PARTNERSHIPS
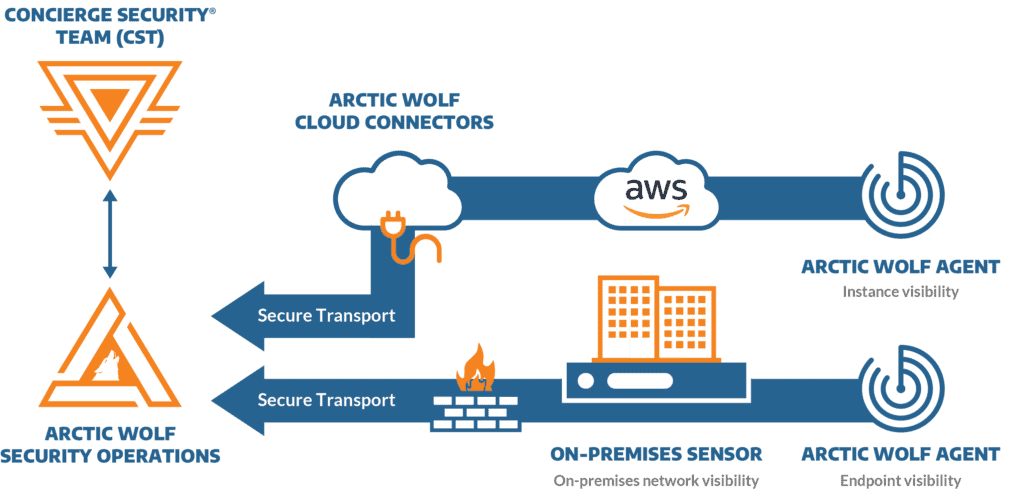
Arctic Wolf detects and responds to advanced threats that impact your cloud-based applications and data hosted in Amazon Web Services (AWS) infrastructure. Our Arctic Wolf Security Teams ensure we have a complete understanding of your unique AWS and IT environment right from the start. Our Security Operations Centre (SOC) then monitors security events enriched and analysed by the Arctic Wolf Platform to provide your team with 24×7 coverage and cloud security expertise. The Concierge Security Team (CST) regularly works with you to proactively identify cloud vulnerabilities and misconfigurations, review your security posture, and create a custom Security Journey to harden your posture over time.
All Arctic Wolf solutions were developed in collaboration with AWS. Our relationship ensures Arctic Wolf technology, processes, and services fully utilise AWS advanced computing, storage, networking, and more. Together, we deliver a fully managed service designed to protect and monitor your essential AWS resources.
Secure Your Cloud Migration With Arctic Wolf and AWS
Centralised Visibility and Monitoring of Your AWS Environment
Arctic Wolf delivers comprehensive visibility into your AWS resources for vulnerability identification and advanced threat detection. Your AWS activity is monitored and correlated with insights from your entire environment—including endpoints, identity, network, and business applications.
24x7 Threat Monitoring
24x7 monitoring for advanced threats delivered by security experts to detect suspicious activity in your AWS environment.
Comprehensive AWS Coverage
Centralised analysis of activity across AWS Security Hub, AWS CloudTrail, Amazon GuardDuty, AWS WAF, and more.
AWS Security Posture Management
Scan and inventory cloud assets, and benchmark and improve security posture.
Host Vulnerability Scanning
Extract vulnerability information from hosts in your AWS environment.
CIS Security Controls Benchmarking
Evaluate the security controls in your AWS hosts against industry standards.
Detailed Reporting
Concierge-delivered and self-service reports of activity across AWS services.
Arctic Wolf Security Operations
Arctic Wolf security operations provides comprehensive AWS monitoring
AWS Data Collection
- Comprehensive AWS Security Hub, AWS CloudTrail, Amazon GuardDuty, and AWS WAF monitoring
- No data volume limits
AWS Events/Alerts Detected
- 120+ alerting rules
- CIS security controls benchmarking
- Sample AWS alerts
- Unauthorised authentication and access
- Suspicious administrative actions
- Brute-force login attacks
The Challenges of Cloud Security
Cloud adoption is rising, but so are cloud threats. Too many IT teams are falling behind.
Number of enterprises today relying on at least one public cloud:
Number of businesses adopting a "multi-cloud" strategy:
Percentage of cyberattacks that are cloud-enabled:
IT teams who lack visibility into cloud infrastructure security: