Today’s security teams are operating in highly distributed, tool-dense environments. The average organization relies on dozens of security and IT platforms, including identity providers, endpoint tools, firewalls, cloud services, and email security layers. While each tool might produce alerts, they also require configuration and operational attention. This creates two major challenges for technical security buyers:
- Fragmented response workflows: Even when threats are detected promptly, coordinating containment across multiple technologies is often slow and error ‑prone
- Operational overload: Teams struggle to keep pace with manual triage and response actions across tools, leading to increased risk and inconsistent outcomes
Arctic Wolf® Managed Detection and Response (MDR) and its Active Response capability are designed to address these exact challenges. Instead of requiring customers to rip and replace, Arctic Wolf is designed to integrate directly with the technologies that organizations already use, allowing the Arctic Wolf® Security Teams to take direct, timely remediation actions on the customer’s behalf.
This approach can help enable faster containment, reduced workload, and a more resilient security posture without additional infrastructure complexity.
How Arctic Wolf Uses Response Actions to Help Contain Incidents and Protect Customers
At the core of Arctic Wolf’s approach is a unified response framework that is designed to execute precise actions across the customer’s existing technology stack. These response actions are powered by a broad and growing set of integrations spanning email, identity, endpoint, network, cloud, and firewall technologies.
Integration Across Existing Tools
Active Response works by establishing integration between Arctic Wolf and the tools already deployed in your environment. Enabling these integrations is straight forward, with self-service options available in the Unified Portal. Supported technologies include, but are not limited to:
- Identity providers: Microsoft Entra ID, Okta, PingOne, Duo, CyberArk
- Endpoint platforms: Aurora™ Endpoint Defense, Carbon Black, CrowdStrike Falcon, FortiEDR, SentinelOne
- Email and collaboration: Microsoft 365, Google Workspace, Abnormal Security, Mimecast
- Network and firewall: Palo Alto Networks Panorama, Fortinet FortiGate, Check Point, Zscaler
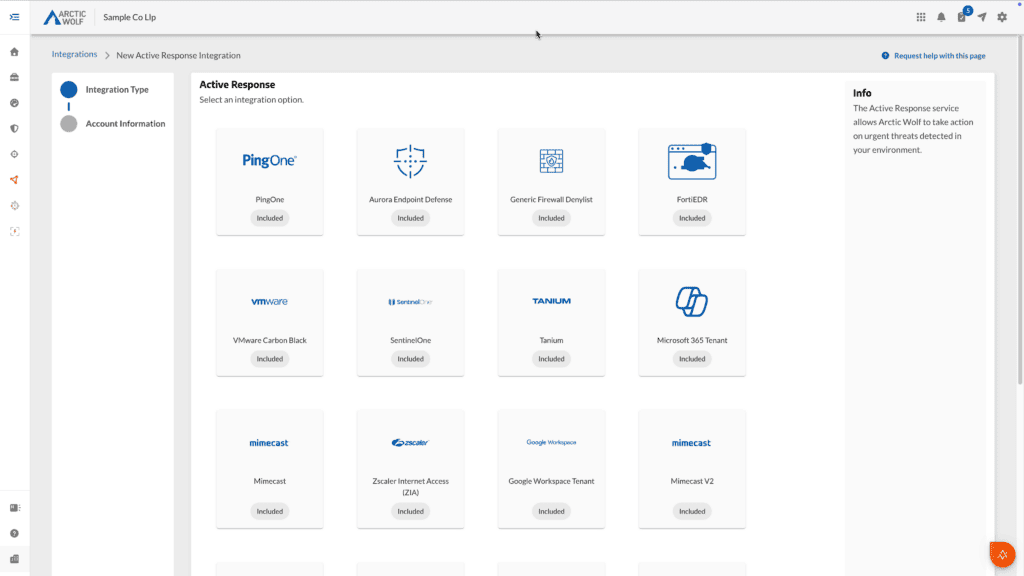
A look at integration options.
Arctic Wolf’s documentation provides a comprehensive view of these integrations, showing examples of how Active Response can disable accounts, isolate endpoints, block malicious URLs, or push denylist entries to next-gen‑ firewalls. [docs.arcticwolf.com]
Containment Through Automated and Analyst-Guided Actions
When Arctic Wolf detects an incident, the threat context is evaluated and can trigger appropriate actions including:
- Identity lockdown: Disable a compromised user account or revoke authentication sessions in platforms such as Microsoft Entra ID or Duo
- Endpoint isolation: Quarantine a device via integrated EDR tools like Aurora Endpoint Defense or SentinelOne
- Network protections: Push a policy update to deny a malicious IP or domain on a customer’s firewall
- Email remediation: Remove malicious messages from inboxes across Microsoft 365 or Google Workspace
These actions may be executed either automatically or by Arctic Wolf analysts, depending on customer preferences and predefined playbooks.
Leveraging the Security Operations Cloud
The Arctic Wolf Security Operations Cloud® is designed to aggregate telemetry from all integrated tools and then applies analytics, threat intelligence, and expert review. This helps enable Arctic Wolf to correlate alerts, eliminate noise, and identify true threats across your ecosystem while also delivering important value.
- Orchestrating cross-tool‑ containment
- Ensuring consistent response actions
- Helping reduce dwell time and limiting lateral movement
This is not a generic, automated playbook system. It is a combination of AI orchestrated response and human-led expertise that also takes customer-defined preferences into account.
Designed for Minimal Operational Friction
A key advantage for technical buyers is that for most environments, Active Response does not impose heavy deployment requirements:
- No new agents
- No complex orchestration software
- No additional infrastructure
Integrations are configured via the Arctic Wolf Unified Portal using standardized, well-documented ‑setup steps. This approach ultimately enables Arctic Wolf to extend your team’s reach and help ensure consistent, repeatable response actions without adding operational burden.
Summary
Arctic Wolf Active Response gives your organization powerful orchestrated containment and remediation across their existing technology stack. By integrating directly with widely used identity, email, endpoint, network, and cloud platforms, Arctic Wolf can quickly take action when threats are detected.
This reduces the time required to contain threats, eliminates the friction of manual multi-tool response workflows, and helps organizations pursue strong security outcomes without adopting new technologies‑ or rewriting their operational models.
If you want to see exactly how easy it is to enable these integrations and watch Arctic Wolf response actions in real time, check out the demo video.
Disclaimer: This blog may include forward‑looking statements. These reflect our current views and are subject to change. They are not guarantees, and actual results may vary.