Active Directory (AD) is a core component of IT infrastructure for many organizations, especially as identity management grows for even small-to-medium businesses (SMBs) and once on-premises organizations turn toward digital operations and cloud-first applications. But this widely adopted tool comes with major security risks as threat actors find more and more value in identity-based attacks.
What is Microsoft Active Directory?
Microsoft Active Directory (AD) is a directory tool for system administrators to set and manage network access and permissions for users within a system. AD contains multiple components, including Active Directory Domain Services, Active Directory Certificate Services, and Active Directory Federation Services.
Active Directory works to efficiently connect users to network resources, and in more technical terms, AD stores data as objects, which can be individual users, groups, or even a singular device like a printer. The tool then sets access controls for the objects, verifying pre-set controls, or giving or denying permission for certain actions.
Active Directory’s Role in Access Control
AD allows organizations to implement their identity and access management (IAM) goals and identity security initiatives by configuring permissions for users and devices within the network. Limiting permissions and network access within AD allows an organization to better follow zero trust models and privilege access management (PAM). AD also creates visibility for security and IT teams, allowing these teams to see the “who, what, and when” of internal access while allowing them to make changes to harden or adjust that access.
Active Directory Security Risks
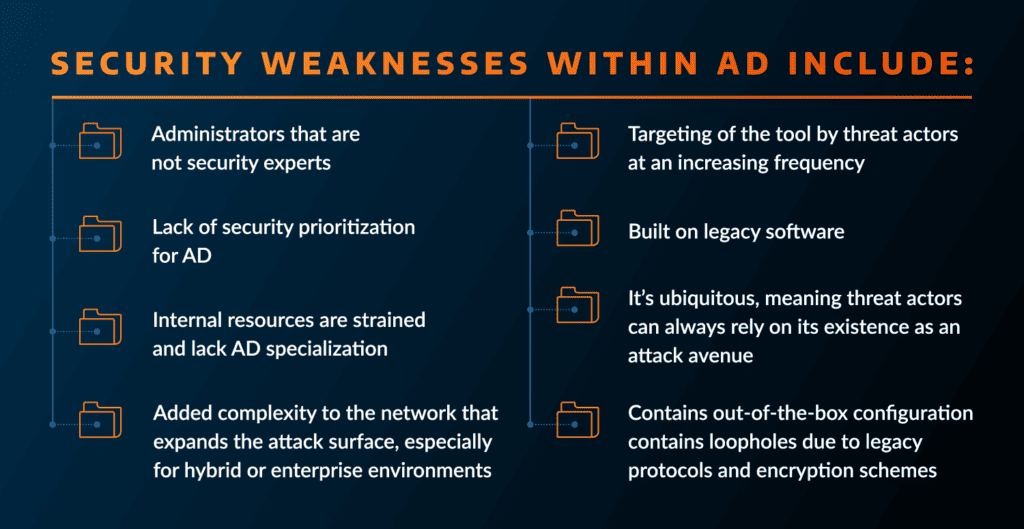
While AD can play a critical role in an organization’s access controls, it also contains inherent security risks that make it a top target for threat actors.
Security risks within Active Directory include:
- Is often run by administrators who may not be security experts
- Is often not prioritized as part of cybersecurity measures
- Can strain Internal resources who lack AD specialization
- Added complexity to the network and an expanded the attack surface
- Is built on legacy software
- Is ubiquitous in organization’s infrastructure, meaning threat actors can always rely on its existence as an attack avenue
- Contains out-of-the-box configurations
- Contains loopholes due to legacy protocols and encryption schemes
- Lacks multi-factor authentication (MFA)
- Weak passwords or insufficient password policies
- Legacy systems running out-of-date or vulnerable versions of AD
- Privilege abuse by an insider or a malicious insider who utilizes their access to steal credentials or data
According to the Arctic Wolf Labs 2025 Predictions Report, these weaknesses, particularly the out-of-box configurations and often permissive policies that follow, mean that we’ll see threat actors target AD more and more.
“Active Directory configurations are not specifically designed to be ‘secure by default.’ This could lead to multiple opportunities for detrimental misconfigurations that require updating or modifying. Unfortunately, making changes to authentication infrastructure can be disruptive to end users, causing needed upgrades/migrations to fall behind. On-premises Active Directory infrastructure often lags behind other high priority work and remains operational longer than it should, even with versions of Windows that have reached end-of-life (EoL) status.” — The Arctic Wolf Labs 2025 Predictions Report
Hardening Active Directory against these security risks is an important part of identity security within an organization. Not taking measures to secure Active Directory could lead to a threat actor gaining access and conducting credential theft, privilege escalation, data exfiltration, or even launching a more sophisticated attack such as ransomware.
Active Directory Security Best Practices
Hardening your Active Directory is not a simple, one-and-done task. It takes both time and resources; however, the continued attention is invaluable considering how vital AD is to an organization’s overall identity structure and security.
There are a multitude of ways to harden AD, from the simple to the deeply technical and complex, the implementation of which are dependent on an individual organization’s security goals, resources, and risk tolerance. But there are seven steps that all organizations should work to achieve first for increased security.
1. Conduct password policy updates. Strong passwords go a long way in preventing man-in-the-middle and other password-based attacks. Standard best practices say that a password should be at least 12 characters long with letters, numbers, and special characters. Strong user awareness training should also be implemented to highlight the value of individual password hygiene. Passwords should be regularly assessed and changed, as well.
2. Implement access control and authentication measures. Limiting the attack surface in case an Active Directory attacks is successful is critical for minimizing or stopping lateral movement. MFA will prevent access, even if a password is hacked or credentials are stolen, and other access controls, such as the following of zero trust guidelines or implementing privileged access management (PAM), especially for administrative account will prevent a threat actor from moving deeper into the network. Hardening privileged groups within AD, such as ensuring member attributes are not word-readable, can also prevent credential theft and lower the impact of an AD-related incident.
3. Enforce strong encryption throughout AD. The out-of-box settings in AD only offer basic encryption. Tightening configurations and adding layers of encryption reduces the chances that an attacker will be able to crack passwords and buys security teams time to detect initial access.
4. Audit permissions and file sharing. Visibility is a major component of any security strategy, and the same is true with AD. An organization’s security team should be able to analyze security groups, privilege escalation paths, user account permissions, and potential attack paths, to identify weaknesses and correct them. The same should be done for any files within AD as well.
5. Implement group policy security. Security settings in AD are specified by group policy configurations. This means that one setting can apply to a high number of users, and both makes AD valuable and a security risk. Security teams should look at these policies granularly and assess them regularly to confirm there are no misconfigurations or permissive policies. If an entire group is compromised, threat actors could use that access to quickly spread ransomware payloads or launch another sophisticated attack network-wide.
6. Have 24×7 monitoring in place. Knowing unusual behavior is happening, in real-time, can be the difference between stopping a threat or having to content with a major incident. It’s important for an organization to have a monitoring solution in place, preferably one like Arctic Wolf® Managed Detection and Response, which can alert a security team to detections coming directly from AD, as well as identities and other network sources, as well as correlate the behaviors and alerts, providing the most accurate and actionable information.
7. Conduct regular security assessments of AD. As an organization’s business and operations change, so does security. By regularly assessing Active Directory, security teams can reduce the risk of misconfigurations, permissive policies, and update access controls based on modifications in user headcount, application installations and network changes, or overall security and business goals.
Hardening Active Directory with Arctic Wolf
Arctic Wolf understands that identity infrastructure is target for threat actors, and as such, identity is a key telemetry source ingested and analyzed by the Aurora Platform. Arctic Wolf offers, through Arctic Wolf Managed Detection and Response, 24×7 advanced identity monitoring of Active Directory, and actively analyses identity risks such as anonymous IP address use, atypical travel, malware-linked IP addresses, unfamiliar sign-in properties, leaked credentials, password spray, and more. As part of an organization’s ongoing Security Journey with Arctic Wolf, our Security Teams can provide periodic Active Directory hardening measures to increase an organization’s security posture.
Better understand the modern threats your organization faces with the Arctic Wolf 2025 Threat Report.
Take proactive steps to harden Active Directory at your organization with our on-demand webinar.






