber attack type: Undisclosed
Location: New York, NY
Cost: Undisclosed
Number of people affected: 150 million
The sports equipment and apparel company disclosed that while most of the passwords were protected with “brcypt,” some of the stolen passwords were hashed using SHA-1.
6. Saks Fifth Avenue / Lord & Taylor
A 2018 malware attack against these Hudson Bay Corporation retailers’ POS resulted in the theft of more than five million credit and debit card numbers. The attackers subsequently attempted to sell the stolen data via the dark web.
Cyber attack type: Malware
Location: New York, NY
Cost: Undisclosed
Number of people affected: 5 million
The attack did not impact the companies’ digital platforms. Following the breach, customers were offered free identity protection services.
5. CVS Health
In 2021, a massive, misconfigured database containing 1.1 billion records — including customer email addresses, user IDs, and customer online search information gathered from CVS Health and CVS.com — was found publicly available and unsecured by cybersecurity researchers.
Cyber attack type: Human error
Location: Woonsocket, RI
Cost: Undisclosed
Number of people affected: Undisclosed
The company restricted access on the same day that third-party researchers notified CVS Health of the unprotected data online.
4. eBay
Using compromised employee credentials, attackers accessed approximately 145 million eBay accounts in 2014. The online auction company acknowledged that attackers managed to copy much of the data tied to the accounts, including email addresses, birthdates, and mailing addresses.
Cyber attack type: Compromised employee credentials
Location: San Jose, CA
Cost: Undisclosed
Number of people affected: 145 million
In response to the attack, eBay required 145 million users to change their passwords. Subsequently, in February 2021, 14 million Amazon and eBay accounts from 2014 to 2021 were sold via a hacker’s forum for $800. It is unknown if the eBay accounts were part of the 145 million accounts stolen in 2014.
3. Neiman Marcus Group
In September 2021, upscale retailer Neiman Marcus notified 4.6 million customers that a hacker had compromised online accounts in May 2020, gaining access to personal data such as usernames and passwords, customer names, contact information, credit card numbers, as well as expiration dates and virtual card numbers.
Cyber attack type: Not disclosed
Location: Dallas, TX
Cost: Not disclosed
Number of people affected: 4.6 million
Neiman Marcus forced every customer impacted by the breach to change their password if they had not already done so since May 2020, when the breach occurred. The company also created a dedicated call center to field calls from customers regarding the incident and how they might be impacted.
2. Home Depot
Using a third-party vendor’s login credentials, attackers gained access to Home Depot’s network, then deployed malware designed to infect the retail giant’s POS system and gather customer payment information. Between April and September 2014, the breach impacted 52 million customers.
Cyber attack type: Compromised third-party credentials/POS malware
Location: Atlanta, GA
Cost: $215 million
Number of people affected: 52 million
Home Depot paid $17.5 million to settle claims across the country. That was just a fraction of the overall costs, however. The company recorded pretax expenses of $198 million related to the breach and subsequent litigation by customers, payment card issuers, and financial institutions before the settlement.
1. Target
A 2013 cyber attack involving Target exposed 41 million payment cards and contact information for approximately 70 million customers. The attack focused on a third-party vendor via a spear phishing attack designed to steal user credentials. Once threat actors compromised Target’s network, they installed malware to seize customer data over the course of two months.
Cyber attack type: Spear phishing/malware
Location: Minneapolis, MN
Cost: $290 million (approx.)
Number of people affected: 70 million
In the aftermath of the breach, Target’s CEO left the company. To resolve country-wide claims, Target paid fines totalling $18.5 million. All told, including remediation, consulting fees, and other payments, the breach cost the company about $290 million.
The Pressing Need for Cybersecurity
With a vast wealth of payment data, personal information, and user credentials, retailers will continue to attract keen attention from sophisticated attackers. Cybersecurity, therefore, must always be a top priority for retailers if they hope to avoid becoming victims of cybercrime, prevent inadvertent disclosure, and protect the vast amount of customer data in their possession.
Discover proactive solutions to the challenges of retail cybersecurity.
Learn how best to secure retail cloud environments.
Learn how Arctic Wolf provides retailers with customized security operation solutions, including around-the-clock, on-demand access to a dedicated team of security experts with extensive expertise helping businesses develop, maintain, and scale their cybersecurity defenses.






