What is Verizon DBIR?
The Verizon Data Breach Investigations Report (DBIR) is an annual publication that provides an analysis of information security incidents, with a specific focus on data breaches. Verizon has been publishing this report on an annual basis since 2008.
Wait, THAT Verizon?
Yes! As a telco, Verizon has a corporate interest in cybersecurity; as a name with global recognition, it has driven a major report with its own independent brand.
Why is the DBIR Important?
The Verizon DBIR is one of the industry’s top reports providing the cybersecurity world with an indication of how well, or how poorly, the industry’s security efforts are performing, as well as giving detailed insight into what techniques cybercriminals prefer to use in exploiting vulnerabilities. Because of its role as a top report, the DBIR serves as a shared reference point with experienced customers, and as a powerful source of insight for customers less familiar with cybersecurity.
Arctic Wolf security engineers have reviewed the report at length and have come up with seven things that organizations need to know.
#1 – External Actors Remain a Major Threat
Roughly 4 in 5 breaches can be attributed to organized crime, with external actors approximately four times more likely to cause breaches in an organization than internal actors.
In other words, external actors are consistently more common than internal, with 80% of breaches caused by those external to the organization. This isn’t surprising, as this number has remained consistent and bad actors have continued being relentless in trying to breach organizations of all sizes
How Arctic Wolf Can Help:
Our industry-leading security operations solutions provide in-depth defense against even the most advanced external attackers. Managed Detection and Response alerts you to—and immediately responds to—external attackers across your systems and surfaces, while Managed Risk helps you identify and remediate your internal and external vulnerabilities, providing you with a proactive approach to cybersecurity.
#2 – Compromised Credentials Are at High Risk of Exploit
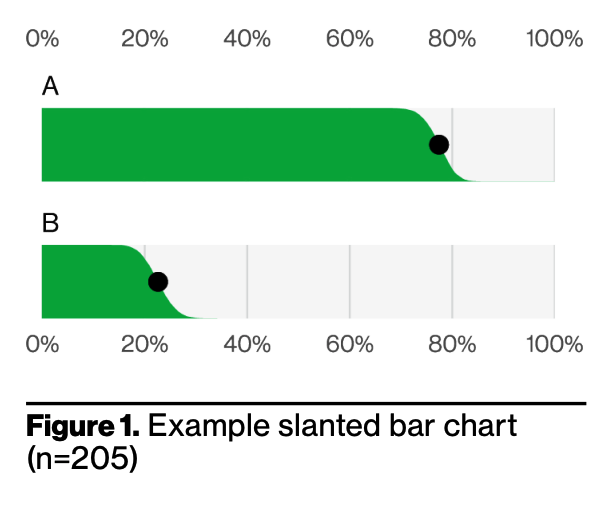
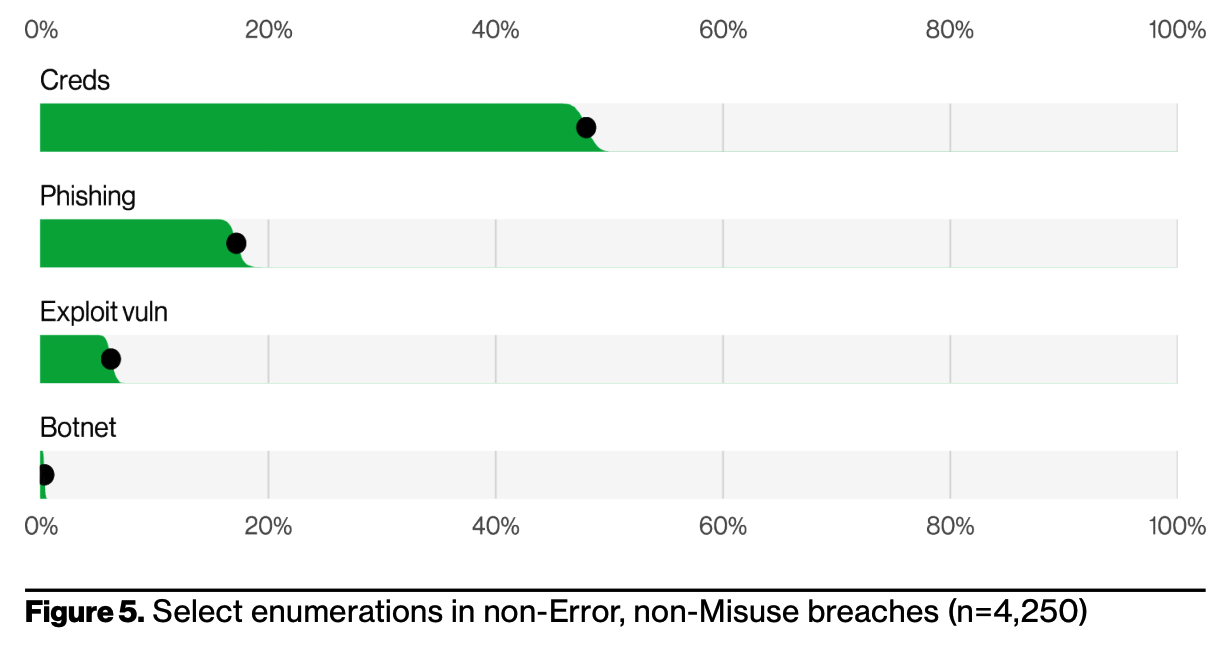
Four key paths lead to your environment: credentials, phishing, exploiting vulnerabilities, and botnets.
All four of these paths are pervasive in all areas of the DBIR, and no organization is safe without a plan to handle each of them. If we look at the below figure, compromised credentials were the most common attack vector exploited, followed by phishing and vulnerabilities.
How Arctic Wolf Can Help:
Managed Security Awareness delivers fun, focused, and consistently fresh content in 3-minute sessions directly to employees’ inboxes. These microlearning lessons teach employees how to avoid phishing attacks and keep their credentials from becoming compromised. Managed Risk continuously scans the dark and gray web for compromised credentials while working to identify and remediate vulnerabilities. And Managed Detection and Response stops phishing attacks in their tracks.
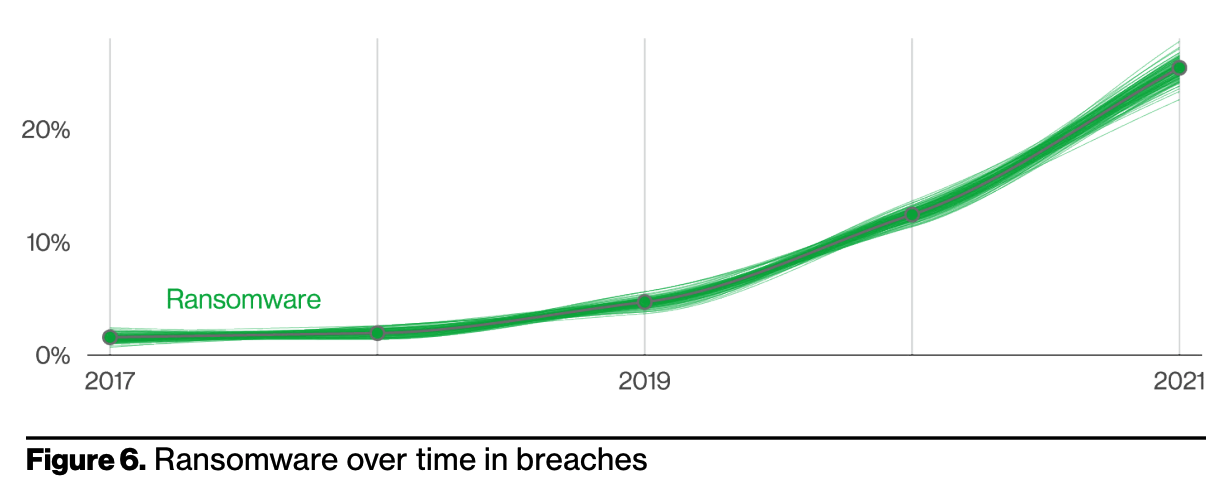
#3 – Ransomware’s Rapid Rise Continues
In 2021, ransomware has continued its upward trend with an almost 13% increase (for a total of 25% of breaches)—a rise as big as the past five years combined. It’s important to remember that, while ubiquitous and devastating, ransomware by itself is, at its core, a model of monetizing an organization’s access. Blocking the four key paths mentioned on takeaway #2 helps to block the most common routes, ransomware uses to invade your network.
The Colonial Pipeline, an American oil pipeline system that originates in Houston, Texas, and carries gasoline and jet fuel mainly to the Southeastern United States, experienced a milestone data leak in May 2021. It had to halt pipeline operations in order to stop a DarkSide ransomware attack. Fuel shortages affected a number of states. The lockdown continued for six days even after the 75 Bitcoin ($5 million) ransom was paid.
How Arctic Wolf Can Help
Managed Detection and Response helps detect and stop ransomware attacks before they can encrypt vital systems or steal data, while Managed Risk and Managed Security Awareness prevent ransomware attacks from ever gaining access, through the remediation of vulnerabilities and the training of employees.
In the event of a breach, world-class Incident Response from Tetra Defense helps you identify, contain, report and recover.
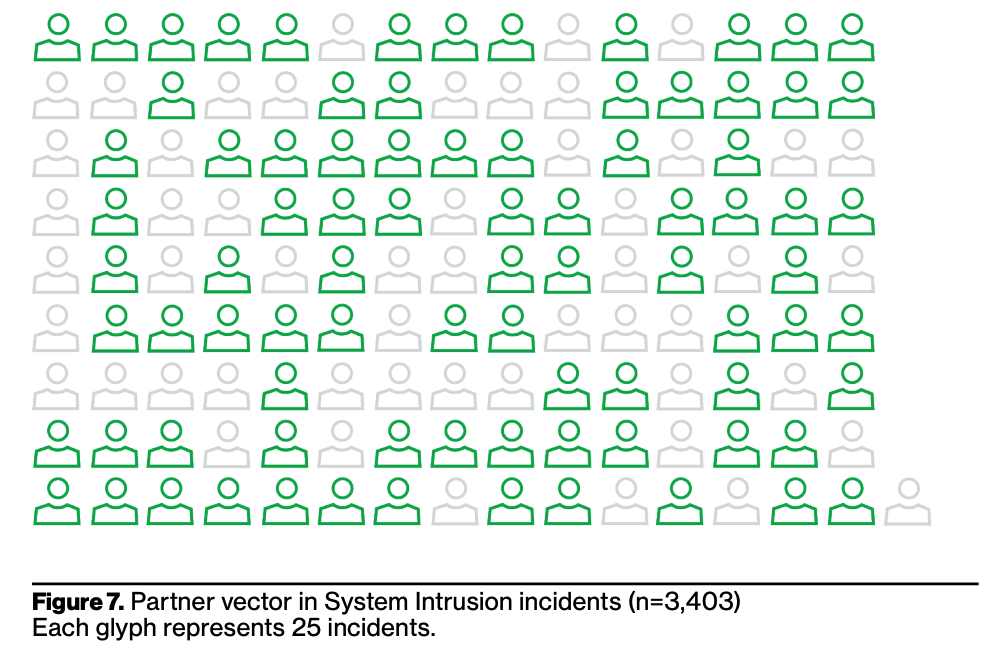
#4 – Supply Chain Security Woes
2021 illustrated how one key supply chain breach can lead to wide-ranging consequences. The supply chain was involved in 61% of incidents in 2021. Compromising the right partner is a force multiplier for threat actors. Unlike a financially motivated actor, nation-state threat actors may skip the breach altogether and opt to simply leverage the access.
As attacks continue to evolve, it’s no longer enough to simply secure your own systems. You need comprehensive, 24×7 visibility into your environment to ensure the protection of your endpoints, systems, and the cloud.
How Arctic Wolf can help:
Arctic Wolf’s Security Operations Cloud provides holistic, unified visibility into your threat landscape.
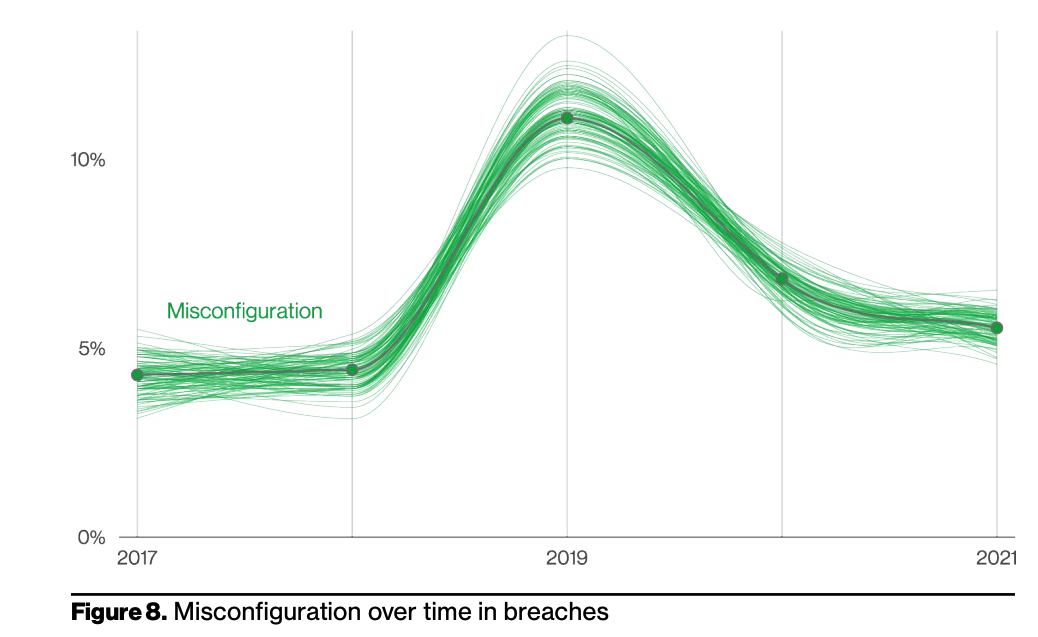
#5 – Misconfiguration and Error
Error continues to be a dominant trend and was responsible for 14% of breaches in 2021. This finding is heavily influenced by misconfigured cloud storage. Misconfiguration accounted for less than 10% of breaches. While this is the second year in a row that we have seen a slight leveling out in this pattern, the fallibility of employees should not be discounted.
Not even the best of intentions can stop misconfigurations, and organizations need a way to address errors in their system.
How Arctic Wolf Can Help:
Managed Risk takes a security operations approach to vulnerabilities and misconfigurations, meaning it can address these risks at scale for organizations of all sides, including in the cloud, through Cloud Security Posture Management.
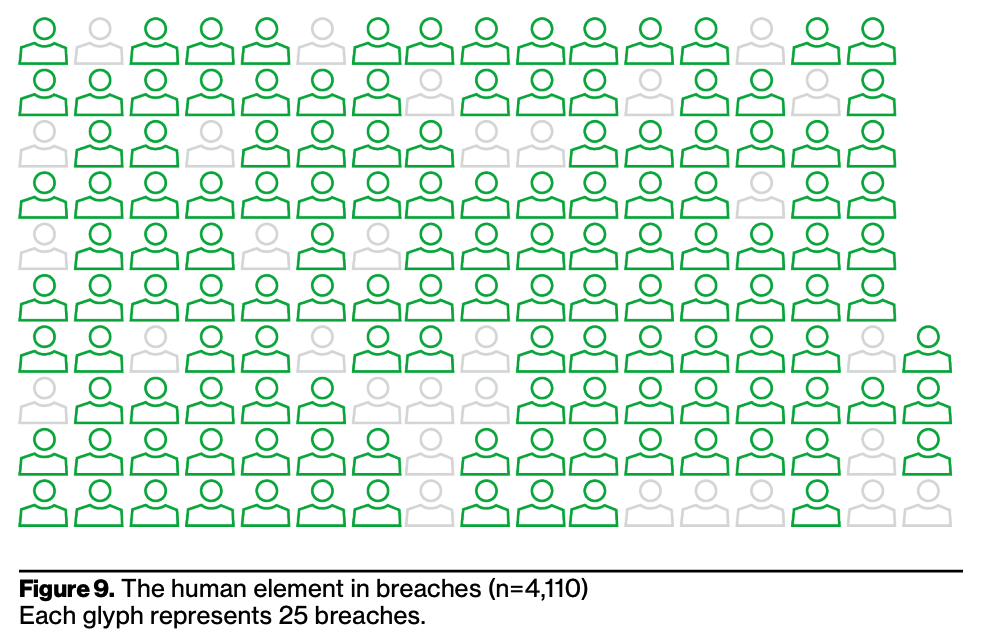
#6 – Humans, We Have a Problem
Security operations remain, in large part, a people problem. This year, 82% of breaches involved the human element. Whether it is the use of stolen credentials, phishing, misuse, or simply an error, people continue to play a very large role in incidents and breaches.
How Arctic Wolf Can Help:
Managed Awareness transforms how businesses promote security capability and culture among an organization’s employees.
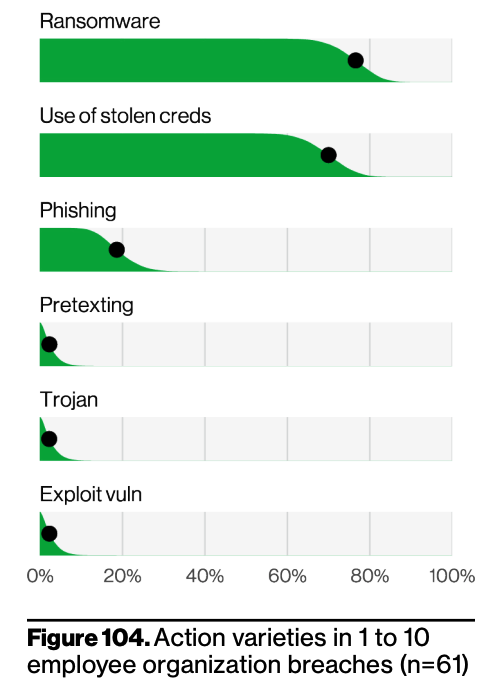
#7 – Attackers Are Coming for Very Small Businesses
Attacks on very small businesses are aiming for the pocketbook, with ransomware accounting for nearly 80% of all attacks. Ransomware is no longer only a threat to large corporations with massive budgets. In this modern threat landscape, no business is too small to be targeted by ransomware gangs.
The number-one action type in the dataset for very small businesses is ransomware attacks. Ransomware is a type of malicious software that encrypts your data so that you cannot view or utilize it, and once the ransomware is triggered, the threat actor demands a (frequently large) payment to unencrypt it.
The second most common action type is the use of stolen credentials. Attackers can get your credentials (username and password) via many different methods: brute force attacks (where attackers use automation to try numerous combinations of letters, symbols, and numbers to guess your credentials), various types of malware (thus the value of having an up-to-date antivirus), along with reused passwords from another site.
Social attacks such as phishing and/or pretexting are also quite common. These attacks can be quite convincing (such as an invoice that looks like it comes from a known supplier but has a different payment account). While most come in via email, criminals have also employed the telephone to convince their target of the legitimacy of their request.
How Arctic Wolf can help:
In today’s landscape, it’s far too expensive for SMBs to build their own Security Operation. It’s also a major challenge for them to find and keep talent as well. Arctic Wolf’s 100% channel sales model and predictable pricing means our industry-leading ransomware protection is available to small and medium businesses everywhere.