Key Takeaways:
- Compared to the second half of 2022, Arctic Wolf Incident Response saw a 46% increase in ransomware incidents during the first half of 2023
- On the dark web, 82% of the victim organisations with data posted to ransomware leak sites in the first half of 2023 were small or medium businesses who had fewer than 1,000 employees
- Lockbit remains the most active ransomware group, with dark web posting by them increasing 17% compared to a year ago
- The median ransom demand across all ransomware incidents Arctic Wolf responded to in the first half of the year was USD$600,000, which is an increase of 43%, compared to the same time frame last year
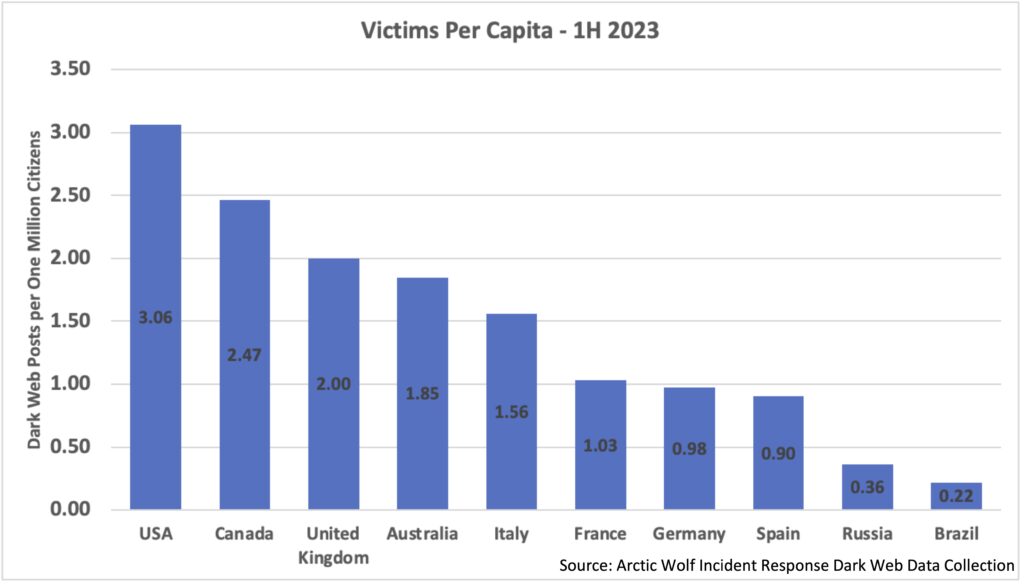
- On a per capita basis, organisations in English-speaking countries, such as the US, Canada, UK, and Australia, are 2-3 times more likely to find themselves on ransomware shame sites than that of non-English speaking countries in the EU, such as Germany, France, and Spain
Ransomware Landscape Update
Threat actor groups maintain dark web shame sites to negotiate ransoms with their victims, name them, and leak their data as punishment for not paying. These sites serve as a major tool for threatening victims and securing ransom payments but are not a precise record of global cyber attacks. However, there’s a lot to learn from the dark web behavior observed in the first half of this year to help contextualise the current threat landscape. Arctic Wolf actively monitors known leak sites to better understand the constantly evolving threat landscape for our customers and partners.
Significantly increased ransomware attacks and activity in general on the dark web in the first half of the year led to the largest dataset Arctic Wolf has ever collected via our dark web monitoring and incident response case data. Compared to the second half of 2022, Arctic Wolf observed an 43% increase in ransomware incidents in our own investigations in the first half of 2023.
Top Threat Actor Groups
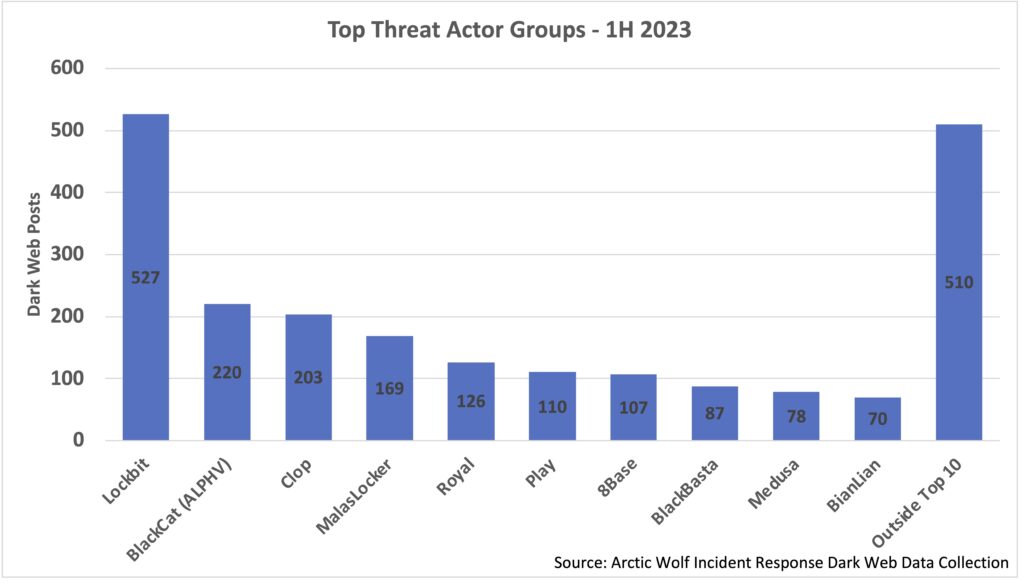
In the first half of 2023, Lockbit was the top posting threat actor group on the dark web, with the volume of postings from the group increasing by over 17% compared to the same period a year ago. However, after a great deal of apparent success in the first four months of the year, May and June 2023 saw a decline in monthly dark web postings from the group, as they were displaced from being the top poster by some emerging groups.
May saw a new group, Malaslocker, emerge which has a large number of Russian-based victims in an initial batch of their dark web postings. While it’s unclear if this is intentional targeting, Malaslocker’s victim locations do not align with what we typically see. This group’s dark shame site and ransom note also includes messaging that suggests more “hacktivism” motivations.
In June, the CI0p ransomware group – first identified in February 2019, was confirmed as the perpetrator behind the large scale MOVEit Transfer exploitations (CVE-2023-34362, CVE-2023-35036, CVE-2023-35708, and CVE-2023-36934). Arctic Wolf tracked CI0p’s activities on dark web ransomware leak sites between June 14 and July 14, 2023. During this period, 169 cases were observed, with the United States topping the list with 120 victims, followed by the United Kingdom (9) and Germany (8).
Apart from MalasLocker that’s currently targeting Russian-based organisations in a potentially more politically-charged play; Cl0p, Lockbit, and the vast majority of attack groups are unsurpringly, motivated financially. No matter a victim’s industry, revenue, or headcount, threat actors will always look for the easiest method to secure a ransom payment. Many have the ability to launch attacks seamlessly via externally-facing vulnerabilities they know how to exploit (Cl0P being a timely example of this) or through sophisticated phishing campaigns, they can send en masse to organisations across the globe.
Top Victim Locations
Across all dark web shame sites, we observed over 2,200 victim posts in the first half of 2023, with essentially half (46.1%) being for US-based organizations. English-speaking countries (US, UK, and Canada) account for the top three victim countries, while for non-English speaking countries in the top-10, on a volume basis, there is little variance in the number of dark web posts.
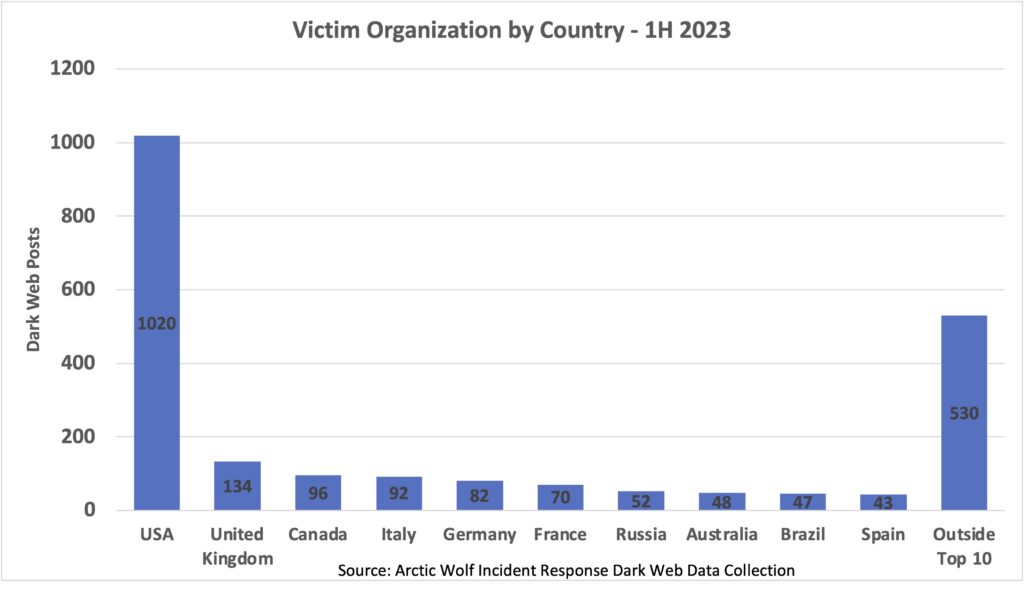
Looking at the same stats on a per capita basis using population data from World Bank, reveals some interesting perspectives. Through this lens, English-speaking countries dominate the top four spots (USA, Canada, UK, Australia), with only Italy being the only non-English speaking country to have a dark web post rate significantly above one post per million citizens.
Additionally, compared to European Union, which is known to have stricter cyber incident disclosure rules and accompanying financial penalties than other regions, organizations in the US, Canada, UK, and Australia, are revealed to be two to three times more likely to find themselves on ransomware shame sites than their non-English speaking counterparts in Germany, France, and Spain.
Top Victim industries
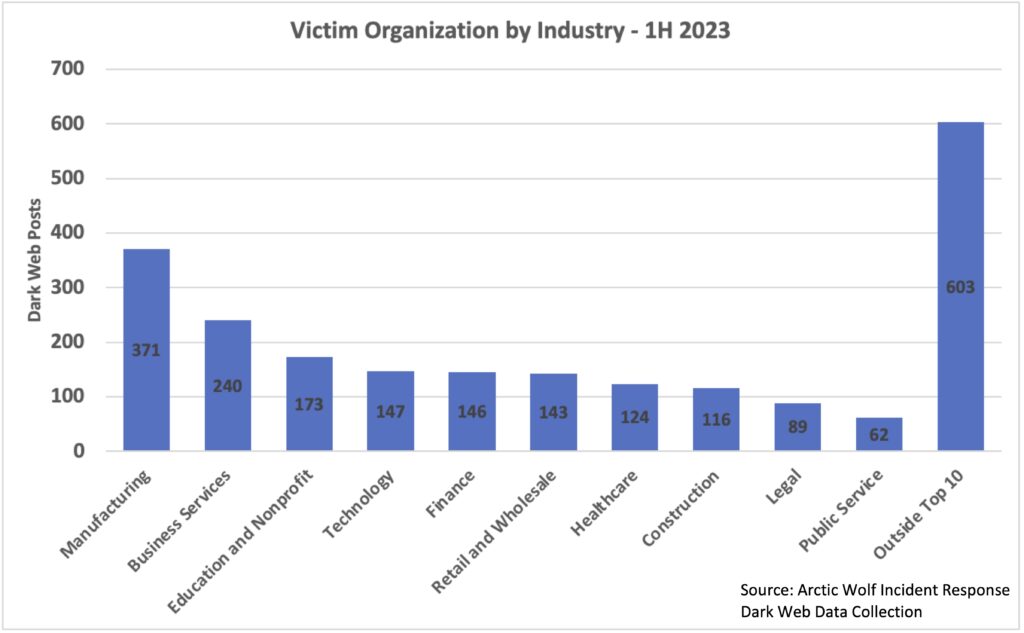
Throughout all months in the first half of 2023, a steady trend of manufacturing victims appearing on dark web shame sites was observed, making them the most impacted vertical by a significant margin. Despite the high number of posts relative to other industries (as shown later in this blog), the median ransomware demand from manufacturing victims was below the median ask in our incident response (IR) cases, revealing that while manufacturing may not have the highest profitability for threat actors, they may be easier to exploit due to the scale and complexity of their operations.
Ransom Demands Rise Across Industries
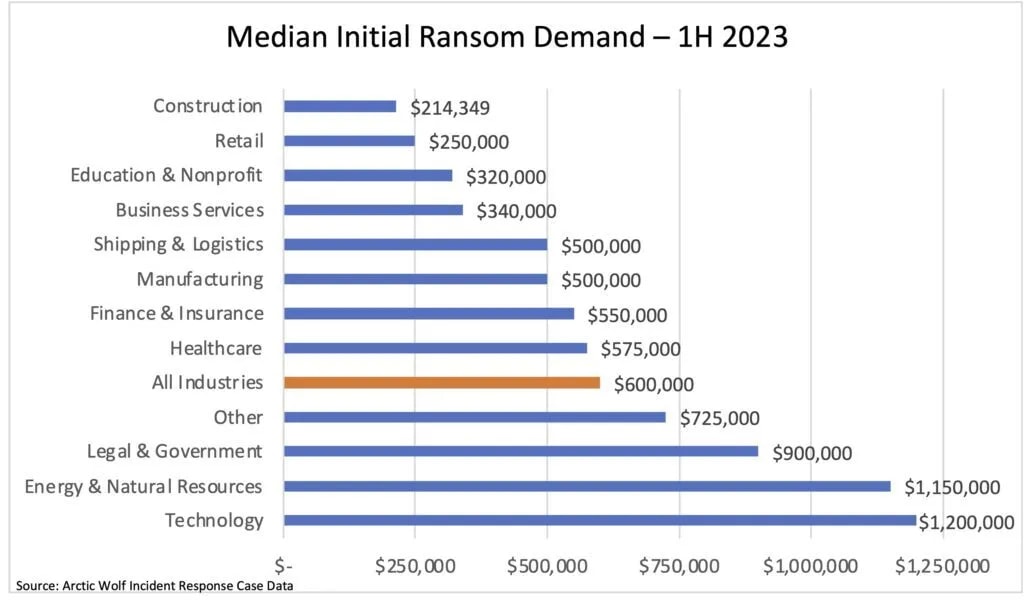
The median ransom demand across all ransomware incidents Arctic Wolf responded to in the first half of the year was USD$600,000, an increase of 43% compared to the same time frame last year.
Have inflationary pressures hit e-crime groups, causing them to raise rates? Not likely, in our opinion. Instead, the fluctuation in median ransom demand is likely a confluence of factors, including ransomware groups trying to maximize bounties after a decline in activities caused by the conflict in Russia and Ukraine, as well as an increase in cryptocurrency values over the past year, which saw Bitcoin increase in value from approximately $25,000 on June 30, 2022, to over $40,000 on June 30, 2023.
Looking at individual industries, compared to the previous year, while there is variance in ransoms demanded in certain industries, technology once again saw the greatest median ransom demand, while construction once again saw the lowest. These stagnant positions reflect the sophistication of threat actors, and how they are well-tuned into how much industries are capable of paying based on both the individual organization’s financial data and their exploitation of thousands of organizations each year.
Important Note: Median figures are used for comparison purposes because the cost of a ransom demand can vary wildly based on the size of the organizations and the threat actor involved. Median figures provide the best approximation of what a “typical” event looks like because very large and very small outlier ransomware incidents can have a significant impact when reporting averages.
SMBs Bear the Brunt of the Damage
With the uptick in ransomware case counts year over year, small and medium businesses (SMBs) were hit especially hard, with 82% of the victims in the first half of 2023 having less than 1,000 employees.
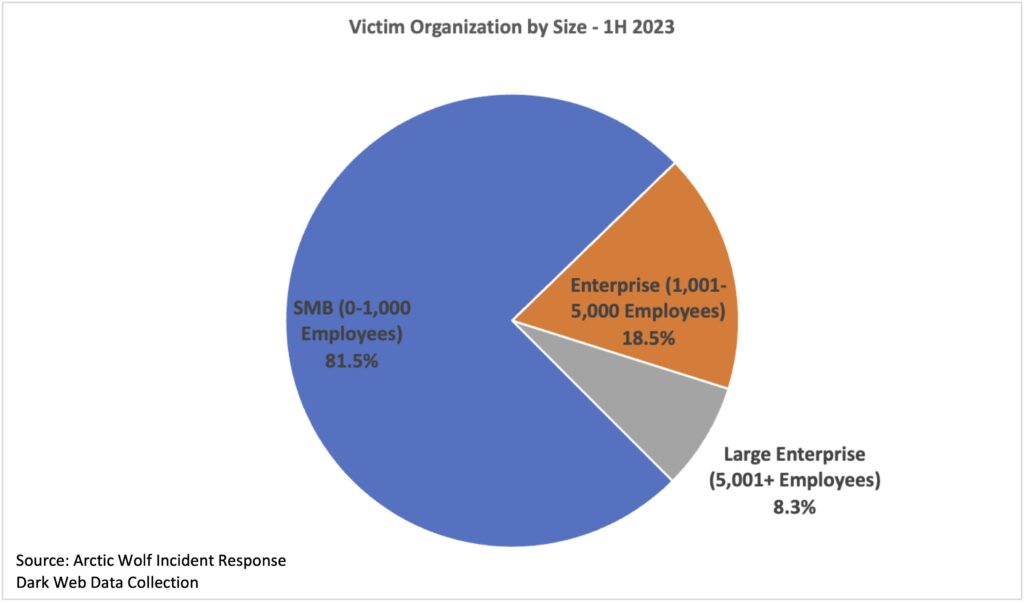
While enterprise and large enterprise organizations are clearly not immune from falling victim to ransomware groups, SMBs are often more challenged to implement an effective Security Operations program, due to a lack of financial resources and internal security expertise. Compared to a large enterprise with billions of dollars in revenue, SMBs are also less likely to be able to withstand the financial impact of a business-disrupting cyber event, which may make some SMBs a more compelling target, as the owners may be willing to quickly pay a ransom to resume operations.
With an uptick in e-crime and dark web activity, this first half review of the incident threat landscape serves as a way for Arctic Wolf to not only share our knowledge with the security community, but also help inform how we build and enhance our detections to anticipate future tactics, techniques, and procedures. We will continue to share additional insights on the incident response landscape and the insights we have as Arctic Wolf works side by side with customers, 24×7, to hunt for activity and deploy new detections—advancing security operations with threat intelligence and analysis to fuel the Arctic Wolf Security Operations Cloud.