The 2020 edition of Momentum Cyber’s CYBERscape outlines 18 distinct categories within the cybersecurity industry. Each includes multiple sub-categories, with thousands of vendors in total.
For organizations of all sizes, the sheer volume of choices can make managing tools and developing a security strategy a difficult task. This fact is underscored by a recent survey conducted by Enterprise Strategy Group, which showed that 55% of enterprises currently use 25 or more cybersecurity technology products within their organization.
While organizations have no shortage of options when it comes to security products and vendors, this creates issues on its own. Gartner, the industry’s leading analyst firm on enterprise security, recently stated that “many security teams have over-invested in a plethora of tools.
As a result, they are also suffering from alert fatigue and multiple console complexity and facing the challenges in recruiting and retaining security operations analysts with the right set of skills and expertise to effectively use all those tools.”
Why More Cybersecurity Tools Isn’t The Answer
Another challenge with the abundance of market options is that many security tools are tightly clustered in terms of efficacy. Using endpoint protection tools as an example, many independent researchers have concluded that top solutions stop the nearly all common malware seen in the wild.
For an IT or security decision maker, this means they can select almost any leading solution in the market and be protected from the vast majority of malware threats.
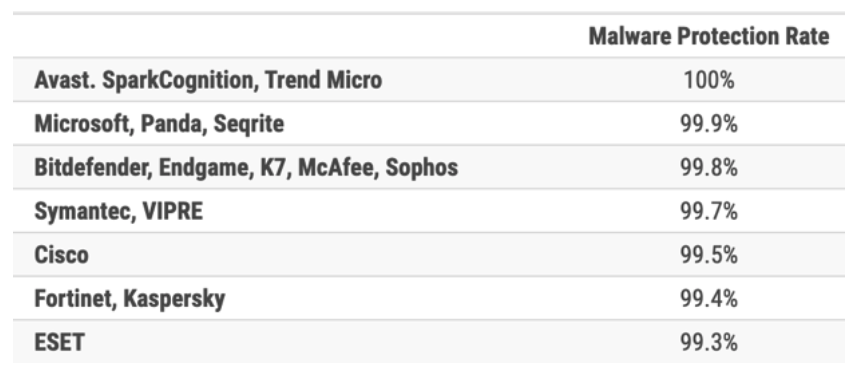
The table above comes from AV Comparatives’ Business Security Test for the second half of 2019. The chart shows that 17 endpoint protection solutions scored over a 99% protection rate against real-world threats.
So, if real-world testing shows the majority of endpoint solutions stop threats, that leaves us with the question of:
Why Do Breaches Still Occur?
Before IT and security leaders spend another penny on cybersecurity, they need to strongly consider if swapping vendors or adding a new tool is actually going to move the needle in terms of overall security effectiveness.
Over time, the cybersecurity industry almost always met new challenges with new tools. Vendors pivoted from focusing signatures to heuristics to reputation to whitelisting to IOC sharing to sandboxing to machine learning to behavioral analytics, and now, to threat hunting. These moves responded to an ever-evolving adversary and only recently has the industry started to realize that the latest “silver bullet” will not stop all threats.
White Hat Cybersecurity Expertise Needed
One reason it’s so hard for organizations to be effective at cybersecurity is because the attackers themselves are smart, capable humans.With advanced persistent threats, the attacker gains a foothold in the environment to leverage “living off the land” strategies and tactics to masquerade as a legitimate user. So, human analysts and human intuition often provide the most effective way to detect and remove these types of threats.
As a result, a winning security strategy for organizations must include a significant emphasis on the human element—which brings its own challenges.
According to research from the 2019 SANS SOC Survey, only one in every 1,000 companies has a security operations center (SOC). Even in large enterprises this figure is only about 50 percent. To counter skilled and persistent human adversaries, organizations need to ensure their strategy includes skilled and persistent human defenders.
But because building a SOC and staffing it with talent is the harder path, they rarely do so.
The ineffectiveness of tools is further highlighted when looking at data from recently onboarded Arctic Wolf® customers. As part of this onboarding process, the Concierge Security® Team (CST) works with customers to configure their environments so that, using the Arctic Wolf® Platform, the CST can detect and respond to threats on their behalf. As new customers, they serve as an ideal environment to examine what types of threats can go undiscovered by a company’s existing tools and processes.
Sample Findings from Arctic Wolf
Advanced Threats
Advanced threats such as malware are found in 70% of all new Arctic Wolf customers. These threats have already bypassed existing security tools and processes deployed by the customer and have been embedded within an organization’s environment.
Phishing
Most companies have some sort of email protection platform in place, but phishing activity is discovered to have bypassed those tools in 18% of the new organizations we protect.
Account Takeover
70% of new Arctic Wolf customers have some form of personally identifiable information tied to their corporate credentials available on the dark web, and 5.5% of all new customers have an exposed plaintext password published online.
Cloud Monitoring
Protecting data in the cloud by identifying misconfigurations and other vulnerabilities is a growing challenge for many businesses. Nearly half (47%) of all security incidents detected across new Arctic Wolf customers include a cloud component. While businesses continue their rapid adoption of cloud applications and services, they still struggle with cloud security—and attackers are exploiting that gap.
If your organization is tired of buying new tools and wishes to develop a more strategic approach to security, our new white paper “The Path to Security Effectiveness” outlines a vision for how businesses can take the first steps on their security journey. The paper highlights the five key pillars of taking an operational approach to security and outlines why many organizations continue to experience failures with their security operations.
Get started on the next phase of your security journey. Read The Path to Security Effectiveness now.






