
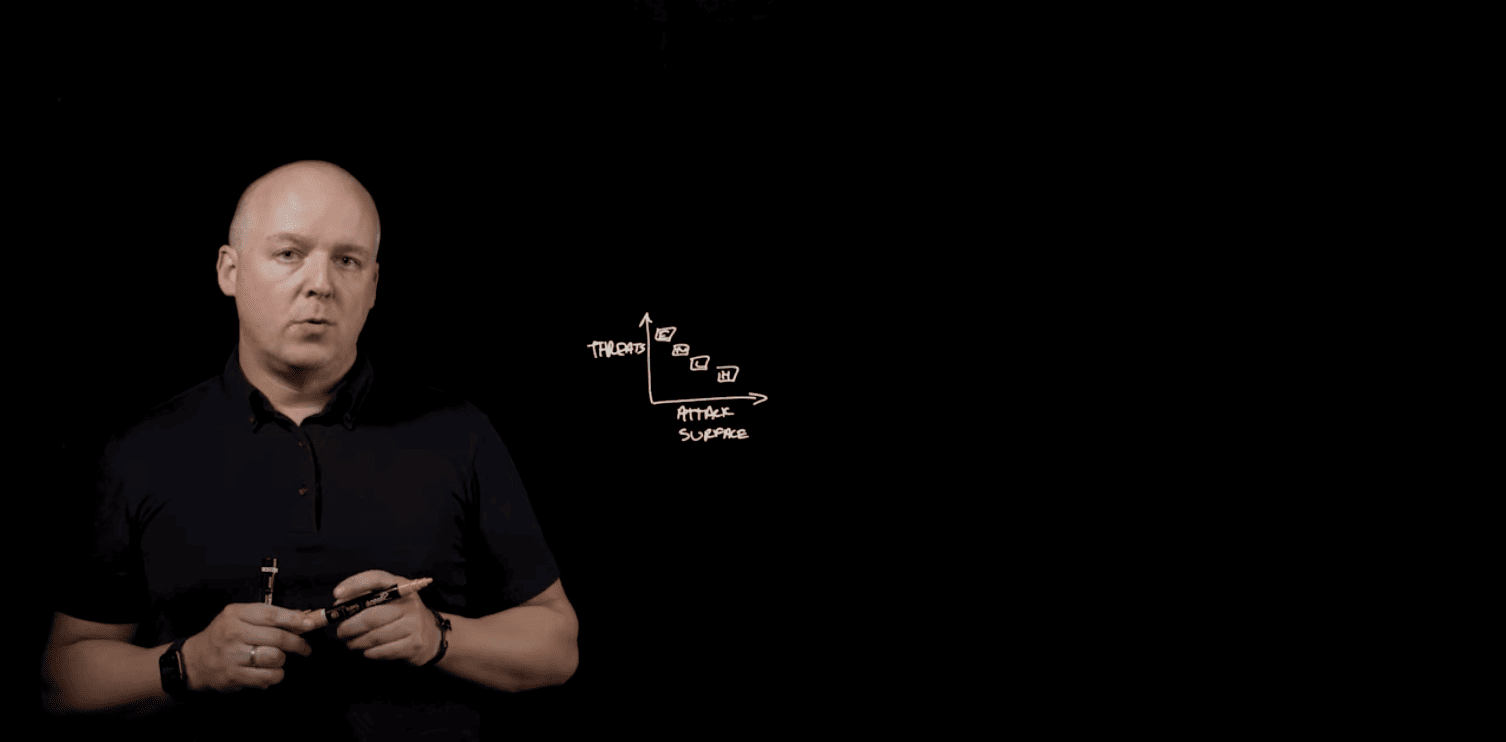
Cyber Risk Spotlight Report: 11 Metrics to Watch
Wondering what vulnerability metrics are most important to watch? Wonder no more.
Delivering security operations outcomes.
Delivering AI outcomes you can trust.
Leverage the power of scale and AI expertise.
Ecosystem integrations and technology partnerships.
Partner with the world’s largest commercial agentic SOC.
Tailored security expertise and guided risk mitigation.
Security experts proactively protecting you 24×7.
Learn how our IR team stops attacks and swiftly restores your organization to pre-incident operations.
Build a resilient business by embracing Security Operations.
Map your security posture against industry standard frameworks.
Continuously discover, prioritize, and reduce exposure across your attack surface.
Receive end-to-end IR coverage for one incident, no matter the incident type.
Engage and prepare employees to recognize and neutralize social engineering attacks.
AI-driven prevention, detection, and response to stop endpoint threats before they disrupt your business.
Quickly detect, respond, and recover from advanced threats.
Recover quickly from cyber attacks and breaches, from threat containment to business restoration.
Stay covered at no cost with up to $3M in financial assistance for cybersecurity incidents.
Increase the likelihood of insurability, and potentially lower your rates.
Access a complimentary suite of tools to reduce risk and improve insurability.
|
2025 Arctic Wolf Threat Report
The Arctic Wolf Threat Report draws upon the first-hand experience of our security experts, augmented by research from our threat intelligence team.
The Arctic Wolf State of Cybersecurity: 2025 Trends Report
The Arctic Wolf State of Cybersecurity: 2025 Trends Report serves as an opportunity for decision makers to share their experiences over the past 12 months and their perspectives on some of the most important issues shaping the IT and security landscape.
Aurora: A New Dawn For Cybersecurity
Join Arctic Wolf on an interactive journey to discover a better path past the hazards of the modern threat landscape. |
Helping Solution Providers scale their business with a comprehensive portfolio of products and services.
Arctic Wolf provides the Insurance Partner Program for Brokers and Carriers to support them within the Cyber JumpStart portal.
Ecosystem integrations and technology partnerships.
Grow your business and solve your customers’ cybersecurity challenges with industry-leading turnkey security operations.
Arctic Wolf OEM Solutions enable ISVs, MSSPs, U.S. Federal Agencies, and security companies.

Wondering what vulnerability metrics are most important to watch? Wonder no more.

Learn how security leaders can effectively navigate the unique cloud security challenges faced by mid-sized organizations.
AWS and Arctic Wolf reveal how you can secure growing workloads, and manage and harden AWS cloud configurations.
Stay protected from cloud threats like business email compromise, ransomware, suspicious resource usage, and phished credentials.
Identify cloud resources at risk and get guidance on hardening your posture, simplifying cloud security.

Now available in the AWS Marketplace, Arctic Wolf delivers premier cloud-native security operations using AWS’s portfolio of cloud capabilities.

Extended detection and response (XDR) has transpired into a market description that, in my not so humble opinion, proves to be as troublesome as the phrases “next gen” or “machine learning” were from 2016 to
Learn how the Arctic Wolf Security Operations Cloud can help your organization solve today’s biggest cybersecurity problems.

Detect, respond, and recover from cyber attacks with 24×7 monitoring of your networks, endpoints, and cloud environments.

Discover, benchmark, and harden your security across your networks, endpoints, and cloud environments.

How Arctic Wolf security capabilities, functions, and features align with HIPAA standards for protecting privacy and security.

Modern enterprises often use hybrid computing architectures that consist of both on-premises and cloud-based resources. A hybrid architecture makes it easier to conduct business but

Discover the four critical steps your business can take to strengthen your security posture.

Organizations have moved to the cloud in large numbers, opening up new areas of attack. Learn how to stay secure.

You’ll often hear the terms software-as-a-service (SaaS) and cloud computing used interchangeably. While closely related, they are actually two different things. We’ll now explain the

Discover the current state of cloud security along with tips and advice on how to keep your organization secure.

These crucial capabilities help you move beyond the latest cybersecurity buzzwords to get to what actually works.

For good reason, businesses continue to move critical applications and storage from on-premises to the cloud. The promise of the cloud as an IT infrastructure

Learn how Cloud Security Posture Management can protect an organization’s cloud environments.

Arctic Wolf Managed Risk enables you to discover, assess, and harden your environment against digital risks.

Earlier this month, J.P. Morgan surveyed 130 CIOs responsible for $88 billion in annual enterprise IT spending. One of the key findings from the survey

Get comprehensive visibility into your cloud security and enhance your overall security posture.

Arctic Wolf enabled Zelle to improve its security posture for far less than it would cost to build an in-house SOC.

Learn how Arctic Wolf helps protect your Salesforce infrastructure and data by detecting and responding to advanced threats.

How Arctic Wolf detects and responds to advanced threats in Amazon Web Services (AWS) infrastructure.

How Arctic Wolf detects and responds to advanced threats targeting your Box deployment and helps you comply with regulations.

How Arctic Wolf works for Google Workspace to detect threats like unauthorized access, human error, and malicious insiders.

How Arctic Wolf detects and responds to advanced threats that impact company data hosted in Microsoft Azure infrastructure.

Phishing, spear-phishing, brute-force login attacks and advanced persistent threats (APTs) often represent step one of a data breach—and not just in on-premises environments. Many organizations
GLOBAL HEADQUARTERS
© 2026 Arctic Wolf Networks Inc. All Rights Reserved. |
||||||
Privacy Notice |
Terms of Use |
Cookie Policy |
Accessibility Statement |
Information Security |
Sustainability Statement |
Cookies Settings |