Inside of every businesses’ core infrastructure lies routers, switches, firewalls, active directory services, email servers, etc., all of which are shipped out-of-the box with default configuration settings built for speed and ease of deployment.
But not for security.
Over time, these configurations start to drift due to poor workflows, processes, lack of monitoring, employee turnover, or the devices in the environment just flat-out forgotten. This creates serious gaps in security posture that can lead to attacks causing significant downtime, financial loss, or data exfiltration.
To help organizations become better positioned, the Center for Internet Security has published a set of 140+ configuration guidelines to follow that are developed through a community of global cyber security experts.
These configuration guidelines provide recommendations for various technology groups and security approaches to harden a company’s security posture and policies.

As monitoring and implementing the more than 140 controls is a daunting task, to narrow it down even further, the CIS publishes a list of the top 20 critical security controls that are divided into three categories:
- Basic
- Foundational
- Organizational
Addressing even just the first five controls of the CIS Top 20 can reduce overall cyber threat risk and impact by more than 85%.
To provide continuous value to customers, Arctic Wolf recently added the Security Controls Benchmarking capability to the Managed Risk solution. This capability provides enhanced scanning coverage that goes beyond simple vulnerability management to help customers better identify gaps in security posture that arise from system misconfigurations and configuration drift.
Delivered as part of host-based vulnerability assessment feature, Arctic Wolf regularly scans customers’ environments against the critical security controls and sub-controls and provides reports on the configurations that have passed or failed the scan based on the configuration criteria.
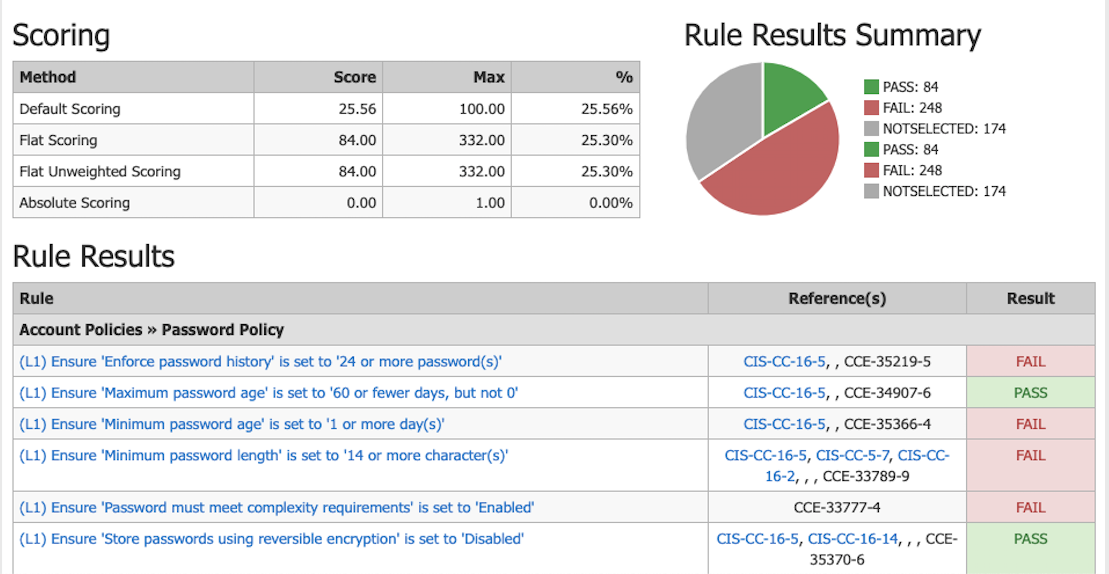
Arctic Wolf Concierge Security Team includes the results from Security Controls Benchmarking scans with regular executive summaries and scheduled Managed Risk reviews. The benchmarking scan results can also be quickly accessed within the Managed Risk Dashboard which includes details on what controls earned a, “Pass” and which earned a “Fail”—including additional insight into the control itself, as well as a recommended fix.
Sample Security Controls Benchmarking Scan results:
This is a unique capability included within the Arctic Wolf Managed Risk solution that extends digital risk coverage beyond simple vulnerability management. System misconfigurations are not software defects and as such, represent critical cyber risks that go undetected that simple vulnerability management products miss 100% of the time.
To learn more about the CIS Top 20 Critical Security Controls, with full, in-depth rundowns, along with information on Arctic Wolf can help you implement and meet these guidelines, download the full white paper.
Here’s an exclusive look at the first control to help get you started.
CIS CONTROL 1: INVENTORY AND CONTROL OF HARDWARE ASSETS
Actively manage (inventory, track, and correct) all hardware devices on the network so that only authorized devices are given access, and unauthorized and unmanaged devices are found and prevented from gaining access.
Organizations of every size struggle with the challenge of managing complex, dynamic network environments. Compound that with devices that rapidly go on and off the network such as laptops, and the task of inventorying and categorizing network assets becomes increasingly difficult. Attackers are located all over the world and continuously scan the address space of target organizations, waiting for new and exploitable systems to be attached to the network.
Even devices that are not visible from the Internet can be used by bad actors who have already gained internal access and are hunting for internal attack points or victims.
Managed control of all devices also plays a critical role in planning and executing system backup, incident response, and recovery. If you can’t see it, you can’t protect it—that’s why active inventory management is a basic first control. When it comes to security, many IT and security professionals don’t know what they don’t know and must first determine what assets are on the network in order to implement controls to protect them.
Taking inventory to categorize assets in the IT environment allows IT managers to ensure only authorized devices have access to critical systems, and unauthorized ones are quickly identified and prevented from gaining further access. Doing so can significantly reduce insider threat and loss risks, clean up the IT environment, and improve the other CIS Critical Security Controls.
Implementation Considerations:
Successful implementation often requires bridging existing system inventory or configuration management services
with host-based network access control. The inventory management portion is typically based on software or endpoint management services such as the Arctic Wolf Agent, while access control can leverage existing network technology to limit device access to networks.
Other points to consider:
The cost benefit is high when deploying these tools because it allows smaller IT teams to quickly have a major impact on their network. They can:
- Utilize an active discovery tool to identify devices connected to the organization’s network and update the hardware asset inventory accordingly.
- Maintain an accurate and up-to-date inventory of all technology assets with the potential to store or process information. This inventory includes all hardware assets, whether connected to the organization’s network or not.
For the other 19 controls, featuring helpful figures and implementation considerations, download the full white paper.
And for more information on Arctic Wolf’s leading SOC-as-a-service, Managed Detection and Response, Arctic Wolf Agent, or Managed Risk, visit arcticwolf.com.





