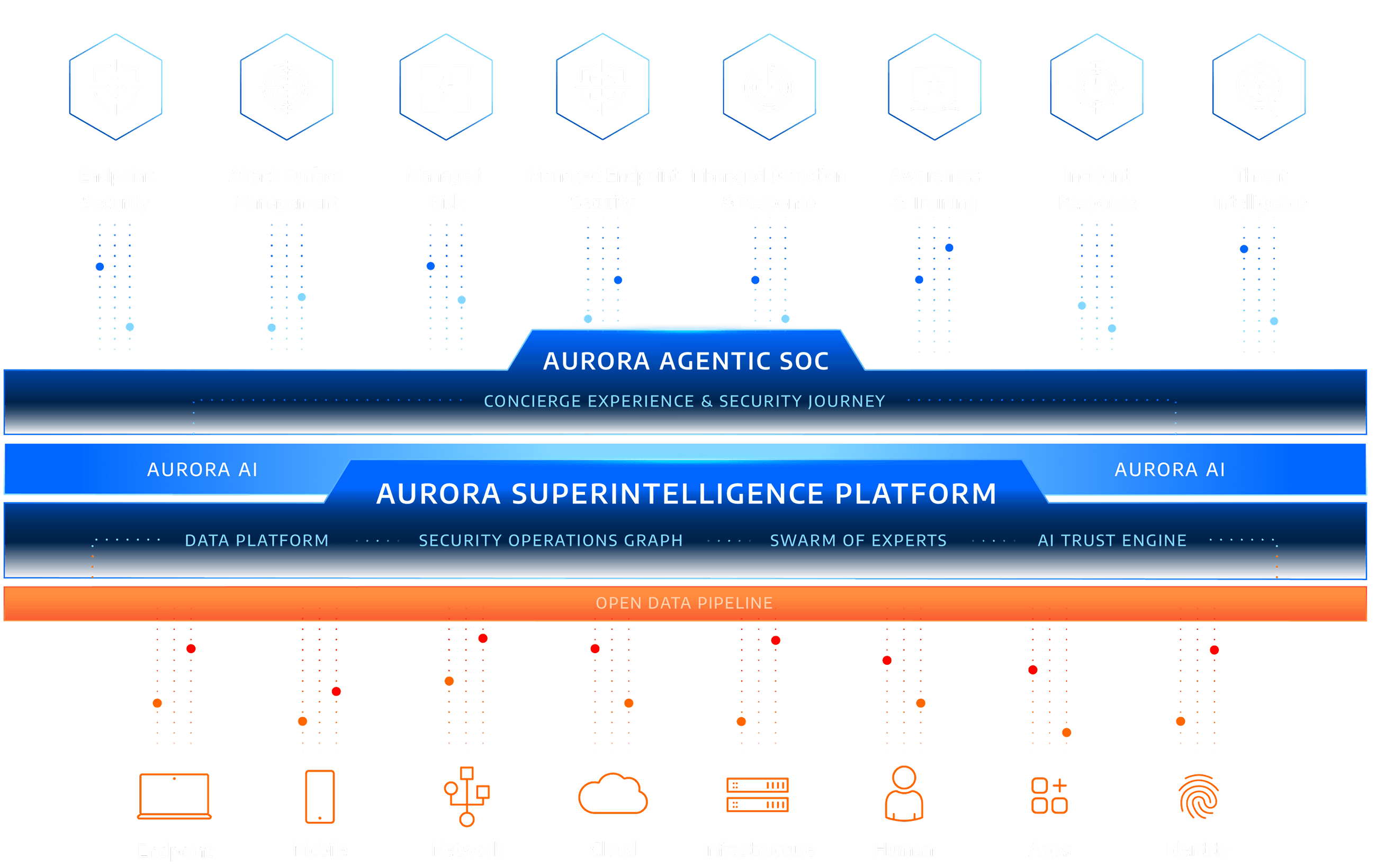
The Aurora® Superintelligence Platform
Delivering AI Outcomes Security Leaders Can Trust
Superintelligent Cybersecurity
The Swarm of Experts™
The Swarm of Experts is Arctic Wolf’s AI-led agentic framework for security operations, orchestrating hundreds of built-in agents across the full range of SOC functions. It coordinates, plans, and executes work end to end, informed by the Concierge Experience and each customer’s unique operating context, with humans in and on the loop for oversight, escalation, and critical decisions.
- Orchestrator
- Judge
- Triage
- Investigation
- Response
- Threat Hunting
- Threat Intel
- Detection Engineering
- Context

Security Operations Graph™
The Security Operations Graph is the platform's proprietary data and intelligence foundation. Built on more than nine trillion telemetry events each week, golden datasets curated over 14+ years by 1,000+ security experts, and customer-specific business context from the Concierge Experience, it gives every agent and workflow the real-world expertise and experience needed to deliver trustworthy outcomes.
AI Trust
Engine™
The AI Trust Engine is the platform's validation process and set of guardrails that help ensure accurate, reliable, and trustworthy outcomes. It bounds agent autonomy, preventing agents from guessing beyond their validated experience and routes to human experts when necessary. All decisions are sent to the Swarm Judge for review, and when a human helps resolve a novel case, those validated outcomes are fed back into the system, expanding what agents can handle autonomously over time.
Open Data Pipeline
How They Work Together
Transforming Security Operation with agentic AI requires a revolutionary new approach to SOC workflows. The Aurora Superintelligence Platform reinvents the legacy operating model by combining a strong data foundation, the Swarm of Experts framework, customer-specific context, and rigorous validation to outperform human-only and AI-only approaches.
Open Data Pipeline
Collects telemetry across an organisation's entire attack surface
Data is parsed, normalised, and enriched into high-fidelity signal
Customer-specific context is created to help downstream agents and workflows act on what is most relevant to your environment
Swarm of Experts™
Oversight Agents coordinate hundreds of specialised agents across core SOC functions
Agents plan and execute work end to end, not as isolated automation
Humans remain in and on the loop for oversight, escalation, and critical decisions
Security Operations Graph™
Leverages 14+ years of security operations expertise and 10K+ customer environments
Brings customer-specific context into every workflow through the Concierge Experience
Provides the massive data foundation required to accurately train and improve AI and ML models
AI Trust Engine™
Deterministic agents operate within bounded autonomy, escalate to humans when confidence is low. The Swarm Judge reviews all agent decisions for accuracy
Humans remain in the loop to handle novel events and provide ongoing reinforcement learning
New agents are battle-tested in the Aurora Agentic SOC before deployment
Superintelligent Outcomes
Faster detection against AI-powered threats across the entire attack surface
Response actions shaped by real-world expertise and customer context
Outcomes that outperform human-only and AI-only approaches
what our customers are saying
"Cybersecurity threats continually transform and mature. Arctic Wolf, however, delivers the tools and expertise to continually monitor our environment and alert on these threats. I rest easier knowing our operations are monitored 24×7 with Arctic Wolf."

"Arctic Wolf’s unparalleled expertise and cutting-edge Aurora Platform will provide us with the confidence and protection necessary to safeguard our operations at every level, ensuring we can dedicate our full attention and energy to what matters most: winning races."

"I don’t need 30 different products to do a million different things. The more I can consolidate and loop in with our existing infrastructure that fits together well, the better it is for us."

"We have seen a 50% reduction in the number of alerts that we’ve had to triage. We like the funnel visualisation because it clearly shows where we need to focus our time."

Meet the Complete Solution for Agentic AI
To rapidly and confidently adopt agentic AI security teams need a complete end-to-end solution that just works. The Aurora Superintelligence Platform, when combined with Aurora AI and the Aurora® Agentic SOC, instantly makes any organisation a leader in AI-powered cybersecurity.
Aurora AI
Aurora AI includes all of Arctic Wolf’s innovation in AI, including the market’s first and longest running predictive AI model for defence against threats. Aurora AI also powers our natural language interface for security operations, Aurora Security Assistant.
Aurora Agentic SOC
The world’s largest commercial Agentic SOC, delivering trusted outcomes with turnkey deployment.
Trusted & Proven
The most consistently validated team in cybersecurity and AI.
Ready to Get Started?
We’re here to help. Reach out to schedule an introductory call with one of our team members and learn more about how Arctic Wolf can benefit your organisation.
General Questions




