What barriers are organizations still dealing with on their security operations journey? The upcoming 2020 SOC Survey hopes to provide more insight into the subject, building off of last year’s survey that highlighted a number of issues preventing a security operations center (SOC) from becoming integrated within an organization.
In Arctic Wolf’s “The Path to Security Effectiveness” white paper that we published earlier this year, we outlined a vision for how organizations can improve their security operations practices. While the white paper laid out how organizations can achieve an ideal state, the vast majority of organizations are still working towards that goal.
2020 SOC Survey: Ongoing Security Operations Challenges
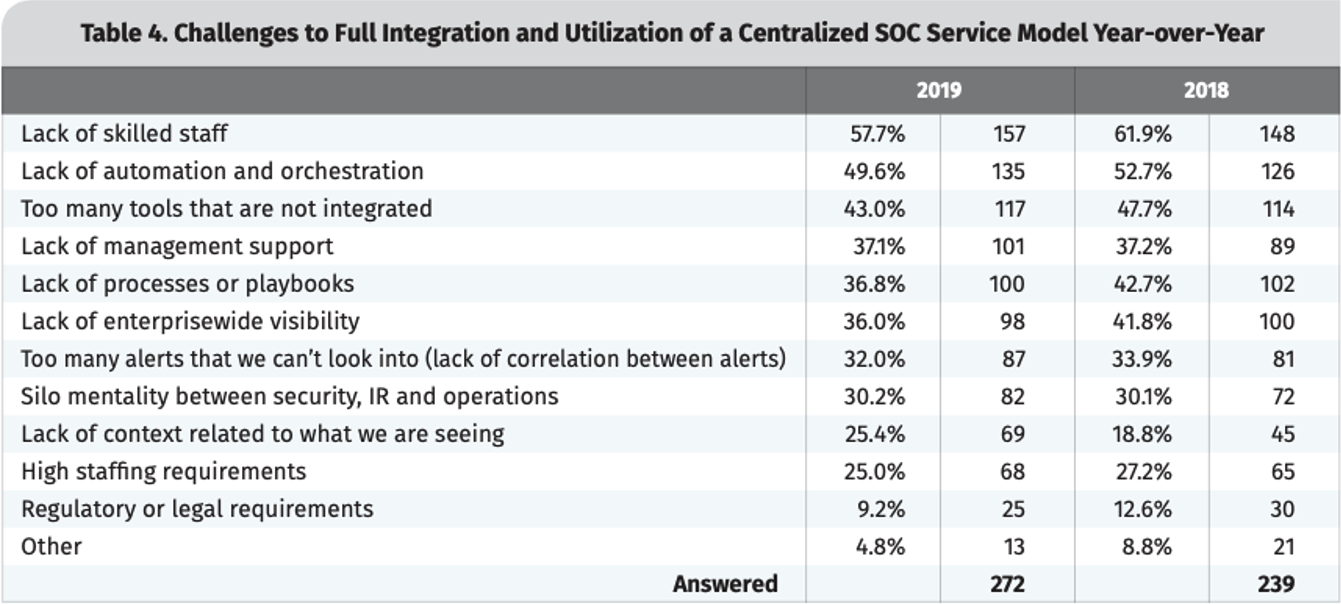
A lack of staff who can accomplish the necessary tasks for the SOC was the most commonly cited shortcoming in the 2019 SANS SOC Survey. After that, tools were blamed for not being integrated and for failing to perform the task of automating work away from analysts.
What does Arctic Wolf expect the 2020 SOC Survey will reveal? To be honest, probably more of the same.
Tools Alone Still Aren’t the Answer
Over time, the cybersecurity industry has typically met new challenges with new tools. Vendors pivoted from focusing signatures to heuristics to reputation to whitelisting to IOC sharing to sandboxing to machine learning to behavioral analytics, and now, to threat hunting. These moves responded to an ever-evolving adversary, and only recently has the industry started to realize that the latest-and-greatest tool will not stop all threats.
One reason it’s so hard for organizations to be effective at cybersecurity is that the attackers themselves are smart, capable humans. With advanced persistent threats, once the attacker gains a foothold in an environment, they leverage “living off the land” strategies and tactics to masquerade as a legitimate user. Human analysts and human intuition are often the most effective way to detect and remove these types of threats. As a result, a winning security strategy must include a significant emphasis on the human element. However, finding the right way to add this human element remains a considerable challenge in itself.
The do-it-yourself model has proven ineffective for most organizations. Hiring in-house security experts and building a 24×7 coverage team is cost-prohibitive for all but the largest organizations. The average salary of a security analyst is approximately $100,000 and, according to Gartner, a fully functional SOC running 24×7 requires at least eight to 12 full-time employees regardless of company size.
We also believe these security operations barriers are compounded in 2020 by the COVID-19 pandemic. With organizations often turning to remote work, many invest in more tools to secure their distributed workforce. Yet, the challenges of integration and alert fatigue only worsen with the addition of more tools. At the same time, the continuing cybersecurity skills shortage is exacerbated as professionals with the skills in demand are generally less willing to change employers in the midst of an uncertain economic climate.
How to Participate in This Year’s SOC Survey
Are we right? Are we wrong? Help us find out by participating in the 2020 SOC Survey.
The survey at SOC-Survey.com takes approximately 20 minutes from start to finish.
The SOC Survey is a community initiative being led by Chris Crowley to provide objective data to security leaders and practitioners looking to establish a SOC or optimize their existing SOCs. The survey is currently open for completion, with a full report and dataset published by Chris and other volunteers this year.
Next Steps
- Take 20 minutes and complete the 2020 SOC Survey
- Revisit the complete 2019 SOC Survey results (SANS account required)
- Get additional insights from Arctic Wolf’s recently published Security Operations Report