ARCTIC WOLF
Cloud Detection and Response
Arctic Wolf® Cloud Detection and Response identifies and stops threats across IaaS and SaaS resources.
HOW IT WORKS
CHALLENGES
of security threats start in the cloud.
Configuration
Overload
IT teams adopting multiple cloud platforms and services struggle to properly configure even basic security controls, logging, and monitoring.
Policy
Complexity
Most cloud security products are difficult to set up and require frequent policy adjustments which often results in security gaps in the fast-moving world of cloud resources.
Cloud
Skills Gap
Finding security experts who are also cloud experts is exceedingly difficult for most organizations.
By the Numbers
The Challenges of Cloud Security
Cloud adoption is rising, but so are cloud threats. Too many IT teams are falling behind.
43%
43%
of IT Teams lack visibility into cloud infrastructure security.
44%
44%
of cyberattacks are cloud-enabled.
84%
84%
of businesses are adopting a "multi-cloud" strategy.
94%
94%
of enterprises today rely on at least one public cloud.
Arctic Wolf®
Cloud Detection and Response
Detect
24x7 SaaS and IaaS Monitoring
Monitor SaaS and IaaS solutions to detect key threats or risks such as phished credentials, impossible travel, or malicious integrations.
Immediate Protection
Service launches with preconfigured detection logic, allowing monitoring to immediately detect the highest-priority attacks.
Tailored Service
With rules tailored to your business environment, see things that others miss while also preventing alert fatigue.
Respond
Managed Investigations
We investigate suspicious activity so you don’t have to, making alert fatigue and time wasted on investigating false positives a thing of the past.
Log Retention and Search
Takes the work out of managing logs, enabling you to easily conduct additional investigations, if needed.
Cloud Incident Response
Every second counts. Detect and respond to critical security incidents within minutes to prevent the spread of threats.
Recover
Guided Remediation
We work with you on detection, response, and remediation to validate the threat has been neutralized and verifying it hasn’t returned.
Management
Our cloud security solution is maintained, tuned, and configured by our Concierge Security® Team to collect the right data and provide the right alerts without extra work from your IT teams.
Cloud Expertise
Cybersecurity experts provide extensive knowledge of cloud platforms, cloud security best practices and frameworks, and business cloud security needs.
Arctic Wolf’s Cloud Detection and Response pricing is based on stable parameters including users and servers, allowing businesses to fully secure environments while controlling costs.
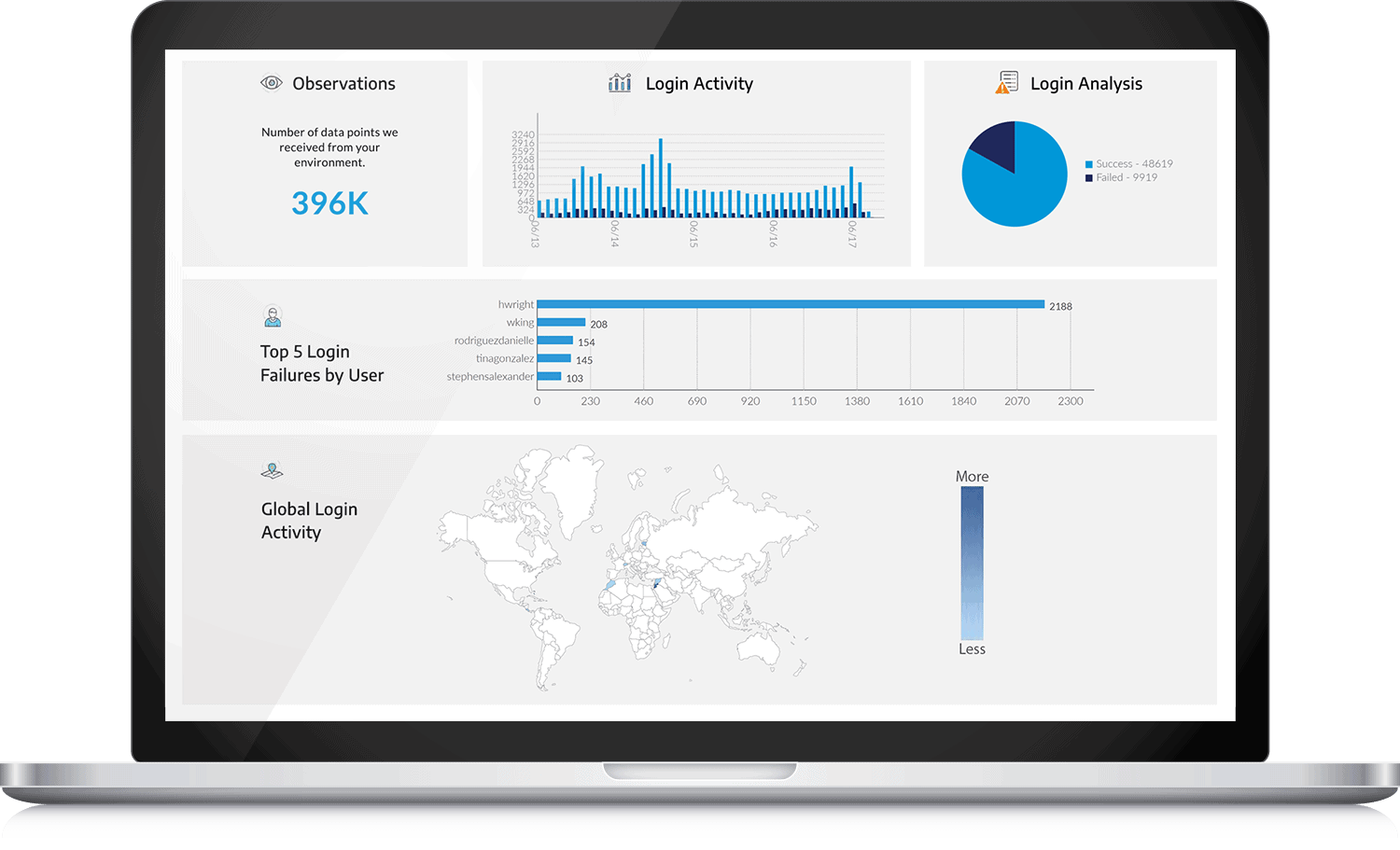
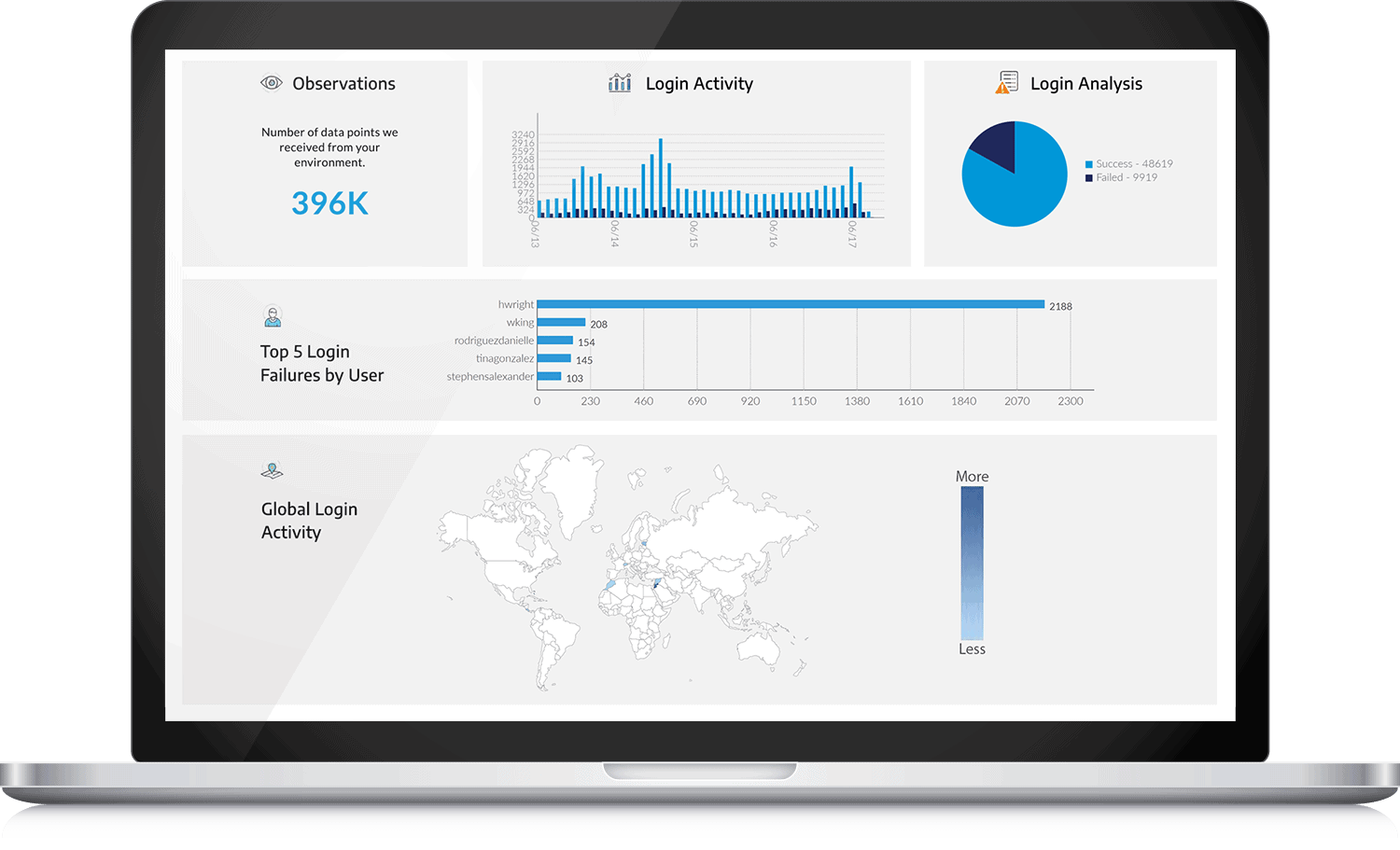
Get unlimited access into cloud security events with dashboards and standard and custom reporting.
Ready to Get Started?
We’re here to help. Reach out to schedule an introductory call with one of our team members and learn more about how Arctic Wolf can benefit your organization.
General Questions
