Arctic Wolf Managed Risk
Concierge-Led Managed Risk Experience
Managed Prioritization and Personalized Protection Delivered by Your Concierge Security® Team
The Concierge Security Team is a force multiplier to your existing security team. If you don’t have a security team, you gain instant access to security professionals that are otherwise difficult, if not impossible to find.
Your named Concierge Security engineer works with you to prioritize vulnerabilities discovered from networks, endpoints, and cloud environments.
- Discover
- Assess
- Harden
Then the Concierge Security Team contextualizes your attack surface coverage with risk policies, asset criticalities, and SLOs (service level objectives). This contextualization enables you to prepare your environment to end cyber risk.
Once we have that perspective, the Concierge Security Team assesses and provides you with the risk priorities in your environment.
Benefits of Managed Risk
24x7 Continuous
Monitoring
Around-the-clock monitoring for vulnerabilities, system misconfigurations, and account takeover exposure across your endpoints, networks, and cloud environments.
Strategic Recommendations
Your named Concierge Security engineer becomes your trusted security advisor, working with you to make recommendations that harden your security posture over time.

Personalized Engagement
Regular meetings with your named Concierge Security engineer to review your overall security posture and find areas of improvement that are optimized for your environment.

Managed Risk Addresses the Most Critical Cybersecurity Challenges
Undetected Risks
Most vulnerability scanners miss digital risks beyond software defects, like system misconfigurations and corporate credential exposure.
Too Many Alerts
The sheer volume of vulnerabilities, both detected and exploited, is increasing sharply. IT and security teams are becoming overwhelmed by too many alerts and not enough context.
Limited Asset Visibility
If you can’t see it, you can’t protect it. Yet, most organizations are unable to accurately account for assets in their environment. This leads to gaps in posture that leave the door open to attackers.
The action variety of Exploit vulnerability is up to 7% of breaches this year, doubling from last year. - - - - - -
Data Breaches in Review for 2022
Discover the Risks that traditional tools miss
Product-based vulnerability scanners miss digital risks that are not specifically software defects.
How it Works
The Arctic Wolf Managed Risk Process


Deployment
Our team will work with you to deploy the Arctic Wolf Platform, integrate critical data points, and build an understanding of your network.


Configuration
Gain clear understanding and visibility into your attack surface by establishing asset context and a vulnerability baseline.


Active Cycle
The Active Vulnerability Management Cycle phase is a steady state and continuous cycle aimed at providing proper coverage, prioritizing risks, hardening of your environment, and ensuring mitigation efforts are successful.
-
Installation and Integration






 Installation
Installation
Stage -
Concierge Kick-Off






 Core
Core

Stage -
Identity and Coverage Resolution






 Fundamentals
Fundamentals
Stage -
Define and Configure Asset Context






 Fundamentals
Fundamentals
Stage -
Threat Landscape and Prioritization Review






 Optimized
Optimized

Stage -
Active Vulnerability Management Cycle






 4 Ongoing
4 Ongoing

Phases
Installation and Integration
Installation Stage
In the installation and integration phase, Arctic Wolf configures and validates the environment, and makes reports available for the internal, external, and agent-based scanners as well as Cloud Security Posture Management.
Concierge Kick-Off
Core Stage
Begin the proactive Managed Risk security process with your Concierge Security Team where we learn about your environments, policies, procedures, patching cycles, service level objectives (SLOs), and more to gain a better understanding of your attack surface.
Identity and Coverage Resolution
Fundamentals Stage
Your Concierge Security Team delivers your overall vulnerability management program context, providing insight on your current device and network coverage, as well as identity issues within the environment. We provide recommendations to fix the coverage issues and ensure we have completed coverage of your entire attack surface.
Define and Configure Asset Context
Optimized Stage
Next, Arctic Wolf provides an initial critical asset list. This list is reviewed with you to identify any gaps. We then recommend asset criticalities, workflow, and organization tagging to make your environment more contextualized.
Threat Landscape and Prioritization Review
Optimized Stage
Finally, Arctic Wolf provides you with tailored risk prioritization according to asset and risk context on your overall attack surface so you can begin patch management.
Active Vulnerability Management Lifecycle
4 ongoing phases
The goal of the Active Vulnerability Management Cycle is to ensure proper coverage, provide prioritization of risks, allow us to consult as the customer is hardening their environment, and ensure the mitigation efforts are successful. It is accomplished through 4 sub-phases that are continuously cycled through.
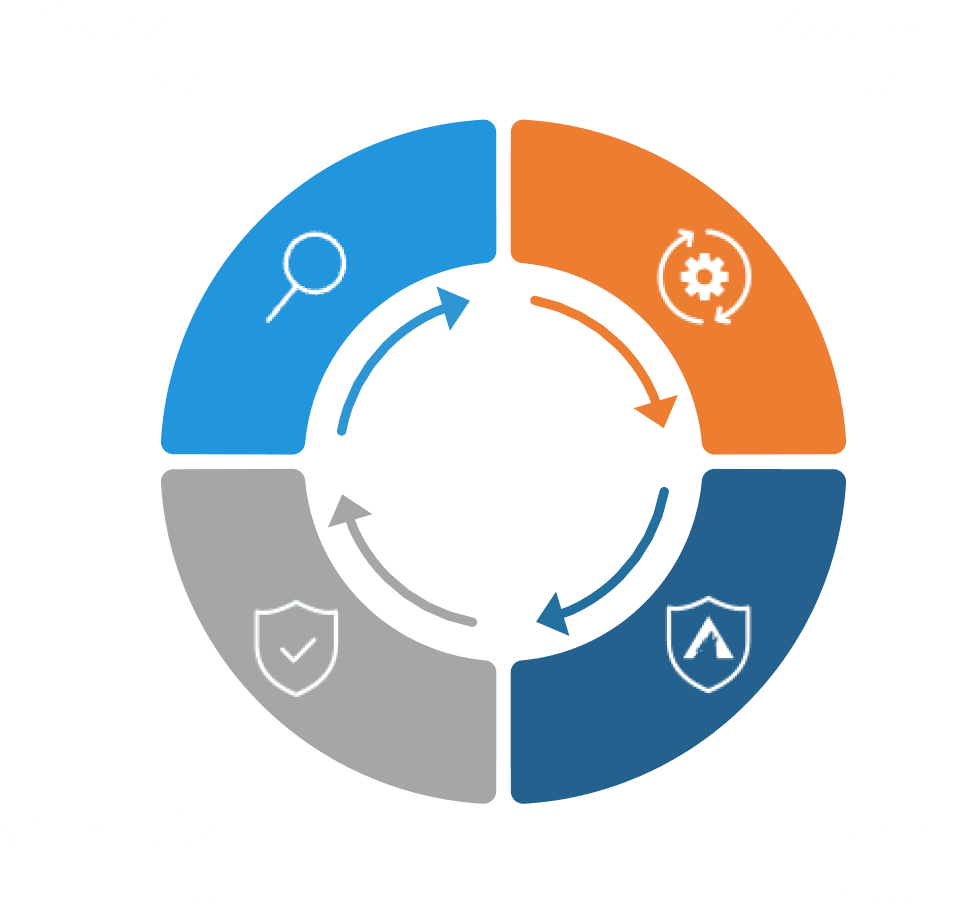
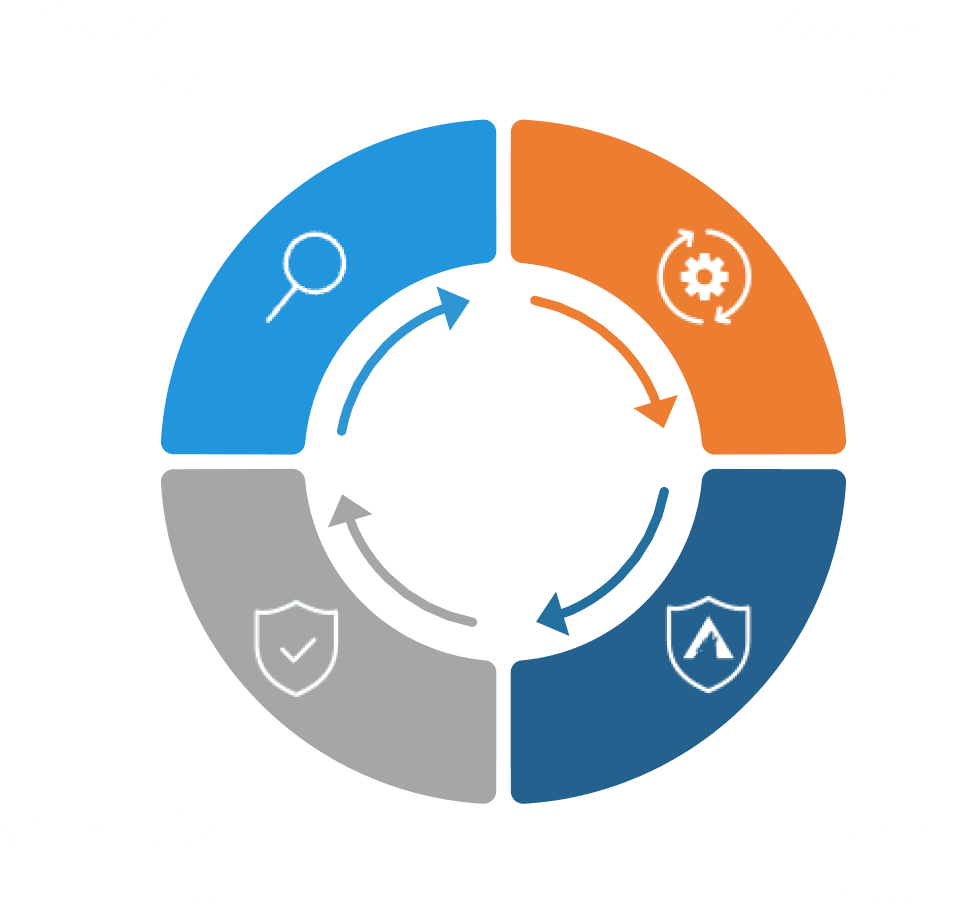


Discover
Identify differences between the initial or previous asset baseline to understand your attack surface.


Assess
Get risk metrics and prioritized risk links to provide a clear understanding of priority risks and to support assigning them to their mitigation team.


Harden
Resolve priority risks and work towards reducing overall risk with your CST supporting you through the process.


Validation
See progress made towards reducing overall risk by rescanning risks to ensure mitigation efforts were successful.
Digital Risk by the Numbers
The growing attack surface compounds cyber risks for organizations. The implementation of new digital initiatives, the adoption of the Internet of Things (IoT), and the continued move to the cloud help drive innovation—but at the cost of increased exposure to threats. Risk management solutions are becoming the norm to combat this issue.
40% of mid-size enterprises have a formal vulnerability management program in place:
60% of IT risk management roles predicted to become dependent on risk management solutions to aggregate digital risks in their business ecosystems by 2025:
Implementing the Center for Internet Security’s (CIS) top five critical security controls can prevent 80% of the most common cyber attacks:
- Gartner
- Gartner
- CIS
Gartner predicts that through 2025, more than 99% of cloud breaches will be traced back to preventable misconfigurations or mistakes by end users. - - - - - - -
Cloud Security Posture Management Extends Managed Risk to the Cloud
The cloud is the new frontier in business IT—and in cyber risk.
Cloud Security Posture Management (CSPM) extends Arctic Wolf Managed Risk to this new frontier, providing cloud asset auditing, environment benchmarking, plus posture hardening and remediation guidance.
The Most Exploited Vulnerabilities of 2023
There were over 29,000 vulnerabilities published in 2023, amounting to over 3,800 more common vulnerabilities and exposure (CVEs) being issued last year than in 2022. With so many vulnerabilities in play, which ones offered the greatest risk to organizations — and the greatest potential reward for threat actors?
AVAILABLE NOW!
Gartner® Peer Insights™ 'Voice of Customer': Vulnerability Assessment Report
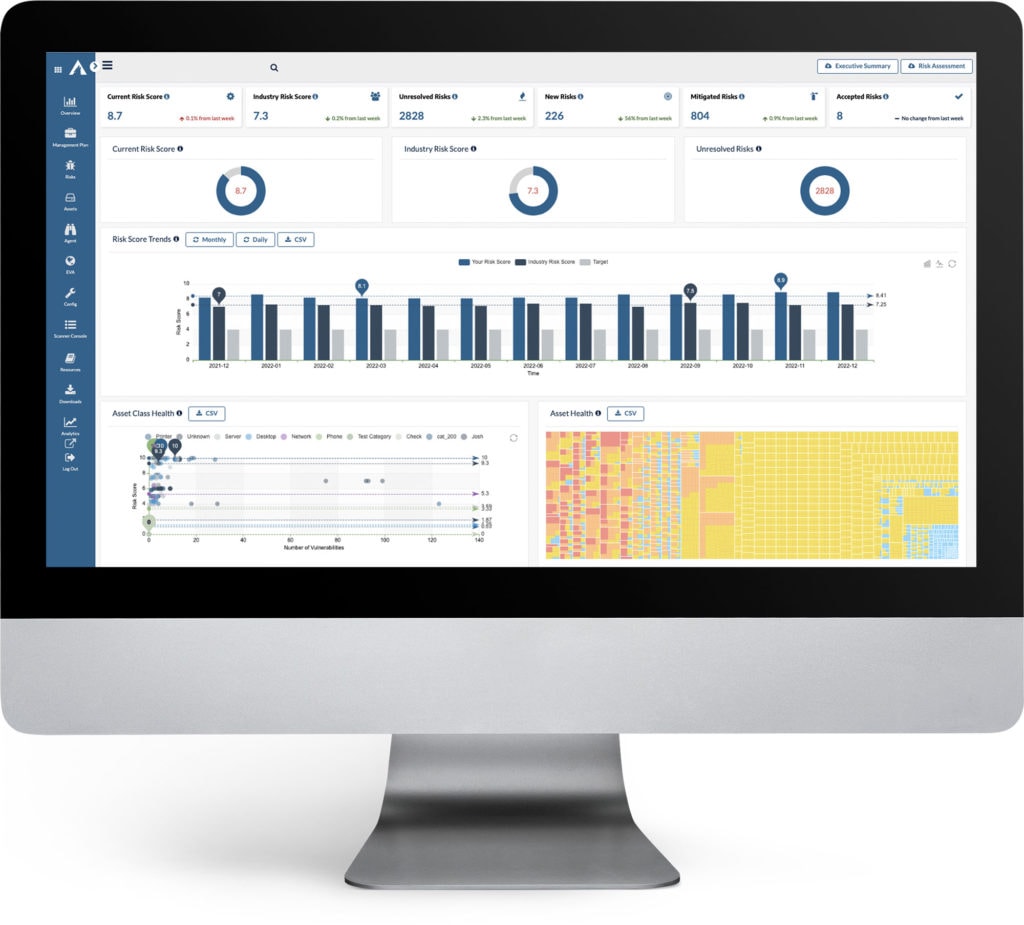
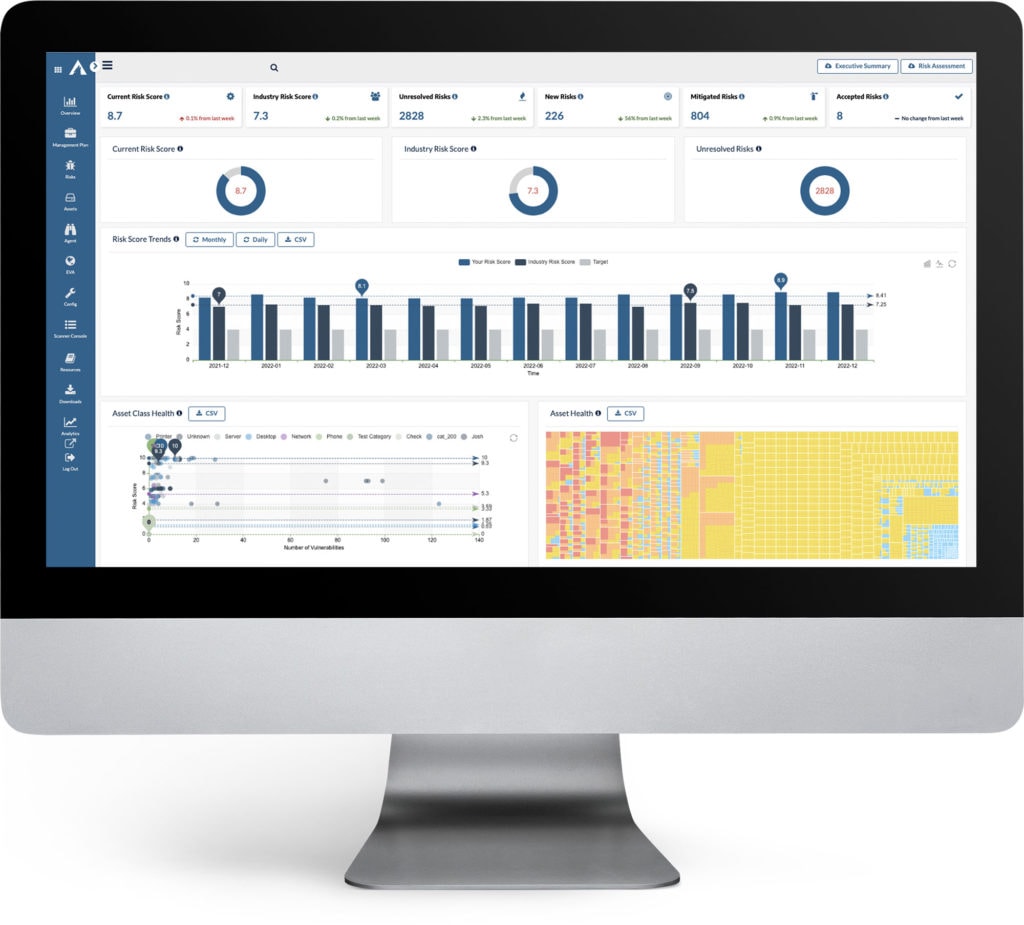
See your current risk score.
See how you are doing against your industry peers.
See your overall trending risk score.
See your overall asset health.
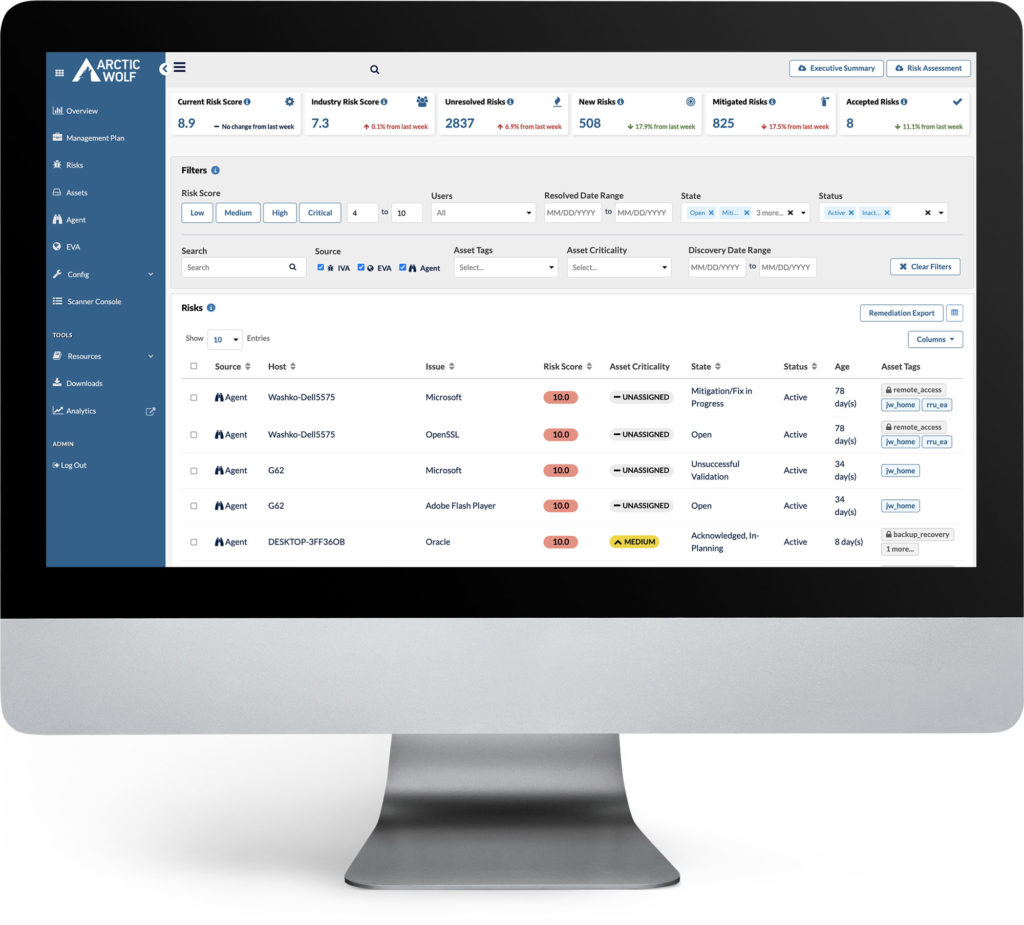
Filter down by the risk score.
Filter by resolved date.
Filter by state including: Open, False Positive, In-Planning, Mitigated and more.
Filter by status - Active; Inactive; Obsolete; Mitigated.
Filter by asset tags that your CST helps you to create.
Filter by asset criticality that your CST helps you assign.
Filter by risk discovery date.
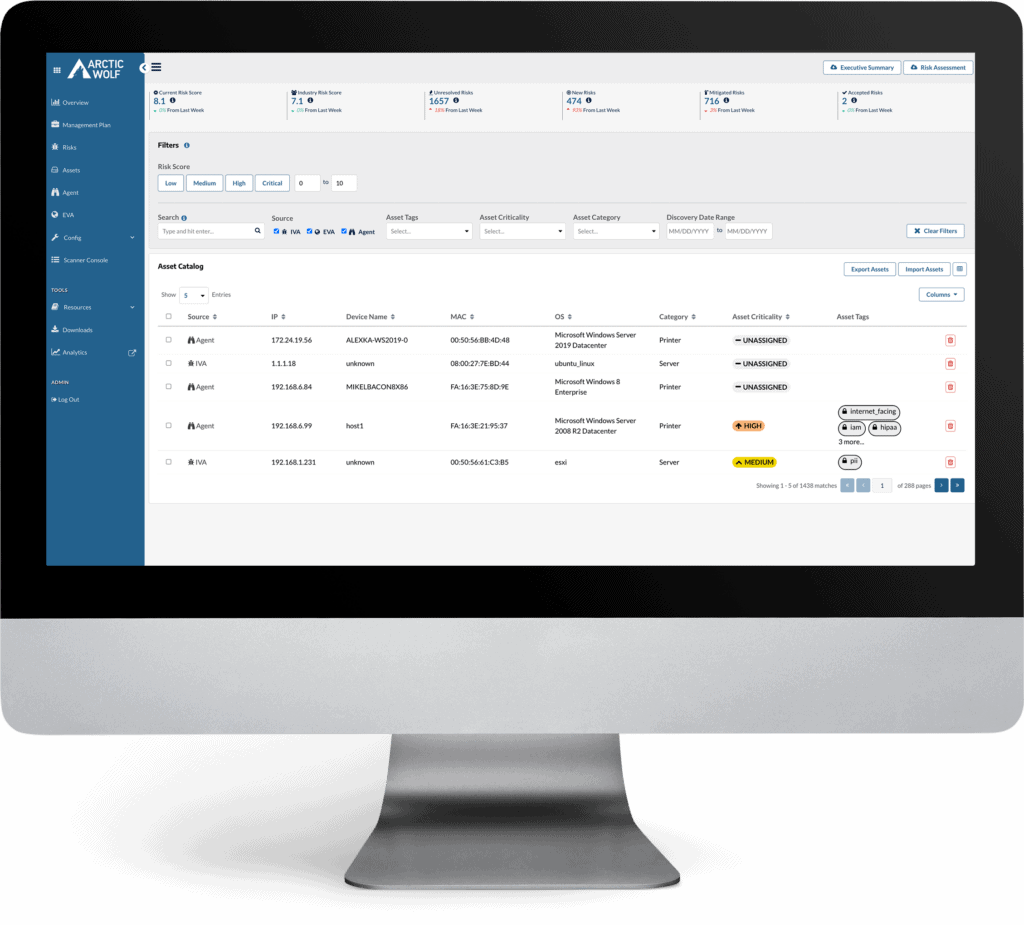
Filter down your assets by risk criticality.
Filter by asset criticality that your CST helps you assign.
Filter by asset category that automatically gets assigned.
Filter by risk discovery date.
See the Managed Risk Dashboard in Action
The Arctic Wolf Managed Risk Dashboard is a cloud-based portal that provides visibility into the real-time risk landscape on your networks, endpoints, and cloud environments. We tailor the dashboard to your organization’s priorities to help you make sense of vulnerabilities, while also managing and prioritizing patching to reduce cyber risk exposure.
A single interface for all things cyber risk:
-
Visibility into your cybersecurity posture, including prioritized threats and your overall cyber risk score
-
Insight into your organization’s risk trends and industry comparisons
-
Operational optimization by giving insight into prioritizing your information security and technology activities


Security Operations Warranty
Arctic Wolf Security Operations Warranty
Cybersecurity, IT, and risk management leaders need a plan to manage the outcomes of inevitable cyber attacks against their businesses. Through Arctic Wolf Managed Risk, get access to the Arctic Wolf Security Operations Warranty, a no-cost customer benefit that provides up to $1,000,000 in financial assistance for cybersecurity incidents.
Gartner® Peer Insights™












ARCTIC WOLF CASE STUDY
“Cybersecurity threats continually transform and mature. Arctic Wolf, however, delivers the tools and expertise to continually monitor our environment and alert on these threats. I rest easier knowing our operations are monitored 24×7 with Arctic Wolf.”
AJ Tasker,
Vice President and Director of IT, First United Bank & Trust


Managed Risk Resources for Vulnerability Management
Arctic Wolf Spring4Shell Deep Scan Tool
Arctic Wolf Offers Tool to Mitigate the Impact of Log4j (Log4Shell)
Arctic Wolf’s open source Log4Shell Deep Scan enables detection of both CVE-2021-45046 and CVE-2021-44228.
Latest Security Bulletins
Predictable Pricing
Arctic Wolf Managed Risk pricing is based on stable parameters including users and servers, allowing businesses to fully secure environments while controlling costs.
Ready To Get Started?
General Questions:
1-888-272-8429
ask@arcticwolf.com