Arctic Wolf Data Exploration
Fast answers to critical security questions.
Data Exploration allows customers to work with their Concierge Security Team to identify and remediate risk in their environment.
Customers can explore raw logs and analyzed data while working with their CST to understand results and take action when needed.
With pre-defined workflows to address common operational security questions Data Exploration makes leveraging your security telemetry easy.
Data Explorer allows customers to access the same analyzed and enriched dataset used by their Concierge Security Team to investigate potential threats. By combining the ability to query, pivot on, and investigate with access to security expertise, Data Explorer enables customers to answer important operational security questions without the complexity and cost of buying and managing their own tools.
Ready for Analysis
Aggregating, normalizing, and enriching data is complex and costly. Data Explorer provides instant access to analyzed data directly from the Arctic Wolf Platform.
Easy Operational Investigations
Curated widgets and flexible search allow for fast, easy exploration of data by username, IP, geography, event ID, user agent, or any other attribute.
Collaborate with your CST
Your Concierge Security Team is ready to help answer questions you may have or go deeper into areas of focus.
Log Search lets Arctic Wolf MDR customers query raw log data ingested by the Arctic Wolf Platform so they can better answer operational and security questions and maintain compliance requirements. Log Search enables customers to query log data from not only on-premises systems, but cloud SaaS and IaaS sources as well.
Log Search. Simplified.
An intuitive interface provides on-demand access to all your raw log data. Pre-defined queries ensure you can answer operational and security questions quickly and easily.
Works With What You Have
Gain broad visibility across your existing systems with detection and security event collection that spans log sources, internal and external networks, endpoints, and cloud.
Flexible Data Retention
All raw log data is stored for 90 days as part of the Arctic Wolf Platform, and longer retention periods are available to meet your compliance requirements.
Log Sources We Support
Arctic Wolf Log Search works with your existing technology stack, allowing you to see the complete picture with broad visibility.
We collect log information from a broad array of systems across your IT environment, including:
-
Active Directory
-
Authentication
-
Endpoint
-
Firewalls
-
IDS/IPS
-
Mail Servers
-
SaaS/IaaS
-
SSL-VPN
-
UTM
-
WAP
-
Web Gateways
-
And several other external sources of log information
Powered by the Arctic Wolf Platform
Our cloud native platform provides security operations as a concierge service. It is designed to collect, enrich, and analyze security data at scale with dedicated security operations experts driving customized security outcomes that improve your security posture.
Discover Answers to Common IT Questions
Operational Log Search Queries
-
Validate IT configuration changes
-
Use login information to answer employee productivity questions
-
Determine if a user has been locked out of their account
-
Find out who is using specific URLs
-
O365
- What login failures have occurred?
- Was email sent to a user?
- Terminated employee activity
Technical Log Search Queries
-
Investigate failed login attempts (AD or O365 log information)
-
Search operational information needed for audits
-
Locate a change event—firewall, router, AD GPO, or any other log source
-
Verify that a firewall is denying or allowing a connection
-
Validate users logging into servers or that servers are being used
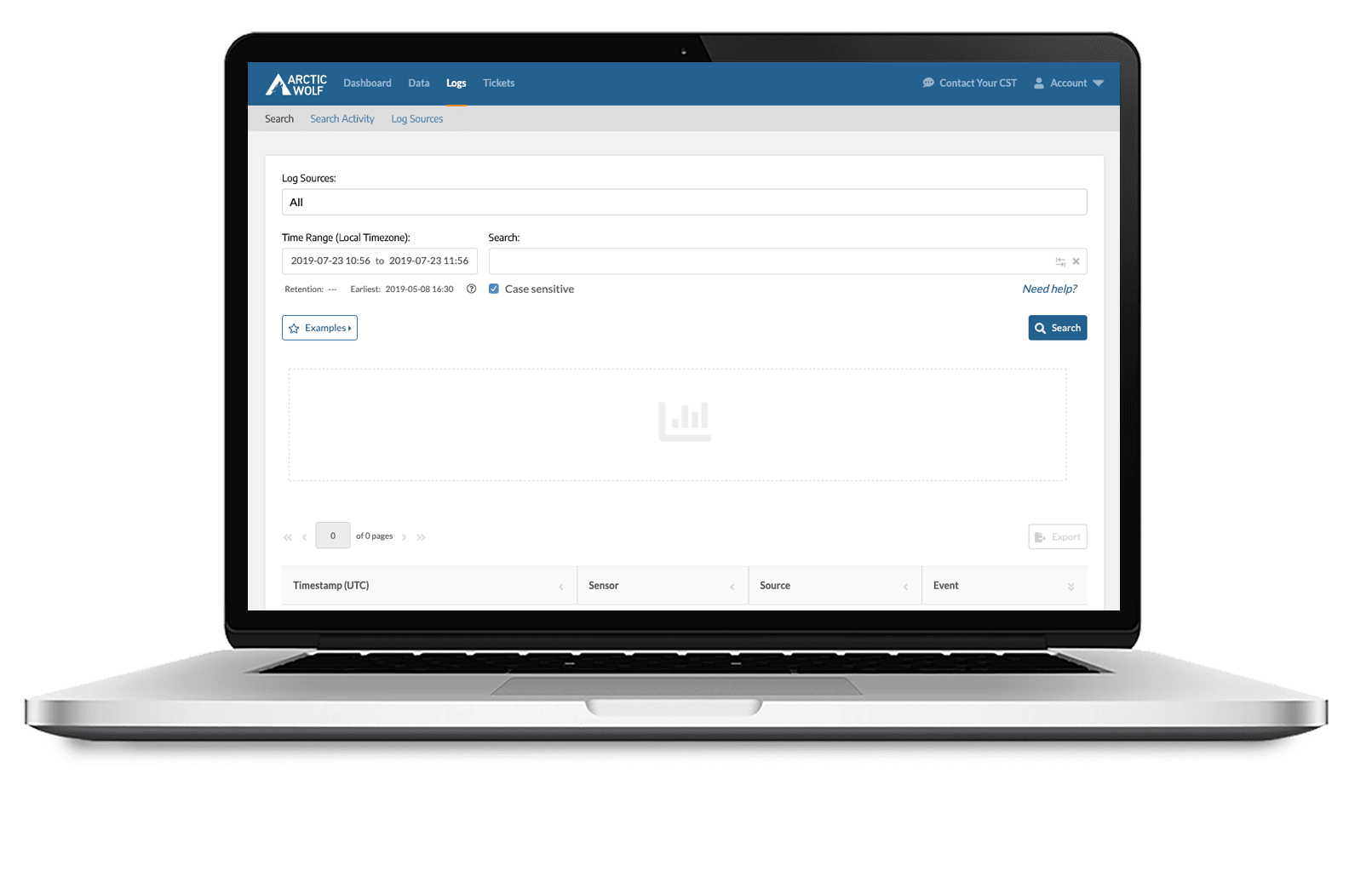
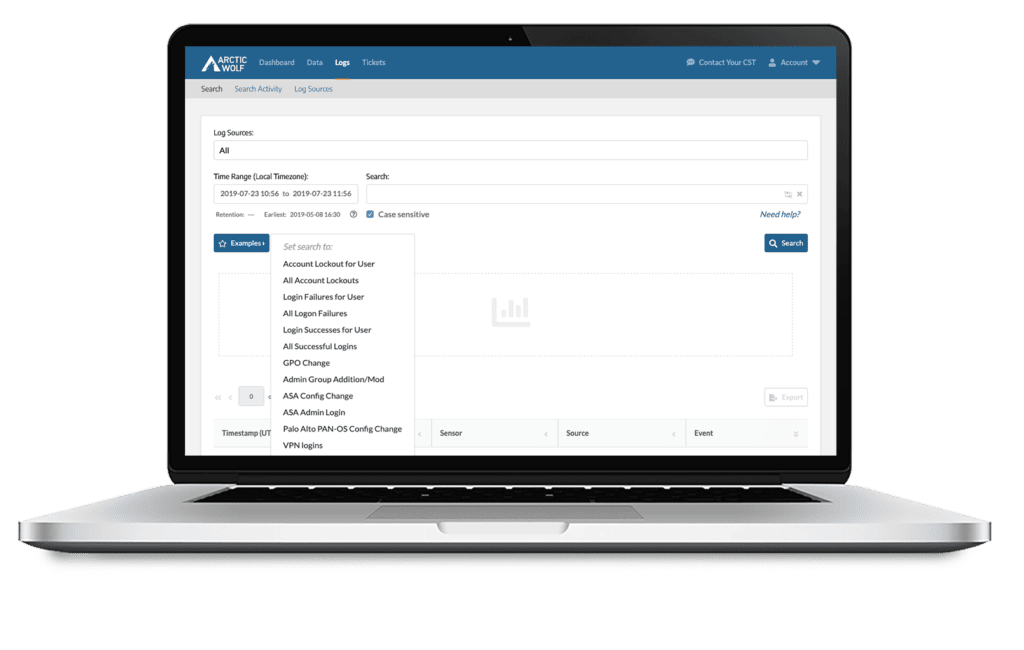
Intuitive Log Search Interface
Simple interface enables users to quickly use log search tool.
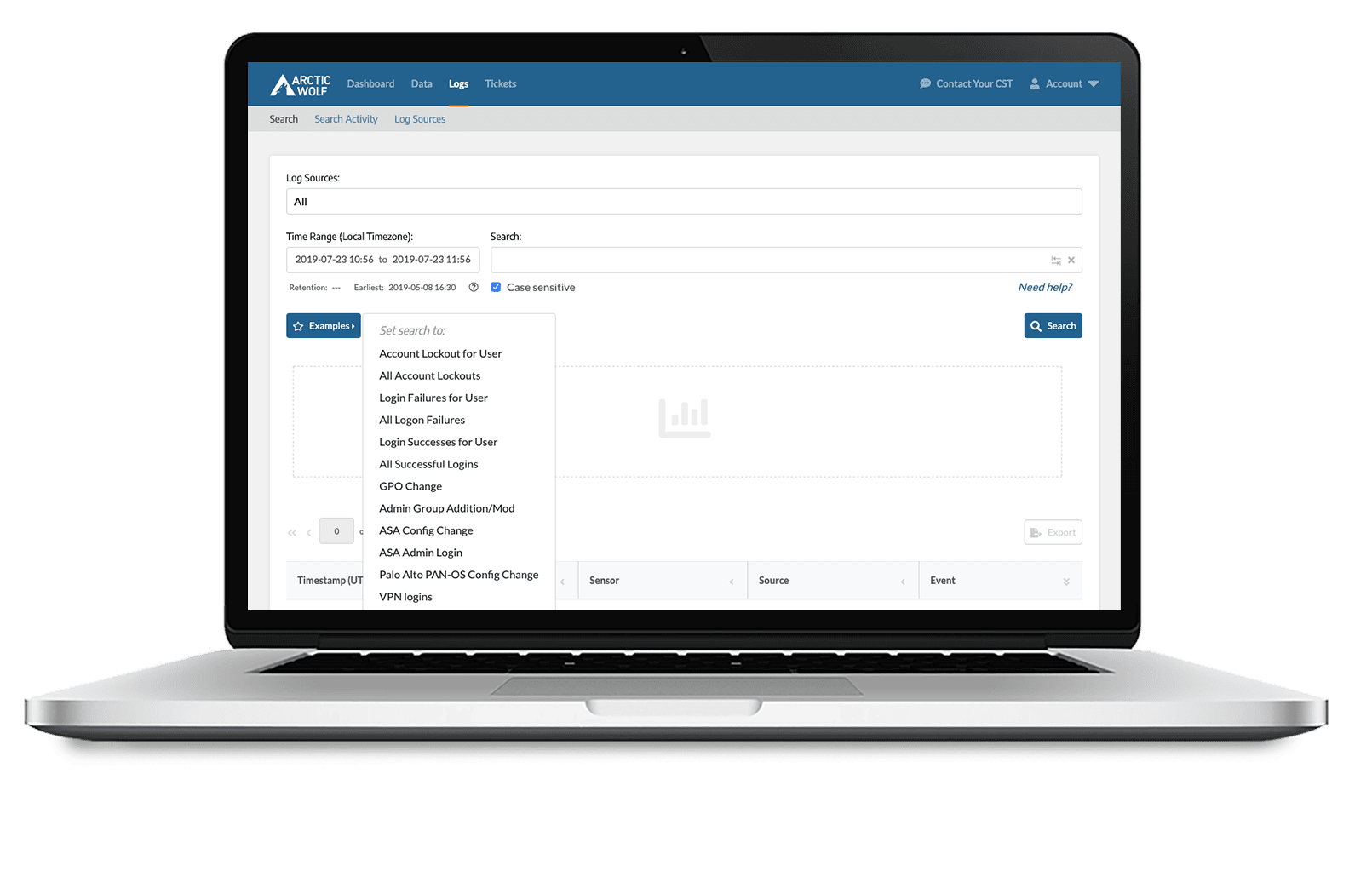
Query Examples Speed Answers
Example templates for frequent searches facilitates rapid searching of data to harvest insights from operational log information.
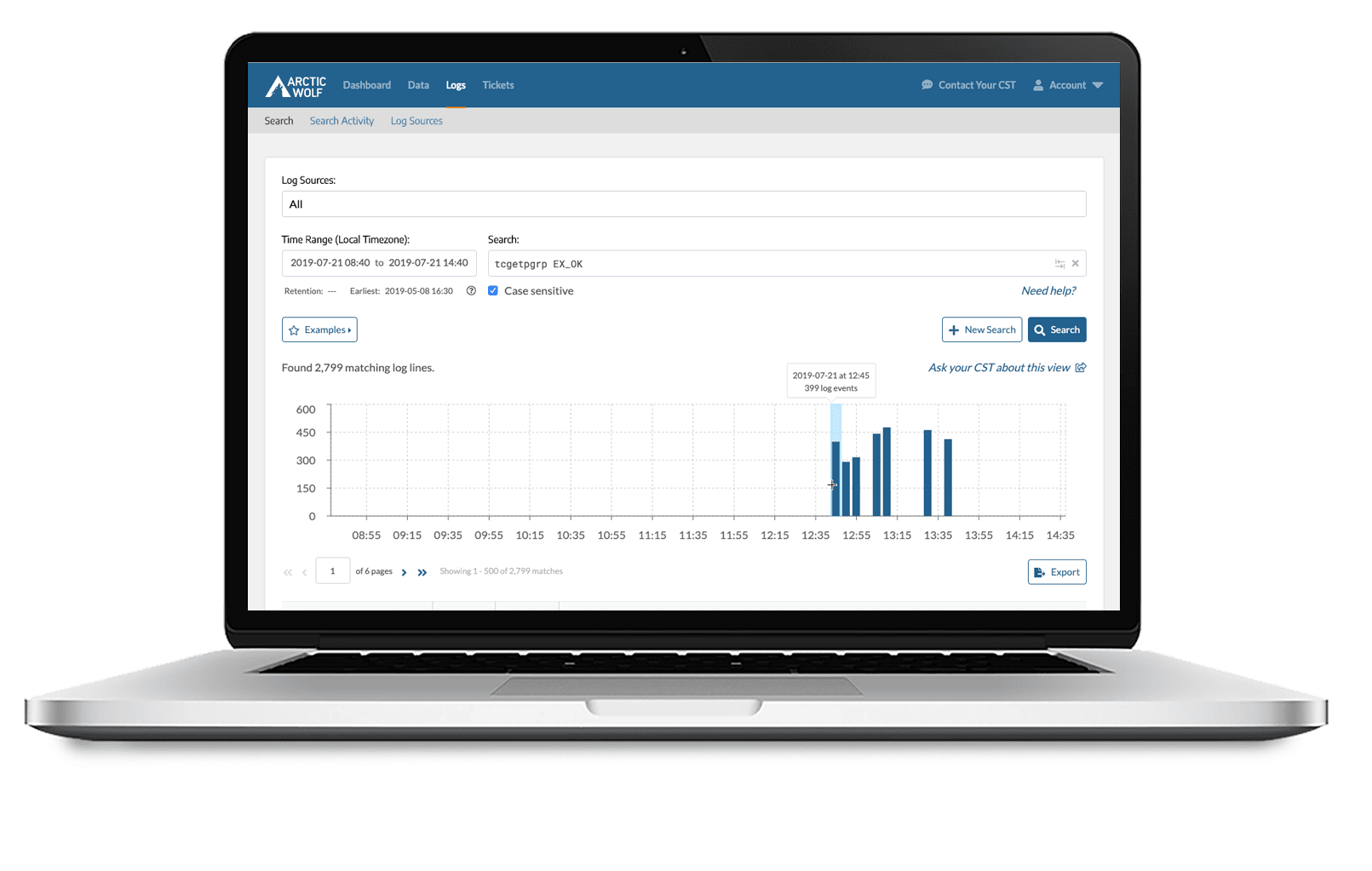
Histogram Summary Shows Hotspots
Search results include a histogram summary to understand data hotspots.
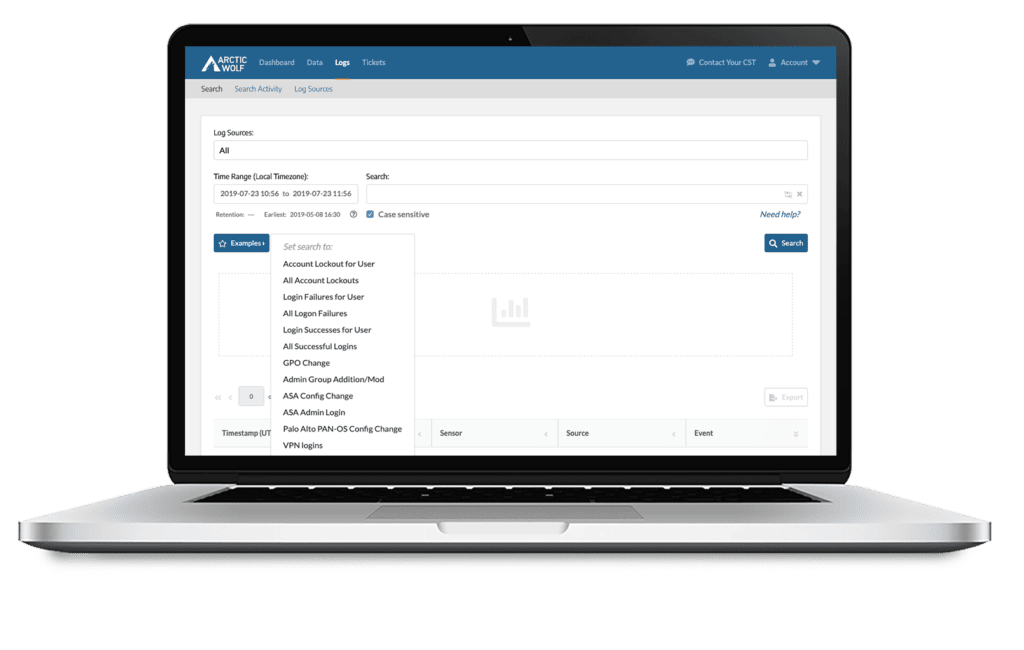
Intuitive Log Search Interface</h2
Simple interface enables users to quickly use log search tool.
Query Examples Speed Answers </h2
Example templates for frequent searches facilitates rapid searching of data to harvest insights from operational log information.
Histogram Summary Shows Hotspots</h2
Search results include a histogram summary to understand data hotspots.
WHAT OUR CUSTOMERS SAY
“Arctic Wolf acts as a force multiplier for our IT team. Arctic Wolf ensures Zelle’s and our clients’ data always remain secure. It has improved our security posture and helped us meet client security obligations.”

