Modern identity‑based attacks often rely on shared infrastructure and reusable attack frameworks, rather than bespoke tooling built for a single target. Phishing kits and phishing‑as‑a‑service (PhaaS) platforms are the clearest example of this model — and today they are the most prevalent sources of account compromise across organisations of all sizes. Device code phishing illustrates how quickly this model evolves: First identified in the wild in August 2024, it moved from nation-state tradecraft to mainstream criminal adoption in a matter of months, and was recently accelerated by purpose-built PhaaS platforms like EvilTokens and Kali365 that made the technique accessible at scale.
For defenders tasked with safeguarding identities, the first line of defense is therefore clear: detect anomalous sign‑in activity. This generally means establishing a baseline of normal behavior for each user — typical geographic locations, ASNs, user agents, devices, client applications, target resources — and flagging sign ins that meaningfully deviate from that baseline.
This approach sits at the core of most identity threat detection and response (ITDR) solutions, and it has dramatically improved our ability to surface potential account compromises at the point of initial access. Yet defenders responsible for investigating, responding to, or authoring anomalous sign ‑in detections often reach the same conclusion: sign-in anomalies alone are frequently insufficient, especially in environments with large identity populations.
To illustrate why, consider the difference in operating context. In a small organisation with a dozen employees, a rare anomalous sign in — perhaps caused by personal vacations or business travel — is easy to validate. The defender likely knows the user personally and can quickly confirm whether the activity was legitimate.
Now contrast that with a small security team responsible for thousands of users. In that environment, anomalous sign‑in alerts may arrive multiple times per day, and the overwhelming majority turn out to be benign. The result is alert fatigue, slower response, and a difficult question that quickly becomes central to identity defense:
How do we reliably distinguish benign anomalies from malicious ones?
The Limits of Single‑Tenant Correlation
Many modern extended detection and response (XDR) solutions aim to answer this question by correlating anomalous sign‑in alerts from identity solutions with telemetry from email and endpoint security solutions. If the same user recently interacted with a phishing email, clicked a suspicious link, or connected to known malicious infrastructure, those additional signals should substantially increase confidence that an anomalous sign‑in event is part of a real compromise.
This correlation approach is genuinely powerful. Arctic Wolf actively develops these same cross‑attack surface correlation capabilities because they help defenders make better decisions, faster.
But even this strategy has limits.
What happens when an email security solution doesn’t flag any phishing, and an endpoint security product doesn’t detect any suspicious DNS queries or network connections to phishing infrastructure? In those cases — common in modern identity attacks — the defender is often left exactly where they started: with an anomalous sign‑in alert that might be malicious but could just as easily be another benign anomaly, lacking sufficient corroborating evidence within the organisation’s own environment to support a confident judgement.
A Data Advantage at Scale
This is where the scale and scope of Arctic Wolf® Managed Detection and Response (MDR) provides a meaningful, data‑driven advantage that most defenders simply do not have access to.
Because we monitor identity activity across a vast number of customer tenants, we observe an enormous volume of anomalous sign‑in events. More importantly, those signals are paired with teams and systems that investigate and resolve these cases every day. We don’t just generate alerts and pass them on to our customers to sort out.
Every day, our teams and systems investigate these anomalies and confirm a large number of true-positive account compromises. The result is an ever-growing, high-fidelity dataset of confirmed malicious identity activity that can be used to refine detections and enrich future investigations.
From this foundation of data emerges a concept that we call “herd immunity.”
Herd Immunity: Confidence Through Correlation at Scale
Herd immunity leverages signals observed across many customer environments to identify malicious infrastructure and attacker behaviors earlier, with higher confidence, and at greater scale than is possible within any single, isolated tenant.
To revisit our earlier scenario: you’re faced with an anomalous sign‑in alert. XDR correlation hasn’t produced any supporting email or endpoint evidence. What next?
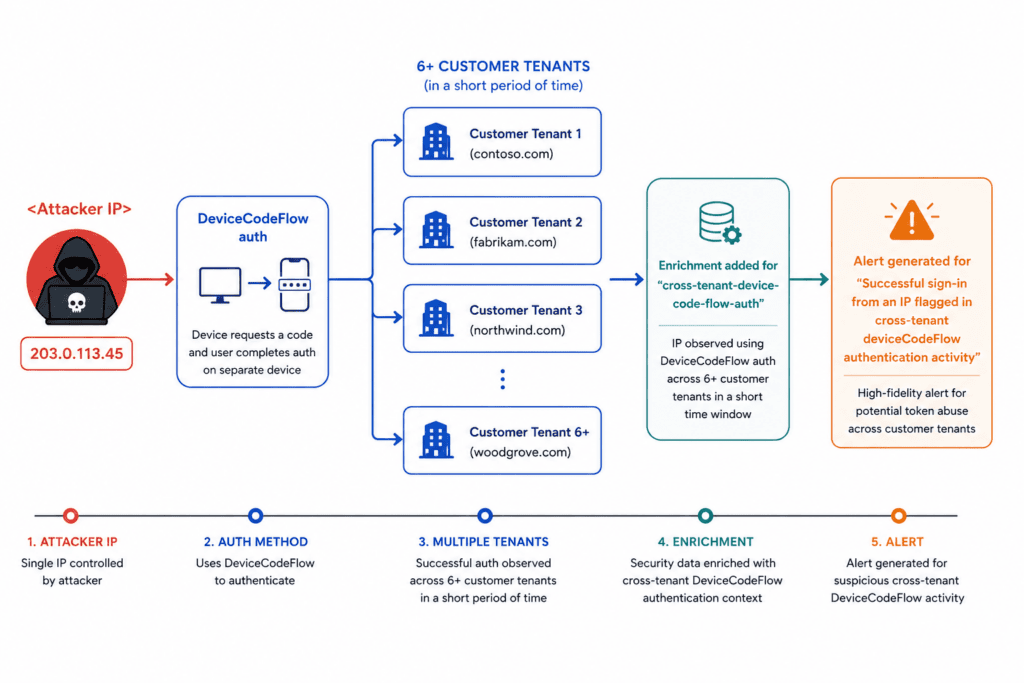
Here’s a concrete example of how herd immunity changes that picture. An analyst opens an anomalous sign‑in alert flagged for device code flow authentication — a technique in which the attacker initiates a legitimate Microsoft authentication request and tricks the victim into completing it, delivering a valid OAuth token directly to the attacker without the victim ever exposing their password or having their connection proxied through attacker infrastructure. Within the alert itself, before any investigation has been completed, the alert is already enriched with two additional, high‑impact forms of context.
First, the sign‑in characteristics — IP address, ASN, user agent, client application, and target resource, etc. — are compared against patterns observed in previously confirmed compromises. The degree to which these characteristics are prevalent in our true-positive dataset directly informs our confidence: High prevalence among confirmed malicious activity is a strong signal that this sign‑in is also malicious; low prevalence or absence shifts the calculus in the other direction. Either way, the enrichment moves the investigation forward.
Second, the solution checks whether the same IP has been observed exhibiting the same behavior — namely, device code flow authentication — across other, unrelated customer tenants in the past seven days. This enrichment doesn’t require the presence of a historical, confirmed, true-positive case in our dataset. The cross‑tenant authentication pattern itself is the enrichment layered onto the alert: the same IP, the same authentication method, across multiple unrelated organisations. That convergence is meaningful, regardless of whether any individual case has yet been confirmed as malicious.
Together, these two enrichments can transform an alert. What might otherwise look like an ambiguous anomaly in a single environment can become a high‑confidence indicator of malicious activity when enriched with context drawn from activity across thousands of customer environments, and the evidence collected from thousands of investigations.
What appears ambiguous in isolation can become unmistakable when viewed across the herd. Attackers benefit when their behavior patterns and infrastructure are a first-seen for every victim. The scale of Arctic Wolf MDR is how we take that advantage away.
Herd Immunity in Action
In April 2026, Arctic Wolf identified a large-scale device code phishing campaign impacting organisations across multiple regions and sectors. By the time we published our report on the campaign, we had observed a single IP address authenticate via device code flow against nearly 150 unique identities across more than 110 distinct customer tenants within a single week. Our investigators confirmed that the infrastructure was hosting a newly observed phishing‑as‑a‑service platform known as Kali365 — a multi-tenant PhaaS ecosystem supporting both device code abuse and adversary-in-the-middle session capture.
For a full technical breakdown of the campaign, the Kali365 platform, and a full list of recommended mitigations, see our Token Bingo report.
Conclusion
When dealing with modern identity-based attacks, detecting anomalous sign‑in activity is of paramount importance. Traditional defense solutions may bombard security teams with an overwhelming number of alerts — particularly in environments with large identity populations — leading to alert fatigue, suboptimal response times, and increased risk to the organisation. Herd immunity cuts through the noise at machine speed with enriched intelligence surrounding anomalies, shifting response from reactive to strategic, and providing defenders with scalable, high-fidelity alerts to deliver better security outcomes.
Learn more about Arctic Wolf MDR, or schedule a demo to see it in action.
Additional Arctic Wolf Resources
- Arctic Wolf’s free Threat Intelligence newsletter: ThreatPulse Community Edition
- View or download our Arctic Wolf MDR data sheet
- Arctic Wolf Tech Den
- Arctic Wolf Blog





