Key Takeaways
- Based on data from Q1 2023, manufacturing is the most heavily targeted industry for Business Email Compromise (BEC)
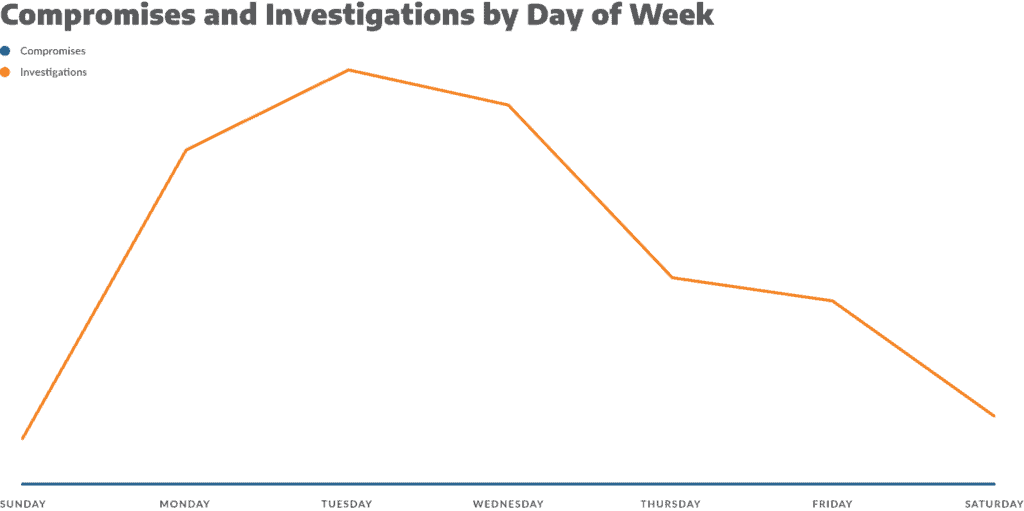
- Monday, Tuesday, and Wednesday are the days with the most BEC activity
While ransomware continues to be a top concern for organisations, Business Email Compromise (BEC) incidents have been rising and targeting all industries. Based on the FBI’s most recent Internet Crime Report, BEC complaints outpace those of ransomware 10:1, and the losses incurred by BEC are 80 times greater than those incurred by ransomware.
While BEC generated losses for businesses of $1.8 billion in 2020, those losses grew to $2.7 billion in 2022. Due to its hard-to-detect nature, BEC is a lucrative business for threat actors and an ongoing challenge for cybersecurity teams. BEC can be one of the more challenging compromises to identify, as the threat actors tend to use the email account as intended: they log in, they write emails, and they send them. It’s also this level of technical simplicity that makes it such an appealing attack vector for threat actors. It’s a low-effort, high-value, volume-based strategy that siphons capital out of unsuspecting organisations via social engineering.
While working with the FBI’s figures provides an excellent baseline for BEC activity occurring in the United States, this doesn’t provide the full picture of BEC as a sub-market within the broader cybercrime industry. The FBI tracks BEC figures based on complaints filed with the FBI and not every victim will come forward to make a complaint, nor will every victim realise that they have been scammed. Plus, BEC is a global activity, so gaining visibility into the broader trends is difficult for any one organisation or investigatory body.
Arctic Wolf, however, can gain visibility into BEC trends from two separate fronts: data collected from Arctic Wolf® Incident Response and Arctic Wolf® Managed Detection and Response (MDR). In the most recent Arctic Wolf Labs Threat Report, which leverages data from Incident Response cases, we found that the volume of successful BEC attacks rose by 29% YoY from 2021 to 2022. We also found that 58% of organisations impacted by BEC attacks did not have multi-factor authentication (MFA) implemented, making it easier for threat actors to gain access to an email account unnoticed.
Based on Incident Response’s root cause analyses, we were able to review BEC attack methods, which effectively is broken down into two parts: the initial email account compromise (EAC) and then follow-on social engineering techniques to target individuals within an organisation to take action on behalf of the attacker. The initial EAC attack can take several forms, from phishing and spear phishing, to purchasing and leveraging compromised credentials from dark web forums. The follow-on social engineering activities tend to fall into the following categories: CEO (executive level) impersonation and fraud, vendor impersonation, data theft, and attorney impersonation.
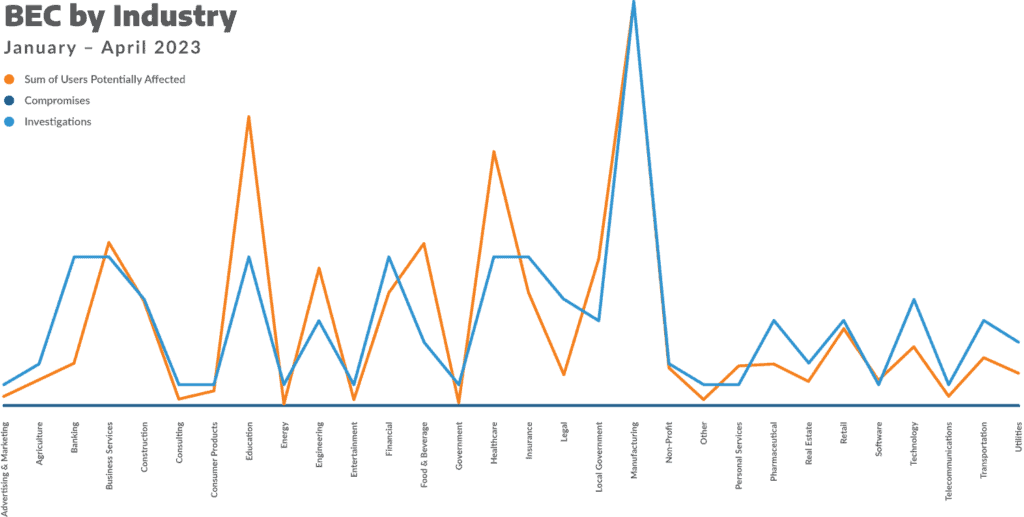
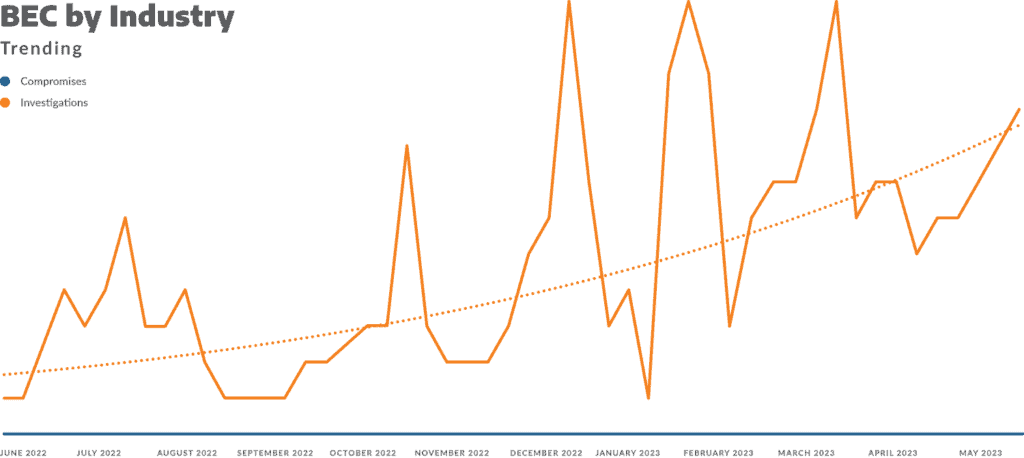
Beyond the data from 2022, we can offer a more tactical look into the trends we’re seeing for Q1 2023 from our MDR offering, which suggests that BEC activity is still on the rise. We see BEC activity increasing based on investigations launched into BEC activity from our MDR offering and an investigation is defined as an analysis of “unauthorised, unexpected, and suspicious activity.“ Based on this activity, there are several trends we’re seeing: 1) Manufacturing has been the most heavily targeted industry, 2) Monday, Tuesday, and Wednesday tend to see the most BEC activity, and 3) the volume of attacks isn’t necessarily correlated with the number of employees an organisation has (which suggests threat actors are taking targeted action against certain industries).
Manufacturing Tops BEC Trends
The manufacturing market has seen 63% more BEC investigations than any other industry, coming in ahead of healthcare, education, business services, insurance, and technology, among others. There are several reasons why this may be the case, including that manufacturing tends to be a more targeted business vertical for cybercrime activity in general, according to the IBM Security X-Force Threat Intelligence Index 2023. When a lot of cybercrime activity begins with phishing or spear phishing (i.e., compromising user credentials), it provides threat actors the opportunity to leverage those credentials to evaluate the opportunity at hand.
Manufacturing organisations tend to have varying degrees of cyber maturity, so threat actors may see a higher success rate of attacks (both in terms of gaining initial access and then in terms of successful execution of an attack). Executing the attack, however, is a nuanced and difficult to define without looking at attacks on a case-by-case basis. Threat actors, though, as they launch an attack may determine once they’ve gained initial access what the best attack strategy is. In many cases, BEC may be a more lucrative attack strategy for the organisation and credentials at hand, and with more attacks focused on manufacturing generally, increased BEC could be a simple knock-on effect.
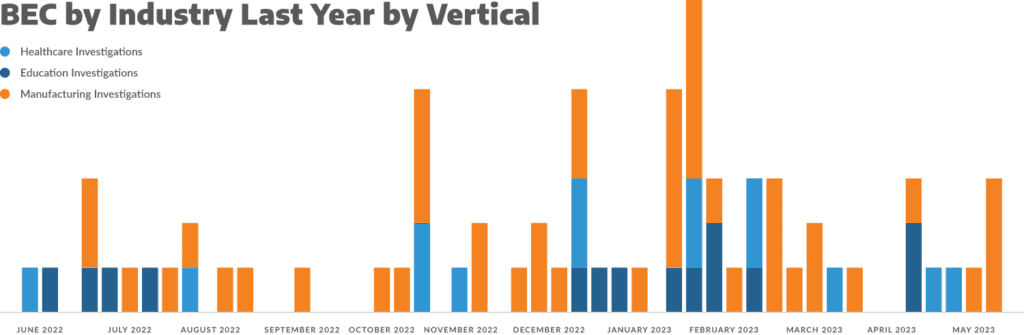
The other possibility is, that because manufacturing organisations have sensitive IP, lists of potential vendors to impersonate, and have a critical position in the supply chain, threat actors may be targeting manufacturing specifically for BEC attacks. Security awareness training will be a critical aspect of defending against these attacks, which is especially critical for manufacturing organisations, who are going to continue to see attacks levied against them.
When Are These Attacks Happening?
From January to April 2023, we saw the volume of BEC-related investigations nearly double and the trend line for weekly investigation volume is continuing to move higher. This means that BEC activity is on the rise in general. There are also some reports that suggest ransomware attacks and ransoms paid are declining, so we could be seeing threat actors pivoting to BEC as one alternative revenue opportunity. We could also be seeing more novice attackers breaking into the cybercrime industry as the allure of high-paying dark web job ads becomes more common place.
BEC is also an attack method that doesn’t require a high degree of technical aptitude. This is a low-technical effort, high-value, volume-based attack strategy that relies on social engineering and scamming people, rather than cracking systems.
With the volume of investigations increasing, as mentioned above, we’re seeing that BEC activity tends to peak at the beginning of the working week: Monday through Wednesday are the busiest days, with Saturday and Sunday being the slowest. The insight here is straight-forward: attackers are taking advantage of typical business norms, aligning their activity to the five-day work week, and placing emphasis on the first three days before employees turn their attention toward the weekend.
Fewer Users Doesn’t Necessarily Mean Fewer Attacks
Manufacturing organisations are commonly attacked targets and typically have a larger user base per organization, but looking at the rest of the Arctic Wolf customer base, user or employee volume doesn’t necessarily determine BEC attack likelihood. For example, healthcare and education sectors both have large employee and user bases per organization, but they saw the nearly the same volume of BEC activity as the financial, insurance, banking, and business services industries. The implication of the Q1 data suggests that threat actors are targeting specific industries that have access to funds and offer the likelihood of a successful social engineering campaign (i.e., impersonation options, vendors requiring payment, sensitive IP, etc.).
Social Engineering and the Human in the Machine
As an example of how BEC can occur, it’s not always through phishing, spear phishing, or the compromising of an unwitting user’s credentials, but it is still by leveraging the behavior of the human behind the keyboard. Arctic Wolf has observed that in some BEC attacks, the credentials of former customer employees have been used to launch an attack before the accounts have been deactivated.
In one instance, a manufacturing organisation of approximately 500 employees was alerted that a user was creating new inbox rules (in an attempt to collect emails from a specific financial services provider and a specific vendor), deleting some emails, and then attempting to sync with the organisation’s AD. We advised the organisation to refresh the credentials for the user and then revoke any active sessions if the activity was unexpected, which then effectively blocked the threat actor’s access to the email account. During the subsequent investigation, we noted that there were unexpected IPs connecting to this account and as the review was conducted, it was discovered that the employee who owned those credentials had been terminated by the organisation, but the account, which had admin rights, was not deactivated. This allowed a threat actor to obtain and leverage those credentials to attempt to snoop the inbox and prepare for the next steps before the credentials were reset.
The Takeaways
From the Q1 data we see, the volume of BEC attacks is likely to continue to increase, manufacturing is still heavily targeted, and the humans behind the keyboards are going to be the biggest threat and defense against BEC. Ensuring you have appropriate cybersecurity policies in place to deactivate accounts of terminated employees is critical. Implement MFA if you haven’t already done so, and perform regular identity lifecycle reviews to identify old and stale accounts (especially those accounts with admin rights).
Learn more about trends and how to combat cybercrime with the Arctic Wolf Labs 2023 Threats Report.
Explore how Arctic Wolf’s Security Operations can help your organisation prevent BEC attacks and harden your security posture.
Watch how the Arctic Wolf® Platform can stop business email compromise attacks.