The ways in which people work are changing, and so are the approaches needed to secure modern work.
As organizations race to gain the benefits of cloud computing, relax rules around bring-your-own devices, and leverage hybrid-work models that require edge devices such as VPN gateways, the result is an expanding, disparate IT environment. And even worse, users are a part of the attack surface — one threat actors are all too ready and willing to exploit.
Organizations, then, need a strategy to secure all their access points and users, regardless of where they may be, while actively preventing and stopping threat actors from gaining access or launching sophisticated attacks.
Enter zero trust.
What is Zero Trust?
Zero trust is a cybersecurity strategy that works to eliminate the concept of trust as a component of the security technologies and approaches within an IT environment.
Historically, organizations have relied on perimeter security devices, such as firewalls and VPNs, to govern the secure external access to sensitive applications and data, which all lived on premises. Today, now that a critical mass of both users as well as sensitive applications and data exist outside the traditional corporate perimeter, a perimeter-based approach to security is no longer sufficient.
Instead, zero trust has emerged as an alternative. A zero trust framework relies on point-in-time verification, control, and restriction of access, never trusting that anyone should have default access to any application or data source. Instead, zero trust frameworks require that access to each system, data, or application be assessed and verified on a point-in-time, one-off basis, ideally preventing threat actors from exploiting any trust to gain access undetected.
A zero trust framework relies on various technologies and tools to hold every user and access request to a rigorous level of scrutiny when trying to access a system, program, or asset. In addition to an external-only security architecture (where the perimeter of a network, not internal access points, is defended), zero trust employs controls at access points within a system.
A good example of zero trust is the access controls central to a strong identity and access management (IAM) system, and how those access controls are deployed and maintained within an environment. In a zero trust framework, each user, regardless of whether the user is directly connected to the on-prem network or connecting from a remote location, not only would need credentials to access a particular application, but would also need to undergo identity verification through a secondary control, such as multi-factor authentication (MFA). Crucially, zero trust requires such verification every single time a user initiates access to that application. Zero trust works against the idea that a user can attain “trusted” status, even if the user has previously verified their digital identity.
Zero Trust vs. Zero Trust Network Access (ZTNA)
Zero trust and zero trust network access (ZTNA) work together to help organizations create a zero trust environment but are not interchangeable terms. Zero trust, broadly, is the strategy, idea, and subsequent framework organizations can take with them as they employ ZTNA, which is the specific technologies, tools, and mechanisms used to implement zero trust, usually in the form of a software-defined virtual perimeter, or an identity-aware proxy.
ZTNA actions can include:
- Governing policy-based access for any number of applications and data systems
- Isolating application access from broader network access
- Granting application access on a one-to-one basis, meaning that a user, once approved, will only have access to that singular application or asset, nothing else
- Application of verification software to applications and assets, be it phishing-resistant MFA or a single-sign on (SSO) program
- Supporting dynamic access policies, meaning they can change based on business, security, and user needs
- Considering and applying context to access verification, such as the time that access is requested or the geographic location of the endpoint
- Blocking all network traffic as the default, allowing it only upon identity verification
ZTNA was originally designed to bridge zero trust principles between on-prem and cloud environments, serving as a replacement for VPN technologies. While ZTNA is still widely used, it is quickly becoming more common for organizations to rely on a cloud-based single sign on (SSO) or MFA solution as the primary mechanism to implement zero trust.
What Zero Trust is Not
Zero trust is often viewed as a cybersecurity buzzword with little weight behind it. When that happens, some cybersecurity providers benefit from the blurring of lines, seeing increases in brand awareness and market share on the back of the term’s rising popularity, providing technologies or strategies that provide little to no semblance to the actual practice of zero trust. It’s just as crucial then, to know what zero trust isn’t. Here are two practices which can be considered components of a zero trust strategy but are objectively not zero trust.
1. Principle of least privilege
Organizations often limit access to specific systems and data only to those users who have a demonstrable need. In cybersecurity terms, this is known as applying the principle of least privilege (PolP). PolP practices ensure that verified users only have any access to sensitive systems, applications, and information at the level required to effectively do their jobs. PoIP acts as a preventative security measure that not only restricts access to sensitive networks and data but also gives organization’s greater control and deeper insights into who is accessing what, when, and why within their organization. However, the principle of least privilege is focused on reducing a user’s access, while zero trust is focused on verifying a user’s access. Both work in tandem to better protect the overall attack surface and prevent data breaches and other security incidents.
2. Multi-Factor authentication
Multi-factor authentication (MFA) is a form of access control that acts as an additional security measure to a user credential-based login. It’s defined as requiring two or more forms of the three factors of verification – something you know (like a password or PIN), something you have (a token such as a cell phone or email address), or something you are (such as a voice or fingerprint) – that are needed to gain access to an application or network by a user. MFA is one of the key tools in zero trust toolbox, but it is not the entire toolbox. Organizations that follow zero trust frameworks should have MFA applied across their environment.
Benefits of Building a Zero Trust Framework
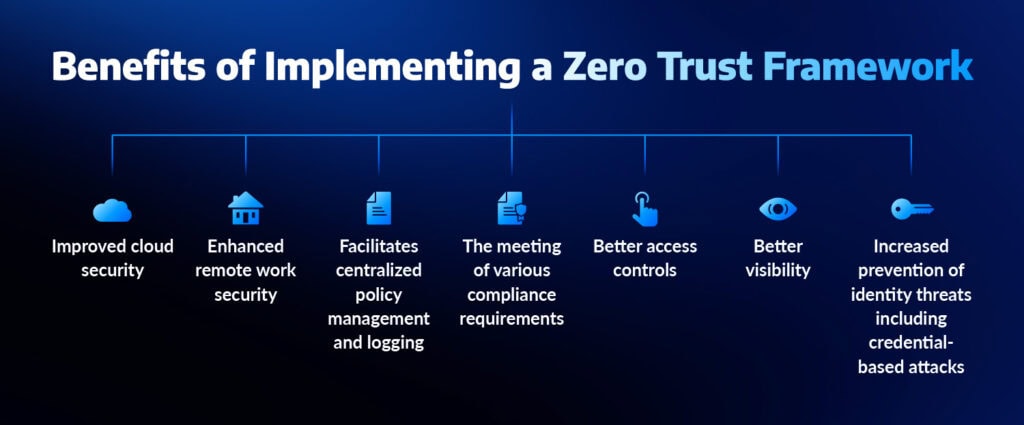
Zero trust effectively reduces risk while hardening the modern-day attack surface by placing digital doors around every application and asset, not just the traditional network perimeter. Zero trust also allows for risk-based and context-based decision making around access governance and response, which creates both the security and flexibility needed in the age of application-based environments and hybrid work models.
Other benefits of zero trust include:
- Improved cloud security as the framework is applicable to cloud environments
- Enhanced remote work security by isolating the identity of the user from the endpoint that the user is logging in to/trying to gain access from
- Facilitates centralized policy management and logging
- The meeting of various compliance requirements around access controls and identity security
- Better access controls across the extended IT environment
- Better visibility into who is accessing what, when, and how
- Increased prevention of identity threats including credential-based attacks
How To Implement Zero Trust
The best way to explain how to implement zero trust is to first break down the various pillars involved. These pillars show exactly what zero trust means when applied to various parts of the IT environment and provide guidance for IT and security teams looking to apply zero trust to their organizations.
The pillars of zero trust are:
1. Workforce security. This involves effectively using access control policies and authentication measures in regard to the workforce within an IT environment.
2. Device security. Like identities, this pillar applies access controls and policies to devices, or endpoints, attempting to access a network or application.
3. Workload security and integrity. This involves security of the applications, processes, and process-driven resources an endpoint or user may try to access.
4. Network pathway security. This involves applying techniques such as encryption, isolation and micro-segmentation to network segments and flows to protect sensitive resources, which in turn prevents unauthorized access.
5. Data protection and categorization. You can’t secure data if you don’t understand its value to both operations and threat actors. By categorizing the data within an IT environment, you can better restrict access to it (based on PolP as mentioned above) and store it appropriately to prevent unauthorized access.
6. Visibility and analytics. Because zero trust is context-based and flexible by nature, an organization needs visibility into who has access to what, when, and what occurs after access is granted. This visibility can not only identify key gaps in the framework but can alert security teams to potential threats in real-time. For example, if security teams can see that a user is repeatedly trying to gain access to an application at 3 a.m. from Russia, it’s probably not a normal use case for that access.
Other methods an organization can use to implement zero trust include:
- Determine and deploy technologies, such as Okta or Zscaler to automate access verification and control
- Follow IAM best practices, and ensure there are no gaps in your IAM structure, such as permissive policies or workarounds to reduce friction with users
- Implement endpoint security measures, including endpoint detection and response (EDR) to better see, detected, and respond to identity-based threats that could originate on remote endpoints and user devices
- Practice network segmentation to limit lateral movement
- Continuously monitor your network, identity sources, and broader IT environment for abnormal behavior or indicators of compromise
Zero Trust and Arctic Wolf
Arctic Wolf believes identity security is vital to a robust cybersecurity strategy, and that identity telemetry should be one of the telemetry sources included and analyzed within a detection and response solution.
As such, not only does Arctic Wolf® Managed Detection and Response, powered by the Aurora™ Platform, pull in identity telemetry for broad visibility and more precise, actionable detections, but Arctic Wolf partners with multiple identity security providers to help organizations implement a zero trust framework and secure both their users and assets.
Understand the value of zero trust in relation to the threats posed to identity sources with the 2025 Arctic Wolf Threat Report.
Discover more about the importance of identity and access management.
Explore how Arctic Wolf makes zero trust possible with our Zscaler partnership.






