When seeking to understand the cyber threat landscape and respond to various incidents, one of the most important factors to consider is how threat actors are gaining access to networks. The root point of compromise, defined as the method used by a threat actor to compromise an initial access point, can not only help an individual organisation understand their weaknesses and security architecture, but help the cyber industry as a whole spot trends, shore– up defenses, and make predictions about threat actors’ next moves.
In the 2023 Arctic Wolf Labs Threat Report, Arctic Wolf’s team of elite security researchers, data scientists, and security development engineers sifted through trillions of security events, processed by the Arctic Wolf® Security Operations Cloud, and presented both what the root points of compromise looked like in the past year, and what it means for the future of both cybercrime and cybersecurity.
External Exposure Dominates the Field
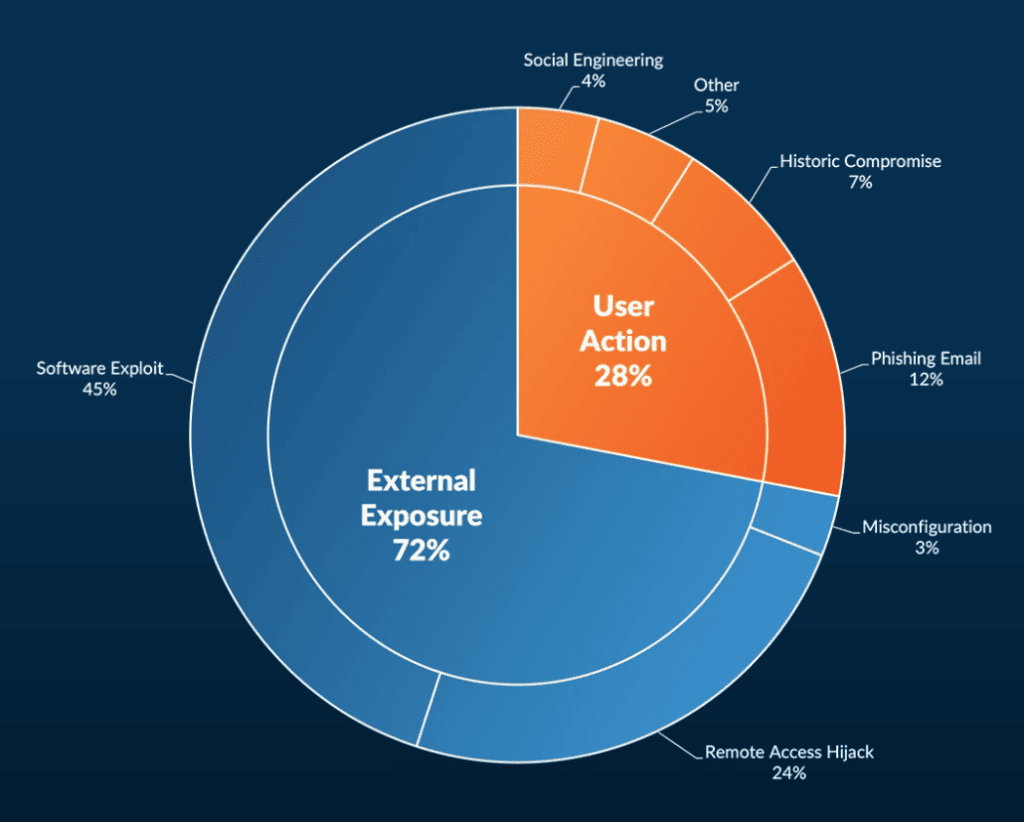
External exposure, meaning a way in from the outside that is not tied to internal users or their behavior, continues to be the preferred method of attack for threat actors. 72% of all attacks begin with external exposure according to Arctic Wolf’s research, and that percentage can be broken down into three preferred methods:
- Software Exploit: 45%
- Remote Access Hijack: 24%
- Misconfiguration: 3%
In the case of software exploits, all of those breaches could’ve been mitigated through patching or other vulnerability management methods, as all originated with known vulnerabilities. In fact, out of the top five vulnerabilities leveraged by threat actors in 2022, four of them were identified in 2021, meaning organisations had months to mitigate risk.
In addition to failing to patch properly, organisations are letting too many users have remote access to their systems, creating a hallway of unlocked doors. This is a high-risk practice that accounted for almost a quarter of external exposure breaches in the last year.
This data highlights how important the proactive side of cyber security is for organisations and shows how many continue to be stuck in a cycle of reacting to incidents. While user action also creates breaches, far and away most attacks originate with issues like vulnerabilities, misconfigurations, or improperly managed access that needs to be, and could’ve been, addressed for many before an incident occurred. Cybersecurity is a holistic practice, where organizations need to focus on every possible entry point and employ both proactive and reactive strategies.
User Action is Still a Threat for Organisations
While external exposure may get top billing for threat actors’ preferred tactics, user action can create issues and, intentionally or not, give threat actors large amounts of access into a network.
User action is defined as any breach (or attempted breach) that began with an internal user giving access to a threat actor. This can be through a social engineering attack, poor credential hygiene, or users clicking on malicious links or downloading malicious files.
A total of 28% of user action incidents were investigated by Arctic Wolf in 2022. It’s important to note this percentage does not include business email compromise (BEC) attacks, which are considered an independent category and can be explored in the full report.
The 28% can be further broken down into the following four categories:
- Phishing emails: 12%
- Historic credential compromise: 7%
- Social engineering excluding phishing emails: 4%
- Other: 5%
All these breaches could’ve been prevented with proper security awareness training, as well as strong monitoring software that can detect suspicious activity, for example an unusual login, before the activity turns into a full attack.
How Organisations Can Protect Against Root Points of Compromise
For an organisation’s cybersecurity strategy to succeed, it needs to be holistic and thorough — a strategy that focuses on proactive and reactive measures, and one which understands that cybersecurity should evolve as business and security circumstances change. These root points of compromise highlight where that kind of effective strategy can be the difference between an attempted breach and a massive attack.
While every organisation’s strategy is personalised, all should follow an outlined framework, like the NIST cybersecurity framework, as their guides, and there are a few specifics businesses should consider:
- A vulnerability and risk management program that can help organisations identify, assess, and patch vulnerabilities before threat actors exploit them.
- A detection and response solution that provides continuous monitoring across the digital environment, and helps those organisations detect and respond to incidents immediately.
- A security awareness program that helps users understand how they can be the first line of defense against user action breach tactics, as well as how they can become targets themselves.
- A strong incident response plan and partner that can offer restoration and other services if an incident occurs.
Arctic Wolf provides all four, and more, combining cutting-edge technology with the human element to help organisations respond to incidents, prevent future attacks, and continually improve their IT environment.
Learn more about our research into root points of compromise, BEC attacks, and threat actor tactics with the 2023 Arctic Wolf Labs Threat Report.
Better understand how the players, trends, and technologies of 2022 is influencing the future of cybersecurity with “2022 Cybersecurity Hindsight and 2023 Insights.”






