In today’s interconnected world, the reliance on secure file transfer software is paramount for businesses dealing with sensitive data. Among these tools, MOVEit Transfer software has been a popular choice worldwide, especially in the US, to ensure secure file transfers. However, recent events have exposed its vulnerabilities, leading to the active exploitation by the CI0p ransomware group. In this blog post, we’ll delve into the impact of CI0p’s activities, the industries and regions most affected, and the importance of securing vulnerable systems.
The Critical Vulnerability and Security Bulletins on MOVEit Transfer
CVE-2023-34362 was initially exploited as a zero-day by Cl0p before it became known and became the entry point for CI0p’s exploitation. This vulnerability affected all versions of MOVEit Transfer software, including end-of-life versions, via both HTTP and HTTPS. Recognizing the severity of the situation, Arctic Wolf Labs released the initial security bulletin on CVE-2023-34362.
Later in June, more MOVEit vulnerabilities were disclosed, and Arctic Wolf Labs published bulletins to address other vulnerabilities, including CVE-2023-35036, CVE-2023-35708, and CVE-2023-36934, offering guidance to secure the software.
According to Arctic Wolf Labs’ guidance, our Concierge Security Teams (CST) followed up with the at-risk organizations and urged them to apply security patches. If organizations weren’t able to apply patches, CSTs offered organizations workarounds to protect them from exploitation.
Here are all the security bulletins that available regarding MOVEit vulnerabilities:
- https://arcticwolf.com/resources/blog/cve-2023-34362-moveit-transfer-sql-injection-vulnerability-actively-exploited-in-the-wild/
- https://arcticwolf.com/resources/blog/new-vulnerabilities-similar-to-cve-2023-34362-identified-in-moveit-transfer-and-moveit-cloud/
- https://arcticwolf.com/resources/blog/cve-2023-36934/
The CI0p Ransomware Group
CI0p ransomware group – first identified in February 2019 – has been confirmed as the perpetrator behind the MOVEit Transfer exploitation. The group follows the common tactic of “naming and shaming” victims by posting company profiles on their leak site to coerce them into paying the ransom. According to their claims, their threats were far-reaching, affecting hundreds of businesses globally.
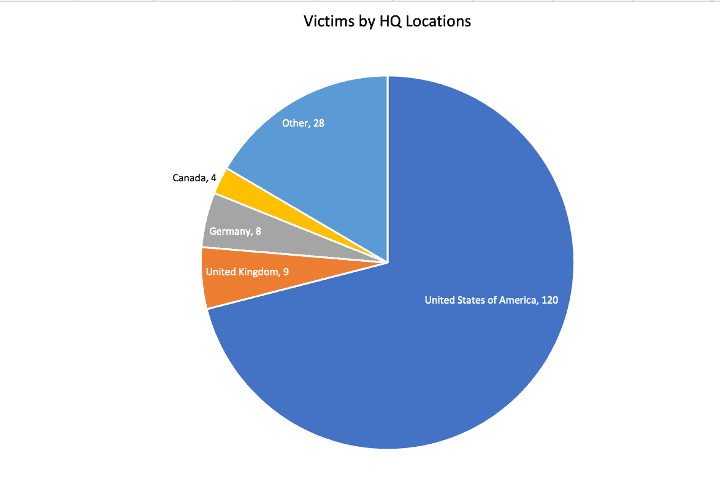
Regions Most Affected
Arctic Wolf tracked CI0p’s activities on dark web ransomware leak sites between June 14 and July 14, 2023. During this period, 169 cases were observed, with the United States topping the list with 120 victims, followed by the United Kingdom (9) and Germany (8). This highlights that while the US has more exposed victims, MOVEit victims, though is that they all appeared to be opportunistic.
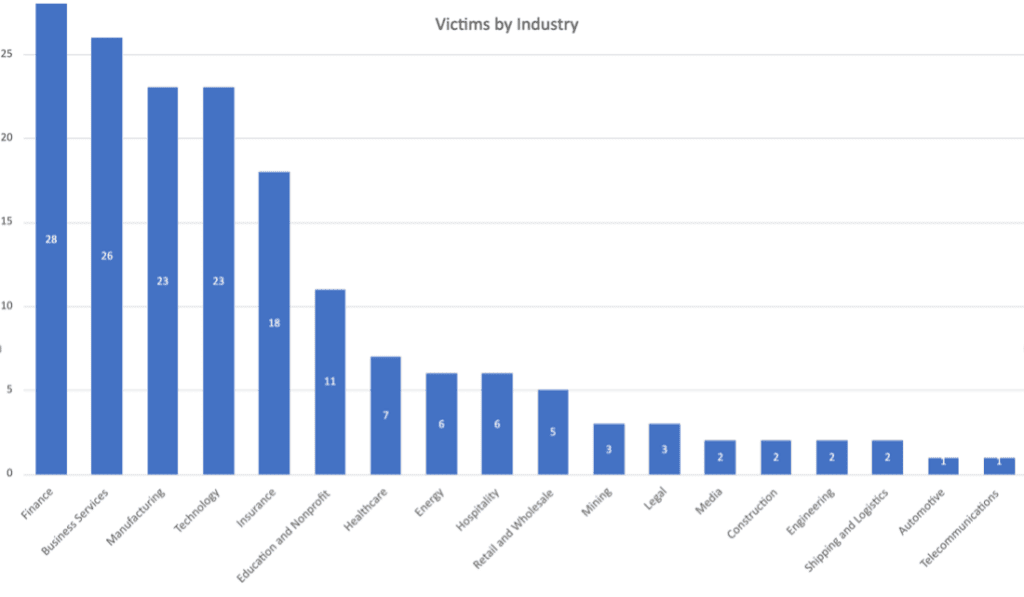
Industries Targeted
Between June 14 and July 14, CI0p started with Finance (28), Business Services (26), Manufacturing (23), and Technology (23) industries which got the first heat on their attacks.
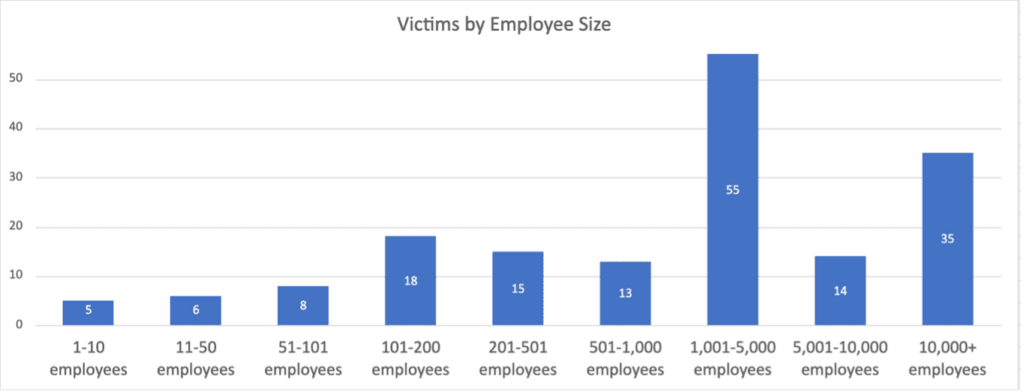
Impact on Organizations by Size
Arctic Wolf’s observation between June 14 and July 14, 2023, revealed that organizations with 1,000 to 5,000 employees were hit the hardest, with 55 victims, according to CI0p’s dark web claims. While there is a correlation between the organization size of those most commonly targeted and the most common users of MOVEit, the broader question remains, did we see widespread exploitation of the MOVEit vulnerability because it presented access to the most desired targets? Threat actors often capitalize on vulnerabilities that are easy to exploit, however, making any size of organizations equally vulnerable. When the opportunity arises, threat actors will target organizations of all sizes.
Key Takeaways
The rise of CI0p ransomware has demonstrated the importance of robust cybersecurity practices for businesses relying on file transfer software like MOVEit Transfer. The exploitation of vulnerabilities can cause irreparable damage to organizations, regardless of their size or location. Yes, it started as zero-day, and some organizations were already hit by the MOVEit Transfer vulnerability. However, if you have a strong security posture, as a whole, both from a reactive and proactive cybersecurity approach, organizations could still contain the situation and might eliminate the spread. As cybercriminals continue to evolve, it is crucial for companies to stay vigilant and employ comprehensive security measures to safeguard their valuable data and systems.
Arctic Wolf MDR
Arctic Wolf® Managed Detection and Response (MDR) solution provides 24×7 monitoring of your networks, endpoints, and cloud environments to help you detect, respond, and recover from modern cyber attacks.
Built on an open XDR architecture, the Arctic Wolf Platform® combines with our Concierge Delivery Model to proactively protect your environment and strengthen your security posture.
Arctic Wolf Managed Risk
Built on the industry’s only cloud-native platform to deliver security operations as a concierge service, Arctic Wolf Managed Risk enables you to continuously scan your networks, endpoints, and cloud environments to quantify digital risks.
Arctic Wolf is uniquely effective at Managed Risk because our 24×7 Concierge Security® Team takes a holistic approach to digital risk. We start with the basic task of discovering risks in your software, assets, and accounts. Then we find risk in those items by both looking for vulnerabilities and benchmarking against configuration best practices. Once we have that perspective, we advise you on how to prioritize your remediation actions to ensure that you are continually hardening your security posture.