
Understanding Telemetry in Cybersecurity
Threat actors don’t just try to gain access to an organization by targeting a single area of their environment. In today’s complex, connected IT environments,
Delivering security operations outcomes.
Delivering AI outcomes you can trust.
Leverage the power of scale and AI expertise.
Ecosystem integrations and technology partnerships.
Partner with the world’s largest commercial agentic SOC.
Tailored security expertise and guided risk mitigation.
Security experts proactively protecting you 24×7.
Learn how our IR team stops attacks and swiftly restores your organization to pre-incident operations.
Build a resilient business by embracing Security Operations.
Map your security posture against industry standard frameworks.
Continuously discover, prioritize, and reduce exposure across your attack surface.
Receive end-to-end IR coverage for one incident, no matter the incident type.
Engage and prepare employees to recognize and neutralize social engineering attacks.
AI-driven prevention, detection, and response to stop endpoint threats before they disrupt your business.
Quickly detect, respond, and recover from advanced threats.
Recover quickly from cyber attacks and breaches, from threat containment to business restoration.
Stay covered at no cost with up to $3M in financial assistance for cybersecurity incidents.
Increase the likelihood of insurability, and potentially lower your rates.
Access a complimentary suite of tools to reduce risk and improve insurability.
|
2025 Arctic Wolf Threat Report
The Arctic Wolf Threat Report draws upon the first-hand experience of our security experts, augmented by research from our threat intelligence team.
The Arctic Wolf State of Cybersecurity: 2025 Trends Report
The Arctic Wolf State of Cybersecurity: 2025 Trends Report serves as an opportunity for decision makers to share their experiences over the past 12 months and their perspectives on some of the most important issues shaping the IT and security landscape.
Aurora: A New Dawn For Cybersecurity
Join Arctic Wolf on an interactive journey to discover a better path past the hazards of the modern threat landscape. |
Helping Solution Providers scale their business with a comprehensive portfolio of products and services.
Arctic Wolf provides the Insurance Partner Program for Brokers and Carriers to support them within the Cyber JumpStart portal.
Ecosystem integrations and technology partnerships.
Grow your business and solve your customers’ cybersecurity challenges with industry-leading turnkey security operations.
Arctic Wolf OEM Solutions enable ISVs, MSSPs, U.S. Federal Agencies, and security companies.

Threat actors don’t just try to gain access to an organization by targeting a single area of their environment. In today’s complex, connected IT environments,

Arctic Wolf is an AI-powered security operations provider, which gives our organization advanced insights into the emerging threats inherent in being an early adopter of

With the rise of hybrid work and software-as-a-service (SaaS) applications for core business functions, as well as the near ubiquity of the cloud, organizations’ attack

What is Ransomware-as-a-Service? Ransomware-as-a-service is a business model where ransomware operators and third parties, called “affiliates,” work together to launch ransomware attacks. RaaS was first

Active Directory (AD) is a core component of IT infrastructure for many organizations, especially as identity management grows for even small-to-medium businesses (SMBs) and once

One of the largest data breaches of 2024 didn’t require advanced tactics, techniques, and procedures (TTPs), or an escalating chain of successful attacks. It simply

The business world has an identity security problem. Identity telemetry dominated Arctic Wolf’s list of the top 10 security investigation types over the past 12
In this video we’ll explore a few of the response actions the SOC team has at their disposal to take action and mitigate impact during

With the emergence of artificial intelligence (AI), there has been a flurry of new terms to describe an increasing variety of new problems. Some of
Witness how Arctic Wolf Data Explorer can provide insight into both security and operational events through three different use cases.

See an example of how Arctic Wolf Managed Detection and Response can protect against fileless malware attacks and how the supporting details are made available

In this demo, follow along as we investigate an alert leading to suspicious events that uncover a full business email compromise (BEC attack).

Arctic Wolf’s integration with iManage Threat Manager enables our concierge security team to monitor alerts. In this demo, see how this integration empowers our team

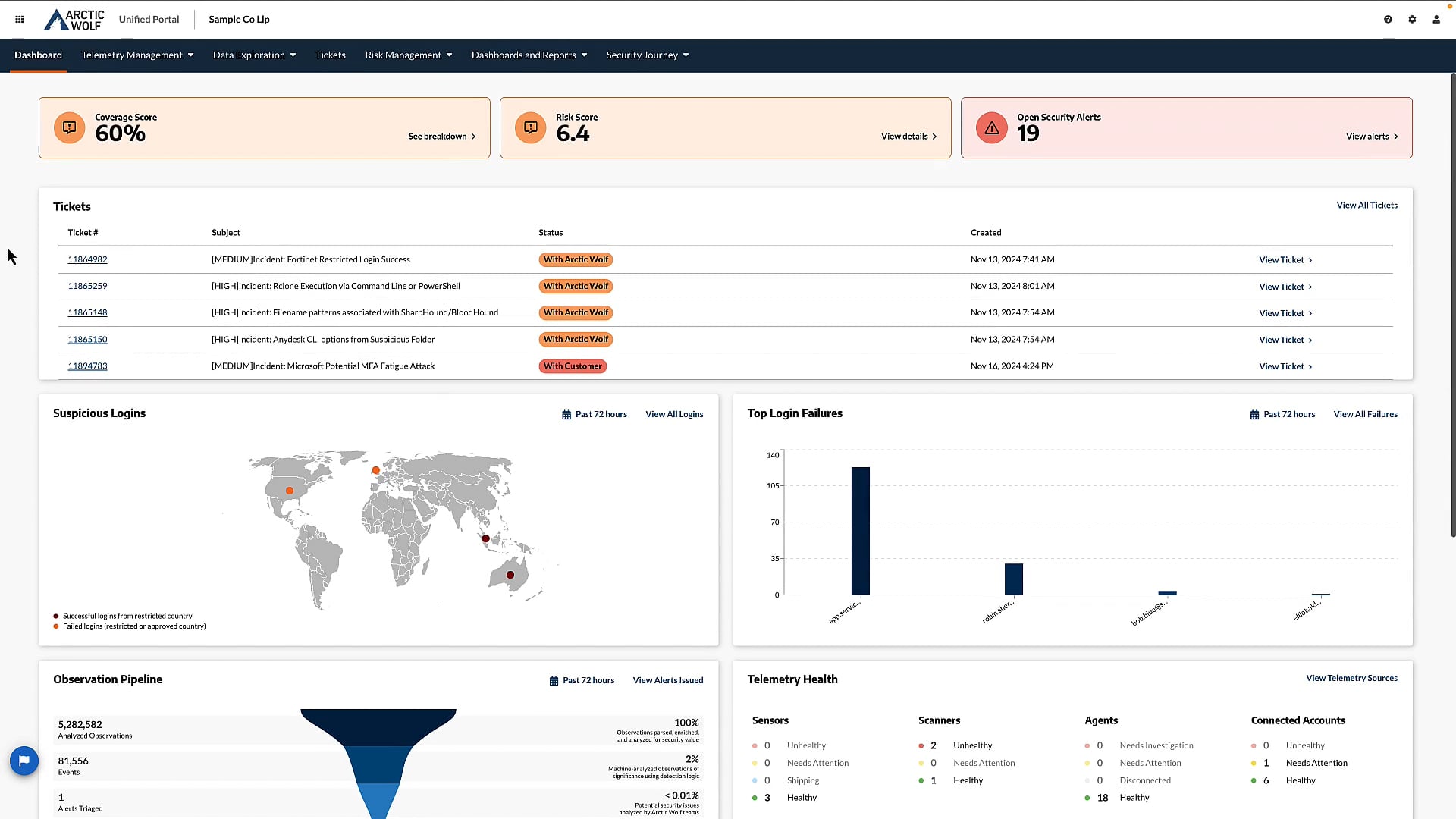
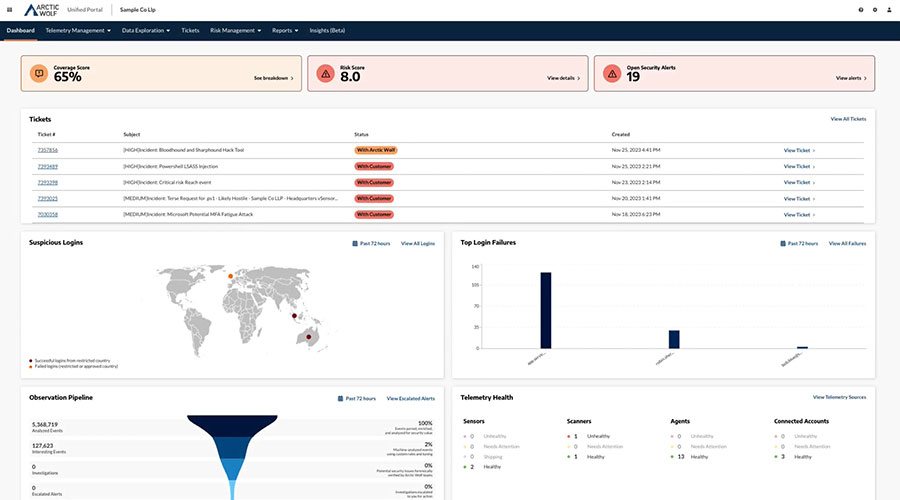
In this demo, explore how the Arctic Wolf unified portal provides visibility into your aggregated security data while also providing flexible visualizations and reporting through

Get actionable insights and aggregated customer reviews of top MDR solutions.
With governments across the globe gearing up for major elections, experts have been predicting an increase in distributed denial of service (DDoS) attacks from nation-states

On April 12, 2024, Palo Alto Networks published a security advisory detailing an actively exploited maximum severity zero-day vulnerability affecting the GlobalProtect feature of PAN-OS.

A ransomware attack is underway. The threat actor has gained initial access to an endpoint and executed malicious code on it. As far as the

Schools and libraries often lack the funding and staffing needed to build and maintain a robust cybersecurity program. They are also the exact kind of

Here’s an endpoint you don’t often think about: your car. But if it’s Wi-Fi enabled, as many new models are, that means it resides at

Gain invaluable insights into the dynamic landscape of a large-scale modern security operations program with actionable guidance on how to reduce your own cyber risk.

Get a comprehensive analyst overview of the evolving MDR landscape.
Having some form of a security operations center (SOC) to protect and secure your assets, applications, and infrastructure is no longer optional. As cyber criminals

You can’t secure what you can’t see goes the saying in cybersecurity. That’s why holistic visibility is so crucial for organizations tasked with staying safe

As the goals of securing as much ransom money and sowing as much discord as possible continues to grow, one of the most preferred methods

This survey of IT and security leaders from North America, Europe, and Australia shows the varying attitudes and approaches organizations take towards risk management and

The cybersecurity industry is always evolving. Whether new solutions arrive because of advances in technology, emerging threats, or changing security needs, every few years a

View IDC’s assessment of the rapidly evolving worldwide managed detection and response (MDR) market.

Forrester interviewed customers about Arctic Wolf’s Security Operations solutions. Here’s their impressive findings.

Understand the benefits and drawbacks of each cybersecurity solution in order to make an informed decision for your organization.
GLOBAL HEADQUARTERS
© 2026 Arctic Wolf Networks Inc. All Rights Reserved. |
||||||
Privacy Notice |
Terms of Use |
Cookie Policy |
Accessibility Statement |
Information Security |
Sustainability Statement |
Cookies Settings |