Key Takeaways
- The Russian Federal Security Services’ (FSB) Snake malware, also known as “Uroburos,” is a highly sophisticated, modular cyber espionage tool used for long-term intelligence collection.
- Snake malware has been used to steal sensitive documents from NATO member governments, journalists, and other targets of interest to the Russian Federation.
- Operation MEDUSA, a court-authorised disruption of the Snake malware network, used the FBI-created tool PERSEUS to disable the malware on target systems.
- An implementation error in the malware’s use of a cryptographic library allowed for communication protected with a weak encryption key to be decrypted by a third party. This potentially played a key role in the ability to monitor FSB operations by intelligence agencies.
Background
On Tuesday 9 May 2023, CISA published a Joint Cybersecurity Advisory titled “Hunting Russian Intelligence ‘Snake’ Malware” which provided an in-depth analysis of the Russian Federal Security Services’ (FSB) Snake malware. Arctic Wolf Labs has analysed the advisory and have summarised the content into key findings and takeaways for the security community.
Notably, on the same day, the Justice Department announced a court-authorised disruption of the Snake malware network, code-named MEDUSA. Throughout operation MEDUSA, the FBI and the U.S. Attorney’s Office for the Eastern District of New York neutralised the Snake malware network using a custom FBI-created tool called PERSEUS.
In late 2003, the FSB began developing Snake, aka “Uroburos”, a highly sophisticated, modular cyber espionage tool used by Center 16 of the FSB. Snake was designed for long-term intelligence collection.
The initial versions of Snake were completed around 2004. The name “Uroburos” appeared in earlier versions of the code as unique strings. At the time, a low-resolution image of the historical illustration of an Uroboros was used as the backdoor key, solidifying the name. In 2014, the developers of Snake left inside jokes or personal interests as well as taunts at security researchers due to public cybersecurity reporting.
Snake operations were attributed to Center 16 of the FSB, which also operate the family of implants commonly referred to as the Turla toolset. Snake is a core component of the unit’s operations and has extensive influence across the Turla toolset. Daily operations using Snake have been carried out from FSB facilities in Ryazan and Moscow in Russia.
Snake’s source code has served as the basis for other implants such as Carbon (aka Cobra) and Chinch (aka ComRAT).
Victimology
For nearly 20 years, Snake malware has been used to steal sensitive documents from NATO member governments, journalists, and other targets of interest to the Russian Federation. International relations documents and diplomatic communications were exfiltrated over a covert network of Snake-compromised computers. An international coalition of cybersecurity-focused government agencies have identified Snake malware infrastructure across North America, South America, Europe, Africa, Asia, and Australia, including the United States and Russia.
In the U.S., the FSB has victimised industries including, but not limited to:
- Critical Infrastructure – local government, finance, manufacturing, and telecommunications
- Education Institutions
- Small Businesses
- Media Organisations
Operation MEDUSA disabled Turla’s Snake malware on compromised computers in the United States through the use of the FBI-created tool: PERSEUS. For victims outside the United States, the FBI is engaging with local authorities to provide both notice of Snake infections within those authorities’ countries and remediation guidance.
Technical Analysis – Key Architecture Aspects
Snake source code is written entirely in C, which provides the advantages of low-level system control and efficiency. The Snake malware was designed to run on Windows, Linux, and MacOS.
Modularity
Snake’s architecture was designed using well-established software development concepts. These concepts included: clearly defined interfaces, modularity, and factory patterns to ensure the integration of new features as well as ensuring the right component is used based on environmental considerations.
As an example, the network stack implements the encryption layer and transport layers using clearly defined interfaces. Protocols such as HTTP or raw TCP sockets will inherit encryption by interfacing with the encryption layer.
The modularity allowed for the malware to utilise environmental factors to ensure communications were successful. For example, when compromising an HTTP server, the operators can ensure that all traffic for the machine uses the custom Snake HTTP protocol. This allows the malware traffic to blend into the existing victim traffic. For a compromised machine that allowed SSH traffic, the custom Snake raw TCP socket protocol is used instead.
As long as the interfaces were implemented correctly, the custom transport layer and adjacent command processing layers can remain agnostic. This level of design is sophisticated and demonstrates the expertise and professionalism by the Snake development team.
Kernel Driver
The sophistication of the Snake attack chain contains a kernel driver and custom loader, which the Snake installer will decrypt and load utilizing platform-specific APIs. The Windows Cryptographic API: Next Generation (CNG) is used to store the AES key needed to decrypt a Windows registry object which contains the kernel driver. This driver is typically named ComAdmin.dat. The image below shows the registry structure and the ComAdmin structure.
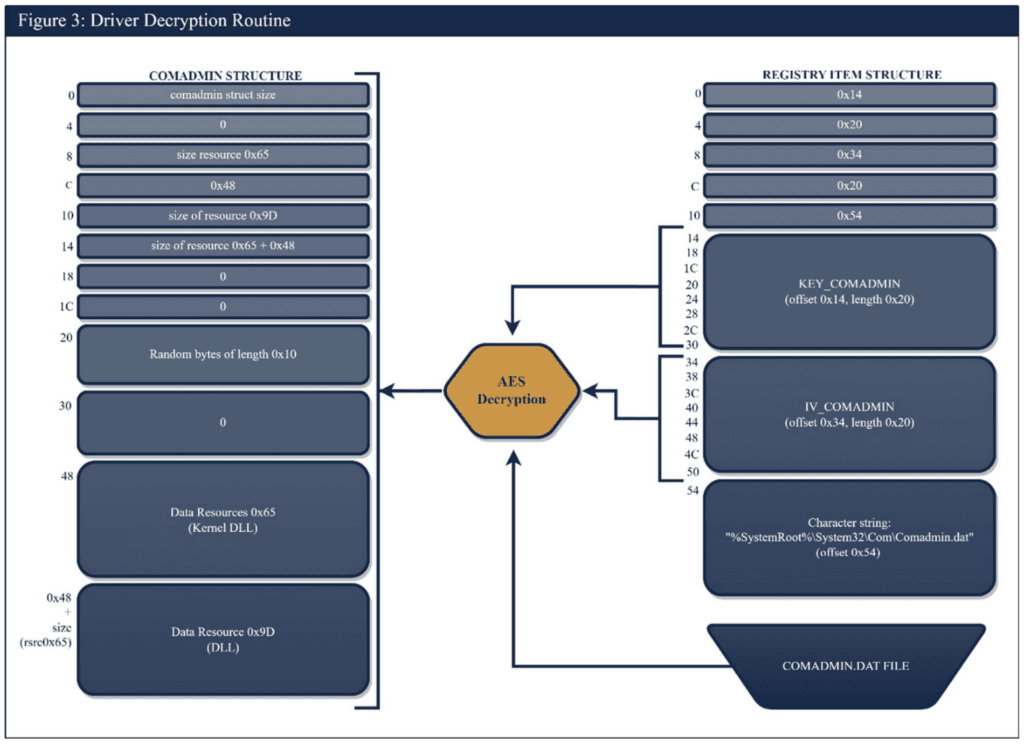
Driver decryption routine (Source: CISA Joint Cybersecurity Advisory: Hunting Russian Intelligence “Snake” Malware)
The Windows registry object contains the Key, IV, and a path to the ComAdmin.dat file. Once the file is decrypted, the installer will drop a kernel driver and a custom DLL used to load the kernel driver in the %windows%\system32\Com directory.
The kernel driver is responsible for facilitating key features of the Snake Malware attack chain. Specifically, decrypting files, passing information between kernel and user mode components, and stealthy network communication.
Network
Snake’s network communications are encrypted, fragmented, and sent using custom methodologies that ride over common network protocols, including both raw TCP and UDP sockets, and higher-level protocols like HTTP, SMTP, and DNS. Snake’s protocols for HTTP and TCP are the most commonly seen, but functionality exists for UDP, ICMP, and raw IP traffic.
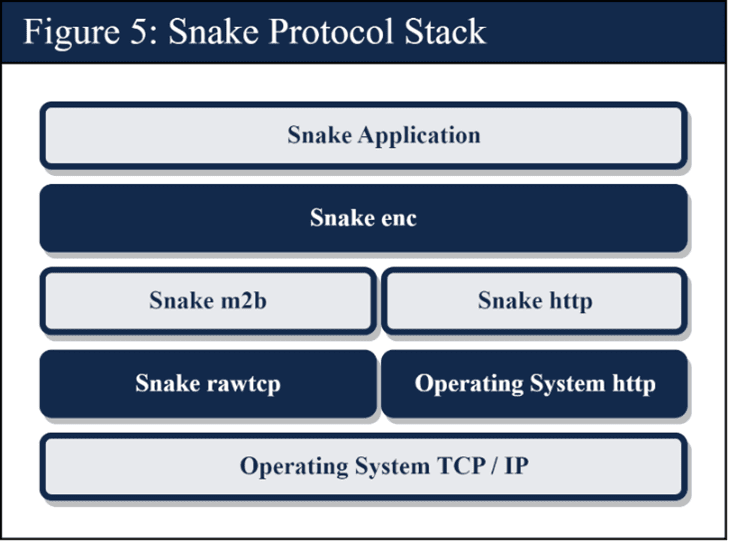
Snake Protocol Stack (Source: CISA Joint Cybersecurity Advisory: Hunting Russian Intelligence “Snake” Malware)
Snake implements its own custom sessions, which are distinct from the underlying protocols (i.e. TCP session). Snake also utilizes multiple encryption mechanisms, one method to secure the “Snake sessions” between P2P nodes (i.e. Snake enc) and a separate method for the application layer (i.e. Snake Application). The Snake Application layer provides end-to-end encryption between the controller (i.e. point of origin) and the command’s ultimate destination.
Typically, Snake malware is deployed to external-facing infrastructure nodes on a network. From there, it uses other tools, and tactics, techniques, and procedures (TTPs) on the internal network to conduct additional exploitation operations.
Stealth
Snake has a unique and sophisticated ability to function effectively as a server without opening ports on the compromised system. Instead, Snake’s kernel module intercepts network traffic and determines whether or not the contents of a packet are intended for the Snake implant or not. If the packet is a Snake packet, it is forwarded to the implant, and if it is not, then it’s passed through to the legitimate application that is listening on the port it’s sharing with the Snake implant. The kernel module utilises a specific authentication mechanism based on random nonces, auxiliary data, and hashes to authenticate the sending Snake machine. The authentication mechanism differs slightly between the HTTP and TCP implementations of the Snake protocol.
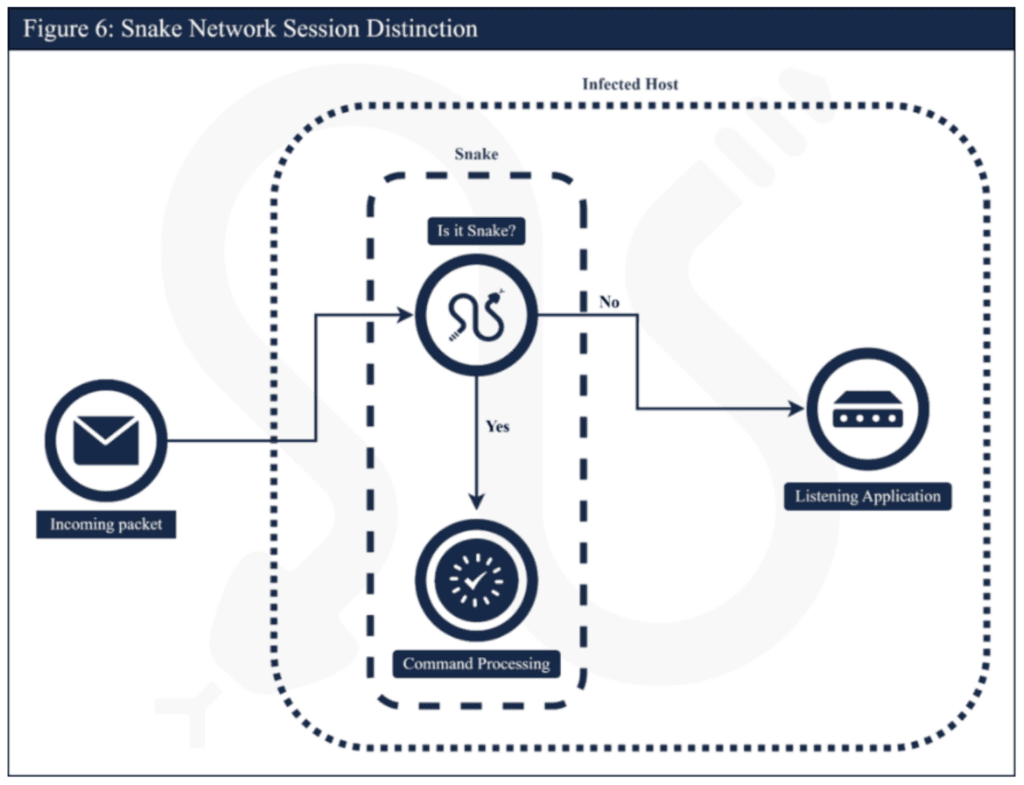
Snake Network Session Distinction (Source: CISA Joint Cybersecurity Advisory: Hunting Russian Intelligence “Snake” Malware)
Utilising the above techniques allow the Snake implant to blend in with the legitimate traffic on the compromised server. Snake will only communicate over TCP ports on which another application is actively listening. This technique makes detecting Snake compromises through network traffic monitoring far more difficult as there may be a single Snake packet intermixed with hundreds of legitimate packets destined for a legitimate running application.
P2P Network
Unlike traditional client-server Command & Control (C2) infrastructure deployments where the attacker and victim machines communicate directly over a socket, Snake uses a Peer-To-Peer (P2P) mechanism to send commands to the compromised machine. Those commands may traverse one or more relay Snake nodes before the command is delivered to the target machine. The relay traffic between the Snake nodes is encrypted using the “Snake Session” (i.e. Snake enc) in the protocol stack diagram above. Using P2P makes it significantly more difficult to identify the true C2 server the FSB operatives are using as the relay nodes in between provide an additional layer of anonymity. With a P2P communication infrastructure, Snake nodes can have two modes of operation: Active and Passive.
During Active operations, Snake commands are issued by an FSB operator to a target machine through “Forward” commands as described above. The result of the command is returned to the point of origin following the same path that the command took to reach the target. Attackers use this mode to interact with the compromised machine and deploy additional post-exploitation tools.
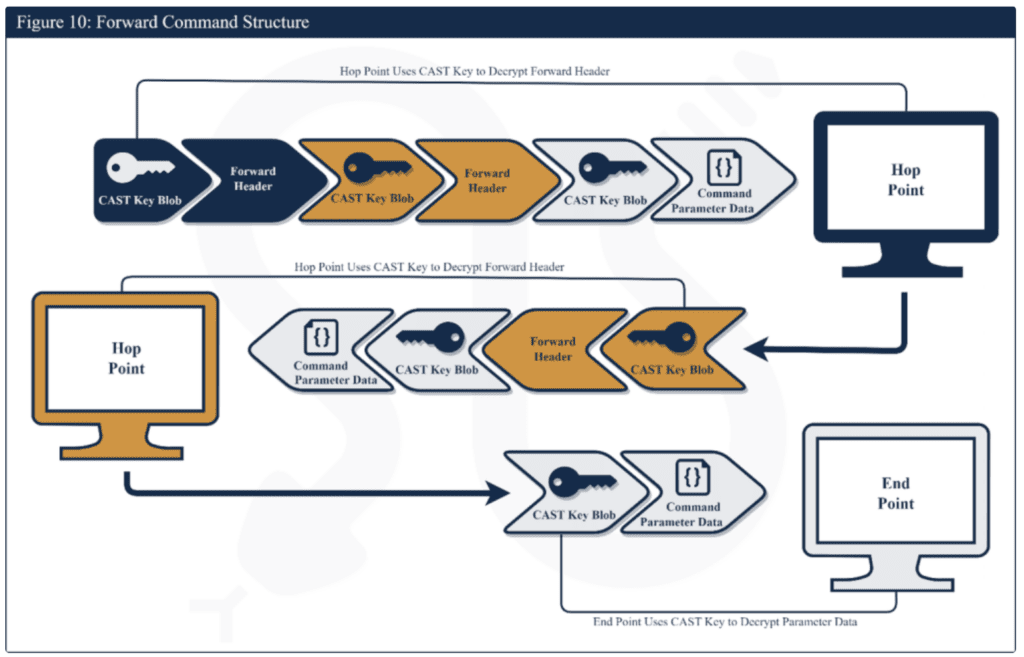
Forward Command Structure (Source: CISA Joint Cybersecurity Advisory: Hunting Russian Intelligence “Snake” Malware)
During Passive operations the Snake implants operate on their own without interaction from FSB operatives. The Snake implant maintains a list of nodes with which it communicates to maintain connectivity to the FSB operators. It periodically beacons out to check if new commands have been issued that it needs to execute. The Snake implant also has the capability to passively exfiltrate data. It can randomly select one of the nodes in its internal list and write data to it – the data can be a file, a screenshot, a keystroke log or even audio/video depending on the post-exploitation steps undertaken by the FSB operatives.
A Key Mistake – Cryptography
The communication methods used by the malware leverage OpenSSL to perform Diffie-Hellman key exchange. A critical mistake was made when calling a function that generates secure communications keys. Instead of generating a 128byte prime number for initialisation the malware authors generate a 128bit (16-byte) key.
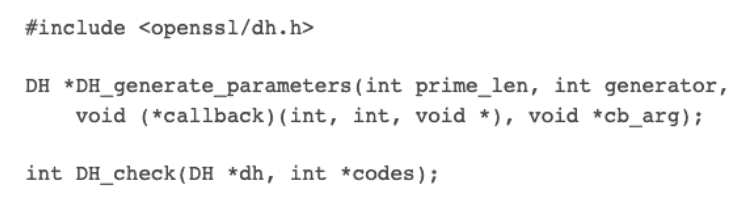
Function Prototype openssl/dh.h (Source: OpenSSL Library)
As a result, communication protected with this key could be decrypted by a 3rd party. This flaw combined with the P2P nature of the malware architecture may have played a key role in intelligence services ability to monitor FSB operations.
Encryption also plays a key role in obfuscating the kernel driver and driver loader. They leverage Microsoft Windows Cryptography API: Next Generation (CNG) key store to store the AES keys needed to decrypt objects. The malware also employs CAST-128 to encrypt and decrypt data used for malware operation. Keys to decrypt this structure are stored as strings in Snake’s kernel driver.
The Take Down – Operation MEDUSA
On May 9th 2023, the Justice Department announced the completion of the court-authorised operation code-named MEDUSA. The operation focused on the disruption of the global P2P malware network. The operation disturbed the operation using a newly built tool by the FBI named PERSEUS. The PERSEUS tool was designed to issue commands which would cause the Snake malware network to overwrite its vital components and effectively disable the malware on the target system.
The Criminal Division’s Computer Crime and Intellectual Property Section provided valuable assistance. Those efforts would not have been successful without the partnership of numerous private-sector entities, including those victims who allowed the FBI to monitor Snake communications on their systems.
Detection Opportunities
CISA has released their own set of detections and IOCs for Snake malware which can be reviewed in the Mitigations section of their report here. Arctic Wolf is actively reviewing the CISA provided detections to determine feasibility of leveraging them, and is also reviewing IOCs and TTPs contained in this report to explore new detection opportunities.
Recommendations
- Administrators that believe their system may be compromised are advised to change credentials from a secure system and execute their Incident Response & Recovery process.
- A tool has been released in the Appendix of the Joint Cybersecurity Advisory (Page 47) that leverages volatility3, a python framework for memory forensics. The tool is designed to identify injected user-mode components of Snake in the memory of a Windows system. When executed, the plugin analyses the processes, searches for the Snake’s user-land injected components, and provides detailed information about the affected processes and memory regions.
- According to the DOJ, Operation MEDUSA did not patch any vulnerabilities or search for other existing hacking tools on victim machines. The Department of Justice strongly encourages network defenders to review the Joint Advisory for further detection and patching.
References
- Joint Cybersecurity Advisory – Hunting Russian Intelligence “Snake” Malware
- Justice Department Announces Court-Authorized Disruption of Snake Malware Network Controlled by Russia’s Federal Security Service
- NSA – U.S. Agencies and Allies Partner to Identify Russian Snake Malware Infrastructure Worldwide
- OpenSSL GitHub Repository
Authors
Christopher Prest | Lead Security Researcher
Christopher is a lead security researcher and a 17 year veteran in Software and Application security development, coupled with 2 years of cutting edge detection engineering and security research. A seasoned expert, Christopher focuses on Malware analysis and reverse engineering to shape the future of cybersecurity.
Constantine Grantcharov | Lead Security Researcher
Constantine Grantcharov is a Lead Security Researcher at Arctic Wolf Labs focused on Adversary Emulation and Malware Analysis.
Jeremy Richards | Lead Security Researcher
Jeremy is a Lead Security Researcher at Arctic Wolf Labs and has nearly two decades of experience Reverse Engineering malware, security patches, and firmware.




