Executive Summary
-On February 23, 2022, multiple security vendors with a business presence in Ukraine identified a new wiper malware primarily impacting Ukrainian organizations in at least the aviation, defense, financial, and IT services industries. In at least one intrusion, Symantec observed the wiper malware impact devices in Lithuania.
-Researchers identified HermeticWiper shortly after a DDoS attack targeted Ukrainian websites earlier that day. Notably, the deployment of HermeticWiper preceded Russia’s assault on Ukraine.
-Arctic Wolf has acquired and analyzed the first HermeticWiper that was subsequently shared by other sources such as ESET and Symantec; this blog includes analysis and technical details of the malware.
-Arctic Wolf has ingested known HermeticWiper indicators of compromise (IOC) and implemented additional detections into our pipeline to protect customers.
-Organizations must be prepared to deal with a new class of destructive cyber attacks in addition to the ransomware activity that is expected, they will have their own class of tactics, techniques, and procedures (TTPs) and objectives that must be understood by system defenders.
What We Know
-HermeticWiper is the second destructive malware to impact Ukrainian organizations in 2022. In mid-January, threat actors tracked as DEV-0586 leveraged WhisperGate to wipe Master Boot Records and display a fake ransom note.
- We assess similar destructive malware campaigns and DDoS attacks targeting Ukraine organizations will almost certainly continue in parallel with the ongoing Russia-Ukraine armed conflict.
-The executable leverages a now revoked certificate issued to Hermetica Digital Ltd.
-Arctic Wolf has not observed HermeticWiper activity in our customer environments, which hinders our ability to identify initial access points. However, Symantec observed the following technique leveraged:
o T1190-Exploit Public-Facing Application:
- In at least one intrusion, threat actors leveraged malicious SMB activity against a Microsoft Exchange Server.
- In at least one intrusion, threat actors leveraged a Tomcat exploit to execute a PowerShell command and download a JPEG file from an internal server.
-Threat actors deployed a Golang-based ransomware in tandem with HermeticWiper in multiple intrusions, according to Symantec.
Analysis of HermeticWiper
Arctic Wolf’s analysis is based on the first HermeticWiper sample (1bc44eef75779e3ca1eefb8ff5a64807dbc942b1e4a2672d77b9f6928d292591) shared by ESET and Symantec on February 23, 2022.
Malicious Capabilities
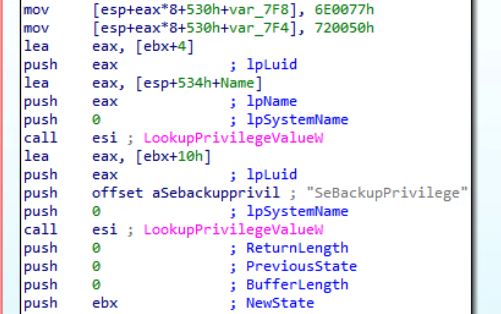
Upon execution, the malware enables SeBackupPrivilege, giving the malware read access control to any file. Later in the execution HermeticWiper enables SeLoadDriverPrivilege allowing the malware to load and unload device drivers and SEShutdownPrivilege allowing the malware to shut down a system.
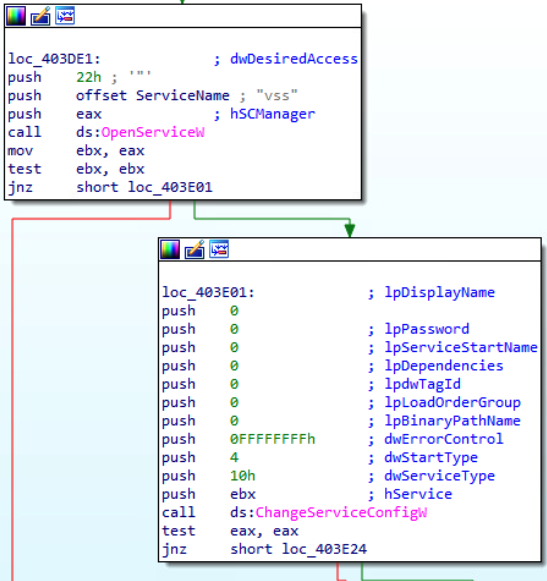
HermeticWiper checks the operating system of the victim device to identify which EaseUS Partition Manager driver to use. The malware disables crash dump generation and the Volume Shadow Service (vss) if enabled.
The malware corrupts the Master Boot Record (MBR) by overwriting the first 512 bytes of all available drives and eventually initiates a system shutdown. Impacted systems will not be able to boot once shutdown. We did not identify additional functionality beyond the malware’s wiper capabilities.
Arctic Wolf will continue to actively monitor and analyze additional samples, IOCs, and TTPs associated with HermeticWiper.
Indicators of Compromise
| Indicator
|
Type |
Context |
| a64c3e0522fad787b95bfb6a30c3aed1b5786e69e88e023c062ec7e5cebf4d3e
|
SHA256
|
HermeticWiper – Sample analyzed by Arctic Wolf |
| a64c3e0522fad787b95bfb6a30c3aed1b5786e69e88e023c062ec7e5cebf4d3e
|
SHA256
|
HermeticWiper |
| a64c3e0522fad787b95bfb6a30c3aed1b5786e69e88e023c062ec7e5cebf4d3e
|
SHA256
|
HermeticWiper |
| 4dc13bb83a16d4ff9865a51b3e4d24112327c526c1392e14d56f20d6f4eaf382
|
SHA256
|
Ransomware deployed in tandem with HermeticWiper |
Sources
IBM Security X-Force: New Destructive Malware Used in Cyber Attacks on Ukraine
Mykhailo Fedorov’s Telegram | Ukraine’s Minister of Digital Transformation
SentinelLabs: HermeticWiper | New Destructive Malware Used in Cyber Attacks on Ukraine
Symantec: Ukraine: Disk-wiping Attacks Precede Russian Invasion