How Arctic Wolf Delivers Managed Detection and Response with Broad Visibility and Proactive Security
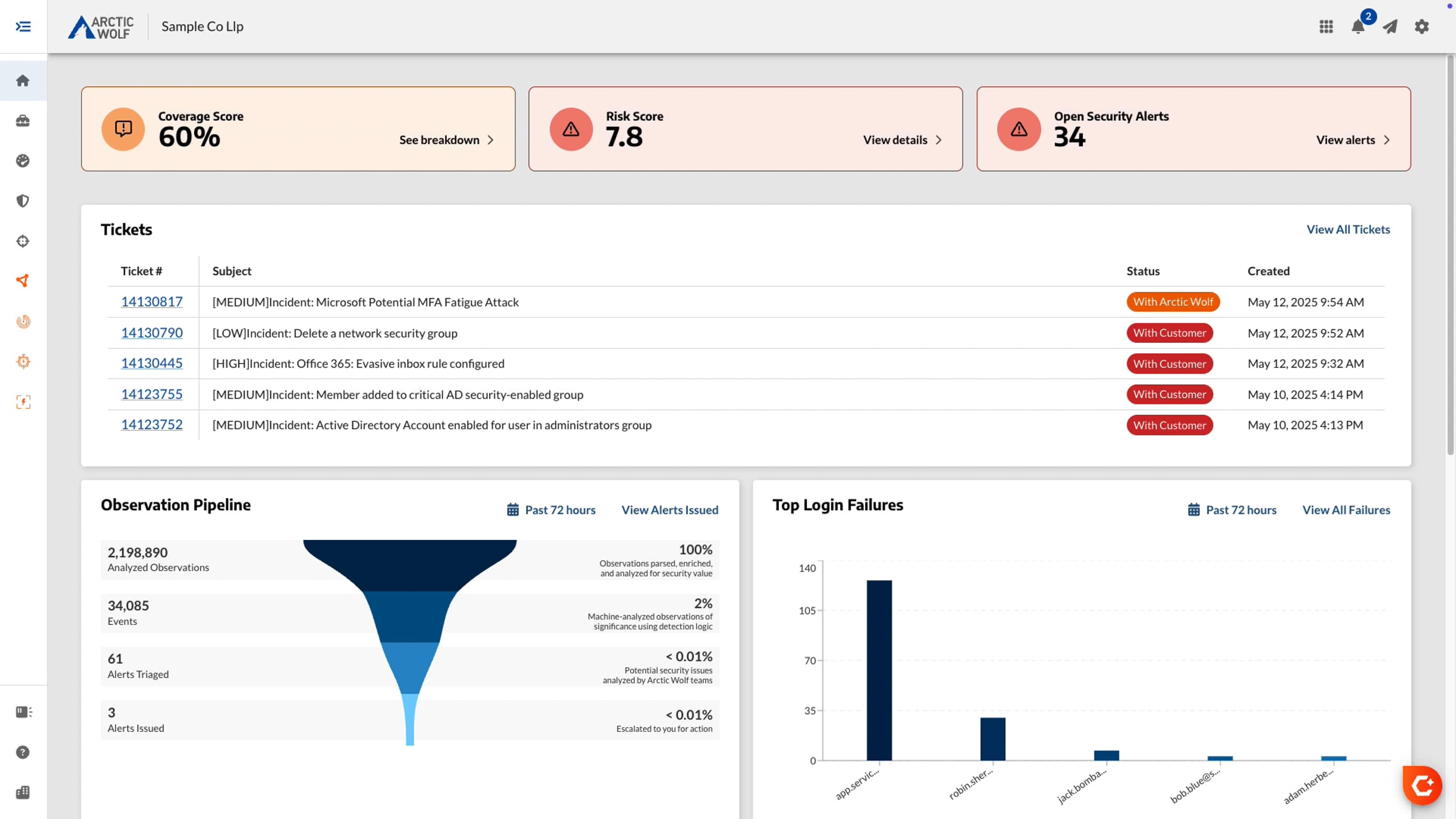
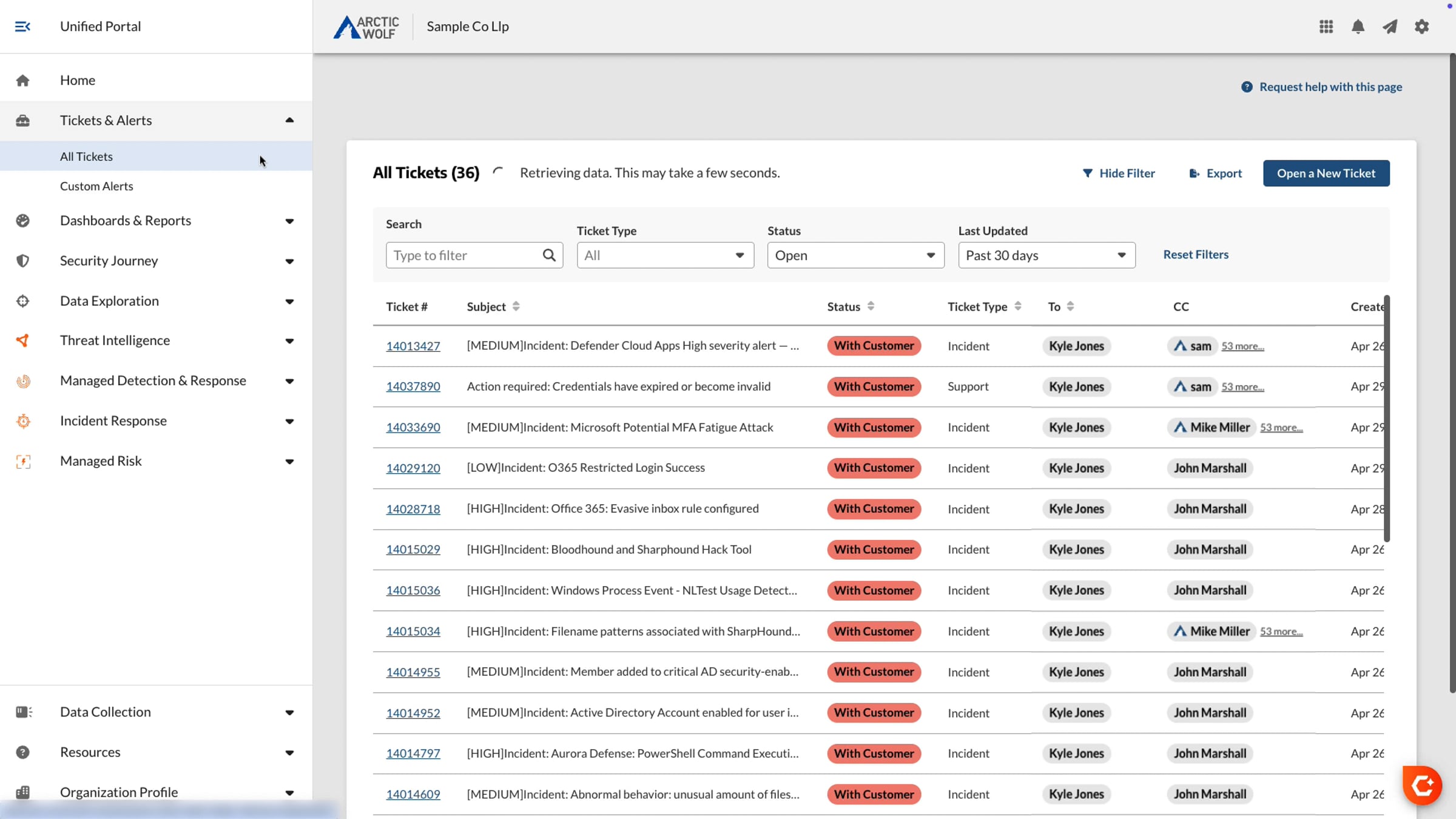
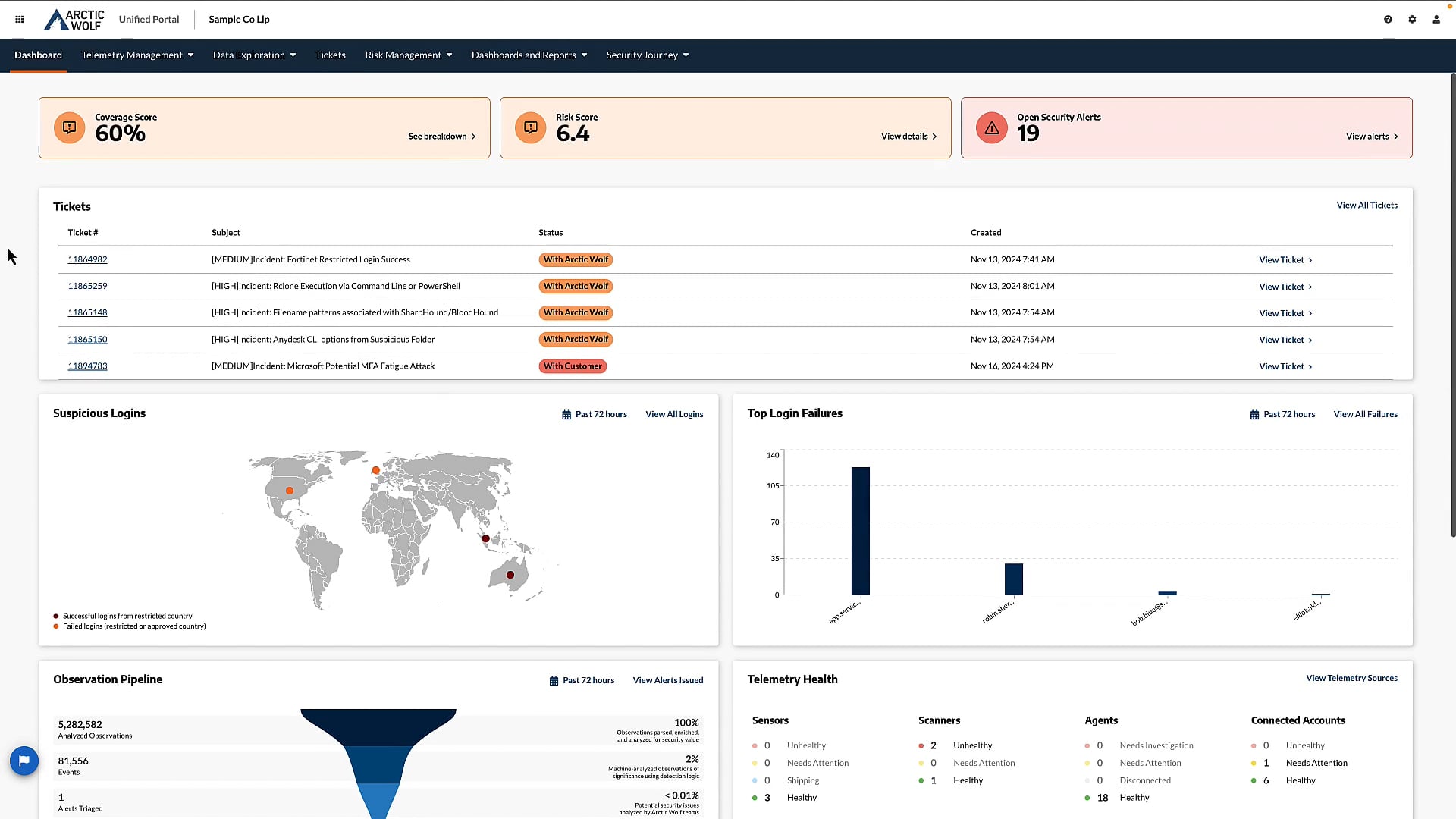
In this Managed Detection and Response overview, we see how Arctic Wolf delivers 24×7 monitoring, broad visibility, response capabilities and proactive security recommendations to our