ARCTIC WOLF
Managed Security Awareness®
Ready to get started?
HOW IT WORKS
Content Options
FOR Industry, Roles, Compliance, and More
Activate industry content tracks and supplemental role-based content across a range of highly targeted sectors with highly targeted employees.
Incorporate cutting-edge content into your awareness program with lessons created by security awareness pioneer, Habitu8.
See our data sheet for more details.
Integrate compliance training with your security awareness program. Arctic Wolf enables group-based assignment of 15 compliance courses covering topics including:
-
PCI
-
HIPAA
-
Title IX
-
FERPA
-
Anti-Discrimination
-
Sexual Harassment Prevention
-
Affirmative Action and Equal Opportunity Employment
-
and FMLA
ARCTIC WOLF ARCTIC WOLF
PRESENTS PRESENTS
Managed Security Awareness
Hop in and see for yourself what it’s like to be an Arctic Wolf Managed Security Awareness customer.
You’ll participate in some microlearning sessions, find out what your Concierge Security Team can do for you, and discover how an ongoing program can change your company culture.
OUTCOMES
Improve
Protection
Prepare employees to recognize and neutralize social engineering attacks, like phishing.
Strengthen
Resilience
Empower employees to identify cyber risks and report mistakes that could expose sensitive data.
Achieve
Compliance
Deliver security awareness training for regulatory compliance.

Jinan Budge - Principal Analyst, Forrester
Program
We provide the tools and expertise to develop the behaviors organizations need from their employees for better protection and stronger resilience. With Managed Security Awareness, you can avoid expensive security incidents and data breaches by having employees on the lookout for social engineering attacks, like phishing, and enables employees to report mistakes, or suspicious emails that could result in data loss. Arctic Wolf also watches for employee credentials on the dark web and alerts you when it discovers breaches.
Awareness
Training
-
Employee-centric security microlearning
-
Timely topics and threat vectors covered in each lesson
-
Continuous engagement through gamification without administrative action
Phishing
Simulation
-
Automated testing based on current phishing threats
-
Built-in coaching when employee engages phishing simulation
-
Tracking and reporting for employees and program administrator
Report Phishing Button & Analytics
-
Enables employees to remove and report suspicious emails with the click of a button
-
Reported email details and analysis displayed in admin dashboard supporting faster response to potentially malicious emails
The Arctic Wolf Difference
Recognize and Neutralize Social Engineering Attacks and Human Error
Arctic Wolf Managed Security Awareness enables employees to recognize and neutralize social engineering attacks and human error through microlearning content, automated phishing simulations, and awareness coaching.
Engage
Microlearning
Brief, purpose-driven, frictionless content designed for optimal learning and behavioral adoption.
Leaderboard
Employees earn points based on their participation and engagement in the Managed Security Awareness program. Admins can keep an eye on employee points in the Leaderboard.
Current Threat Vectors
Relevant content informed by real-world threat intel and industry trends.
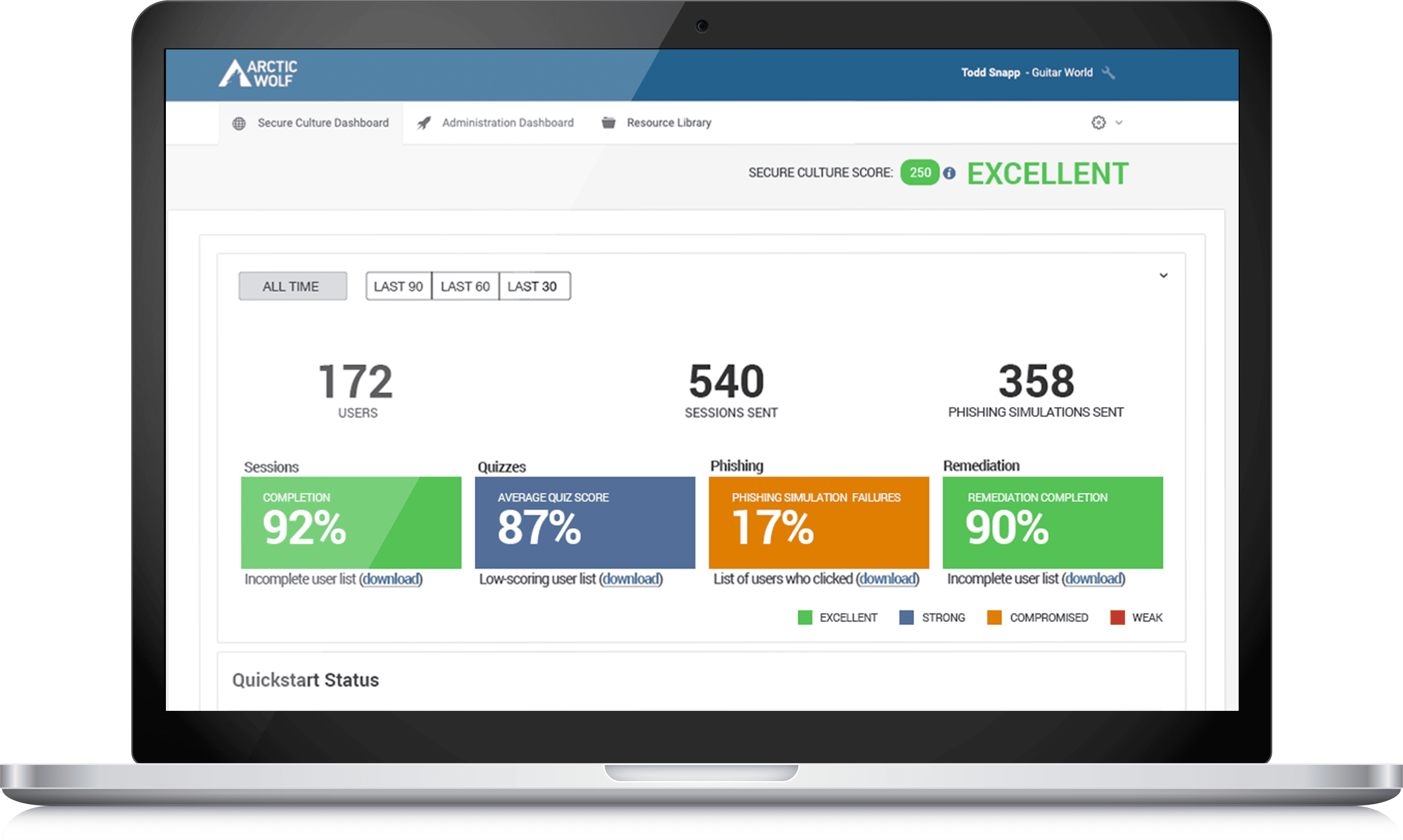
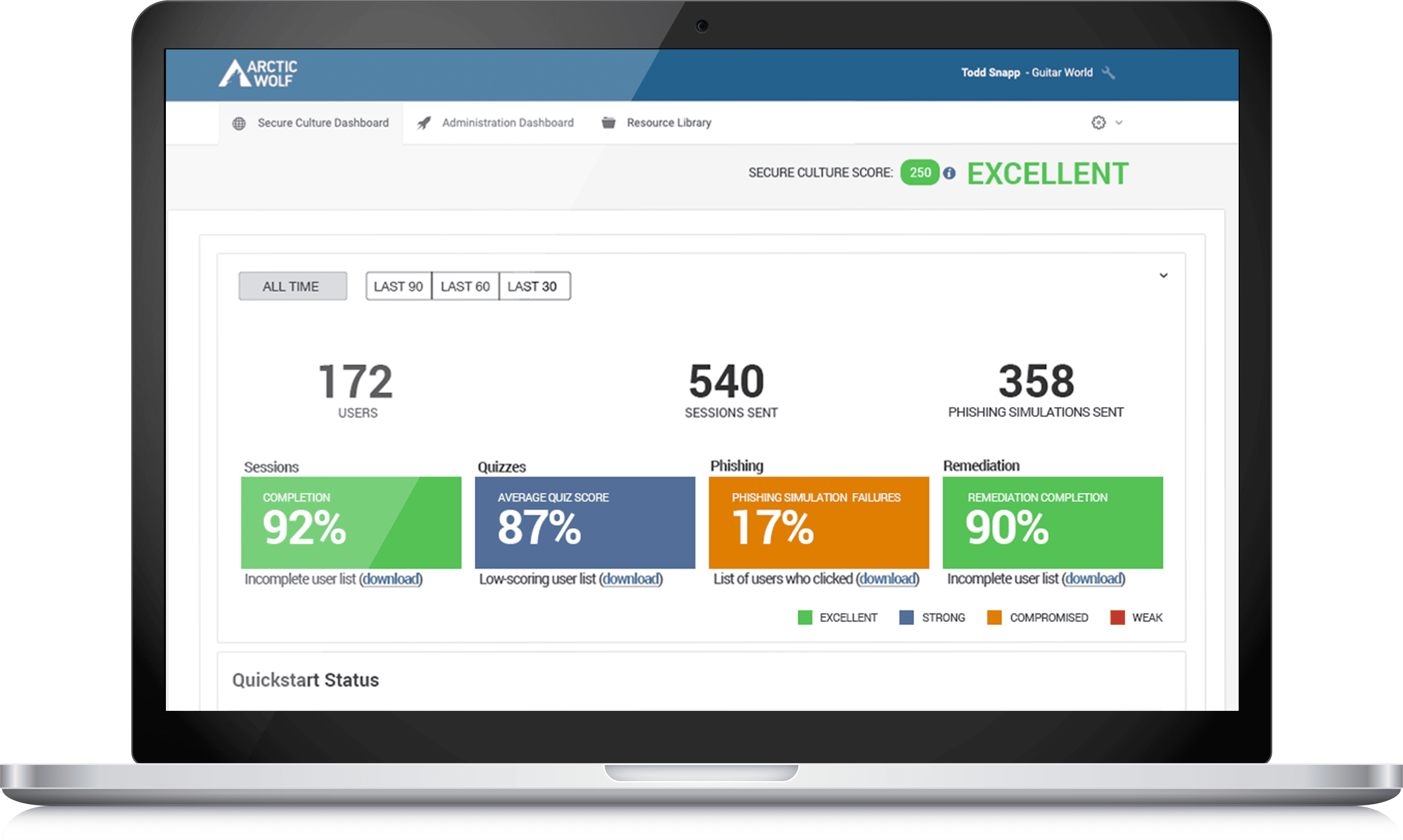
Measure
Employee Performance
Identify employee risk with quizzes, automated phishing simulations, and report cards.
Program Effectiveness
Track and measure your Culture Score based on employee behaviors.
Reported Emails
See your employees do their part to protect their inboxes and your organization by reporting suspicious emails.
Transform
Employee Confidence
Positive reinforcement and guidance to develop security awareness champions.
Security Culture
Peer-to-peer coaching with your CST to advance your awareness program.
Cyber Resilience
Reduce the risk of social engineering attacks with prepared and alert employees.


Arctic Wolf Security Operations Warranty
THE PACK HAS YOUR BACK
Get the industry-leading Arctic Wolf Security Operations Warranty with $1,000,000 in financial assistance for cybersecurity incidents when you purchase MDR, Managed Risk and Managed Security Awareness together.
Awareness
Prepare, launch, and run your awareness program focused on outcomes.
Behavior
Drive individual and organizational progress toward desired behaviors.
Culture
Transform employees to be 24x7 cybersecurity champions.
A fully managed, ongoing security awareness program that utilizes microcontent, quizzes, and phishing simulations to give you confidence that your team is equipped to defend themselves and your organization from social engineering threats. The backbone of this program is the Concierge Security Team, who proactively monitors your organization’s progress and coaches you on educating your people and helping them grow into cyber resilient employees.


Watch Lessons
Our in-house developed content includes current events and cyber threats to make lessons more relatable, memorable, and meaningful. Our content is designed to get better engagement from employees to always keep awareness top of mind.


Arctic Wolf Managed Security Awareness®: The Mission | 47sec


Staying Secure on Vacation | 2m 49sec


Now What? Consequences of a Data Breach | 3m 00sec
WHAT OUR CUSTOMERS SAY
Jon Armstrong,
Director of IT & Security, Fullsteam

Ready to Get Started?
We’re here to help. Reach out to schedule an introductory call with one of our team members and learn more about how Arctic Wolf can benefit your organization.
General Questions