Cyber attacks wait for no one; they routinely disrupt even the best-laid plans. That’s why Arctic Wolf’s Concierge Security® Team has put together a checklist to help you start the year off on the right foot. These recommendations are already helping our customers improve their security posture, and they can make your operations run smoother as well.
Security Operations Checklist
1. Catch Up on Patching
As a cybersecurity professional, you know full well the devastating effects poor patch management can have on an organization, and that it’s caused some of the world’s most notorious cyberattacks. The start of the new quarter is a great time to catch up on any outstanding patching tasks before they catch up with you.
2. Reevaluate the Metrics You’re Tracking
Do they make sense given changes to your business and the threats they face? Make sure the metrics still add value to operations management and tell a story to champion your successes or highlight further investment needs.
3. Determine What Features of Your Existing Technologies Are Underutilized, and Quantify Your Risks
Over the last several years, we’ve seen a rapid increase in the number of security tools used by both large and small organizations, which limits return on investment while often increasing the risk of cyberthreats.
This “security tool tipping point” results in technology that’s often underutilized, wasted security resources, and overwhelmed security teams who spend more time trying to manage tools than proactively defending against threats.
This year, shift your focus. Get more out of the investments you’ve already made, become more selective with new technology acquisitions, and ensure what you use fits with your existing security models.
4. Map Risks Broadly
Make certain that your security practices are informed by larger business priorities, compliance frameworks, and known threat actor types; then, after that, address risks at a micro-level to ensure a thorough and well-rounded security posture.
5. Update Your Attack Surface Map
Over time, your understanding of the attack surface improves. Use that knowledge to incrementally identify and manage future risks as changes occur both internally and externally. Ask yourself:
- What’s changed?
- What are we doing differently? (New technology, a new approach, new threats.)
- What holes could have opened up?
Use your answers to make the appropriate changes and mitigate your risk.
6. Take a “Tour” Around the Data Center
Things change. There are a number of factors to keep in mind to make sure your security posture is current and still meets your organization’s objectives. Here are a factors to routinely keep an eye on and address:
- Are there passwords that need updating?
- When was the firewall configuration last evaluated?
- Does the employee database match active directory?
- Are there rogue IT devices on the network?
- Are the email filtering controls tight enough?
7. Improve Your Visibility Across the Enterprise
Are you aware of all of the devices your company has? Do you know where each of them is located? Any idea what versions they are?
You’re not alone. Many security departments don’t have a solid grasp of where all their valuable assets are located or how they are secured. Make it your business to find out.
Always remember: You can’t protect what you don’t know you have.

8. Recognize and Celebrate your Wins
While the job of managing cyber risk is never done, it’s essential to take time to celebrate the large and small wins by you and your team.
Use the metrics from above to illustrate tangible improvement to both your team and the C-suite. This will increase morale and confidence in your security program.
9. Up-Level Your Team
Provide your team with opportunities to grow by making regularly scheduled time for skill development to stay up to date on your industry, new threats, new technologies, and new methodologies. Take advantage of free webinars, internal lunch and learns, and virtual networking with former colleagues to learn about the strategies they’ve seen success with at their organizations.
10. Plan for Ransomware
As high-profile ransomware incidents happen more frequently, it’s critical that you have a plan in place in case it happens to you. Who has the authority to “shut it all down” at 3:00 in the morning? What can be preauthorized? Figure it out now so that your team is ready later. You probably already have a crisis management plan; review it to ensure it includes a procedure for dealing with ransomware.
11. Look in the mirror and determine what can be outsourced
As much as you might like to have everything in-house, organizations increasingly rely on key partners for certain aspects of security operations. And for good reason: no one can do it all alone, not with the sheer number of threats coming at you every day.
Here are three areas you should consider outsourcing:
1. Security Operations Center (SOC): Affordable and reliable 24×7 coverage is available to help ease the burden for your internal team.
2. Vulnerability Management: Find a trusted partner that can help you manage the never-ending list of vulnerabilities your organization faces.
3. Cloud Monitoring: Business units are quickly moving applications and workloads to the cloud, forcing a hybrid cloud management strategy onto IT and security without fully understanding the risks or complexity of cloud environments.
New year, new threats. And this year, just like every year previously, will bring more risk than ever before. However, by checking these 11 activities off your list at the beginning of the year, your organization will be more secure than it’s ever been.
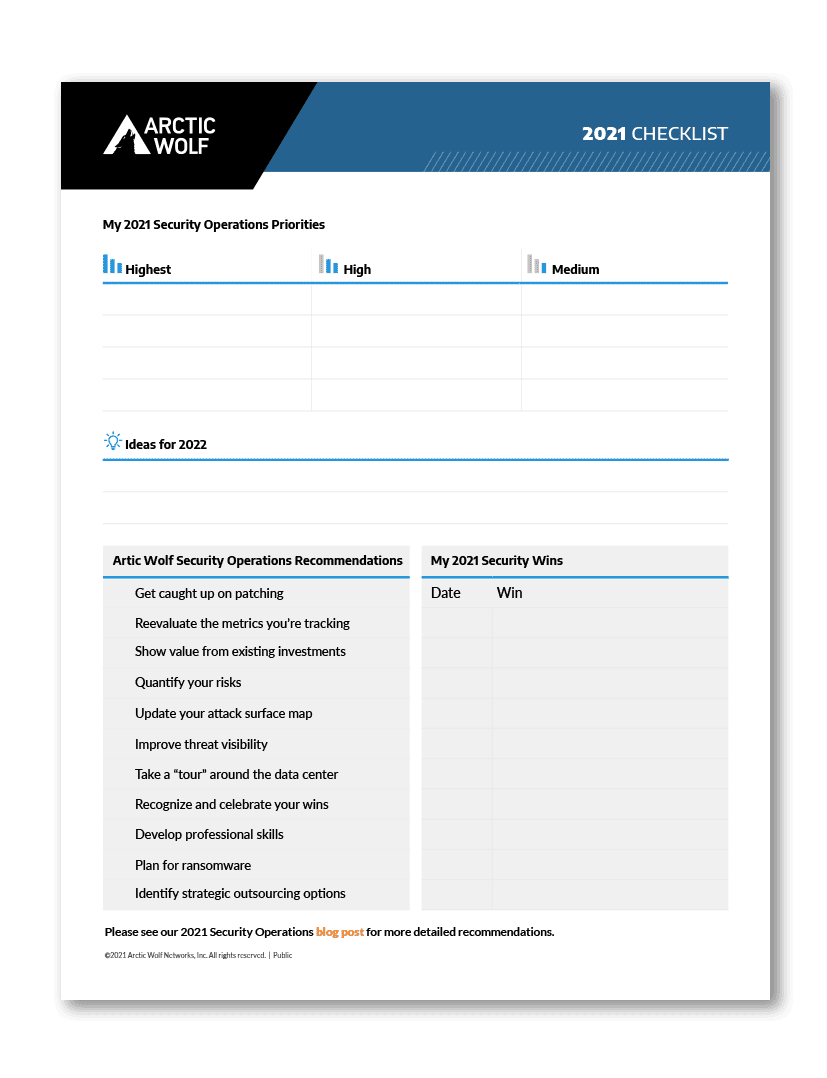
Download your interactive 2021 Security Operations Checklist to highlight your priorities and showcase internal wins.
Need to strengthen your security posture? Help is just a click away. Arctic Wolf delivers dynamic 24×7 cybersecurity protection tailored to the specific needs of your organization.
-Mark Manglicmot, Vice President Security Services