Host Containment for Arctic Wolf® Managed Detection and Response
ISOLATE HOSTS, PREVENT LATERAL MOVEMENT, AND BLOCK INTERNET CONNECTIONS
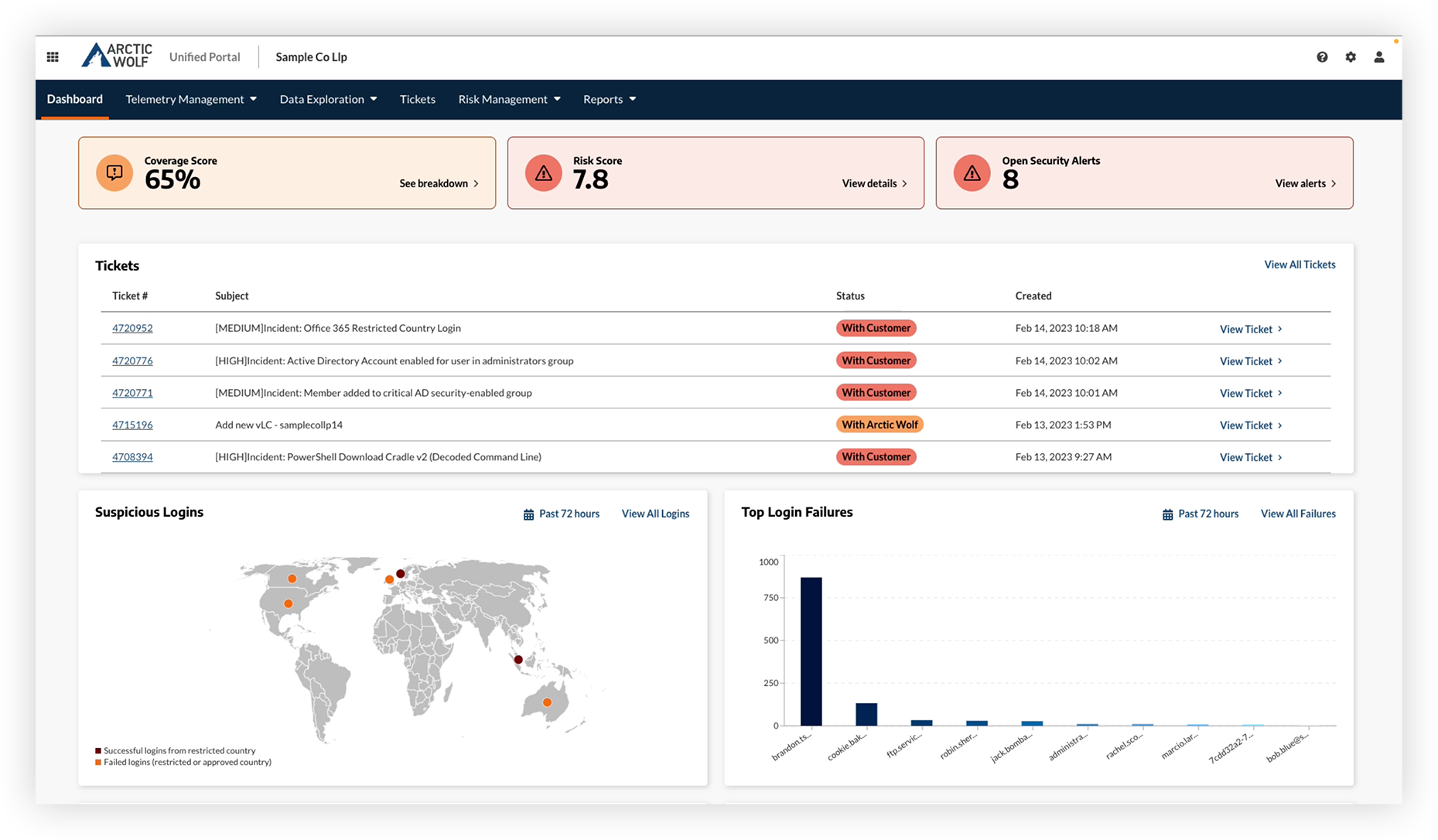
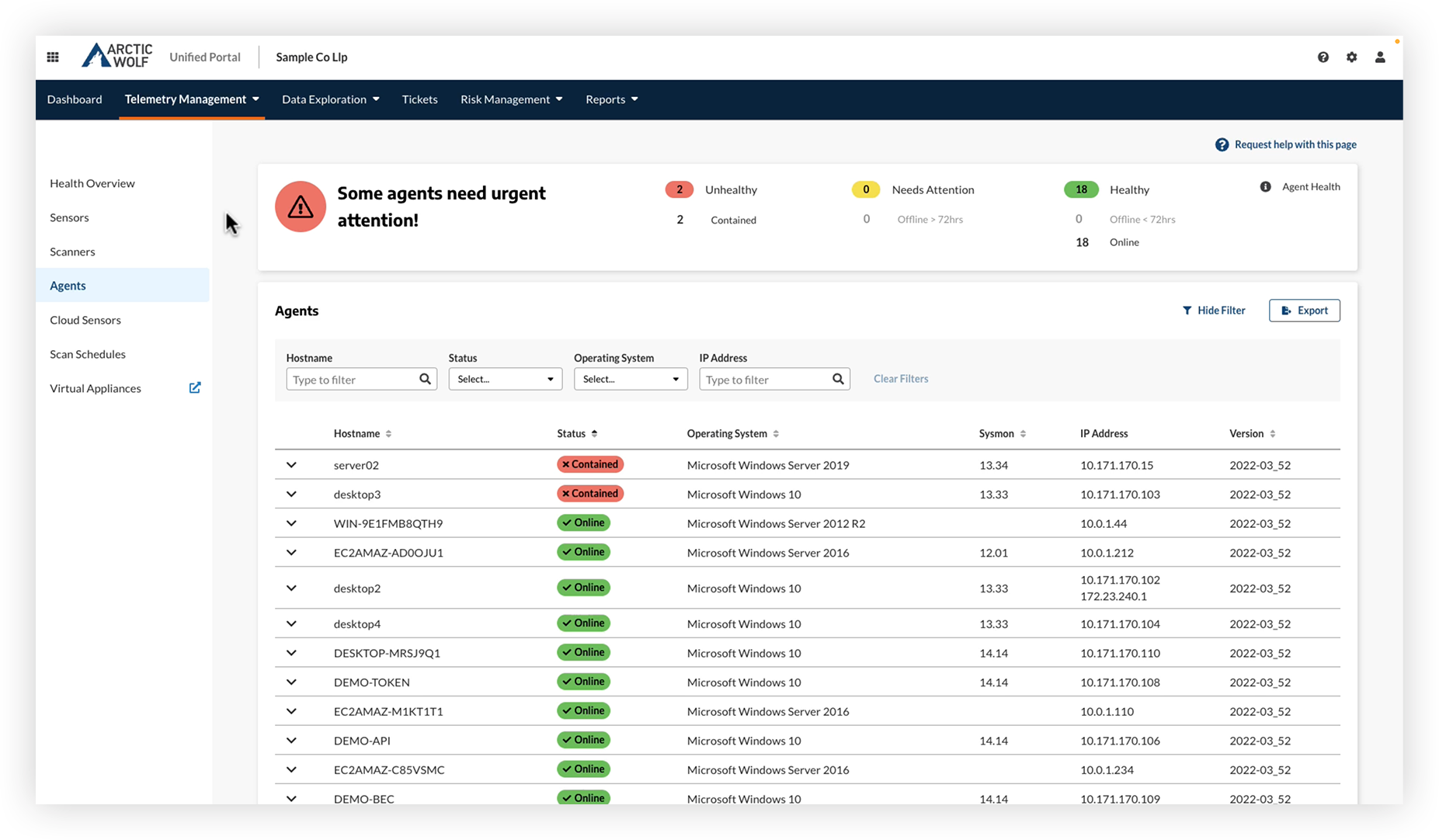
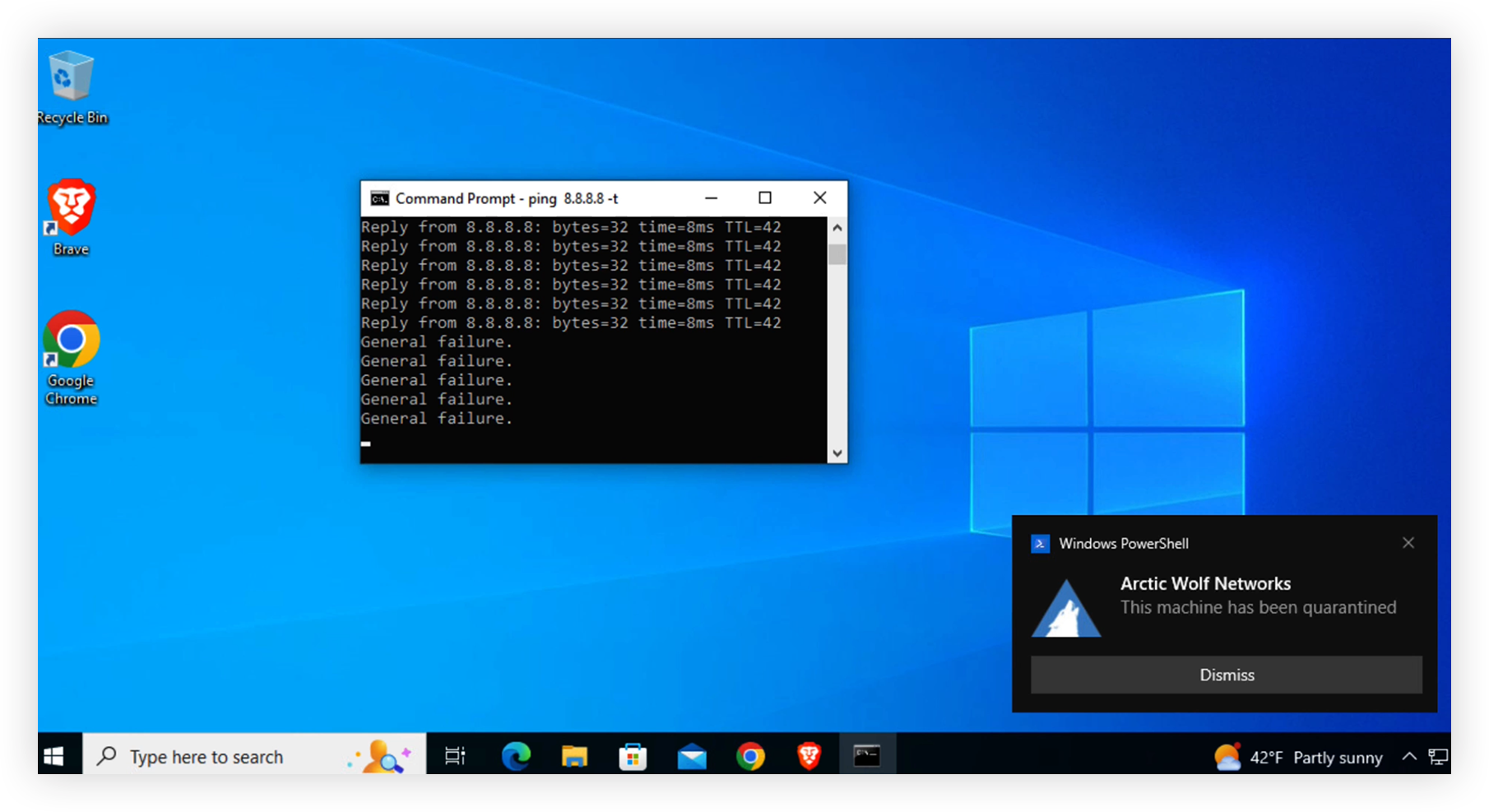
When we see something, we do something. Our host containment capability extends Arctic Wolf’s ability to help customers respond to threats detected on their endpoints through targeted integrations and the Arctic Wolf® Agent.
On-Demand Host Containment Demo
See Host Containment for Arctic Wolf® Managed Detection and Response for yourself. This capability extends the Arctic Wolf Triage Team’s ability to help customers respond to threats detected on their endpoints through targeted integrations and the Arctic Wolf Agent.
Host Containment currently available for:
How Host Containment Works
Host Containment blocks data exfiltration and the propagation of threats, such as malware, by enabling rules to prevent host devices from communicating externally and with other devices on your networks.
Looking to learn more about how Arctic Wolf can help your organization?
Fill out this form and one of our experts will be in touch shortly.
Arctic Wolf is the Market Leader in Security Operations
We envision a future without cyber risk. Every organization should be so effective at security operations that both the likelihood and impact of a cyber attack is minimized to the point where risk is essentially zero.
Read Our Blog
Read about the latest security operations trends, challenges and best practices.
Talk to an Expert
Let a SecOps expert guide you through Arctic Wolf’s award-winning services.