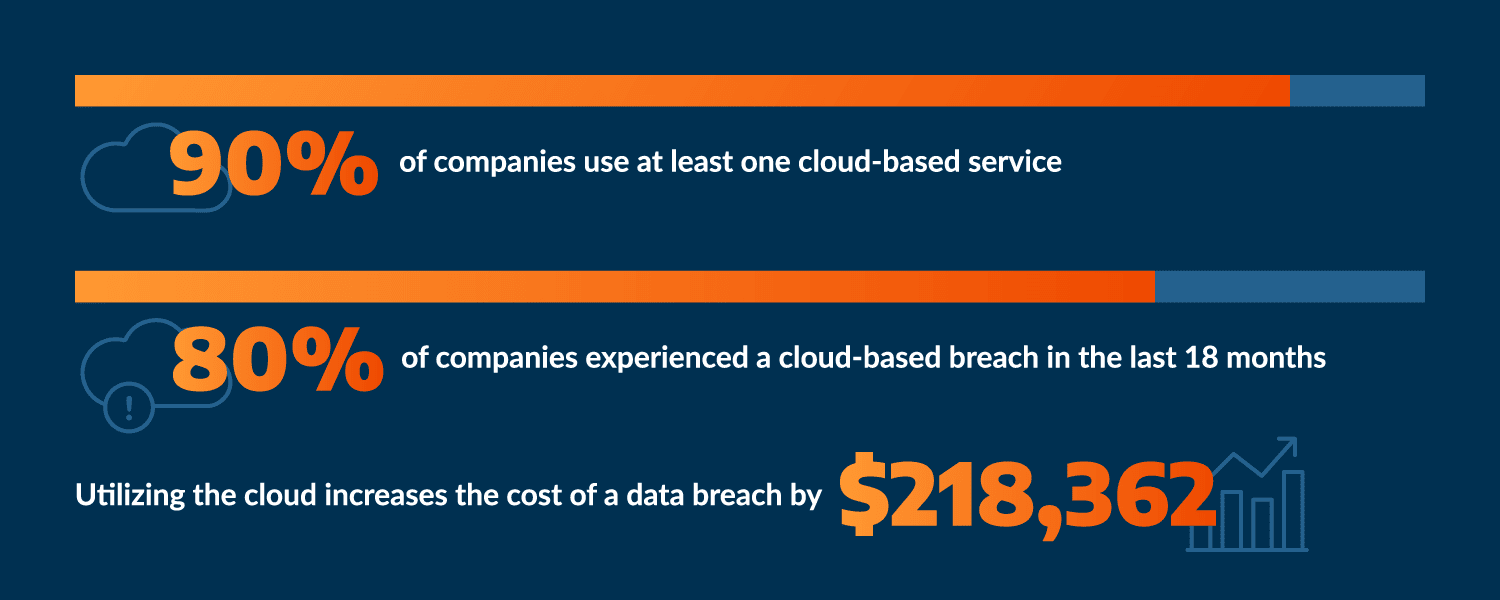
Cloud security is top-of-mind for organizations of all sizes and industries. According to Arctic Wolf’s 2023 State of Cybersecurity Trends Report, 53% stated that they currently have plans to add or update their cloud security technology within the upcoming calendar year — a 31% increase from what respondents reported a year prior. In addition, 48% of organizations are concerned about cloud breaches, which topped the list of attack-type concerns. These concerns make sense, as now 94% of organizations use at least one cloud-based service.
While it brings great benefits, the cloud also brings challenges, including properly securing cloud-based assets. Cybercriminals are well-versed in corporate cloud usage and are successfully exploiting that knowledge. In the past year and a half, nearly 80% of companies suffered a cloud-based data breach. And attacks have hit everyone from the smallest companies to the biggest names, like Accenture, Yahoo, Facebook, and more.
This doesn’t include the cost of cloud-based breaches, either. The cloud carries with it inherent risks that add to your total bill if your organization is breached. According to the IBM Cost of a Data Breach Report 2023, migration to the cloud increases the mean cost of a data breach by $218,362.
Many companies are failing to adequately protect themselves in this shift to the cloud, as cloud security is more complex than simply applying existing on-premise security policies and protocols in a cloud environment. Moreover, companies cannot simply rely on their cloud providers to manage all aspects of security. Organizations need to understand their responsibilities for cloud security, the unique security strategies that come with the cloud, and the steps they should take to ensure they have the most secure environment possible.
What is Cloud Security?
Cloud security, broadly, is the procedures and technologies that prevent internal and external threats to an organization’s cloud environment, including all cloud-based tools.
Cloud security, like all security, should follow a framework, like the NIST cybersecurity framework, and any cloud security solution should be able to identify and monitor threats, and be able to be operationalized as business and security needs change.
Cloud infrastructure security solutions currently fall into three categories:
- Cloud Access Security Broker (CASB). These are policy enforcement points (in the cloud or on-premises) that sit between cloud end users and service providers.
- Cloud Security Posture Management (CSPM). These solutions protect against misconfigurations of cloud resources, as well as vulnerabilities within the IaaS and cloud infrastructure.
- Cloud Workload Protection Platforms (CWAPP). These solutions protect cloud workloads, and are best for hybrid environments that span on-premises, multiple public infrastructure-as-a-service (IaaS) clouds, private cloud, and virtual machines.
It’s important to note that cloud-native application protection platforms (CNAPP) are also rising in use and combine cloud security posture management with CWAPP and cloud service network security (CSNS).
The Five Pillars of Cloud Security Infrastructure
No matter the solution, cloud security needs to follow five pillars in order to maintain proper fortification and function properly.
- Identity and access management. This is the security of who is accessing what in the cloud, and often, the “when” and “where” of that access.
- Infrastructure protection. It’s likely that an organization’s cloud infrastructure is through AWS or Azure, and can be protected through their tools. Learn more about AWS cloud security.
- Data protection. This is achieved through encryption. Encryption tools are available through both AWS and Azure.
- Detection controls. This alerts your organization to a flaw or a potentially malicious event. Solutions such as Cloud Detection and Response (CDR) are vital for this kind of security control.
- Incident Response. If the worst happens, organizations need to be prepared to respond to both cloud and on-premises incidents.
Why Is Cloud Security Critical for Better Cybersecurity?
Organizations are struggling with cloud security, which makes sense. The cloud comes with complications and security risks. Major ones include:
- Complexity in configuration. Understanding how to configure the cloud, especially as more organizations move to a digital-first environment and hybrid work model, becomes a top problem. The skills shortage gap, which continues to impact organizations around the world, doesn’t help ease concerns either, as organizations find they have no one to turn to internally to help them with configuration.
- Rapid cloud adoption. The cloud has become common place, and as with other areas of cyber, adoption often outpaces security, meaning organizations are playing catch-up when it comes to securing their now vital cloud environment. In addition, many organizations are running a variety of SaaS programs on the cloud, only increasing the complexity and obscuring the visibility.
- Cybercriminals are targeting the cloud. Considering it’s nebulous, complicated, and often ignored, cybercriminals have found the cloud to be the perfect target for their crimes.
Understanding that cloud security is needed is different than actually implementing it, but there are concrete steps organizations can take to shore up their cloud defenses and prepare for future threats.
How To Improve Security for Cloud Computing
Cybersecurity is a journey — the same is true for cloud security. It’s an ongoing process that adapts as an organization’s business and security needs change. As organizations take steps along this journey and work to mature their cloud security, there are a few steps they should complete and items they should consider.
- Know Your Cloud Environment and Responsibilities. Most cloud service providers employ a shared responsibility model. Your degree of responsibility depends on the type of services you employ and the degree to which you have transitioned services and data to the cloud. Responsibilities can vary significantly. Understanding how your organization uses the cloud, and what security aspects your organization is responsible for will dictate how you allocate security budget and personnel.
- Implement cloud-specific security policies. An organization’s security policies need to extend beyond the premises, especially if that organization is utilizing remote work, IoT, or a lot of SaaS or IaaS software. Security policies should be unique to the organization’s security journey and consider all aspects of security — including access policies.
- Be vigilant about misconfigurations. Cloud service misconfigurations are a primary source of attacks on corporate cloud systems. Common misconfigurations include unrestricted inbound and outbound ports, poor identity management and access controls, failure to manage internet control message protocol (ICMP) properly, and improper API management and documentation.
- Invest in CSPM or cloud detection and monitoring software. Utilizing the cloud without the right security is like leaving the door to your office unlocked at night; it’s just a bad idea. There are a variety of solutions on the market to help your organization better secure your cloud environment, including tools from cloud provider AWS.
Learn more about how visibility into your cloud environment, made possible through CDR solutions, can transform your cloud security.
Better understand what kind of cloud security works for your organization with our Cloud Security Buyer’s Guide.






