Key Takeaways:
- The second quarter of 2022 saw a significant uptick in business email compromise (“BEC”) attacks, accounting for over a third of total cases we responded to. At 80% of the organizations where a BEC attack occurred, there was no Multi-Factor Authentication (“MFA”) solution in place prior to their incident.
- The median ransomware demand from threat actor groups was $450,000, with Technology and Shipping/Logistic industries experiencing demands that more than double the global median.
- While the human element is a common attack vector that threat actors can exploit, over 80% of incidents are driven by the exploitation of unpatched vulnerabilities or remote access tools.
- Incidents tied to the well-publicized ProxyShell and Log4J vulnerabilities continue to be twice as costly for organizations to respond than a median incident.
Arctic Wolf Labs regularly collects and analyzes data and insights from the incident response activities of Arctic Wolf’s incident response business unit, Tetra Defense. These insights, as laid out in the charts and graphs in this blog, enhance the threat detection capabilities of the Arctic Wolf Security Operations Cloud, and are leveraged by Arctic Wolf’s community of partners. These incident response insights support the underwriting strategies, loss prevention programs, broker advisement, and client security priorities of Arctic Wolf’s insurance partners. Our broader channel partner community uses these insights to determine areas of risk and opportunity to strengthen customer security postures.
Some of the most notable observations from the first half of 2022 (January – June) include:
Business Email Compromise Attacks Jump in Q2
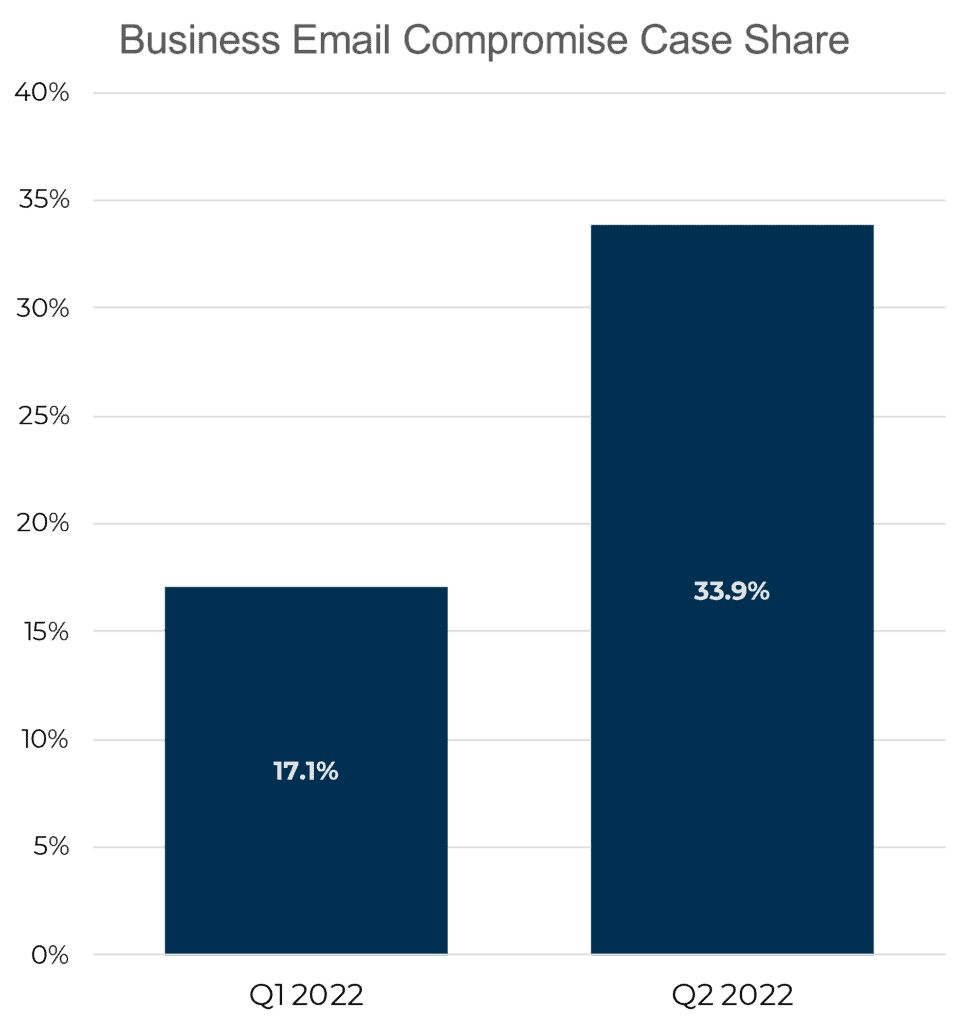
One of the most notable changes in the threat landscape since we published our Q1 findings (January-March 2022) was a significant uptick in the number of successful business email compromise (“BEC”) attacks that were observed in the second quarter. As a percentage of case load, BEC attacks nearly doubled quarter over quarter, accounting for over one-third of total cases. Industries such as Finance and Insurance, Business Services, and Legal and Government saw a significant increase in this attack type with case share more than doubling in the second quarter.
Of significant note in these BEC cases, 80% of the impacted organizations did not have multi-factor authentication (“MFA”) in place. The ongoing exploitation of compromised credentials in BEC attacks highlights the importance that multi-factor authentication (“MFA”) and dark web monitoring play in securing organizations. With MFA in place, exploitation of compromised credentials becomes more challenging. Even if a threat actor has a known username and password pair, the account remains inaccessible without a second factor of authentication such as an app push notification, text message, or security token. As a next layer of defense, in a worst case scenario, a dark web monitoring feature can alert organizations if credentials have been exposed.
In addition to the need for MFA, the ongoing exploitation of compromised credentials in BEC attacks also underscores the need for organizations to have robust security awareness training programs, focused on increasing user vigilance of fraudulent credential requests, in addition to 24/7 monitoring. This user vigilance training is critical due to the increasing number of phishing toolkits that prompt users to enter MFA tokens.
Ransom Demands Vary Across Industries
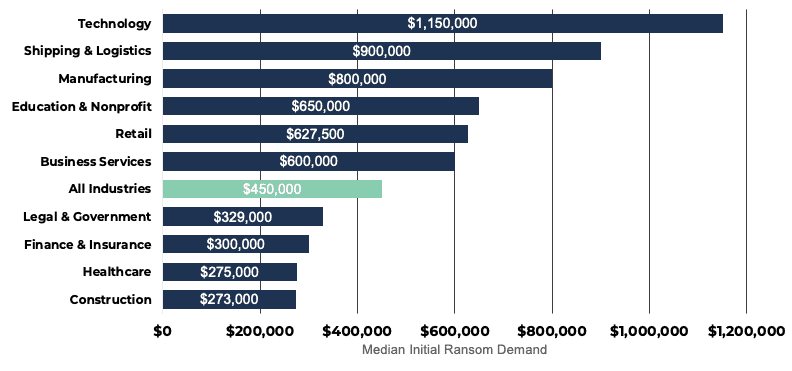
The median ransom demand across all ransomware incidents Tetra Defense responded to was USD$450,000. Threat actors can use several factors including organizational size, corporate revenue, and the sensitivity of encrypted data to determine their initial ransom ask of an impacted organization.
For an industry like Shipping & Logistics, the median ransom demand may be significantly higher than the global average because these industries tend to have less organized network and data structures and weaker backup practices. This, combined with significant business interruption costs due to the nature of their services, signals to threat actors that they may be able to extract a higher ransom from companies in this industry.
In contrast, the Healthcare industry and the Finance & Insurance industry has a median ransom demand below the global average, despite accounting for over 30% of caseload. While the Healthcare and the Finance & Insurance industries harbor very sensitive and valuable data, they are typically more mature in their cyber hygiene practices. This means threat actors likely have less leverage to demand a high ransom because they are unable to impact the entire organization or know the organization can likely utilize offsite backups to restore operations.
Important Note: Median figures are used throughout this blog for comparison purposes because the cost of a ransom demand or incident response activities can vary wildly based on the size of the organizations and the scope of the incident. Median figures provide the best approximation of what a “typical” event looks like because very large and very small outlier incidents can have significant impact when reporting averages.
Root Point of Compromise (“RPOC”) Deep Dive
The Root Point of Compromise (“RPOC”) is the initial entry point of a threat actor—how the threat actor first infiltrates a victim organization’s systems. RPOC is defined by two main categories:
- External Exposure: A threat actor utilizes a technological exploit to compromise a publicly accessible system (i.e., a known vulnerability or weakly secured/implemented remote access). This is the easiest method for threat actors to deploy, therefore it is widely used.
- User Action: A threat actor gains entry to a system through a specific user’s behavior on the
victim network (i.e., downloading a malicious document from a phishing email). Threat actors need a user to perform a specific action for the attack to be successful, making them less reliable avenues for attack.
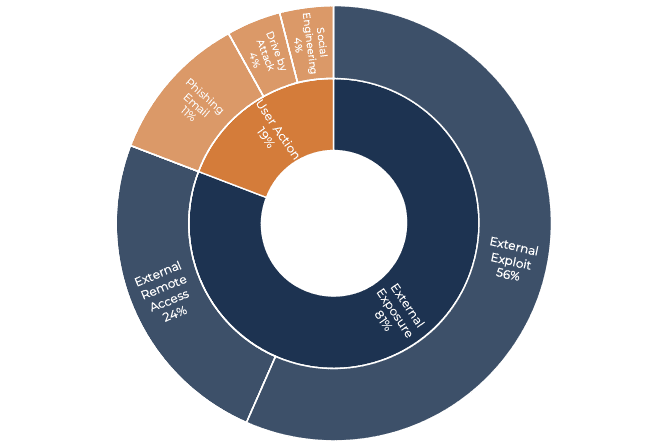
In the first half of 2022, the vast majority (81%) of total incidents happened through external exposure of either a known vulnerability on the victim’s network or a Remote Desktop Protocol (“RDP”). These external exposures are classified in two ways:
- External Exploits which could be mitigated through publicly available security patches and software updates. In these instances, a threat actor utilizes a known vulnerability to gain access to the network before the internal organization patches the system. In the second half of 2022, 56% of total incidents were caused by the exploitation of external vulnerabilities.
- External Remote Access are IT practices that are designed to allow authorized users remote access to the network, such as leaving a RDP port open to the public internet. These practices introduce increased cyber risk to a business because the mitigation relies on an organization’s continued security vigilance and willingness to enforce consistent standards over long periods of time. In the first half of 2022, 25% of total incidents Tetra Defense handled were caused by external remote access.
Root Point Product of Compromise
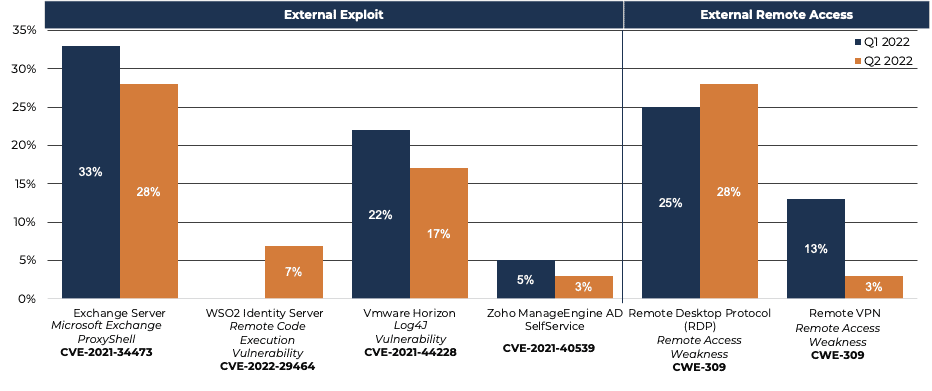
A deeper dive into the products that threat actors are exploiting reveals that a handful of solutions are responsible for a significant portion of the ransomware incidents. As we highlighted in our Q1 review of incidents, Microsoft Exchange (ProxyShell) and VMWare Horizon (Log4J) remain the top two External Exploits being leveraged to deploy ransomware. In both cases, the CVEs for these products were published in late 2021, but despite available patches and significant media coverage, they are still being exploited in the wild. However, between Q2 and Q1, a decline in case share may indicate that organizations are making progress with patches for these vulnerabilities.
With respect to the exploitation of remote access tools, Microsoft Remote Desktop Protocol (RDP) continues to be the root point of compromise for a significant number of incidents. The common thread to incidents where external remote access is the root cause was not due to a flaw in the protocol or application, but a lack of MFA that allowed threat actors to leverage weak or reused passwords that these systems use (such as Virtual Private Networks without MFA).
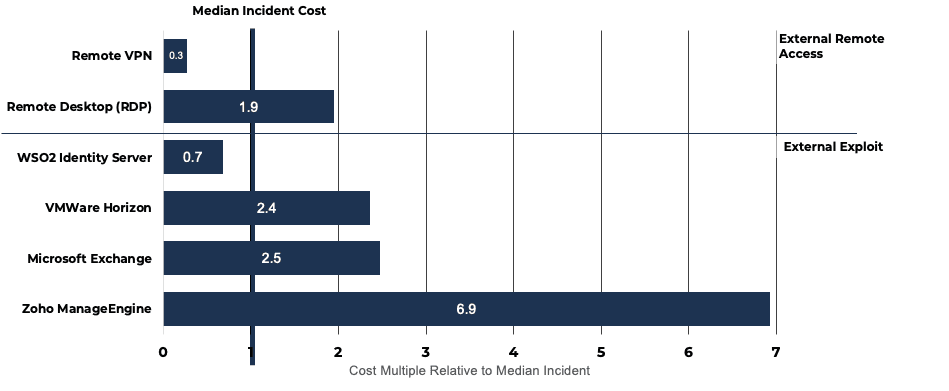
Aside from the popularity in the enterprise market, Microsoft Exchange and VMWare Horizon make up such a significant portion of incidents because threat actors can make significant financial gain from their exploitation with very little effort.
When comparing the median cost across all incidents to the median cost across some of the most exploited External Exposures, incident response for the three most common External Exposure incidents (Microsoft Exchange, VMWare Horizon, and RDP) costs organizations twice as much to respond to compared to other incidents.
The other two types of User Action incidents, which each only account for only 4% of total incidents, were caused by “Drive by Attacks” where a threat actor creates a webpage that downloads malware to the end user’s system and “Social Engineering”, where scam phone calls or social networking applications were leveraged to gather information threat actors need to gain access to an organization.
LockBit Dominates Ransomware Ecosystem
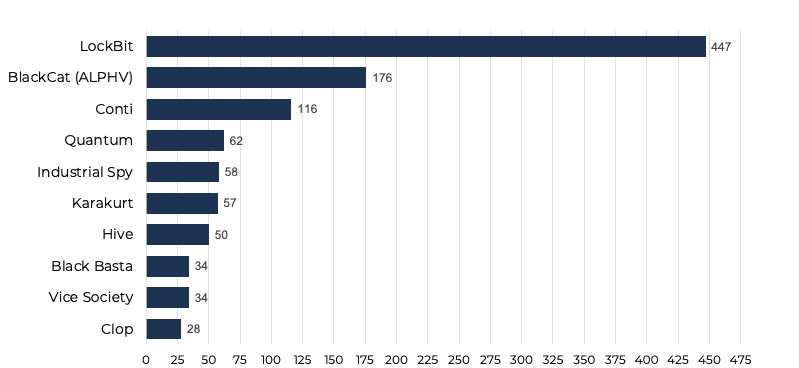
Across Tetra Defense’s cases and all publicly observed attacks by e-crime groups on the dark web, there was a diverse number of threat actor groups observed. While Conti was the dominant threat actor group observed in 2021, the group faced turmoil in early 2021 as it stated its allegiance to Russia in the wake of its invasion of Ukraine and experienced a major leak of its internal chat logs from one of its members. This internal strife has led to Lockbit rising as the dominant threat actor group in ransomware, accounting for more publicly disclosed ransomware incidents than the next three leading threat actor groups (BlackCat, Conti, and Quantum).
Industry Insights: Healthcare Continues to Lead in Incidents
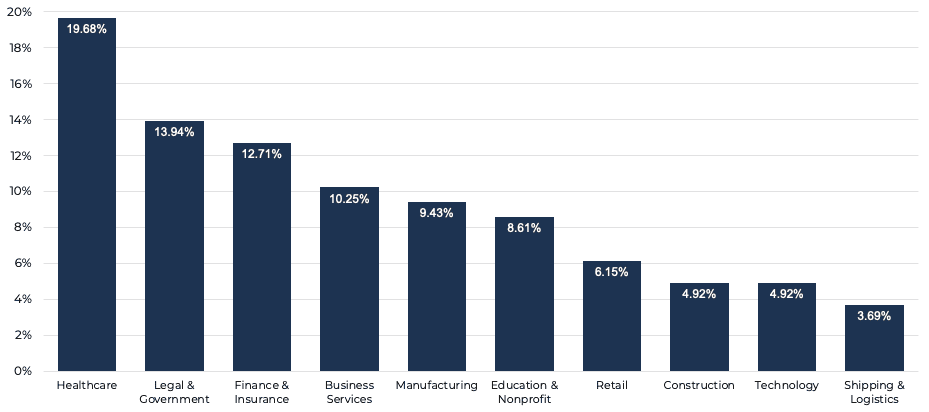
Tetra Defense, Arctic Wolf’s incident response unit, assists organizations with a wide range of cyber risk planning activities, active cyber insurance policies, and varying industry considerations like costly downtime (Manufacturing, Construction, Finance) or even life threatening interruptions (Healthcare). With these wide-ranging industry relationships, so far in 2022, Tetra Defense has responded to incidents across more than ten verticals, with Healthcare, Legal & Government, Finance & Insurance, Business Services, and Manufacturing being the industries that Tetra Defense responded to the most frequently.
The first six months of 2022 were filled with unprecedented international geopolitical strife and economic uncertainty, but even with these global events, threat actors continued cybercrimes against organizations of all sizes.
This first half review of the incident response landscape serves as a way for Arctic Wolf Labs to not only share our knowledge with the security community, but also help inform how we build and enhance our detections to anticipate future tactics, techniques, and procedures. Arctic Wolf works side by side with customers, 24×7, to hunt for activity and deploy new detections—advancing security operations with threat intelligence and analysis to fuel the Arctic Wolf Security Operations Cloud.






