Key Takeaways:
- Arctic Wolf Labs has observed one in four organizations in our customer base targeted with Log4Shell exploitation attempts since January 2022
- Log4Shell exploitation was the root point of compromise in 11% of Arctic Wolf’s incident response cases throughout 2022
- Approximately 60% of all Log4Shell incident response cases investigated by Arctic Wolf were attributed to three ransomware groups, LockBit (26.9%), Conti (19.2%), and Alphv/BlackCat (11.5%).
- The average incident response cost of a Log4Shell incident exceeds US$90,000
As we approach the one-year anniversary of the Log4Shell vulnerability (CVE-2021-44228), Arctic Wolf Labs decided to look back on the impact that this critical vulnerability had (and continues to have) on organizations and assess the long tail of activity we’ve seen with threat actors continuing to use the exploit. The high level of ongoing exploit activity nearly 12 months after the vulnerability was first announced is sobering and clearly demonstrates the need for comprehensive cyber protection that includes advanced threat detection, patching, and vulnerability scanning.
Protecting and Detecting Against Log4Shell
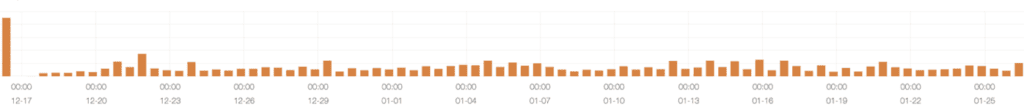
The Log4Shell vulnerability was first disclosed on December 9, 2021, and after quickly tuning our correlation and analysis systems, as well as deploying additional detections, we were able to get insight into the early days and weeks of threat actor activity. As we published early last year, in the first 47 days (until January 25, 2022), we identified and triaged 29,338 unique incidents of adversarial scanning for CVE-2021-44228 within the environments of 807 of our customers.
After the initial hype around this vulnerability died down it became clear that there are traditional defensive steps that could be taken to mitigate the risk of exploitation. Both the Arctic Wolf® Security Operations Cloud and Arctic Wolf Concierge Security® Team were able to deliver tailored intelligence and remediation guidance in a rapid response to allow our customers to mitigate the risk caused by the Log4Shell vulnerability.
But what Log4Shell impact have we seen since January 25, 2022?
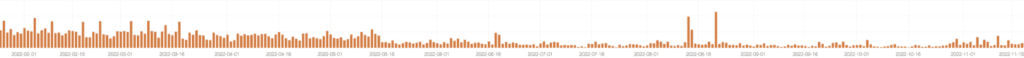
Looking at data from the past eleven months, it’s clear that threat actors are still trying to exploit the Log4Shell vulnerability, with Arctic Wolf identifying 63,313 unique incidents of adversarial scanning and attempted exploitation activity at 1,025 (approximately 25%) of our customers.
Responding to Log4Shell Incidents
While the Arctic Wolf Security Operations Cloud was able to protect our current customers from the impact of Log4Shell, the vulnerability was responsible for a significant number of our incident response engagements by organizations that are not Arctic Wolf customers.
As first highlighted in our 2022 1H review of our incident response engagements, Log4Shell was the second-most leveraged external exploit (11% of total cases) used by threat actors to deploy ransomware in 2022, behind only ProxyShell (CVE-2021-34473), a vulnerability in Microsoft Exchange published in 2021. In addition to a significant number of incident response cases, Log4Shell, like any cyber incident that requires incident response support, represented significant costs for impacted organizations, with the average Log4Shell incident response engagement costing over US$90,000.
Approximately 60% of all Log4Shell incident response cases investigated by Arctic Wolf were attributed to three ransomware groups, LockBit (26.9%), Conti (19.2%), and Alphv/BlackCat (11.5%). We observed other ransomware groups exploiting Log4Shell too, including Babuk, HIVE, Jolyoga, and Pandora. However, these incidents represented a much smaller share or our total Log4Shell incident response caseload.
Preventing Future Log4Shell Incidents
With Log4Shell representing 11% of incident response cases, and threat actors continuing to attempt to exploit, identifying all vulnerable instances of Log4j library within an organization continues to be an ongoing challenge for IT and security teams.
Last year, Arctic Wolf Labs published a number of recommendations for organizations looking to prevent being exploited by the Log4Shell vulnerability. In addition to those recommendations, we also created a Log4Shell Deep Scan open source tool that will conduct a scan of a host’s file system to identify Java applications and libraries with vulnerable Log4j code. The tool exposes which applications are affected and where each vulnerability exists, so that IT and security teams can then conduct rapid prioritization and targeted remediation of this vulnerability.
Arctic Wolf’s Log4Shell Deep Scan tool should be used as a complement to existing network-based vulnerability scanning solutions that organizations should already have in place. We recommend organizations periodically run this tool on their most critical cyber assets that are publicly exposed, as well as those behind your perimeter.
At Arctic Wolf, we believe that advancing defense across the entire NIST security operations framework is the only way for organizations to advance their posture against sophisticated threats like Log4Shell. Since Arctic Wolf is one of the few companies with outcomes that span the entire framework, Arctic Wolf Labs is uniquely positioned to understand the adversary behavior that targets the thousands of customers we protect each day, as well what non-Arctic Wolf customers have experienced through the response cases of Tetra Defense, Arctic Wolf’s incident response business unit.






