Cybersecurity is a journey full of fresh challenges.
Cybercrime is increasing at an alarming rate, endpoint detection and response (EDR) is no longer enough to secure a complex IT environment, and organizations are struggling with skills gaps, cloud security, and obtaining comprehensive solutions that meet the mark without breaking the bank.
Building and operating an in-house security operations center (SOC) and utilizing a SIEM alongside it is an option. However, there are two other security options an organization may consider that allow them to achieve the benefits of an internal SOC without spending the capital or resources needed for internal operations.
Those two are:
- Managed security services providers (MSSPs)
- Managed detection and response (MDR) solutions
Each service is unique and has its own advantages and disadvantages. Each plays a different role in the cybersecurity space, but which is the right solution for your organization?
What Is a SIEM?
As the name implies, SIEM combines security event management (SEM) — which monitors, gathers, analyzes, and correlates log and security or event data in real time — and security information management (SIM), which provides more of a historical, long view of the log data, as well as reporting functions.
The SIEM is often considered the cornerstone of a SOC, as the solution helps security teams monitor their environments and respond to threats.
What Are the Advantages of a SIEM?
There are a few reasons why, back in 2015, the SIEM was the fastest growing security segment. Advantages of a SIEM include:
- Collecting, aggregating, and storing data from a variety of sources
- Offering control and flexibility over the ingestion sources
- Rule creation capabilities that specify normal behavior for all the systems, allowing the SIEM to automatically find anomalies and create alerts
- Compatibility with typical compliance reporting for regulations such as HIPAA, PCI, and others
While having this ability to quickly collect data from various sources and display it on a single pane of glass is valuable for security, the SIEM is no longer the fastest-growing security segment for a reason. While a SIEM is still a security mainstay for countless organizations, its effectiveness for threat detection and response is hampered by several factors.

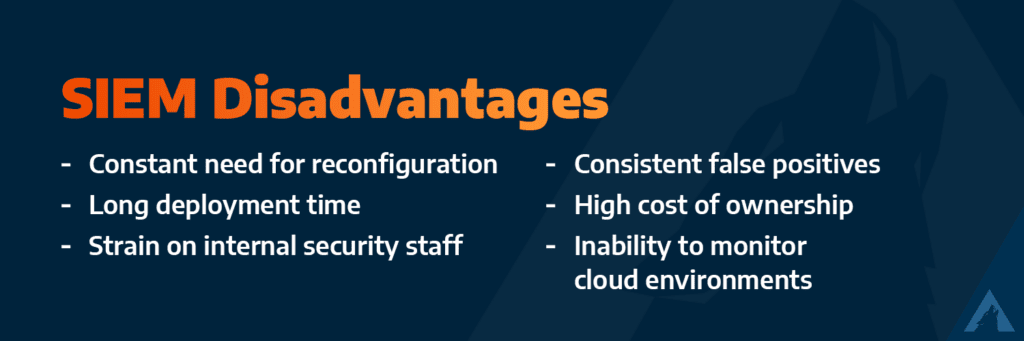
What Are the Disadvantages of a SIEM?
The disadvantages of a SIEM include:
- Constant need for reconfiguration due to SIEM’s ruled-based functions. This is both challenging, resources intensive, and can lead to missed threats.
- A long deployment time, which on average takes six months to a year. This includes the time needed by security engineers to set new rules and disable preconfigured correlations.
- Strain on your internal security staff during deployment and management.
- Consistent false positives that will occur without correct correlations.
- High cost of ownership due to expertise and time needed for deployment and management.
- Inability to monitor cloud environments due to SIEM’s traditional design as an on-premises solution.
Discover How To Define and Optimize Your Relationship With Your SIEM in our new guide.
Should Your Organization Employ a SIEM Solution?
While SIEMs are great for data aggregation, event correlation, compliance and IT troubleshooting — and do help with threat detection — these solutions can be complex, labor-intensive, expensive, noisy, and limited in insights. They require continuous tuning and updates for new threats, which can be difficult for organizations that lack skilled staff or other resources.
In short, a SIEM is only as effective as the people managing it. A SIEM has its place as a data ingestion tool in a SOC, and will for the foreseeable future, but it lacks the ability to perform meaningful analysis that will reduce false positives or allow for advanced threat detection and mitigation without significant operational maintenance. It’s no longer enough by itself.
Organizations should take a step back and ask themselves why they want to deploy a SIEM solution to solve security challenges and if there are more effective ways of achieving their security goals. Staffing is a key component organizations should consider in this decision-making process. If your organization contains an in-house SOC team, then a SIEM can be a strong tool for them. If not, however, then the cost and resources needed for a SIEM may not be worth the outcome.
What Is A MSSP?
MSSPs are IT security providers that monitor, maintain, and manage security for individual organizations. Some organizations outsource all their security functions to MSSPs, while others use a provider to supplement their in-house capabilities and bridge gaps. Managed security services are an increasingly popular option for a simple reason: They provide an efficient, subscription-based security model.
MSSPs are NOT MSPs. An MSP offers broader IT and infrastructure operations, which may or may not include cybersecurity. An MSSP is dedicated exclusively to cybersecurity.
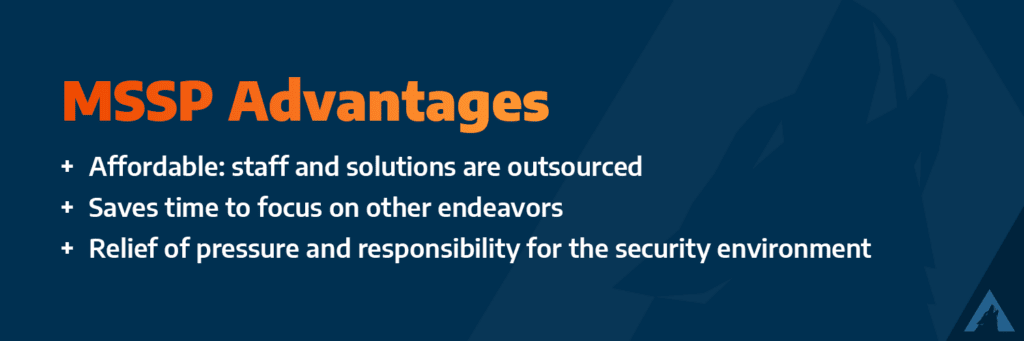
What Are the Advantages of A MSSP?
A MSSP can sound attractive to an organization that’s struggling with staffing and resources. Advantages of an MSSP model include:
- Predictability with outsourced staff and solutions
- Saved time that can be focused on other endeavors
- Relief of both pressure and responsibility for the security environment
While passing on all the work to another organization can be beneficial, especially for SMBs, lack of authority also means your organization has a lack of control over how the security environment is managed.
What Are the Disadvantages of A MSSP?
MSSPs can bring value to your security posture, but only if they fill a gap in your existing IT ecosystem — something that’s difficult to assess without independently evaluating the capabilities of the vendor.
Disadvantages of utilizing an MSSP include:
- A lack of control over the provider’s security portfolio, which can introduce risk
- A lack of personalized support
- Few offer incident response or post-breach support
- Limited scope of capabilities that can exclude triage and response
- A lack of visibility into your organization’s security environment

Should Your Organization Employ A MSSP?
MSSPs are a cost-effective way to augment your in-house capabilities and alleviate the security talent gap. The lack of personal support, lack of compliance support, and poor visibility, however, adds new risks.
If your organization is small or short on budget or resources, utilizing an MSSP may be a great way to augment your security and take care of some of those responsibilities. But, when it comes to scaling and improving your security posture in the long run, you may need to reevaluate that relationship and offerings.
In addition, an MSSP is not a replacement for a SOC. While your MSSP may have a security expert managing a set of point solutions for you, these tools are still just that: tools. You won’t get a premium security service that helps you elevate your threat detection and incident response capabilities.
SIEM vs. MSSP
The best way to think of a SIEM and a MSSP is that the SIEM is the tool and an MSSP are the people, and it’s possible for an organization to employ both. The SIEM will gather all the data and the MSSP will manage it and create security alerts based on the aggregated data the SIEM provides. This is often referred to as a hybrid SOC model.
In addition, while a SIEM may be a good fit for a large enterprise with an internal SOC, an MSSP may be better for a smaller organization, like an SMB, that lacks capital and resources for internal management, or even a larger organization that has limited IT resources or desires an MSSP to manage certain repeatable IT tasks.
Now that those two solutions are clear, it’s time to introduce a third that takes the capabilities of both a SIEM and an MSSP and elevates them: MDR.
What Is an MDR Solution?
MDR is a type of security service that offers customers 24×7 continuous threat monitoring of their IT environment, including events, logs, suspicious activity, and alerts. MDR is not synonymous with a managed SIEM service, nor is it a replacement for a SIEM.
Rather, MDR’s defining feature is the provided team of SOC analysts that monitor an organization’s environment. They act as extensions of the customer’s IT and security teams, performing real-time and continuous monitoring, incident response, vulnerability scans and assessments, compliance management and reporting, and provide regular reports on the state of the organization’s security posture.
MDR solutions are also gaining popularity across industries. Gartner predicts that 50% of organizations will utilize an MDR solution by 2025, and 40% of mid-sized organizations will use it as their only solution by 2024. It’s becoming a must-have in the security toolbox.
What Are the Advantages of a MDR Solution?
By combining a security platform with the human element, an MDR solution can enhance what’s offered by a SIEM in a few ways. Advantages of MDR include:
- Human-led AI detections created by the combination of human expertise, data, and advanced event analysis
- Threat response
- Ability to work with MSSP and MSP providers
- High-quality alerts that can be more accurate and actionable compared to SIEM alerts
- Strong reporting

MDR vs. MSSP
The main difference is that MDR is a full-service solution, and an MSSP is a vendor that facilitates a solution. In a co-managed situation, an MSSP will manage customer’s tools on their behalf, while the MDR side monitors data from those tools to triage and alert customers of threats. The two also diverge when it comes to incident response. Incident response is often a separate service and retainer when it comes to MSSPs.
However, many MDR companies offer different incident response levels as part of their fee structure. MDR solutions, as the name suggests, also respond to alerts raised, which can stop a problem before it turns into a high-severity incident or breach.
MDR vs. SIEM
As mentioned above, MDR is not a replacement for a SIEM. It’s instead a layer on top that provides better visibility, stronger coverage, and security posture improvement. While a SIEM can inform an organization about their attack surface, an MDR solution can actively harden attack surfaces by identifying threats and remediating them before threat actors can exploit them. Some MDR solutions even provide threat hunting, which combine automated tools with human analysts to track unknown threats.
Should Your Organization Employ a MDR Solution?
MDR provides the cost efficiency of an MSSP, the on-demand expertise of an in-house SOC staffed by security experts, and a significantly enhanced version of a SIEM. It’s a more holistic approach that improves your security posture. MDR offers personalized service by a dedicated team that understands your business and environment plus better technology, proactive capabilities, and greater cost savings compared to an in-house SOC.
From a proactive and reactive position, MDR solutions allow organizations to detect, respond, and recover with ease. They are also on the cutting edge of technology while utilizing the innate ability of human experts to detect, understand, and respond to unusual or unseen threats.
Learn How To Define and Optimize Your Relationship With Your SIEM with our guide.
Explore how an MDR solution can help your organization’s security posture with A Security Leader’s Guide to Leveraging MDR for Security Maturity and Development.






