Arctic Wolf and SC Media surveyed an audience of more than 500 North American IT security professionals in the fall of 2023 and discovered that, among those who currently have cyber insurance policies, 47% of them have had coverage for 12 months or less .
A significant increase among the insured reflects the kind of growth one might expect from
an industry that has seen monumental change in just a few short years. In the twelve months between 2021 and 2022, for example, direct written premiums increased 47.6%, to $9.7 billion USD, according to the National Association of Insurance Commissioners.
Clearly, major changes have occurred in the past several years that have drastically altered the cyber insurance landscape. Hyrid and remote work models necessitated new protections for a more mobile workforce. At the same time, ransomware-as-a-service (RaaS) rose to prominence , seizing on remote-access based attacks to help drive the average cost of a data breach to a record-setting $4.45 million USD, according to IBM.
As more organizations seek policies and more cyber attacks raise the potential payouts those policies might be asked to cover, cyber insurers have undertaken significant efforts to right-size the market.
Our survey with SC Media revealed that 48% of those covered say their insurer added new requirements they had to meet to maintain coverage. The good news is that, in many cases, demonstrating these requirements helped customers avoid premium increases or even lower their premiums by some margin.
It’s clear, now barely a decade into the availability of these types of policies, that cyber insurers are committed to rigorously evaluating organizations seeking coverage by their cyber risk profile. But what are those profiles, how are they evaluated, and how can organizations improve theirs to ensure access to the best policies and premiums?
What is a Cyber Insurance Risk Profile?
Like other kinds of liability insurance, cyber insurance is a way for organizations to transfer part of their risk over to an insurance carrier in the event of a cyber incident or breach. Depending on the policy, the carrier may cover costs related to remediation, negotiation, and payments of ransoms, or damages associated with stolen or leaked data. But that risk transfer is not as easy to obtain as it was just a few short years ago, as cyber insurers have sought to create accurate profiles to properly categorize the risk of insuring the organizations seeking their policies.
Through our research and work with insurance partners, we’ve identified three major risk profiles that cyber insurers slot organizations into, which we’ve dubbed:
- Basic
- Premium
- Elite
Slotting into any of these three risk profiles grants an organization access to a cyber insurance policy. However, the policy available to someone in the elite profile tier will provide more comprehensive coverage and a lower policy premium than the policy available to an organization in the basic profile tier.
But just what elements are being evaluated when cyber insurers decide on an organization’s cyber risk profile?
First, cyber insurers are examining the size of the organization’s attack surface, how distributed it is (between on-premises, network, and cloud), the number of employees in the organization, as well as the industry.
For example, the 2024 Arctic Wolf Labs Threat Report revealed that the median ransom demand in the construction industry was $500,000 USD, while in the energy and natural resources sector it was $2 million USD. Threat actors target manufacturers aggressively – they recognize that manufacturers have little tolerance for production downtime – however many manufacturers can maintain production even if incidental or ancillary business systems are temporarily unavailable. In contrast, healthcare organizations are under regulatory pressure to protect the sensitive data they handle, so they may be more inclined to pay a ransom. Similar pressures apply to legal and government organizations. As a result, organizations within these industries are more likely to seek robust cyber insurance. These factors all play a role in determining policy premiums and coverage.
But that’s just the beginning of what cyber insurers look at. The major evaluation occurs when looking at an organization’s security controls — the tools, technology, solutions, and staffing dedicated to proactive cybersecurity. As more organizations seek policies, and as the rate and cost of attacks continue to climb, insurers are expecting more from organizations seeking coverage. They want to see robust efforts being made to protect data, rather than simply relying on insurance to step in and clean up the inevitable mess.
How Security Controls Impact Cybersecurity Insurance Coverage
When it comes to cyber insurance, underwriters are looking at two things when evaluating an organization’s cyber risk: how their existing cybersecurity controls combine to reduce the frequency of an attack and — more importantly — reduce the severity of an attack.
Basic
- Multi-factor authentication (MFA)
- Remote desktop protocol (RDP)
- Virtual private network (VPN)
- Patch management program
- Incident response plan
- System and database backups
Premium
- Endpoint detection and response (EDR)
- Vulnerability / risk management
- Employee security training program
- Privileged account management
- Remote access controls
Elite
- Managed detection and response (MDR)
- Centralized log monitoring
- Email and web filtering
- Asset inventory
- Email and network security
- 1-hour incident response time
- Threat intelligence services
As you can see, the basic profile expects table-stakes security controls that any organization serious about their cybersecurity should have in place. However, even within this basic profile, not all controls are created the same.
For example, to ensure proper backup coverage that not only protects you but satisfies underwriters, it’s best to follow the 3-2-1 principle of file backup, meaning an organization has:
- 3 copies of data (1 primary and 2 backup)
- 2 copies stored (at separate locations)
- 1 off-site storage (ideally in a secure private cloud)
In addition, it’s critical to regularly test backup recovery to ensure they function and are complete. In 71% of Arctic Wolf® Incident Response engagements for ransomware, the victim organization was able to leverage backups in some capacity to restore their environment
In the premium risk profile, insurers are looking for organizations to undertake more proactive measures, including ways to monitor, protect, and quarantine endpoints, a proactive vulnerability management solution, as well as reduce their human risk through training that protects against social engineering attacks like phishing.
To earn the elite risk profile — and, in turn, the most comprehensive policies and affordable premiums — organizations need to go even further, investing in 24×7 monitoring, detection, and response for their entire environment, as well as active engagement with an incident response provider who can mitigate the damage and cost of a cyber attack.
How Organizations Can Elevate Their Cyber Risk Profile for Insurance
Organizations can’t do much about their chosen industry, their headcount, and the reach of their attack surface. If they’re looking to elevate their risk profile, it’s going to have to come through proactive efforts in security controls.
Here are three stats from our report, The Cyber Insurance Outlook, that make this point clear:
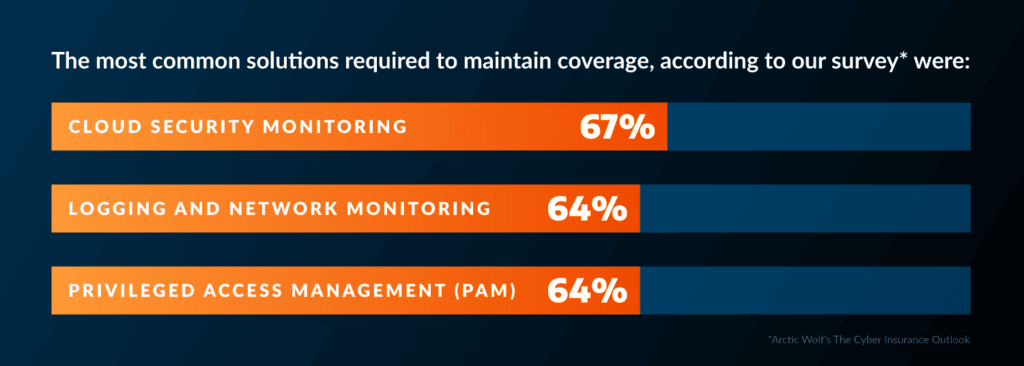
- The most common solutions required to maintain coverage were cloud security monitoring (67%), logging and network monitoring (64%), and privileged access management (PAM) (64%).
- By demonstrating hardening techniques, including Remote Desktop Protocol (RDP) mitigation, nearly half (47%) were able to avoid a premium increase.
- Some respondents saw the biggest reductions to their premiums (at least 15%
- below what they were previously paying) if they could demonstrate PAM (23%), patch management and vulnerability management (20%), or having incident response professional services on retainer (19%).
This is where a good insurance broker partnership can come into play. Brokers should have a strong understanding of how to help an applicant demonstrate the value of their security investments during the evaluation process, and then advise them on selecting the right
coverage based on the applicant’s risk profile.
There are multiple benefits to working with a cyber insurance broker. Brokers can assist applicants in satisfying the minimum requirements for coverage, such as advising them on which tools and protections to purchase. Brokers can also help applicants negotiate their annual premium and get the right coverage.
The reality is that carriers are becoming much more selective about who they insure and renew coverage for, which means that even insured organizations can’t get complacent. Rather, companies need to remain constantly aware of their risk profile and what adjustments
must be made to retain coverage.
Discover how coverage is evolving with the current cyber threat landscape and get insurance insights directly from cybersecurity leaders in The Cyber Insurance Outlook.
Download our Best Practices for Cyber Insurance data sheet and learn the most common controls insurers are looking for, and the five first steps you can take on your way to getting the best policy possible.
Learn more about Arctic Wolf Incident Response and our IR JumpStart Retainer.






