The window to patch your critical systems is shrinking. The White House says the Microsoft Exchange Server vulnerability has moved the time to patch from days to just hours to reduce the risk of a cyberattack. With the stakes so high as an endless stream of vulnerabilities arrive at the doorstep of security teams, organizations must rely on effective security operations.
Arctic Wolf has been busy responding to attacks in customer environments that attempt to exploit these vulnerabilities. Our customers depend on us to quickly detect and respond to high-profile events like this one. And even after patching, security teams need to perform remediation to remove backdoor web shells left behind by attackers. To make matters worse, exploits of these vulnerabilities have been reported to compromise Exchange Servers with a new variant of ransomware known as DearCry.
Threats like these require an agile response from talented teams of security experts to ensure organizations are protected. This article goes behind the scenes to show how Arctic Wolf handles events like The Microsoft Exchange Server vulnerabilities, and how we help our customers mitigate the cyber risk they create.
What Are These Microsoft Exchange Server Vulnerabilities?
On Tuesday, March 2, 2021, one week ahead of its typical Patch Tuesday release, Microsoft released an out-of-band patch to address multiple critical vulnerabilities in Microsoft Exchange, the company’s email and calendar server. These vulnerabilities (CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, and CVE-2021-27065) allowed attackers to take full control of a Microsoft Exchange Server exposed to the public internet. Microsoft reported that these vulnerabilities were being actively exploited by HAFNIUM, a threat group they describe as state-sponsored and operating out of China.
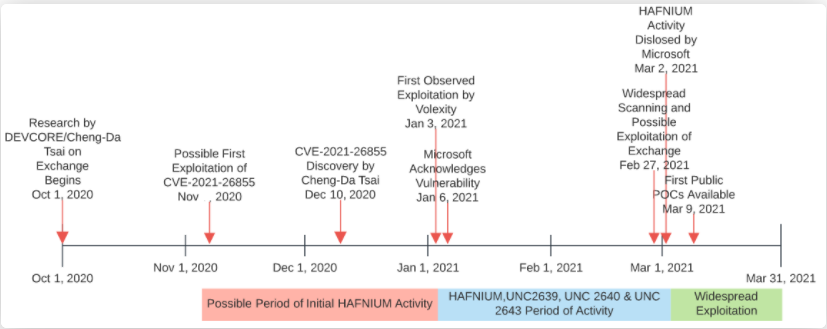
Image via DomainTools
HAFNIUM exploited these vulnerabilities to drop web shells onto thousands of Exchange Servers that allowed them full remote access. They then leveraged this access to establish a deeper persistence. Since, we have seen more advanced post-exploitation activities, including credential dumps, lateral movement, and exfiltration of e-mails.
You can read more on Microsoft’s ongoing blog on the issue. But to summarize—it’s bad.
Detecting Exploits Related to These Events
Our focus, both for these vulnerabilities and other recent high-profile attacks (SolarWinds) have rallied our customers around the use of effective security operations to detect and responds to these events. Our systems, people, and processes work 24×7 on behalf of customers to diminish the impact of an attack. But, before we get to talking about the response specific to the Microsoft Exchange vulnerabilities, let’s talk about detection.
These vulnerabilities present just one opportunity for malicious actors—they are an entryway. However, getting in is not their end goal, it is only the start of an attack, the first step to a broader objective.
Once they gain some level of access, there are additional steps an attacker typically completes to accomplish their mission. They may:
- Elevate privileges to obtain a desired level of access
- Perform reconnaissance on their target’s internal network to identify other systems of interest
- Spread laterally and compromise additional accounts along the way
- Beacon to command-and-control servers
- Login from remote parts of the world and attempt to exfiltrate data
These steps can leave a trace, giving security teams a chance to detect the intruder.
Often in cybersecurity, things can feel hopeless in the face of an attack and it may appear the advantage is always with the attacker. That’s why perspective is important. The initial intrusion is typically the easiest part; trying to evade detection is harder and can swing the advantage back to the defender. One careless, lazy, or sloppy move might be detected.
Let’s go through the specific Exchange Server vulnerabilities and see how they could be used by an adversary:
CVE-2021-26855
A server-side request forgery (SSRF) vulnerability in Exchange, which allows an attacker to send arbitrary HTTP requests and authenticate as the Exchange Server.
CVE-2021-26857
An insecure deserialization vulnerability in the Unified Messaging service. Exploiting this vulnerability can provide an attacker with the ability to run code as SYSTEM on the Exchange Server. This vulnerability requires administrator privileges or another vulnerability to exploit. Microsoft has observed HAFNIUM chain CVE-2021-26855 with this vulnerability to authenticate using elevated privileges.
CVE-2021-26858 and CVE-2021-27065
These two are post-authentication arbitrary file write vulnerabilities in Exchange.
If an attacker can authenticate with the Exchange Server, then they can use one of these vulnerabilities to write a file to any path on the server. Microsoft also observed HAFNIUM chain CVE-2021-26855 with this one to authenticate with elevated privileges.
You can see why this combination provides great opportunities for attackers. The announcement of the vulnerability kicked off a race between threat actors seeking to exploit environments and the security community attempting to protect them. Our mission at Arctic Wolf: Stay ahead of the pack.
Time Is Critical for Thwarting Attacks
When these Exchange Server vulnerabilities became widely known, Microsoft published guidance on how to detect any exploit activity. The Arctic Wolf team contacted customers to assist them in analyzing Exchange logs, using Microsoft’s Test-ProxyLogon.ps1 PowerShell script to check for specific IOCs associated with HAFNIUM and its attacks.
Our customers have different sets of procedures to patch, identify, remediate, and implement lessons learned from this kind of event. Some are decommissioning legacy on-prem Exchange Servers and starting over. Some are moving to the cloud. Others are using the Microsoft tool to remediate and clean up known web shells and malware artifacts. Our teams are designed to work with each customer’s unique environment to mitigate risk.
Visibility into the endpoint is also critical to identify any post-compromise activity. The Arctic Wolf® Agent gives our teams visibility into and over endpoints that could be vulnerable. Having the visibility and data is excellent, of course, but there is A LOT of it. We log activity that doesn’t always warrant suspicion. Any time a file is created, or a process is spawned, it might be a normal activity, or it can be an indicator of an attack. By capturing all that activity, we leverage our robust detection engines to look for “the needle in the haystack” and identify threats that might otherwise be missed.
Security Community Tools Can Help
There are some great tools out there to help you quickly identify if you were compromised. Researchers at the security firm Unit 221B have launched a new website, Check My OWA, that allows organizations to submit one of their e-mail addresses to quickly discover if Unit 221B has intelligence indicating if the domain’s Exchange Server was targeted or compromised.
The dataset that backs this website was obtained by Unit 221B through security industry partnerships, including with cloud hosting providers that seized control of servers belonging to some of the threat actors exploiting these Exchange vulnerabilities. These seized servers contained logs of targeted and compromised Exchange Servers, their IPs, and e-mail domains from a specific point in time.
Sites like this are another signal to determine if your Exchange Servers were potentially targeted or compromised. We strongly caution that a “negative” result back does not guarantee an Exchange Server is free of infection, as the dataset that backs this website is not 100 percent complete. Additionally, a “positive” result may not accurately reflect the current infection state of the Exchange Server if an organization has performed remediation steps following the discovery of the compromise.
Our Concierge Security® Teams use a combination of external information and internal collaboration to share results to quickly, create new detections, and immediately, deploy them into all customer environments. As we detect a new threat in one customer’s environment, we use that intelligence to create new detections to identify that same type of threat in all other customer environments.
This brings us back to our earlier topic of why security operations are so important. As the White House stated, the difference between minutes, hours, and days can be the difference between coming out okay or getting completely owned. Organizations must be ready 24×7 to respond to these events swiftly and systematically.
Put up Your Dukes and Defend Your Environment
History shows us that follow-on attacks leveraging significant vulnerabilities such as this are to be expected. And, in recent days, we have seen that play out across the landscape.
For example, enter RANDOM:Win32/DoejoCrypt.A, aka DearCry.
This new ransomware has specifically targeted unpatched Exchange Servers. It does appear at the moment to be human-operated but, instead, auto-spreading. Some, however, believe this may just be a beta version of something bigger to come.
Evidence of DearCry or any other ransomware would trigger an immediate critical customer escalation for containment by Arctic Wolf. That is the benefit of having coverage of the endpoint, network, and cloud—we can contain hosts at the device level with host-based firewalls or block them at a network level with the Arctic Wolf Sensor. This is an action we would only take in coordination with our customers, but it can be highly effective at stopping any post-compromise activity.
Effective Security Operations Is a Must
Responding to this kind of event requires a consistent team of security experts upon which you can trust and rely. These situations are stressful enough without having to teach someone in real-time how you want to respond. Our concierge approach in combination with continuous vulnerability management is how we manage overall risk and create proactive defense strategies.
Zero-day exploits, while very powerful tools, pale in comparison to the overall risk to an organization when compared against announced vulnerabilities like the ones in Microsoft Exchange Servers. Meaning, when a software developer announces a patch for a newly discovered vulnerability, this starts the clock for both threat actors and defenders to accomplish their missions.
The identification of Zero-Days like the Exchange Server exploit rightly grab headlines. However, the day-to-day reality of cybersecurity is more prosaic and important. You need to patch fast, and you need to expect to continue to patch and respond to additional exploits. That requires discipline, expertise, and resource —all of which are the hallmarks of effective security operations. And that is something that of which Arctic Wolf takes pride.
If you are looking for help with your security operations, check out Arctic Wolf® Managed Detection and Response and Managed Risk solutions. If your environment extends into the cloud, you will want to read about our Managed Cloud Monitoring solution as well.
And, if you are already an Arctic Wolf customer, we look forward to helping you fight whatever comes next.
Additional Resources
- Join the conversation with Arctic Wolf on Facebook, Twitter, LinkedIn, and YouTube
- Visit arcticwolf.com to learn more about our security operations solutions
- If you’re ready to get started, request a demo or get a quote today