THE BIG BU$INE$$ OF
CYBERCRIME
Cybercrime has become a big business – an entire ecosystem of organizations run just like yours. Keeping up with the players, weapons, and enemies can feel like a free-for-all action game. To fight back, we need to understand that world and its key actors and methods.






How big is the cybercrime business?
The $1.5 Trillion Dollar Cybercrime Industry
- #1
- $1B
- 3X
- $6.9T
-
#1
#1 Global Business Risk
Allianz Risk Barometer 2025 lists cyber incidents as the #1 global business risk, above business interruption and natural disasters.
-
$1.5T
$1.5 Trillion in Annual Revenue for Cybercriminals.
According to the FBI, Cybercriminals earned $16 billion in annual revenue with $1 billion in 2024.
-
17X
17X Greater Gains Compared to Largest U.S. Company
Cybercrime totals $12 trillion in annual damages. Walmart’s income reached $681 billion in 2024. In comparison to Walmart, cybercrime enjoys over 17 times greater gains.
Source: Arctic Wolf
Cybercrime
$12T/yr
Walmart
$572B/yr
-
$12T
$12 Trillion in
Annual DamagesMeasured as a country, cybercrime would be the world’s third-largest economy after the U.S. and China with inflicted damages totaling $12 trillion USD globally by 2025.
Source: Statista Technology Market Outlook, National Cybersecurity Organizations, FBI, IMF-
United States$20.9T
-
China$14.7T
-
Cybercrime$12T
-
THE BUSINESS OF cybercrime IS SHIFTING
Exposing the Ecosystem
As organized cybercrime entities join forces—forming groups and organizations—Arctic Wolf® is shedding a light on the full extent of the online cybercriminal ecosystem that enables these attacks, their business models, and the bad actors targeting your organization.
Cybercrime in Action
Ransomware as a Service (RaaS)
What is RaaS?
Ransomware-as-a-Service (RaaS) is the commercialization and commodification of ransomware where individuals or ransomware gangs sell ransomware tools to affiliate groups for use.
Attack Method
In these kinds of attacks, the ransomware is purchased by affiliate groups from developers or ransomware gangs and then deployed. The developer usually takes a cut of the profits as well.
Ransom Payments
In late 2020, Darkside, a ransomware gang, announced the launch of their own affiliate program in an effort to maximize revenue. They announced details of the program on two major Russian cybercrime forums: they would provide a crypto-locking malware code with a unique ID embedded for each affiliate.
For every victim that pays a ransom, the affiliate shares the take with the ransomware operator taking anywhere from 10-40% of the ransom payment.

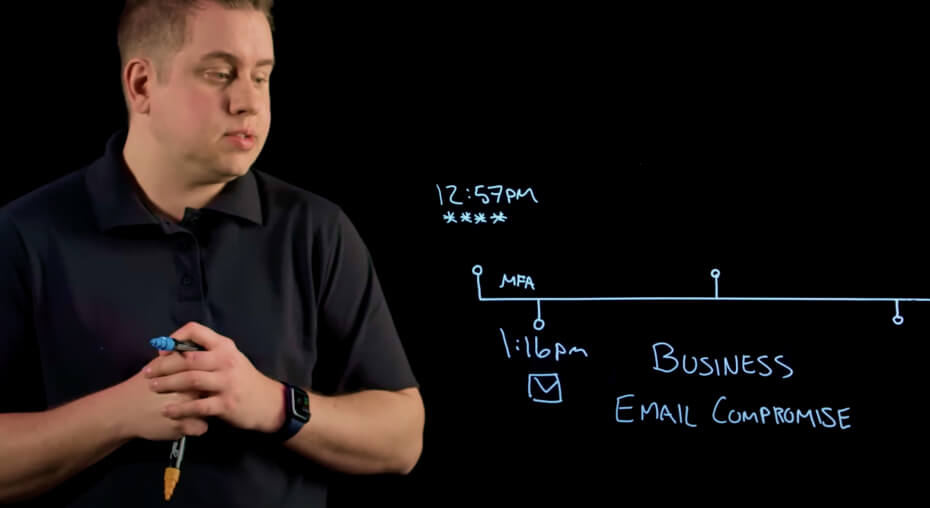
See how effective our response timeline is when a ransomware attack happens.
Cybercrime in Action
Business Email Compromise (BEC)
What is BEC?
Business email compromise (BEC) is the tactic of spoofing and taking over email addresses.
Attack Method
BEC attacks can come in various forms – from attackers positioning themselves as the CEO requesting an emergency fund to acting company suppliers and requesting fund transfers to fraudulent accounts.
Cybercriminals deploying BEC attacks target employees up and down the corporate ladder.
Fueled by Payouts
In August 2021, officials in Peterborough, NH were scammed out of $2.3 million in a BEC scheme. Bad actors outside the country had sent two separate emails over a period of several weeks, purportedly representing the local school district in one case and a construction contractor in the other. Each netted more than $1 million.
Cybercrime in Action
Zero-Day Exploits Market
What is the Zero-Day Exploits Market?
The commercial activity of trafficking software exploits.
Attack Method
Since Zero-Days are flaws or loopholes already present in the system in place, it makes the attack more reliable and sophisticated. They are undetected until the day they are released and therefore can be exploited while staying under the radar, which makes them highly effective for threat actors.
Making Money from Vulnerabilities
Zero-day vulnerabilities can be used in several ways to make money. Initial cybercriminals seek out and discover these vulnerabilities within vendor systems and turn around and sell the zero-day threats to threat groups at expensive rates.
Threat actors who have access to these threat in turn use zero-day vulnerabilities to steal data and request large sums through a ransomware attack in order stop the release of this data.
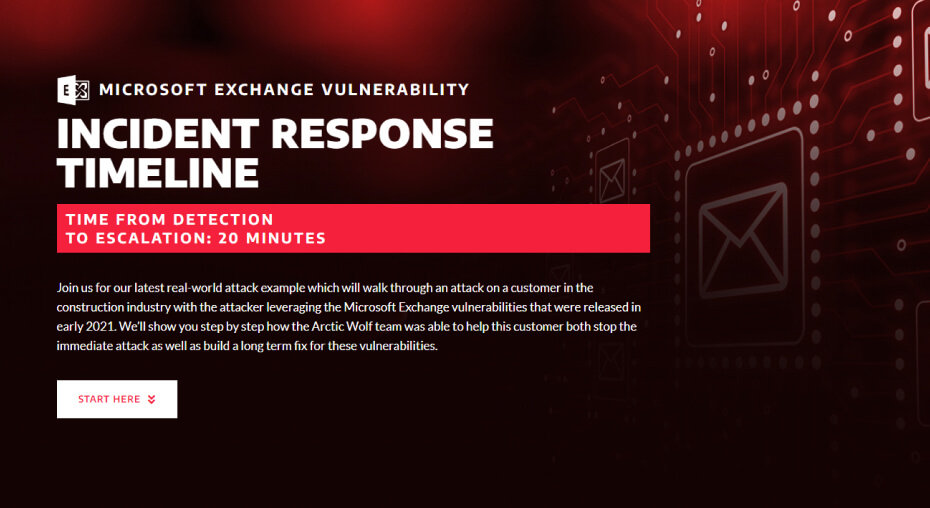
Explore an example of the Microsoft Exchange Vulnerabilities exploit in action and how it was resolved before damage could be caused.
WHO TO LOOK OUT FOR
Meet the Players
While there are many cybercriminals out there, these are the six key threat actor groups to look out for.
CYBERCRIMINAL
THREAT
ATTACKER
OPERATOR
SPONSORED ACTOR
HACKERS










ALL ABOUT THE BENJAMINS
They want access to personal, financial, or health data in order to sell it on the dark web. For the retail sector, the stolen data from these hacks typically appears on the black market within days of the theft.
Cybercriminals operate behind anonymous peer-to-peer networks, using encryption technologies and digital currencies to hide their communications and transactions.
Depending on the attack type, they may work solo or as part of an organization, but they often have relationships with each other.
CHARACTERISTICS
REAL-LIFE EXAMPLES
TECHNIQUES
-
Phishing
-
Social engineering
-
Business email compromise (BEC)
-
Malware
-
Ransomware
-
Remote access trojans
Targets
-
Large cash
-
Data-rich enterprises
MOTIVATORS
-
Financial gain/profits
Business Model & Financing
Provide Ransomware as a service (RaaS), extract ransoms from targets. Usually paid in decentralized currencies / crypto / other digital assets.
IMPACT TO GLOBAL ECONOMY
Cybersecurity Ventures expects global cybercrime costs to grow by 15 percent per year, reaching $10.5 trillion USD annually by 2025, up from $3 trillion USD in 2015.


WORKING FOR AND WITH GOVERNMENTS
Nation-state attacks are originated and executed by entities working for and with the approval of a government against another government. A true force to be reckoned with, these attackers can cause unparalleled damage. They are often backed by substantial financial, technical, and material resources.
They’ve been known to exfiltrate data, steal sensitive information, and redirect funds as part of national espionage programs. Their goal is to spy on or steal from businesses or governmental bodies in order to further the interests of their nation.
CHARACTERISTICS
REAL-LIFE EXAMPLES
TECHNIQUES
-
Custom malware
-
Zero-day vulnerabilities
-
Hidden malware
-
Ransomware
-
Quieter tactics
Targets
-
Government
-
Military
-
Corporations
MOTIVATORS
-
Political
Business Model & Financing
Works as an unofficial extension of a federal government, financed by 3rd party contracts or undisclosed state funding.
IMPACT TO GLOBAL ECONOMY
In the United States alone, the value compromised information due to international hacking is estimated between 25 billion and 100 billion
dollars annually.
Global espionage is occurring all around the world, and although the size of the damage varies, the effects are generally the same. China currently receives about 13% of all cyber attacks globally.


SOPHISTICATED AND ALONE
A large number of individuals in the cybercrime world hack computers just because they can. They’re known as Black Hat Hackers or Rogue participants, and they always break into networks and systems with malicious intent. They may also insert malware, conduct ransomware attacks, or steal data like credentials, financial data, or other personal information.
Black hats are motivated by self-serving reasons, such as financial gain, revenge, or simply to spread havoc. Sometimes their motivation might be ideological, by targeting people they strongly disagree with.
Black hat hackers often develop specialties, such as phishing or managing remote access tools. They find their jobs through the dark web, develop and sell malicious software themselves, or work as a contractor through franchises or leasing arrangements.
CHARACTERISTICS
-
-
-
-
Business Risk
REAL-LIFE EXAMPLES
TECHNIQUES
-
Customized codes/scripts/ penetration testing
-
Custom malware
-
Zero-day vulnerabilities
-
Ransomware
-
Phishing
Targets
-
All Organizations
MOTIVATORS
-
Financial motivation
-
Revenge
-
Entertainment
Business Model & Financing
Financial motivation, revenge or simply for entertainment.
IMPACT TO GLOBAL ECONOMY
Similar to novice attackers, it is hard to trace the total global impact of lone Black Hat hackers, but global cybercrime is expected to grow by 15 percent per year over the next five years, reaching $10.5 trillion USD annually by 2025.


THE THREAT’S COMING FROM INSIDE THE ORG
Insider threats are bucketed into two categories – those who unintentionally make mistakes opening up their organization to attacks, and those who maliciously take advantage of privileged access in effort to harm the company.
In cases when employees turn against employers, the impact can be devastating on a business and their security. Additionally, certain threat actors will infiltrate a workforce, express grievances via criminal activity, or turn insiders towards their cause with the promise of financial reward. This is a malevolent threat, given that the insiders they turn have privileged access. Disgruntled former employees are an especially tempting target for organized cybercriminals looking to gain easier access to an organization.
CHARACTERISTICS
REAL-LIFE EXAMPLES
TECHNIQUES
-
Privileged insider access to systems and networks
Targets
-
Disgruntled employees
MOTIVATORS
-
Revenge
-
Monetary gain
-
Competitive advantage
Business Model & Financing
The insider could be disgruntled and looking to exact revenge on their former employer by inflicting maximum pain. They may also be compromised or blackmailed by an outside threat actor using them to help hack your organization.
IMPACT TO GLOBAL ECONOMY
The latest research from the Verizon 2021 Data Breach Investigations Report, suggests that insiders are responsible for around 22% of security incidents.
Overall, the average global cost of insider threats has increased 31% over the last 2 years, from $8.76 million in 2018 to $11.45 in 2020 and the largest chunk goes towards containment, remediation, incident response, and investigation.

IT’S FUN TO DO BAD THINGS
Novice attackers they are usually younger people who acquire hacking tools built by more talented hackers.
They may often be unsophisticated, highly visible, and impulsive with their attacks. Despite their name and lack of depth of knowledge, many of these threat actors can still be dangerous. Companies that haven't taken basic security precautions are a prime target.
Some novice attackers may also begin to sell their services to others, contracting out their services to larger criminal organizations in an effort to make money off their hobby. They do not always realize the seriousness of the organizations they are contracting for, they’re simply motivated by the entertainment and monetary gain of their “hobby.”
CHARACTERISTICS
REAL-LIFE EXAMPLES
TECHNIQUES
-
Purchase existing ransomware services
-
Purchase off-the-shelf exploits
-
Social engineering
Targets
-
Organizations with weak spots or easy vulnerabilities
MOTIVATORS
-
Entertainment
-
Small financial gains
-
Notoriety
Business Model & Financing
May be interested in low-level ransoms or simply doing it for fun.
IMPACT TO GLOBAL ECONOMY
It’s difficult to quantify the global impact of novice hackers. What we do know is that based off where they reside, these "amateur" hackers often face little or no legal consequences.

WHEN THE BAD GUYS TEAM UP
Cybercriminals intent on conducting a ransomware attack often buy or rent the ransomware code from other cybercriminals who write and deploy the malicious code through an affiliate program. The ransomware operators provide technical leadership and step-by-step instructions on how to launch the attack. Some RaaS setups are even equipped with a platform that allows both parties to view the status of the attack on a real-time dashboard.
These attackers are so brazen that they even advertise their RaaS on the dark web, much like cybersecurity companies promote their services and solutions as pop-up ads on numerous websites.
There are four common RaaS revenue models: monthly subscription for a flat fee; affiliate programs, which are the same as a monthly fee model but with a percent of the profits (typically 20-30%) going to the ransomware developer; one-time license fee with no profit sharing; pure profit sharing.
CHARACTERISTICS
REAL-LIFE EXAMPLES
TECHNIQUES
-
Ransomware
-
Malware
Targets
-
Large cash
-
Data-rich enterprises
MOTIVATORS
-
Financial gains
Business Model & Financing
When a RaaS attack is successful, the ransom money is divided between the provider and the attacker. For the involved parties, it’s a quick buck through an attack that’s hard to trace, while the authors of the code rake in even more cash when they roll out these pre-packaged digital schemes to multiple attackers.
IMPACT TO GLOBAL ECONOMY
The ransomware business model generates a staggering amount of money for cybercriminals. Like we said earlier, RaaS is a business — and business is booming. According to reports, total ransomware costs are expected to exceed $20 billion in 2021. And as cybercrime tends to beget more cybercrime, that’s a figure that will only increase.
LEVEL UP
Going Deeper with Incident Response Insights from Arctic Wolf Labs
-
Threat Actors:
The Usual SuspectsAcross insights generated by Arctic Wolf’s Incident Response team and all publicly observed attacks by dark web groups, there was unsurprisingly a diverse number of threat actor groups.
-
Industry Insights:
Healthcare Leads in IncidentsIn Q2 2022, Arctic Wolf’s Incident Response team responded to incidents across twelve different verticals, with Healthcare, Finance & Insurance, Legal & Government, Business Services, and Manufacturing being the most frequent industries affected.
-
User
ExploitationIn Q1 2022, the vast majority — 81% — of total incidents happened through external exposure of either a known vulnerability on the victim’s network or a Remote Desktop Protocol (RDP).

January — June 2022
Incident Response Insights from Arctic Wolf Labs
Insights generated by Arctic Wolf’s Incident Response team highlights the most targeted industries, the root point of compromise, the primary vulnerability exploits that opened the door for attack and key threat actor groups.
DOWNLOAD THE REPORTWHY IS THIS IMPORTANT?
Cybercrime
is a Lucrative Industry
As long as there is money, attackers will continue to attack, grow their businesses, and improve their strategies to siphon money from organizations.
How Much Money is There?
In 2022, data breach costs rose from $3.8 million to $4.2 million, the highest average total cost in the 17-year history of this report.
What Can I Lose?
As cyber attacks continue to evolve, their direct and hidden costs of data breaches continue to grow.
Calculate the Cost of a Breach
Use our Cost of a Breach Calculator to estimate how your organization may be affected financially by a cyber incident.
TRY OUR COST OF BREACH CALCULATORGAME OVER
Defeat Threat Actors with Arctic Wolf
Cybercriminals are looking for easy targets with large cash flow – making money with the least amount of effort. At Arctic Wolf, we work with each of our customers to provide 24×7 monitoring of your networks, endpoints, and cloud environments to help you detect, respond, recover and prevent modern cyber attacks.
Request a DemoAdditional Resources

The Big Business Of Cybercrime

Investigating the Big Business of Cybercrime